The Android ecosystem, long celebrated for its open architecture and flexibility, is undergoing a significant shift in how it manages the installation of applications from outside the official Google Play Store. Effective as early as September of this year, Google is implementing changes that introduce a deliberate "high-friction" process for installing apps from developers who have not undergone formal verification. This move, while undoubtedly chafing power users accustomed to uninhibited freedom, appears increasingly pragmatic when viewed through the lens of escalating digital threats targeting the broader, less tech-savvy user base. Far from being an eradication of sideloading, this adjustment represents a critical evolution, designed to fortify the platform against sophisticated malware campaigns without resorting to the restrictive "walled garden" approach often associated with competitors.
The Shifting Landscape of Mobile Threat Vectors
To understand the necessity of this friction, one must first appreciate the dramatic intensification of threats targeting Android devices. The very openness that allows enthusiasts to deploy beta software, specialized tools, or open-source applications also provides fertile ground for malicious actors. The traditional vectors of attack have evolved beyond simple, poorly coded viruses; modern threats are highly targeted, socially engineered, and exploit user trust with alarming efficacy.
Recent industry data underscores this alarming trend. Cybersecurity firms have tracked a significant surge in attacks utilizing malicious Android Package Kits (APKs). Reports indicate that potential infection incidents on Android devices have risen substantially year-over-year, with a significant percentage of these discovered malware strains specifically engineered for financial theft. A third of these identified APK threats, for example, are directly linked to banking fraud schemes. This transition from general nuisance malware to organized, financially motivated intrusion demands a commensurate response from the platform owner.

Malwarebytes and Zimperium have cataloged numerous recent campaigns where attackers leverage social engineering—preying on human curiosity or desire for "free" premium content—to distribute weaponized APKs. These malicious packages frequently masquerade as cracked versions of popular subscription services (like Netflix or Spotify), enticing users who seek premium features without payment. Crucially, these disguised applications often function as advertised initially, building user confidence before silently deploying secondary payloads. These payloads frequently include embedded Software Development Kits (SDKs) capable of installing Remote Access Trojans (RATs), granting attackers persistent, deep-level control over the device, with the ultimate objective being the systematic draining of linked bank accounts.
