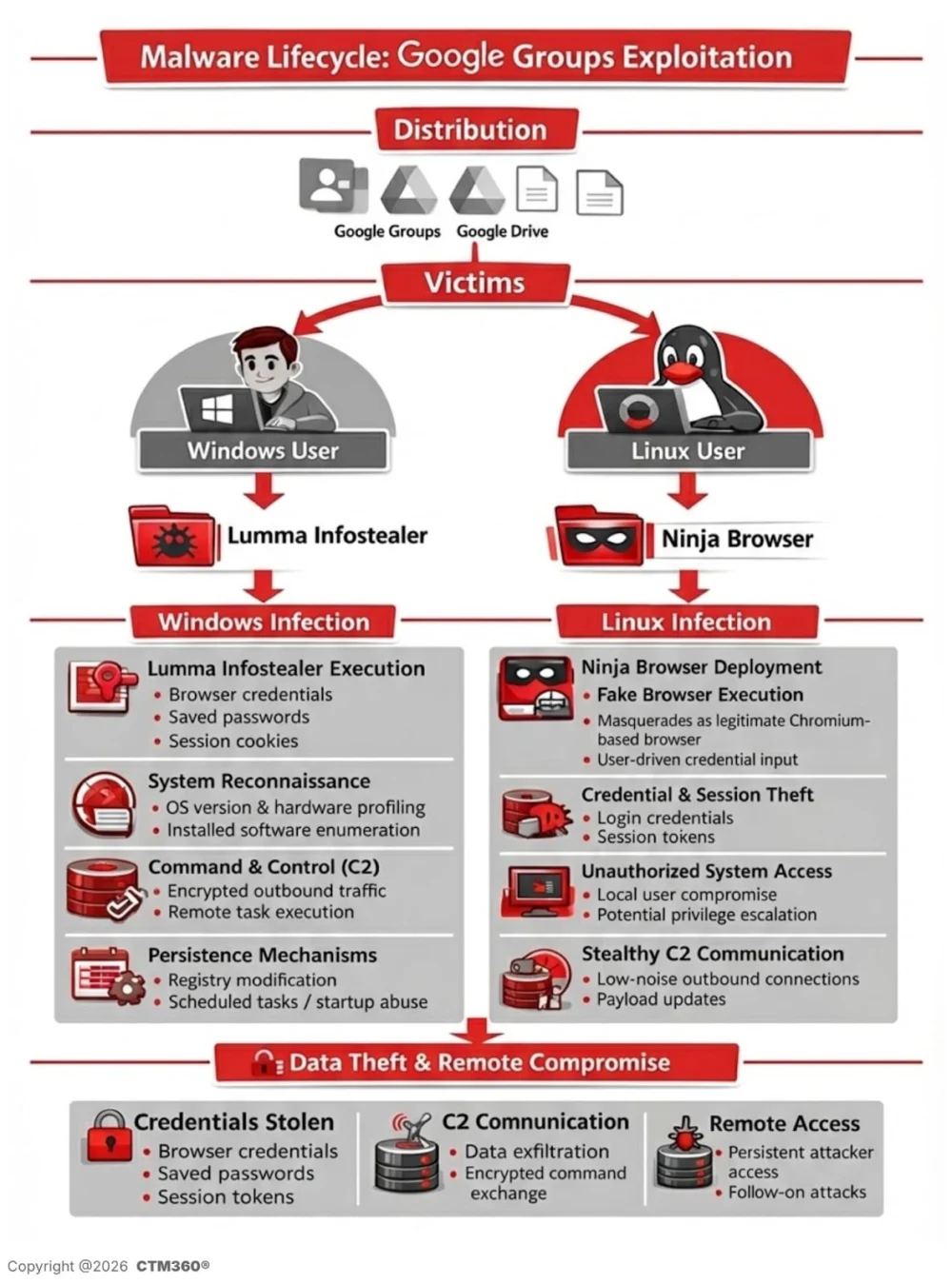
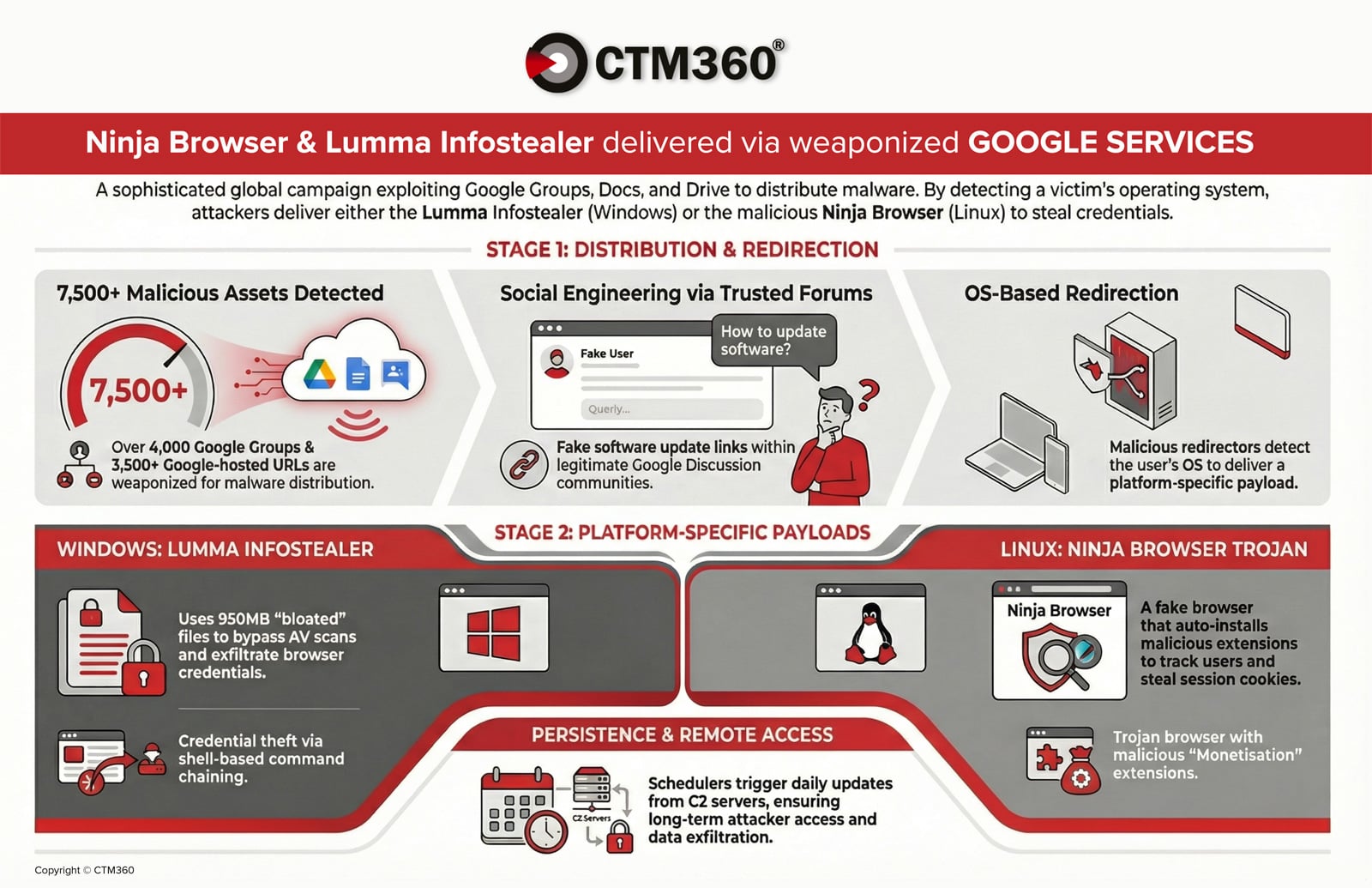
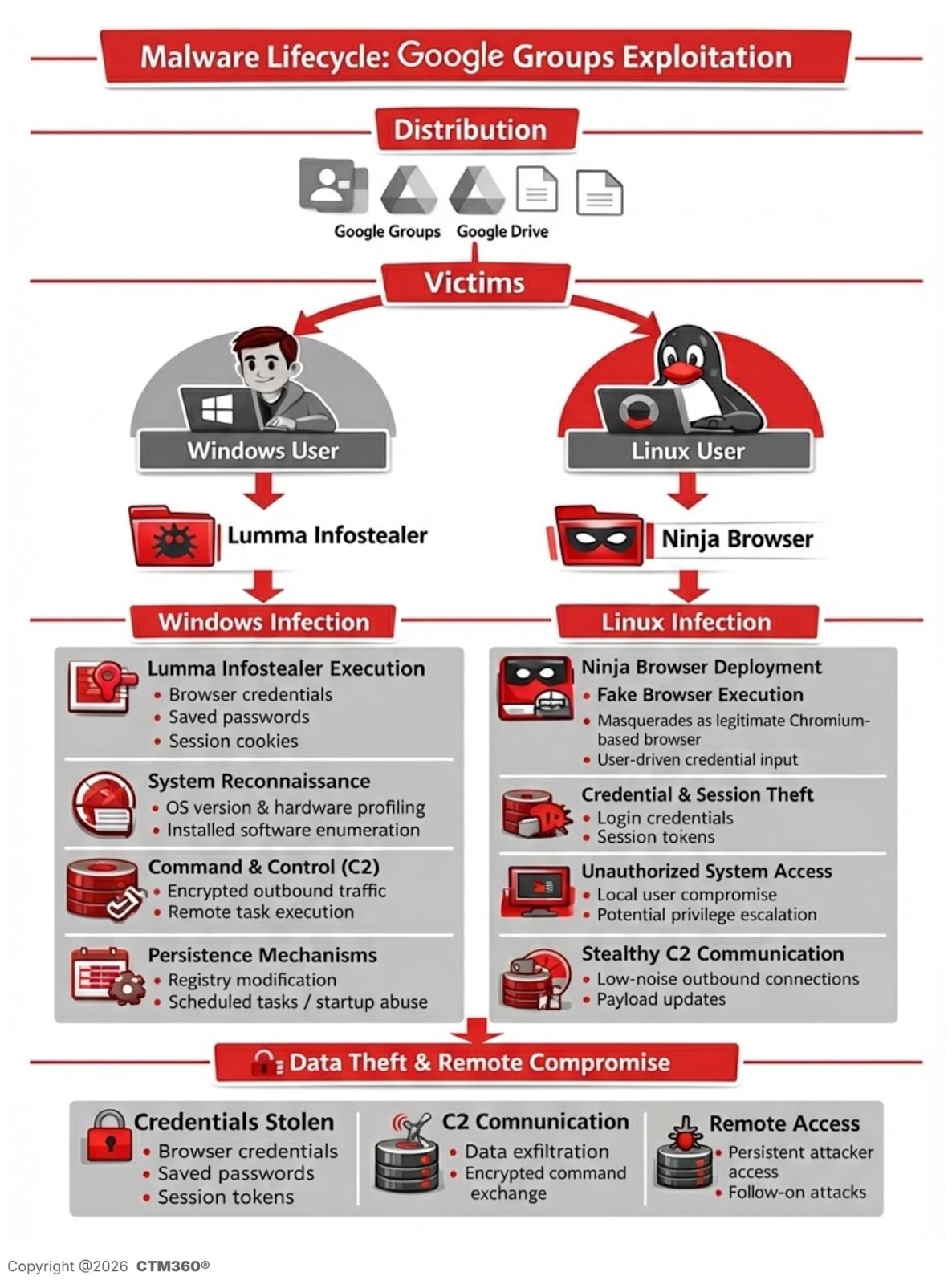
A significant, geographically widespread cyber threat operation has been uncovered, leveraging the inherent trust associated with Google’s ecosystem to distribute sophisticated malware payloads. Security researchers report the widespread abuse of over 4,000 malicious Google Groups and an estimated 3,500 Google-hosted URLs, functioning as command-and-control (C2) infrastructure and initial distribution vectors. This campaign is meticulously engineered to bypass conventional security controls by nesting its malicious components within platforms that security tools and end-users inherently trust. The dual-pronged attack primarily targets Windows and Linux environments with distinct, yet equally damaging, pieces of malware: the well-known Lumma Info-Stealer and a novel, trojanized application dubbed "Ninja Browser."
Context: The Erosion of Trust in Cloud Services
The contemporary threat landscape is characterized by attackers moving away from hosting malicious files on easily flagged, third-party domains. Instead, they increasingly pivot toward legitimate, high-reputation services—a technique known as "living off the land." Google Workspace, including Google Groups, Docs, and Drive, offers a near-perfect delivery mechanism. These services benefit from high domain reputation scores, meaning traffic originating from them is less likely to trigger email gateway warnings, web filters, or endpoint detection heuristics based solely on domain reputation. This campaign represents a chilling escalation in this trend, showing an advanced understanding of how to weaponize platform features for global reach and sustained operational security.
Anatomy of the Attack Chain: Social Engineering via Forum Infiltration
The operation commences with highly targeted social engineering orchestrated within Google Groups dedicated to specific industries or technical domains. Threat actors actively infiltrate these forums, often posing as legitimate IT professionals or system administrators. They seed discussions with seemingly authentic technical troubleshooting scenarios—covering complex topics like authentication failures, complex network stack configurations, or specific operating system patches.
