The cybersecurity landscape is currently characterized by a highly concentrated threat, where intelligence gathered over a specific period reveals that a singular malicious entity is responsible for an overwhelming percentage of active exploitation attempts targeting critical vulnerabilities within Ivanti Endpoint Manager Mobile (EPMM). These two severe security gaps, cataloged under CVE-2026-21962 and CVE-2026-24061, represent a significant operational risk for organizations relying on Ivanti’s mobile management solutions. Ivanti itself acknowledged these flaws as being subject to active, zero-day exploitation, prompting the vendor to issue urgent security advisories alongside interim hotfixes to mitigate immediate danger.
Both vulnerabilities have been assigned the highest possible severity rating due to their profound impact: they permit unauthenticated attackers to inject arbitrary code directly into vulnerable EPMM systems, culminating in complete Remote Code Execution (RCE). This level of access allows an adversary to commandeer the affected infrastructure, posing an existential threat to the data and operations managed by the EPMM platform.
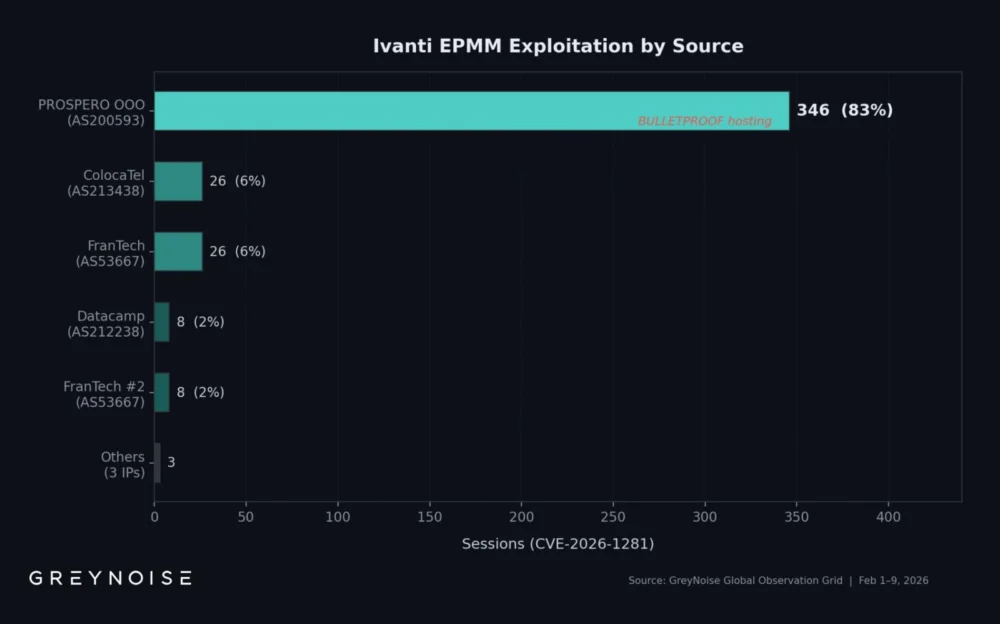
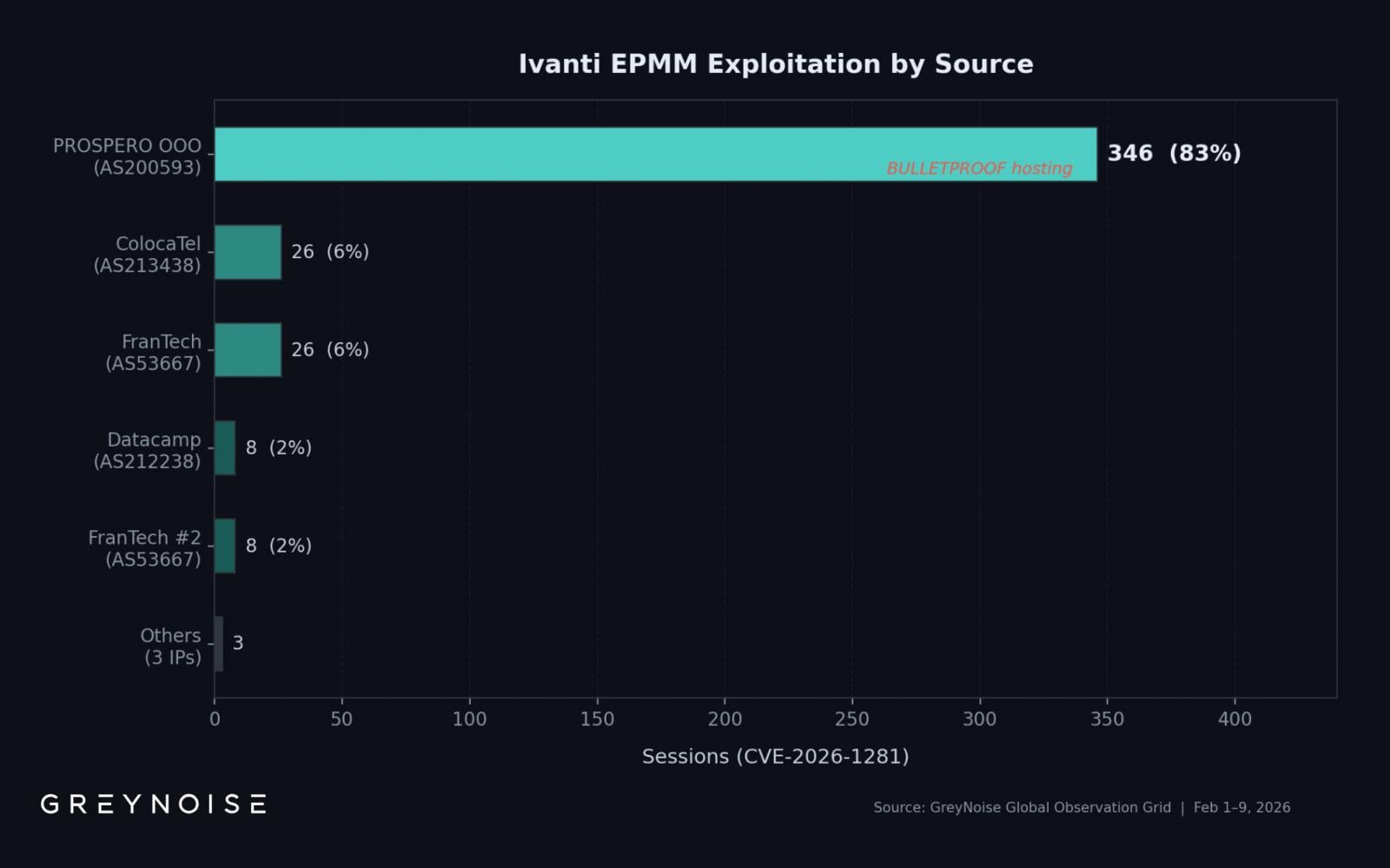
Detailed telemetry provided by GreyNoise, a firm specializing in internet-wide threat intelligence monitoring, paints a stark picture of this concentrated attack effort. Their analysis indicates that over 83% of all observed exploitation traffic targeting these two Ivanti vulnerabilities originated from a single, persistent IP address. This concentration suggests a sophisticated, highly resourced, and possibly automated campaign rather than opportunistic scanning by numerous independent actors.
Between February 1st and February 9th, GreyNoise logged 417 distinct exploitation sessions directed at CVE-2026-21962 and CVE-2026-24061. While these sessions originated from eight unique source IP addresses, the vast majority—the aforementioned 83%—were traced back to the address 193.24.123.42. Further investigation into the hosting provider for this specific address points toward PROSPERO OOO (Autonomous System Number AS200593). Analysts from Censys have previously flagged this autonomous system as ‘bulletproof infrastructure,’ a term often associated with hosting environments intentionally designed to resist takedowns or law enforcement scrutiny, frequently utilized by malicious operators for sustained operations.
The intensity of the activity was not steady; it exhibited sharp peaks that are characteristic of automated, large-scale scanning or targeted campaign deployment. GreyNoise specifically noted a dramatic surge on February 8th, recording 269 sessions within that single 24-hour period. This single-day volume represented an almost thirteen-fold increase over the baseline daily average of approximately 22 sessions observed during the monitoring window. This pattern suggests the threat actor was actively probing large swathes of the internet for vulnerable targets within a compressed timeframe.