The complexity of these attacks is further amplified by the proliferation of AI coding agents. These tools allow threat actors to generate complex, functional, yet malicious applications at an unprecedented velocity and scale. The barrier to entry for creating convincing imposter apps—ones that mimic legitimate system applications like Chrome, WhatsApp, or even trusted banking interfaces—has drastically lowered. In this environment, the most insidious attacks bypass technical scrutiny entirely, relying on social context. For instance, a common tactic observed in certain international markets involves distributing APKs disguised as urgent communications, such as digital wedding invitations or official-looking traffic violation notices delivered via instant messaging platforms like WhatsApp. An unsuspecting recipient, driven by social obligation or fear of authority, is persuaded to tap and install the file, granting immediate system access to the embedded payload.
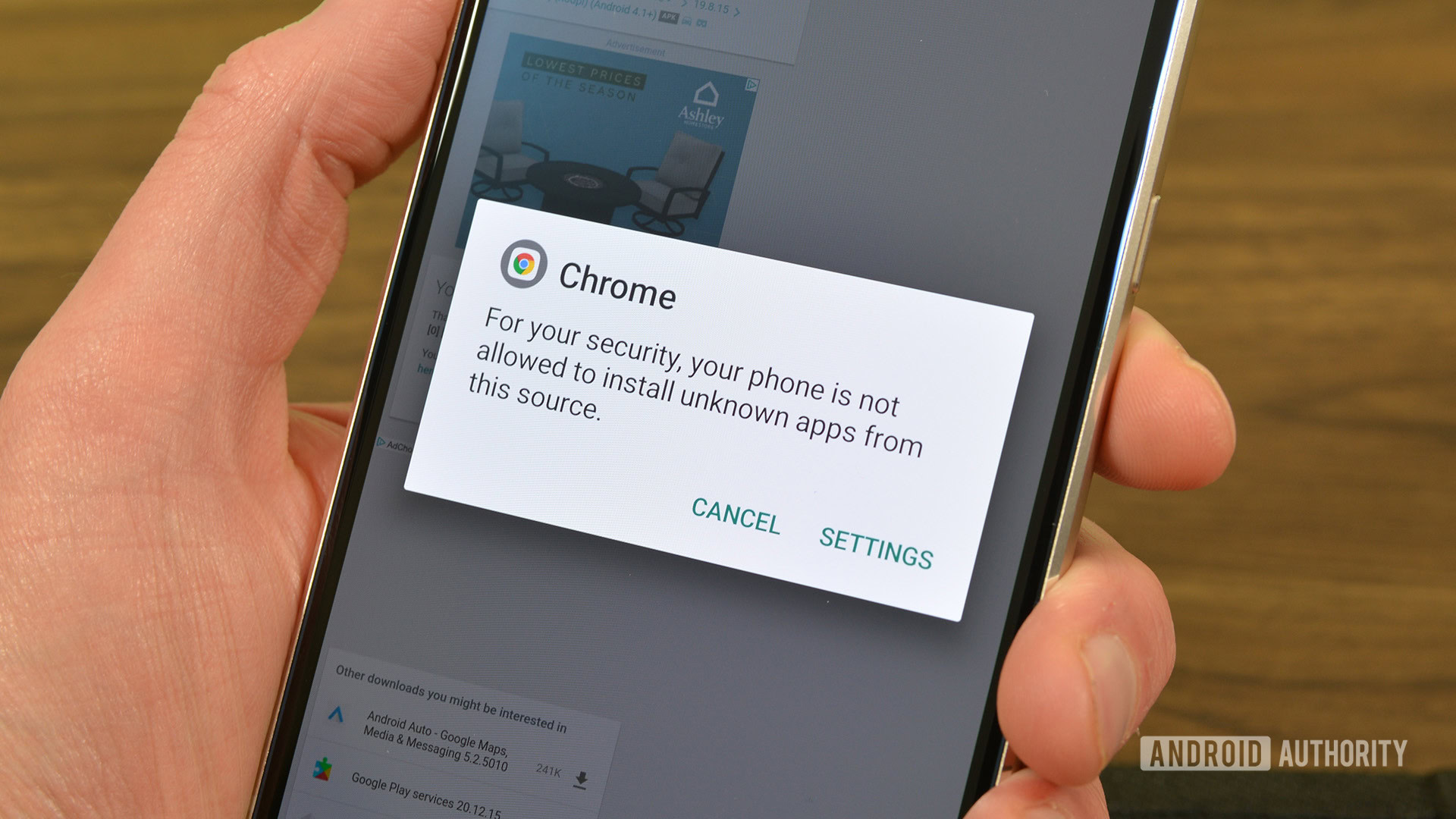
The core argument for Google’s impending procedural changes is simple: APK-based attacks have undergone a qualitative and quantitative leap, necessitating a corresponding upgrade in platform defenses. The previous "all or nothing" toggle for "Install from Unknown Sources" proved insufficient against these sophisticated, socially engineered distribution methods.
The Evolution of Google’s Stance: From Verification Mandate to High Friction
Google’s initial response to this escalating threat environment was to propose a stricter developer verification requirement for all applications distributed outside the Play Store. This approach, articulated by figures like Sameer Samat, Android Ecosystem President, aimed squarely at denying anonymity to those scaling attacks. The logic was sound: hold developers accountable through verifiable identities, thus creating a deterrent against mass malware distribution.

However, this initial proposal generated significant backlash within the established Android developer community. Concerns were raised, particularly from developers operating in regulatory gray areas or those focusing on specialized use cases. A prime example cited was console emulation software. While the emulator application itself might be entirely legitimate, its functionality often relies on the user supplying game ROMs—content whose distribution rights are often ambiguous or actively contested by publishers. Forcing these developers into a potentially cumbersome verification process felt disproportionate to the perceived risk, threatening niche but legitimate innovation.
In response to this community friction, Google moderated its approach. The requirement for mandatory developer verification for all sideloading sources has been scaled back, shifting the focus from absolute prohibition to procedural deterrence. The new strategy centers on implementing a "high-friction flow" for applications sourced from developers not registered with Google Play.
This high-friction flow is not a block; it is a barrier of inconvenience designed to force a moment of critical user reflection. For the seasoned Android power user—the individual who intentionally seeks out and understands the risks associated with obscure repositories—this added step is a minor annoyance. They are equipped to navigate warnings and understand the provenance of the files they download.
