The cybersecurity landscape is witnessing a rapid transformation, driven significantly by the integration of Large Language Models (LLMs) into the development lifecycle of malicious software. A recent, fleeting intrusion into the threat ecosystem, dubbed the Arkanix Stealer operation, provides compelling, albeit brief, evidence of this trend. Emerging on various clandestine forums in the latter part of 2025, Arkanix vanished as quickly as it appeared—its entire infrastructure dismantled without warning just two months after its initial promotion. This rapid self-immolation suggests that Arkanix was not a long-term criminal enterprise but rather a high-velocity proof-of-concept, likely engineered with significant assistance from generative AI tools.
The operational model for Arkanix mirrored established, sophisticated malware-as-a-service (MaaS) frameworks. It featured a dedicated administrative control panel for affiliates and a centralized Discord server intended to foster a community for user support, feature requests, and operational updates. This structure, typical of successful stealer operations, was deployed with astonishing speed, according to analysis conducted by security researchers at Kaspersky. The key differentiator, and the source of its unusual trajectory, lies in the underlying development methodology. Forensic analysis of the code revealed distinct signatures strongly indicative of LLM involvement, a factor that security experts posit drastically compressed the usual timelines and resource expenditures associated with creating new, functional malware.

Background Context: The Shifting Malware Economy
The prevalence of sophisticated infostealers—malware designed to harvest credentials, cryptocurrency wallets, and sensitive files—has been a consistent threat for over a decade. Traditionally, developing a competitive stealer required specialized coding expertise, extensive reverse engineering knowledge, and significant time investment to implement evasion techniques and modular functionality. This barrier to entry often favored established cybercriminal syndicates.
The advent of highly capable LLMs, however, is democratizing the creation of complex tools. By leveraging these models, less experienced threat actors can rapidly prototype functional code, debug issues, and integrate advanced features previously requiring specialized knowledge. Arkanix appears to be a direct manifestation of this new capability. It presented itself not as a raw, vulnerable script, but as a polished, dual-tiered product ready for immediate deployment by affiliates, signaling an attempt to test the viability of LLM-assisted malware development in a live, albeit brief, market setting.
The rapid withdrawal of Arkanix—the shuttering of its control panel and community forum—is noteworthy. For a typical, successful MaaS operation, two months is insufficient time to recoup development costs, let alone establish market share. This brevity reinforces the hypothesis that Arkanix was fundamentally an experiment. The goal may have been