The landscape of mobile application security is undergoing a profound transformation, shifting from reactive threat management to proactive, intelligent defense. Recent disclosures from Google confirm an aggressive escalation in its efforts to sanitize the Android ecosystem, driven largely by the necessity to counter increasingly sophisticated, AI-assisted adversarial tactics. This strategic pivot involves leveraging advanced machine learning models to vet applications and developers before they ever reach the vast user base of the Google Play Store.
This intensified campaign represents more than just a routine policy enforcement cycle; it signifies an arms race where platform custodians must continuously outpace malicious actors who are themselves utilizing generative AI to craft novel malware and evasive techniques. According to insights provided by Vijaya Kaza, Google’s Vice President of App & Ecosystem Trust, the scale of these defensive operations over the preceding year was staggering. The company successfully intercepted more than 1.75 million applications deemed in breach of established policies prior to public availability. Furthermore, the crackdown extended to the source, resulting in the termination of over 80,000 developer accounts identified as persistent vectors for harmful software distribution.
The Core of the Defense: AI Integration in Vetting
The critical differentiator in this recent security push is the deep integration of artificial intelligence directly into the application review pipeline. Historically, app vetting relied heavily on a combination of static code analysis and human inspection. While human expertise remains crucial for interpreting context and nuanced policy violations, the sheer volume of submissions—coupled with the increasing complexity of obfuscation techniques employed by malware—necessitated automation at a higher level.
Google’s deployment of sophisticated AI models within the review process fundamentally alters the speed and efficacy of threat detection. These machine learning systems are trained on vast datasets of known malicious code, behavioral anomalies, and policy contraventions. They excel at identifying subtle, non-obvious patterns indicative of deceptive functionality, hidden data exfiltration methods, or exploitation payloads that might be easily missed during a rapid human audit. This capability is paramount in an environment where threat actors use AI to rapidly iterate and test new malware strains designed specifically to evade traditional signature-based detection methods. By embedding AI early, Google effectively shifts the point of failure backward, catching violations during the submission phase rather than post-publication, which significantly mitigates user exposure.
Deepening Privacy Safeguards and Developer Tooling
Beyond outright malware, a major focus of this heightened scrutiny involves granular control over data access and privacy violations. The sheer proliferation of apps demanding excessive permissions—a common tactic to harvest user data for advertising, profiling, or outright fraud—has been met with equally robust algorithmic countermeasures. Last year alone, Google reported blocking access for over 255,000 applications that exhibited disproportionate requests for sensitive user data.
This statistical evidence points to a systemic enforcement against what might be termed "permission creep." For instance, applications ostensibly serving simple functions, like a calculator or a utility tool, were flagged for unwarranted requests for continuous location tracking or access to the device’s contact list or photo gallery. This level of enforcement suggests the AI models are capable of context-aware analysis, cross-referencing the declared function of an app against its requested API access profile.
Crucially, this defensive posture is being reinforced at the point of creation through developer tooling. The introduction and enhancement of tools like Play Policy Insights, integrated directly into the Android Studio development environment, serve as an upstream deterrent. These tools provide developers with real-time feedback regarding potential policy conflicts within their code before compilation and submission. For legitimate developers, this accelerates compliance; for malicious actors attempting to deploy slightly modified, "grayware" applications, it forces a quicker iteration cycle, making sustained evasion more resource-intensive.
Combating Ecosystem Manipulation: Review Spam and Rating Integrity
The battle for platform integrity extends beyond the binary of malware versus benign software; it heavily involves maintaining the credibility of the ecosystem’s social proof mechanisms, namely user ratings and reviews. Organized manipulation of these metrics—both boosting legitimate apps via fake positive reviews (astroturfing) and damaging competitors via coordinated negative attacks (review bombing)—erodes user trust and distorts market visibility.
Google reported blocking a massive 160 million spam ratings and reviews throughout 2025. This figure underscores the industrial scale of review manipulation operations. The company noted a significant success in neutralizing organized efforts to artificially suppress an application’s score, claiming to have prevented an average drop of half a star for apps specifically targeted by coordinated negative campaigns.
Analyzing this success requires understanding the AI’s role in discerning genuine user feedback from bot-generated noise. Modern review spam often involves sophisticated tactics like staggered posting times, varied language generation (often using LLMs), and behavioral patterns that mimic legitimate users. Google’s security apparatus must therefore employ behavioral analytics, IP clustering, and sentiment analysis tools that operate at a scale far beyond manual verification to effectively quarantine and nullify these synthetic contributions.