For the vast majority of Android users—those who are less technologically adept, younger users, or older relatives who rarely venture beyond trusted apps—this deliberate friction acts as a crucial safety net. The process will likely involve multiple confirmation screens, explicit risk disclosures, and perhaps even a mandatory waiting period or re-authentication step before installation proceeds. A user receiving a malicious "wedding invitation.apk" through a chat app is significantly less likely to bypass three consecutive screens detailing device risk than they were to simply toggle an existing system setting. This mechanism targets impulse and ignorance, two primary exploit vectors.
Industry Implications: Balancing Openness and Security
This strategic pivot has profound implications for the mobile operating system market. For years, the core competitive advantage of Android over iOS has been its openness, encapsulated by the ease of sideloading. Google is carefully navigating a path that preserves this philosophical differentiator while mitigating tangible security liabilities that could otherwise erode consumer trust in the platform overall.
If the Android ecosystem were to suffer a series of high-profile, widespread security compromises traceable to sideloaded malware, the long-term consequence could be a consumer migration toward perceived safety—i.e., Apple’s tightly controlled App Store. By introducing friction, Google is attempting to recalibrate the risk-reward calculation for the average user concerning third-party APKs.
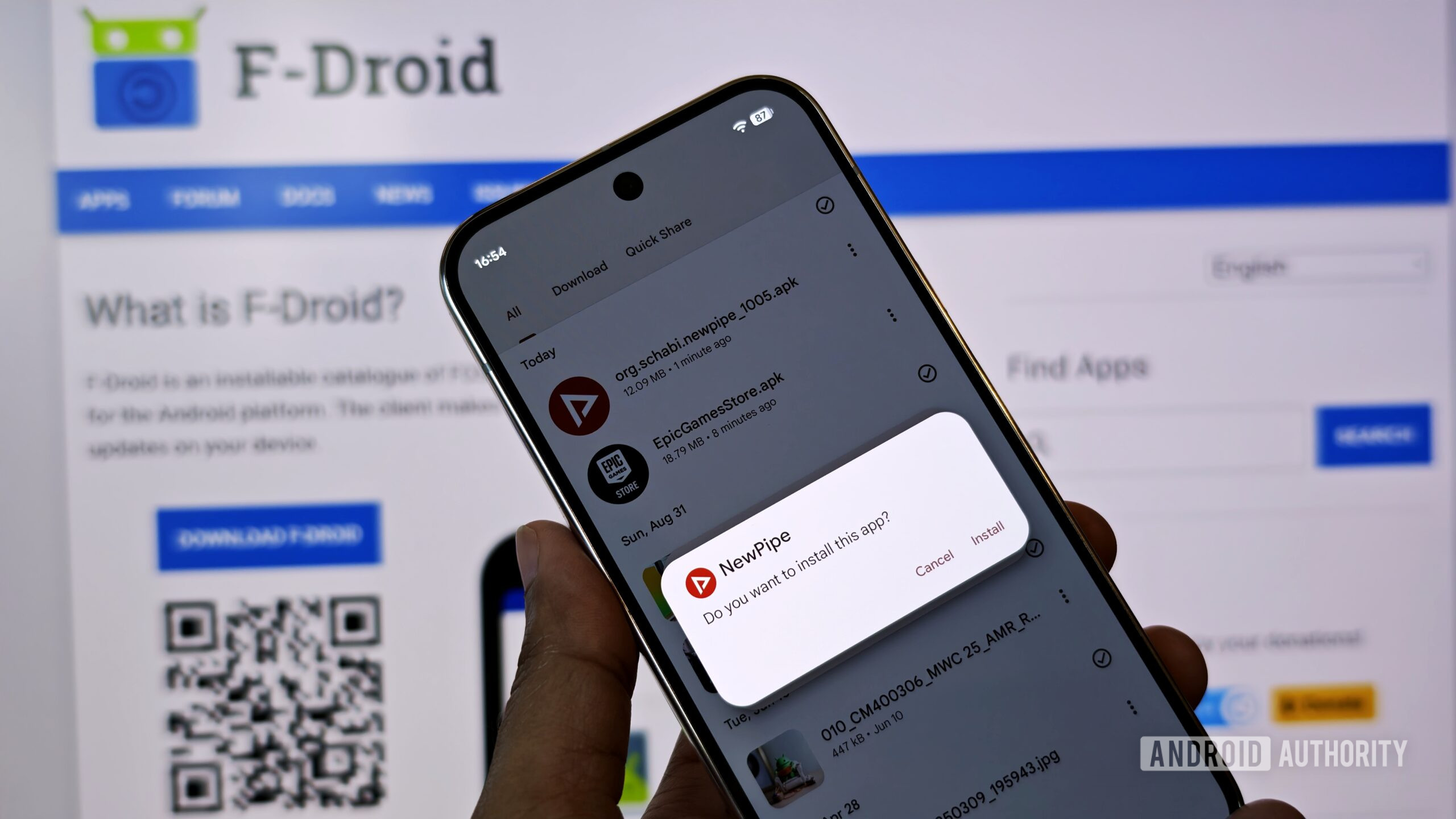
Furthermore, this move addresses the complex reality of third-party app stores. Following regulatory pressure, particularly from entities like Epic Games, Android is increasingly accommodating verified, high-quality alternative distribution channels. For stores that adhere to Google’s standards for developer identity and security checks (even if they operate outside the Play Store structure), the installation flow is expected to remain relatively seamless. This differentiates between established, vetted third-party marketplaces and ad-hoc, anonymous file sharing—a vital distinction for platform governance.
