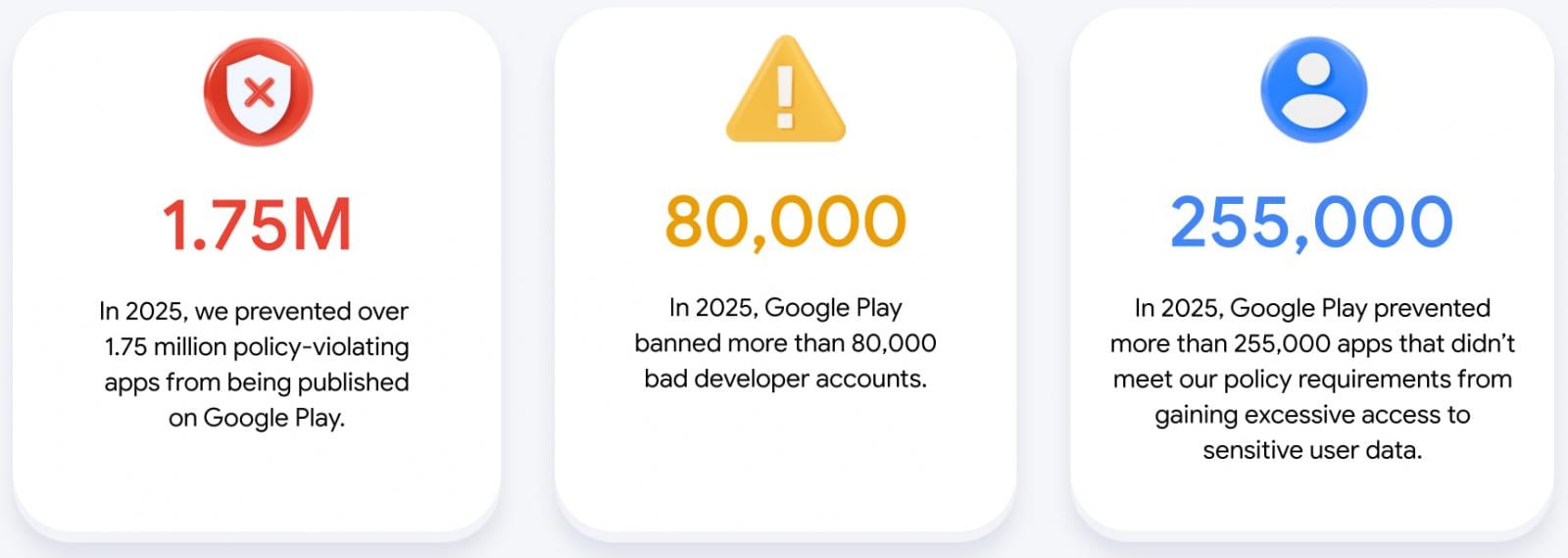
The digital distribution landscape for Android applications underwent a significant maturation phase in 2025, according to Google’s latest comprehensive security assessment. The report underscores a dramatic escalation in the platform’s defensive posture, highlighted by the rejection of over 1.75 million application submissions attempting to breach established publishing policies. Beyond outright rejections, the company proactively halted more than 255,000 proposed Android applications from gaining unwarranted, excessive access to sensitive user data—a critical metric reflecting a commitment to granular privacy control. This annual security review serves not merely as a statistical recap but as a roadmap detailing the effectiveness of layered security mechanisms deployed to preserve the integrity and trustworthiness of the Google Play ecosystem.
"Our commitment remains steadfast: we are perpetually refining our policies and fortifying our protective measures to cultivate an environment populated by high-quality, secure applications while preemptively neutralizing malicious actors before any potential harm can materialize," a representative statement from Google confirmed, signaling an aggressive stance against digital malfeasance.