The critical juncture occurs when the attacker embeds a download link within these technical threads. These links are strategically cloaked, often appearing as necessary resources for the problem being discussed, frequently formatted with organizational identifiers to enhance perceived legitimacy, such as: "Download Organization_Name for Windows 10 Update Utility."
To obfuscate the final destination and provide dynamic delivery, the links rely on a layered redirection scheme. This often involves URL shortening services or, more effectively, Google-hosted redirectors hosted via Google Docs or Drive. This redirection layer is sophisticated, capable of fingerprinting the visitor’s operating system (OS). This dynamic capability ensures that Windows users receive the Lumma payload, while Linux users are steered toward the trojanized "Ninja Browser." This precise, OS-aware payload distribution maximizes the campaign’s effectiveness across diverse corporate environments.
Windows Infection Flow: The Deceptive Delivery of Lumma Stealer
For Windows endpoints, the infection chain culminates in the delivery of a password-protected, compressed archive. This archive is hosted on an attacker-controlled file-sharing infrastructure, accessible only after the user navigates through the Google-hosted redirects.
Evasion through Oversized Packaging
A key finding by researchers involves a deliberate tactic to subvert static analysis tools. The delivered archive, upon decompression, yields a file structure vastly larger than necessary. While the actual malicious executable is a relatively small 33MB, the archive is padded extensively, pushing the total decompressed size to nearly 950MB. This "null-byte padding" technique is designed explicitly to exceed typical file-size scanning thresholds employed by many legacy antivirus solutions and static analysis sandboxes, causing the analysis engines to either time out or skip deep inspection due to resource constraints.
AutoIt Reconstruction and Credential Harvesting
Once the executable is launched, the malware employs an AutoIt-based reconstruction process. This suggests the initial executable acts as a dropper or loader, assembling the final, functional malware components in memory or staging them in temporary directories before execution. The resulting behavior unequivocally matches that of Lumma Stealer, a known commodity malware sold on underground forums, specializing in aggressive credential harvesting.
The operational profile of Lumma Stealer is comprehensive, focusing on exfiltrating a wide array of sensitive information:
- Browser Credential Theft: Targeting stored login credentials, session cookies, and autofill data from major web browsers (Chrome, Edge, Firefox, etc.).
- Cryptocurrency Wallet Seizure: Identifying and extracting private keys and wallet data from local cryptocurrency storage files.
- System Enumeration: Collecting detailed system information, including installed software, hardware configurations, and network topology data, to aid in further exploitation or resale of the compromised access.
- File System Scanning: Searching for specific document types, financial files, or proprietary data based on configured keywords.
The sustained nature of this operation is confirmed by the identification of multiple associated IP addresses and specific SHA-256 hashes tied directly to these Lumma Stealer payloads, providing concrete indicators of compromise (IOCs) for defenders.
Linux Infection Flow: The Stealthy "Ninja Browser" Trojan
The campaign demonstrates cross-platform sophistication by targeting Linux users with a bespoke threat. Instead of delivering an infostealer directly, Linux victims are directed to download a Chromium-based web browser rebranded as "Ninja Browser." This application is skillfully disguised as a privacy-centric alternative, boasting built-in anonymity features—a potent lure for security-conscious or privacy-aware technical users often found in forum environments.
Covert Extension Installation and Data Exfiltration
The veneer of privacy quickly dissolves upon deeper analysis. The trojanized browser silently installs malicious extensions without requiring explicit user consent, a severe breach of standard browser security models. The primary malicious extension, identified as "NinjaBrowserMonetisation," exhibits several concerning behaviors:
- Clipboard Monitoring: The extension monitors clipboard contents, a critical vector for intercepting copied passwords, API keys, or cryptocurrency wallet addresses when users paste sensitive data.
- Form Grabbing: It actively intercepts data submitted through web forms, meaning login credentials or sensitive inputs are captured before encryption can take full effect.
- Background Data Transmission: It periodically transmits captured data to external command-and-control servers.
The code within this extension is heavily obfuscated, utilizing complex encoding schemes, including XOR and variations resembling Base56, designed to thwart automated JavaScript analysis tools. While not all embedded communication domains appear active immediately, the comprehensive infrastructure strongly suggests a staged deployment capability, allowing the attackers to activate secondary communication channels or deploy entirely new payloads in the future.