to validate the efficiency gains provided by AI development tools: Can a fully functional, obfuscated stealer be built, marketed, and tested in a compressed timeframe? If so, the implications for the speed at which new, highly evasive threats will emerge are profound.

The Two-Tiered Offering and Aggressive Marketing
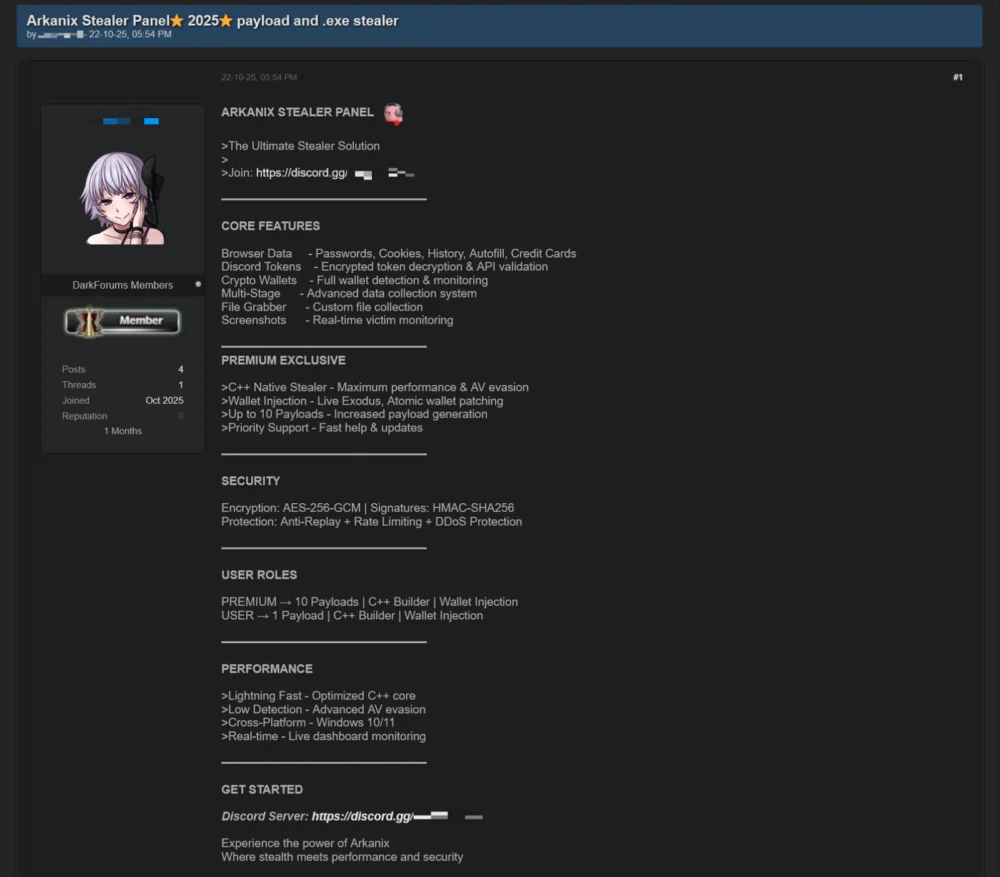
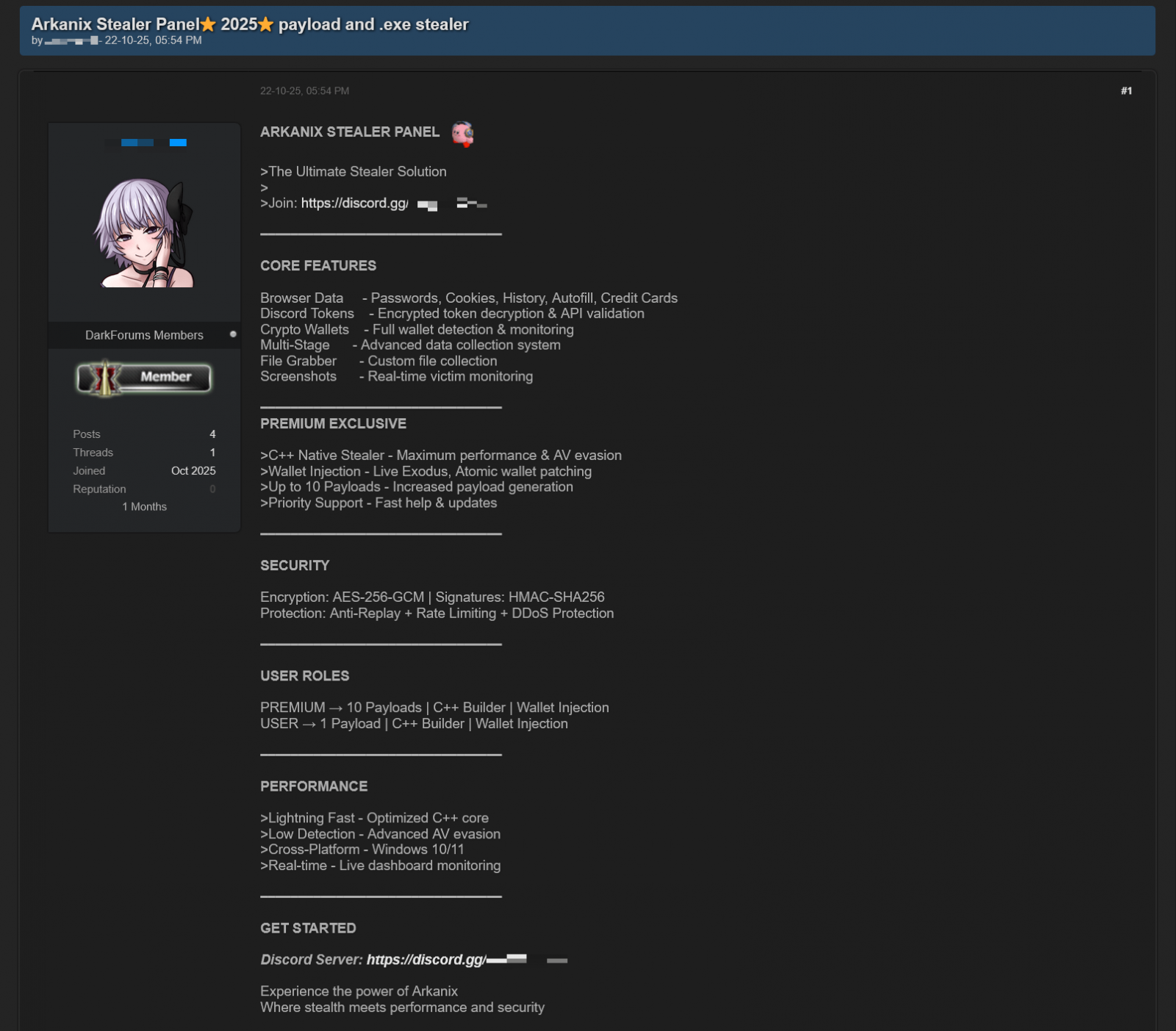
When Arkanix first surfaced in October 2025, it was immediately positioned with a clear value proposition targeting varying levels of criminal sophistication. The basic tier utilized a Python-based implementation, offering fundamental data exfiltration capabilities suitable for entry-level actors. The "premium" tier, however, represented a significant escalation in complexity and defensive measures. This version was compiled into a native C++ payload, fortified with VMProtect obfuscation, and crucially, integrated advanced anti-analysis features alongside specific wallet injection capabilities designed to siphon digital assets directly from compromised systems.
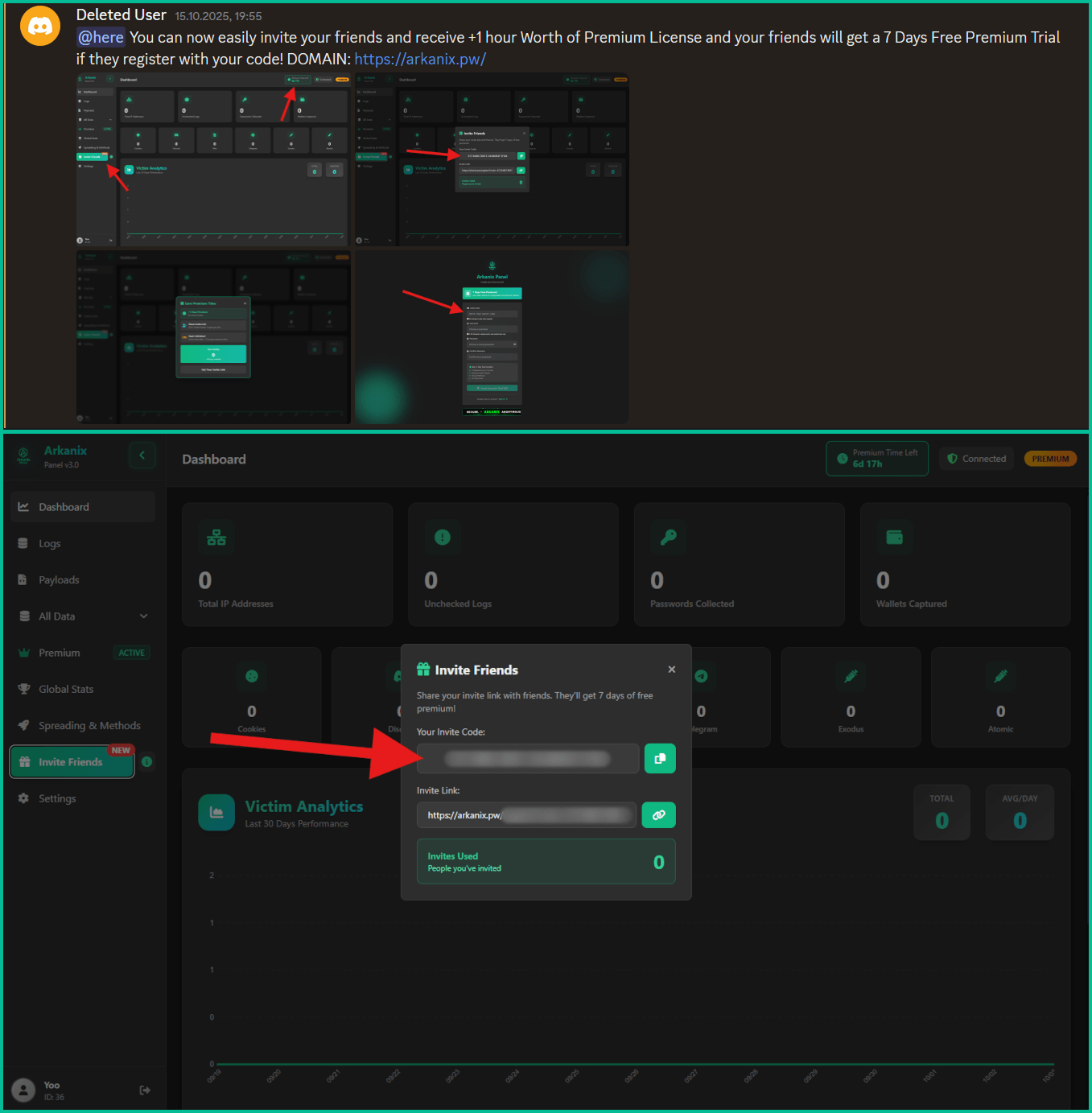
The operational infrastructure supported this tiered marketing approach. The developer maintained an active engagement channel via Discord, transforming what might have been a simple transaction platform into a nascent community hub. This allowed for real-time patch deployment, feature roadmap discussion, and direct technical support—a hallmark of professional software distribution, albeit applied to illicit activities.