This proactive stance is inextricably linked to technological advancement, particularly the deep integration of sophisticated machine learning. In 2025, the enforcement apparatus benefited from the deployment of over 10,000 discrete safety checks applied to submitted applications. Crucially, the effectiveness of these checks was amplified by weaving Google’s most advanced generative Artificial Intelligence models directly into the application review pipeline. This AI augmentation has proven transformative, enabling human analysts to identify intricate, polymorphic, and rapidly evolving malicious coding patterns with superior speed and accuracy compared to preceding years. The synergy between automated, AI-assisted detection and expert human oversight forms the bedrock of modern platform security.
The year’s enforcement achievements paint a vivid picture of the scale of operations required to maintain platform health. Key figures released include the outright banning of over 80,000 developer accounts identified as repeat or high-volume offenders—a direct measure targeting the source of coordinated attacks. These account purges complement the rejection of 1.75 million policy-violating apps and the denial of access for the aforementioned 255,000 apps seeking illicit data permissions. Analyzing these figures reveals a shift toward addressing systemic bad actors rather than reacting solely to individual compromised submissions.
The War on Deception: Ratings, Spam, and Ecosystem Integrity
Beyond traditional malware and data exfiltration threats, the integrity of user perception through ratings and reviews emerged as a significant battleground in 2025. Malicious actors increasingly leverage "review bombing" campaigns—coordinated efforts to artificially depress an app’s rating through a flood of negative, inauthentic reviews—or conversely, inflate the scores of undesirable software using bot networks. Such manipulation directly impacts discoverability, user trust, and ultimately, developer revenue.

Google’s defenses against this form of social engineering were robust. The company reported successfully blocking 160 million individual ratings throughout the year that were flagged as inauthentic or spam. Furthermore, the success of these countermeasures is quantified by the prevention of significant reputational damage: Google estimates it averted an average 0.5-star rating degradation for applications that would have otherwise been targeted by review bombing campaigns. This metric speaks volumes about the sophisticated nature of the deception being countered, moving security beyond mere code analysis into the realm of behavioral anomaly detection within user interaction data.
Strengthening the Perimeter: Play Protect and Sideloading Defense
While the Google Play Store represents the primary, curated distribution channel, the Android ecosystem inherently supports sideloading—installing applications from sources outside the official marketplace. This avenue remains a perennial vector for malware dissemination. Android’s foundational security layer, Play Protect, plays a crucial role in mitigating this risk.
Play Protect’s scanning capabilities, now reportedly analyzing over 350 billion applications daily, represent a massive computational commitment to ecosystem hygiene. This continuous vigilance resulted in the identification of over 27 million malicious applications that originated from third-party, non-Play Store sources. For users who bypass standard safeguards, Play Protect acts as a vital, last line of defense.
The expansion of Play Protect’s "enhanced fraud protection" framework further extended the security envelope. This feature, now operational across an estimated 2.8 billion Android devices spanning 185 distinct global markets, actively intercepts potentially dangerous installations. In 2025, this system successfully blocked 266 million installation attempts originating from 872,000 unique, high-risk applications identified across the network. The sheer volume of blocked installation attempts illustrates the constant, high-stakes dynamic between platform security teams and the global pool of opportunistic attackers.
Developer Tools and API Integration: Shifting Left on Security
A fundamental strategic shift observable in Google’s security narrative is the move "left"—embedding security checks and compliance mechanisms directly into the developer workflow rather than waiting for final submission. This preventative approach reduces friction for legitimate developers and raises the bar for malicious actors.
The Play Integrity API stands out as a core component of this strategy. Designed for developers to verify that their application is running on a genuine Android device, unmodified operating system, and unmodified application binary, the service has scaled dramatically. It now processes upwards of 20 billion integrity checks daily. The enhancements rolled out in 2025—specifically the incorporation of new hardware-backed security signals and the introduction of in-app remediation prompts—provide developers with finer-grained control over abuse vectors, enabling real-time responses to tampering or rooting attempts without user disruption if possible.