From an economic standpoint, this friction subtly reinforces the value proposition of the Google Play Store. While not blocking alternative sources, it makes the curated, verified, and instantly accessible Play Store the path of least resistance. Developers who wish to reach the broadest, least technical audience will remain incentivized to use the Play Store, while those opting for sideloading accept the implicit trade-off: greater autonomy for increased procedural hurdles.
Expert Analysis: The Necessity of Inconvenience
In cybersecurity, the concept of "security through obscurity" is largely discredited, but "security through deliberate inconvenience" holds significant weight when dealing with human error. Security experts often analyze user behavior in terms of cognitive load. Low cognitive load actions—like a single tap to install—are executed rapidly, often without reading accompanying text. High cognitive load actions—like navigating multiple warnings, reading technical jargon, and confirming intent across several prompts—force the user to pause and process the action.
This high-friction flow converts a potentially blind action into a conscious decision. While it is true that a determined, savvy user will always find a way around these hurdles, the goal is not to stop the expert; the goal is to safeguard the non-expert. The implementation is less about hardening the kernel and more about optimizing the human firewall.
The effectiveness hinges on the clarity and severity of the warning presented. If the prompt merely states, "This app is unverified," it may be ignored. If the prompt explicitly states, "Installing this application from an unregistered developer may allow the sender to monitor your SMS messages and access your banking credentials," the cognitive barrier is significantly raised. Google’s ability to dynamically assess the risk profile of the APK and tailor the warning severity will be key to the success of this layered defense.
Moreover, this approach avoids the pitfall of creating a completely closed system. True technological freedom often requires accepting some inherent risk. By maintaining the ability to sideload, Google preserves the core open-source ethos of Android. The system is evolving from being permissionless to being intentionally gated for unverified sources. This is a sophisticated middle ground that acknowledges the platform’s maturity and the maturity of its threat environment.

Future Trajectories and The Long-Term Impact
Looking ahead, the high-friction model sets a precedent for how operating systems will manage decentralized software distribution. We can anticipate an increasing reliance on reputation systems and metadata analysis rather than simple binary verification. Google is likely to leverage advanced Play Protect scanning, not just before installation, but continuously post-installation for sideloaded apps, flagging anomalous behavior even if the initial APK appeared clean.
One key trend to watch is the interoperability between developer verification levels and operating system capabilities. If a sideloaded app needs highly sensitive permissions (like accessibility services or SMS interception), the friction might increase exponentially, potentially requiring biometric authentication or even device reboots to confirm user intent at a critical juncture.
For developers who rely on sideloading for legitimate purposes—such as distributing updates to internal corporate apps, open-source projects not yet ready for mass release, or niche utilities—the emphasis will shift toward voluntarily registering with Google to achieve a "trusted but non-Play Store" status. This registration would likely confer the benefit of a lower-friction installation path, rewarding good actors with a smoother user experience while isolating truly anonymous threats.
Ultimately, Google’s calculated introduction of procedural friction is a strategic admission that the digital environment has become significantly more hostile. It is an acknowledgment that the freedom celebrated by power users must be tempered by robust, system-level warnings to protect the vast majority of users from becoming unwitting victims of highly motivated, AI-assisted cybercriminals. Android remains fundamentally open, but it is gaining necessary barricades—a pragmatic evolution ensuring the platform’s viability and security in an increasingly perilous mobile landscape. The inconvenience is a premium paid for collective digital safety.