Furthermore, the marketing strategy leaned heavily into viral adoption through a referral system. Affiliates who successfully brought in new customers were rewarded with extended premium access, while prospective buyers were offered a week of complimentary access to the high-tier C++ variant. This calculated approach aimed to rapidly seed the malware across various threat actor networks, maximizing initial infection vectors and gathering early performance metrics before the inevitable detection by security vendors.
Deep Dive into Arkanix’s Exfiltration Capabilities
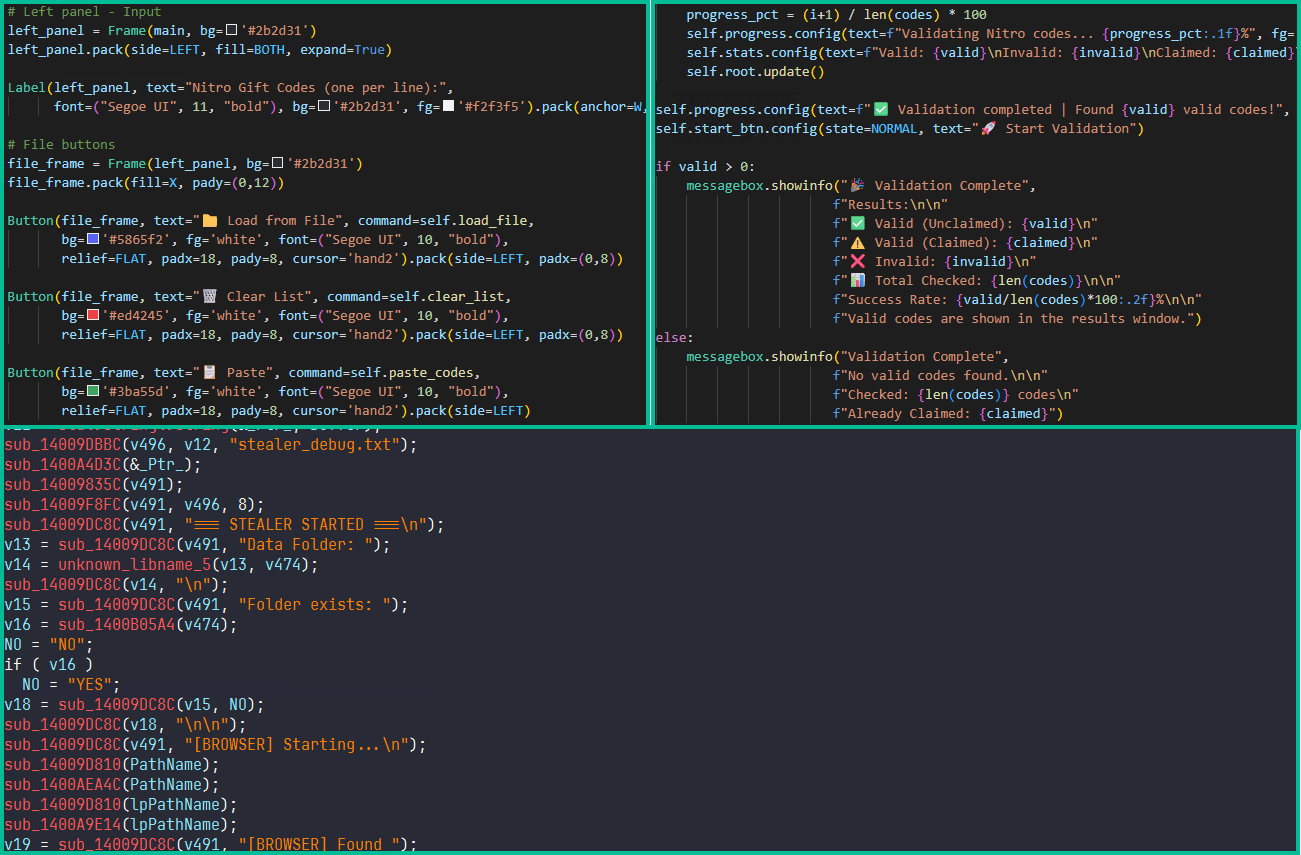
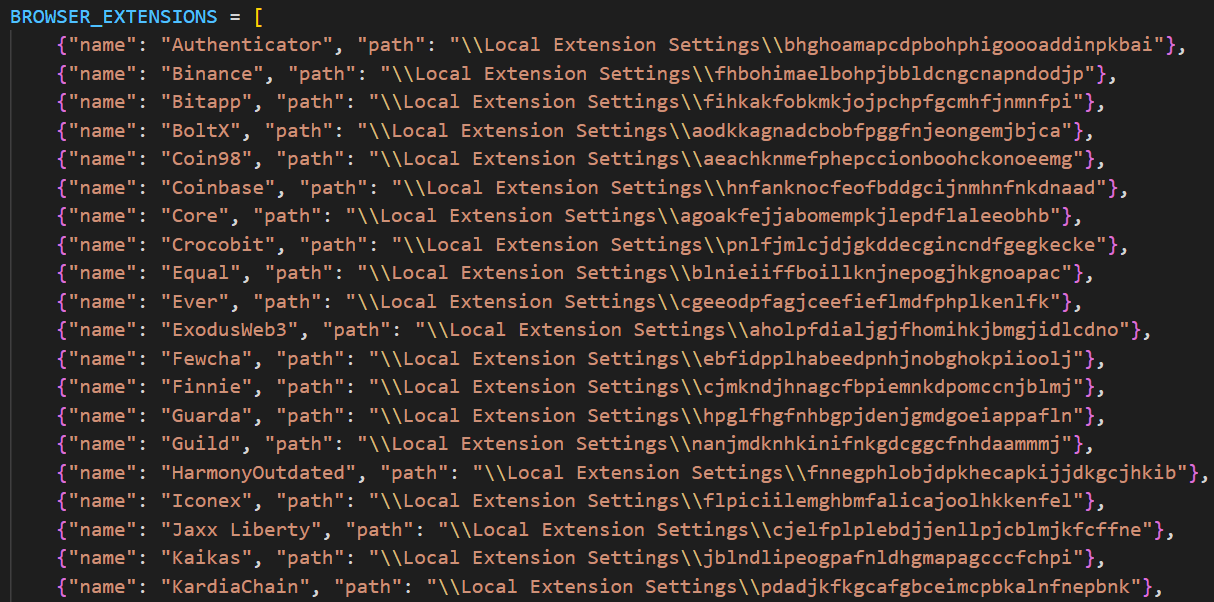
The functionality baked into Arkanix underscores the sophistication achievable even in a short development cycle, likely due to LLM augmentation. The malware’s baseline capabilities included comprehensive system reconnaissance, data harvesting from 22 different web browsers (including history, cookies, saved passwords, and autofill data), and the direct targeting of cryptocurrency wallet credentials. Kaspersky researchers specifically noted the malware’s ability to extract OAuth2 tokens from Chromium-based browsers, a method that allows for session hijacking beyond simple password theft.
Beyond standard browser scraping, Arkanix exhibited specialized targeting:
- Communication Hijacking: It actively sought credentials for Telegram and Discord. Of particular concern was its ability to leverage the Discord API to propagate itself laterally, sending malicious messages to the victim’s contacts or channels, effectively using compromised accounts as vectors for further infection.