Furthermore, platform-level operating system enhancements are directly contributing to security without requiring significant developer overhaul. The introduction of built-in defenses against "tapjacking attacks" in Android 16, released in the preceding June, is a prime example. Tapjacking, a highly deceptive technique where hidden, often transparent overlays trick users into unknowingly clicking malicious buttons or advertisements, has been substantially neutralized by default OS-level blocking mechanisms. This move shields users from fraudulent financial gains derived from these automated clicks, requiring minimal, if any, code modification from app creators.
Industry Implications and Expert Analysis
The sheer scale of these enforcement statistics—millions of rejected apps, tens of thousands of banned accounts—has profound implications for the broader technology industry and the application economy.
Erosion of the Low-Effort Attacker: The heightened sophistication of Google’s AI-driven review process effectively raises the barrier to entry for low-effort, mass-produced malware or simple policy-violating applications. These actors, who often rely on quickly iterating minor changes to evade outdated signature-based detection, are increasingly being caught by models trained to recognize abstract malicious intent and complex behavioral anomalies. This necessitates that threat actors invest significantly more time and resources into developing evasive, zero-day-style exploits, which are inherently more expensive and riskier to deploy.
The Value of Verified Developers: The banning of 80,000 developer accounts signals a hardening of developer identity verification protocols. In the current environment, trust is no longer solely placed in the submitted code but in the verifiable identity behind the submission. This trend forces developers, particularly those operating in sensitive sectors, to embrace more rigorous Know Your Customer (KYC) and developer verification standards, aligning the app store with the compliance demands of traditional financial or enterprise software distribution.
AI as the New Security Arms Race: The integration of generative AI into the review process positions security as an AI-versus-AI contest. While Google leverages these models for defense, threat actors are simultaneously employing similar techniques for creating polymorphic malware, crafting highly convincing phishing lures within app descriptions, or rapidly generating code to exploit known vulnerabilities before patches are widely adopted. The industry must view these numbers not as a sign of victory, but as evidence of a perpetual, escalating technological conflict where the defender’s primary advantage lies in superior computational resources and data access.
Future Trajectories: Proactive Compliance and Ecosystem Maturity
Looking forward, Google has articulated a clear trajectory focused on embedding security deeper into the application lifecycle. The continued investment in AI-driven defenses is inevitable, but the most critical future direction appears to be the expansion of developer verification and the proactive embedding of compliance tools directly into development environments.
This concept of "shifting security left" moves beyond simple submission checks. If compliance tools can be integrated into Integrated Development Environments (IDEs) or Continuous Integration/Continuous Deployment (CI/CD) pipelines, developers can receive immediate feedback—and potentially automated code correction—if their build attempts to request excessive permissions or utilizes deprecated, insecure APIs. This approach aims to achieve near-zero policy violations upon final submission, dramatically reducing the load on the review teams while ensuring higher baseline security across the board.
Furthermore, the expansion of verification efforts suggests a move toward establishing tiers of trust within the developer community. Developers who consistently adhere to standards, utilize advanced security APIs like Play Integrity, and pass enhanced identity checks may benefit from faster review times or privileged access to beta testing programs. Conversely, developers with a history of violations, even if the individual apps are now compliant, will likely face perpetual scrutiny, creating a digital reputation system that governs access to the platform.
The cumulative effect of these strategies—AI-enhanced detection, hardware-backed integrity checks, aggressive account termination, and proactive developer tooling—is intended to transform the Play Store from a gatekeeper reactive to threats, into an ecosystem actively self-regulating and architecturally resistant to low-level abuse. While the volume of blocked submissions in 2025 demonstrates the persistent challenge posed by bad actors, the technological sophistication deployed in response confirms Android’s ongoing commitment to maintaining a platform where user trust is a quantifiable and actively defended asset. The success of these measures will be measured not just in rejected apps, but in the sustained health and reliability experienced by the billions of users accessing Android services daily.