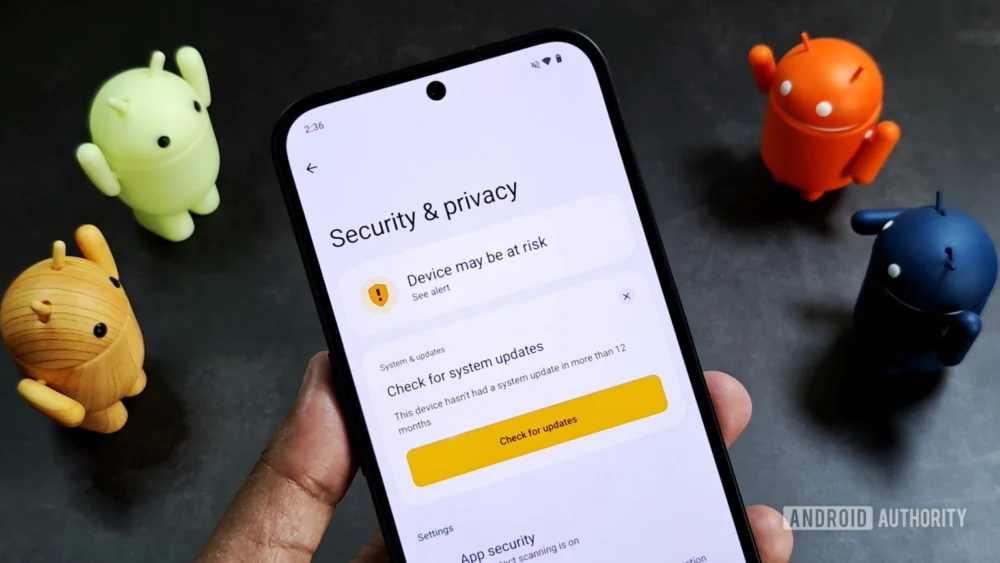
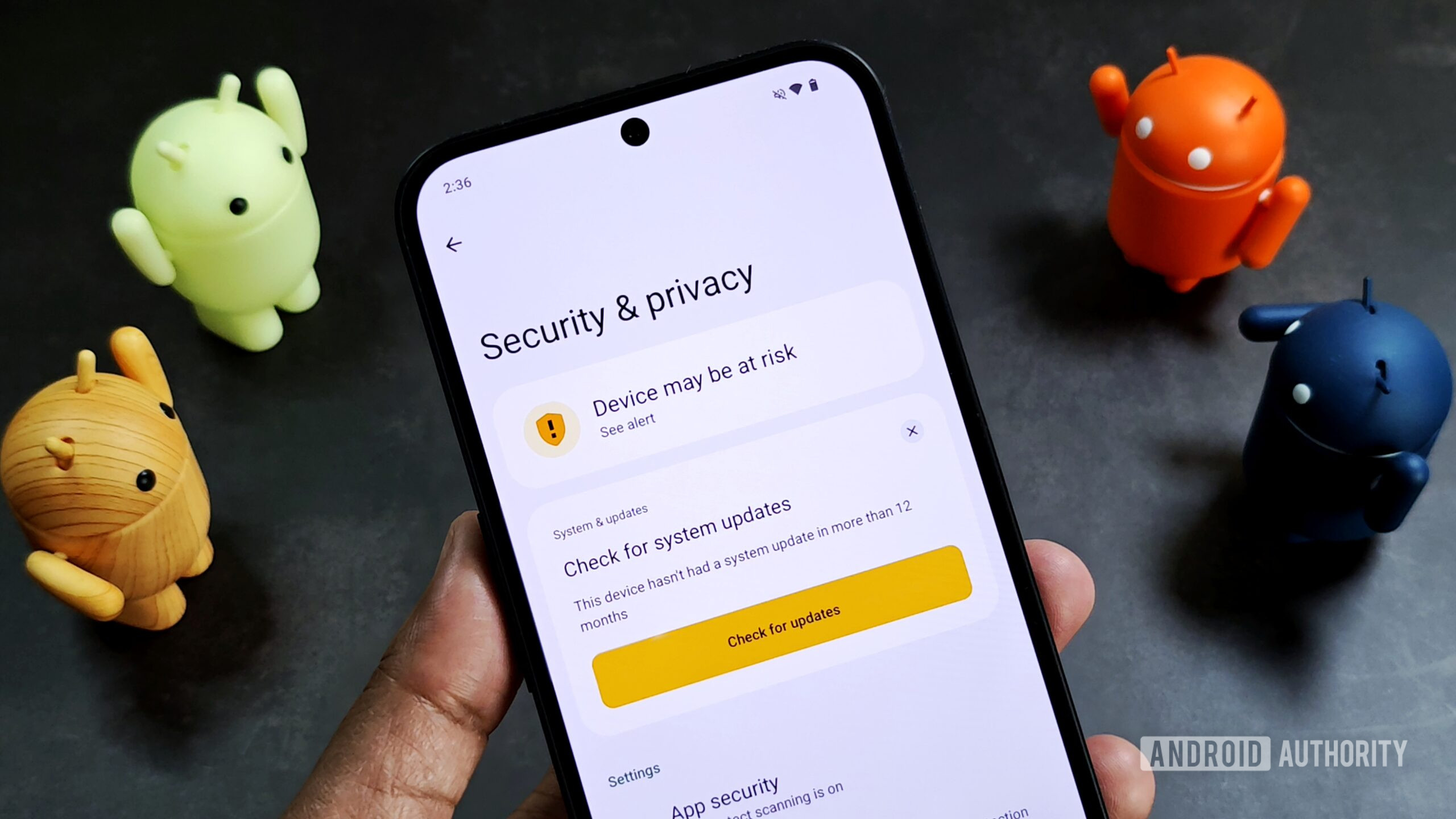
Extending Defenses Off-Store: The Role of Google Play Protect
The security perimeter is no longer confined solely to the official storefront. Given Android’s open nature, users frequently sideload applications from third-party repositories, forums, or direct web downloads. Google Play Protect, the platform’s integrated, always-on malware scanner, serves as the crucial last line of defense in these scenarios.
Play Protect’s operational scope is immense, performing daily scans on over 350 billion installed applications. This continuous monitoring is essential because malware often remains dormant or only activates its malicious payload after deployment. In the past year, this real-time scanning capability successfully identified and flagged 27 million new malicious applications sourced from outside the Play Store ecosystem.
A particularly significant advancement has been the hardening of Play Protect’s protection against installations originating from untrusted internet sources. The enhanced fraud protection module now actively intervenes when an application downloaded via a browser or messaging client attempts to request highly sensitive permissions. This targeted blocking mechanism, which launched across 185 markets and covered 2.8 billion active devices, resulted in the prevention of 266 million risky installation attempts. This metric is a direct indicator of user behavior modification—preventing the installation is inherently superior to detecting malware after it has already compromised the device.
Furthermore, Google has taken steps to neutralize social engineering tactics frequently employed during the installation or initial setup phase. Scammers often rely on phone calls or immediate in-app prompts to trick users into temporarily disabling security features. In a powerful policy update, Play Protect has now removed the user-facing option to disable its core protective functions while an active phone call is in progress. This directly thwarts a common attack vector where distraction is weaponized to bypass layered security controls.
Industry Implications and Future Trajectories