- VPN Credential Theft: The stealer specifically targeted login details for prominent VPN services, including Mullvad, NordVPN, ExpressVPN, and ProtonVPN. This suggests an awareness among the operators that high-value targets often employ VPNs, and stealing these credentials grants persistent, disguised access.
- Asynchronous Data Staging: The malware was capable of identifying, archiving, and exfiltrating selected files from the local filesystem asynchronously, ensuring that large data pulls did not immediately trigger system performance alerts or network monitoring flags.
The premium C++ variant elevated the threat profile substantially. It incorporated robust defensive measures such as anti-sandbox and anti-debugging checks, essential for evading automated analysis environments used by security firms. It also employed WinAPI-level screen capturing for targeted surveillance.
Critically, the premium version included modules for stealing Remote Desktop Protocol (RDP) credentials and targeted gaming/software platform credentials (Epic Games, Battle.net, Riot, Unreal Engine, Ubisoft Connect, and GOG), indicating a strategy focused on both corporate access (via RDP) and digital asset/account takeover.
The most advanced component shipped with the premium variant was the ChromElevator post-exploitation tool. This module demonstrated advanced evasion by injecting code directly into suspended browser processes. This technique is specifically designed to circumvent modern browser security mechanisms, such as Google’s App-Bound Encryption (ABE), which protects stored user credentials, allowing unauthorized access even when the browser is not actively running.
Industry Implications: The AI-Driven Velocity of Threat Evolution
The Arkanix incident serves as a significant canary in the coal mine for the cybersecurity industry. The primary implication is the drastic reduction in the time-to-market for new, feature-rich malware strains. If an actor can leverage LLMs to produce a modular, evasive stealer with integrated marketing and support infrastructure in a matter of weeks—a process that traditionally took months or years—the defensive timeline shrinks critically.
This accelerates the "arms race" dynamic. Security vendors must now contend with polymorphic or novel malware variants appearing with greater frequency, potentially outpacing the deployment cycle for updated threat intelligence signatures and behavioral detection models. Kaspersky’s assessment that Arkanix felt "more of a public software product than a shady stealer" highlights this professionalization. Malicious tools are increasingly resembling legitimate commercial software in their structure, support, and modularity.
For security operations centers (SOCs), this necessitates a fundamental shift away from purely signature-based detection towards robust, AI-powered behavioral analytics. Systems must be capable of identifying the intent and pattern of execution, rather than relying on known file hashes, which are obsolete almost immediately upon the release of a new variant like Arkanix.
Future Impact and Expert Analysis: The Experiment’s True Purpose
While the immediate threat posed by Arkanix is now neutralized due to its self-termination, its existence provides invaluable intelligence on the trajectory of cybercrime development. Security analysts suggest that the project’s swift demise was likely deliberate, serving one of two primary purposes:
- Benchmarking AI Efficacy: The developer may have sought to measure the efficiency gains. By launching a fully featured product, they could quantify how much time and cost were saved in coding, debugging, and feature implementation using LLMs compared to traditional methods. The data gathered from this two-month sprint could inform the development of a far more robust and enduring next-generation stealer.
- Testing Market Viability and Evasion: The brief public offering allowed the developer to test the C++ payload’s evasion capabilities against existing endpoint detection and response (EDR) solutions without committing to a long-term infrastructure investment. If the payload survived detection for two months across a broad user base, it validated the LLM-assisted obfuscation techniques.
The most concerning aspect is the integration of the ChromElevator tool. Bypassing technologies like ABE indicates that LLMs are not merely stitching together existing code snippets; they are capable of generating novel exploitation chains tailored to defeat specific, cutting-edge security countermeasures. This implies a future where malware dynamically adapts its exploitation methods based on the target environment, potentially rendering static defenses obsolete almost instantly.
In conclusion, Arkanix Stealer was less a sustained criminal venture and more a high-speed laboratory test for AI-augmented malware engineering. Its fleeting presence signals a worrying acceleration in the sophistication and availability of potent cyber tools. Security practitioners must treat this incident not as a closed case, but as a preview of the next generation of threat actors who will operate with AI-driven efficiency, demanding an equally rapid and technologically advanced defensive response. The indicators of compromise (IoCs) released by researchers—including file hashes, domains, and IP addresses—provide a necessary short-term containment measure, but the underlying technological shift demands long-term strategic adaptation.