Establishing Persistent Footholds
Beyond the immediate data theft via the extension, the Ninja Browser installation incorporates robust persistence mechanisms crucial for long-term access. Researchers documented the creation of scheduled tasks within the Linux environment configured to execute stealthily at regular intervals. These tasks serve dual purposes: to maintain an active communication channel with the C2 infrastructure and to potentially re-inject the malicious extension if it is manually removed by an administrator.
Further evidence of malicious intent includes the forced modification of browser settings. The browser defaults to a Russian-based search engine named "X-Finder" and further redirects user queries to another suspicious, AI-themed search portal. This redirection not only serves the threat actors’ immediate objectives (e.g., collecting search query data or ad revenue) but also demonstrates control over the user’s primary browsing environment.
Campaign Infrastructure and Defense Implications
The sheer scale of this operation—thousands of groups and URLs—points toward a well-resourced threat actor or a highly automated infrastructure setup. The identified indicators of compromise (IOCs) reveal a complex network:
- C2 Domains: A list of domains, many utilizing recent registrations, are tied to credential exfiltration and payload staging.
- Associated IPs: A pool of IP addresses, often shared across different stages of the attack chain (redirection and final C2), provides crucial anchors for network defense teams.
The primary risk to organizations stems directly from the method of delivery. Traditional security frameworks often rely on perimeter defenses that inspect inbound files or scrutinize known-bad external domains. By using Google Groups and Google Drive as the initial staging ground, the campaign effectively neutralizes these initial trust barriers. Employees are conditioned to trust links from established platforms, lowering their guard against sophisticated social engineering cues embedded within contextually relevant technical discussions.
For Lumma Stealer, the risk is immediate data loss and session hijacking. For Ninja Browser, the risk is insidious: a long-term compromise of Linux workstations, potential access to corporate source code repositories (if developers use these machines), and the theft of SSH keys or other configuration secrets stored locally.
Expert Analysis and Future Trajectory
This campaign underscores a critical pivot in cyber adversary methodology: the weaponization of Software-as-a-Service (SaaS) platforms. Attackers are no longer just exploiting software vulnerabilities; they are exploiting trust models. The success of this operation relies less on zero-day exploits and more on meticulous social engineering within trusted communication channels.
From an industry perspective, this necessitates a fundamental shift in security posture. Relying solely on domain reputation filtering for all external links is obsolete. Security teams must integrate advanced behavioral analysis and context-aware link verification, especially for files downloaded following interaction within community forums or collaboration platforms.
The future impact suggests that we will see an increase in multi-platform operations targeting niche operating systems (like Linux desktops) where traditional endpoint protection might be less robust or less frequently updated compared to Windows installations. Furthermore, the use of commodity malware like Lumma Stealer suggests that the operators are focused on high-volume, low-effort credential harvesting, potentially acting as brokers for initial access brokers (IABs) who then sell established network access to more advanced persistent threat (APT) groups.
Defensive Strategies for Mitigation
To counter this evolving threat vector, organizations must implement a layered defense strategy focusing on user education, technological hardening, and rigorous monitoring:
- Elevated User Vigilance: Mandate specialized training focusing on social engineering within trusted platforms. Users must be explicitly warned that links embedded in Google Groups, even those appearing technical, require external validation before download or execution.
- Endpoint Hardening for Windows: Deploy advanced Endpoint Detection and Response (EDR) solutions capable of detecting file padding techniques and suspicious AutoIt execution patterns, regardless of the host file’s perceived origin. Application whitelisting should be strictly enforced to prevent unauthorized executables from running, even if downloaded.
- Linux Workstation Integrity: Treat Linux machines with the same scrutiny as Windows endpoints. Ensure robust configuration management tools monitor for unauthorized scheduled tasks and enforce strict policies regarding the installation of non-approved software, particularly browsers or system utilities sourced outside official repositories.
- Network Visibility and Monitoring: Implement DNS sinkholing and network traffic inspection capable of flagging communication attempts to the identified C2 domains and suspicious IP addresses associated with the campaign, providing a last line of defense even if the endpoint is compromised.
- SaaS Policy Review: Conduct a thorough review of internal policies regarding the use of Google Workspace for non-sanctioned activities or the sharing of external files through Docs/Drive links, ensuring clear boundaries are established to prevent internal abuse of these trusted services.
The findings detailed in the comprehensive threat intelligence report serve as a stark reminder that the perimeter is no longer the network edge; it resides at the point of user interaction with trusted cloud services. Continuous threat intelligence consumption and adaptation of security controls remain paramount to navigating this environment effectively.