These aggressive defensive measures have significant implications for the broader technology sector. For platform developers, Google is setting a high, AI-driven baseline for security compliance. This forces smaller, less resourced developers to either adopt better internal security practices or risk immediate rejection or removal. The cost of compliance rises, but the overall security posture of the platform benefits.
The increased focus on AI-driven detection validates the ongoing industry shift toward predictive security analytics. Competitors and adjacent technology sectors are likely to follow suit, embedding similar machine learning frameworks into their own vetting processes, whether for enterprise software distribution or content moderation.
Looking ahead, Google is signaling a dual focus: easing entry for legitimate creators while tightening verification for all. The planned opening of developer verification to a wider pool, including students and hobbyists, suggests a desire to foster innovation, albeit coupled with a commitment to a "simpler process" that presumably integrates automated identity verification or enhanced background checks to maintain trust.
Moreover, the platform itself is receiving underlying security enhancements. The anticipated arrival of Android 16 includes architectural improvements designed to mitigate specific application-level threats. The introduction of a simplified coding mechanism to safeguard sensitive user data—such as credentials entered into banking applications—against "tapjacking" attacks (where an invisible overlay redirects a user’s input to a malicious target) demonstrates a commitment to addressing obscure but high-impact vulnerabilities at the OS kernel level.
In conclusion, Google’s recent operational report reveals a determined, technology-forward strategy against digital threats. By aggressively deploying machine learning to police submissions, scrutinize permissions, maintain review integrity, and fortify real-time scanning, the company is constructing a significantly more resilient environment. This move confirms that in the modern mobile landscape, security is no longer a feature; it is the fundamental operational imperative, driven by an escalating technological arms race against evolving adversaries. The sheer volume of preemptive blocks underscores a success story in digital defense, but the underlying arms race suggests this heightened state of vigilance is the new normal for the Android ecosystem.