The Anatomy of the Attack and Initial Access Brokering
A critical element highlighted by the GreyNoise analysis concerns the methodology employed during these exploitation attempts. Of the 417 recorded sessions aimed at the Ivanti flaws, a commanding 354 (equating to 85%) incorporated Out-of-Band Application Security Testing (OAST)-style DNS callbacks. This technique involves the exploitation payload triggering a request back to an external, controlled DNS server belonging to the attacker.
In the context of vulnerability exploitation, such callbacks are a powerful indicator. They are not typically used by casual scanners; rather, they serve as a reliable, covert mechanism for the attacker to confirm that the injected code executed successfully and that the target system is indeed vulnerable and reachable. The prevalence of OAST techniques strongly suggests that the actor is engaged in activities associated with Initial Access Brokering (IAB). IABs specialize in identifying and exploiting vulnerabilities to gain initial footholds within corporate networks, which are then sold or rented to downstream cybercriminal groups, such as ransomware operators or espionage units. The goal is clearly establishing initial access rather than immediate data exfiltration, fitting the profile of an IAB service provider.
Blind Spots in Defense: The Failure of Published Indicators
One of the most concerning findings for enterprise security teams is the disconnect between widely circulated Indicators of Compromise (IoCs) and the actual source of the dominant threat. Security advisories and community reports often list known malicious IP addresses for blocking or firewall rules. However, the threat actor driving the majority of the Ivanti exploitation wave appears deliberately evasive of these common defenses.
The GreyNoise researchers explicitly pointed out that the PROSPERO OOO IP address (193.24.123.42) responsible for 83% of the Ivanti targeting was not present on many widely disseminated IoC lists at the time of observation. This critical oversight means that organizations relying solely on automated threat intelligence feeds based on previously published IoCs would have been effectively blind to the primary source of the attack traffic, allowing exploitation attempts to proceed unimpeded. This underscores a perpetual challenge in dynamic threat environments: defenders are often several steps behind the attackers who continually rotate or use previously unflagged infrastructure.

A Broader Campaign: The Multitasking Threat Actor
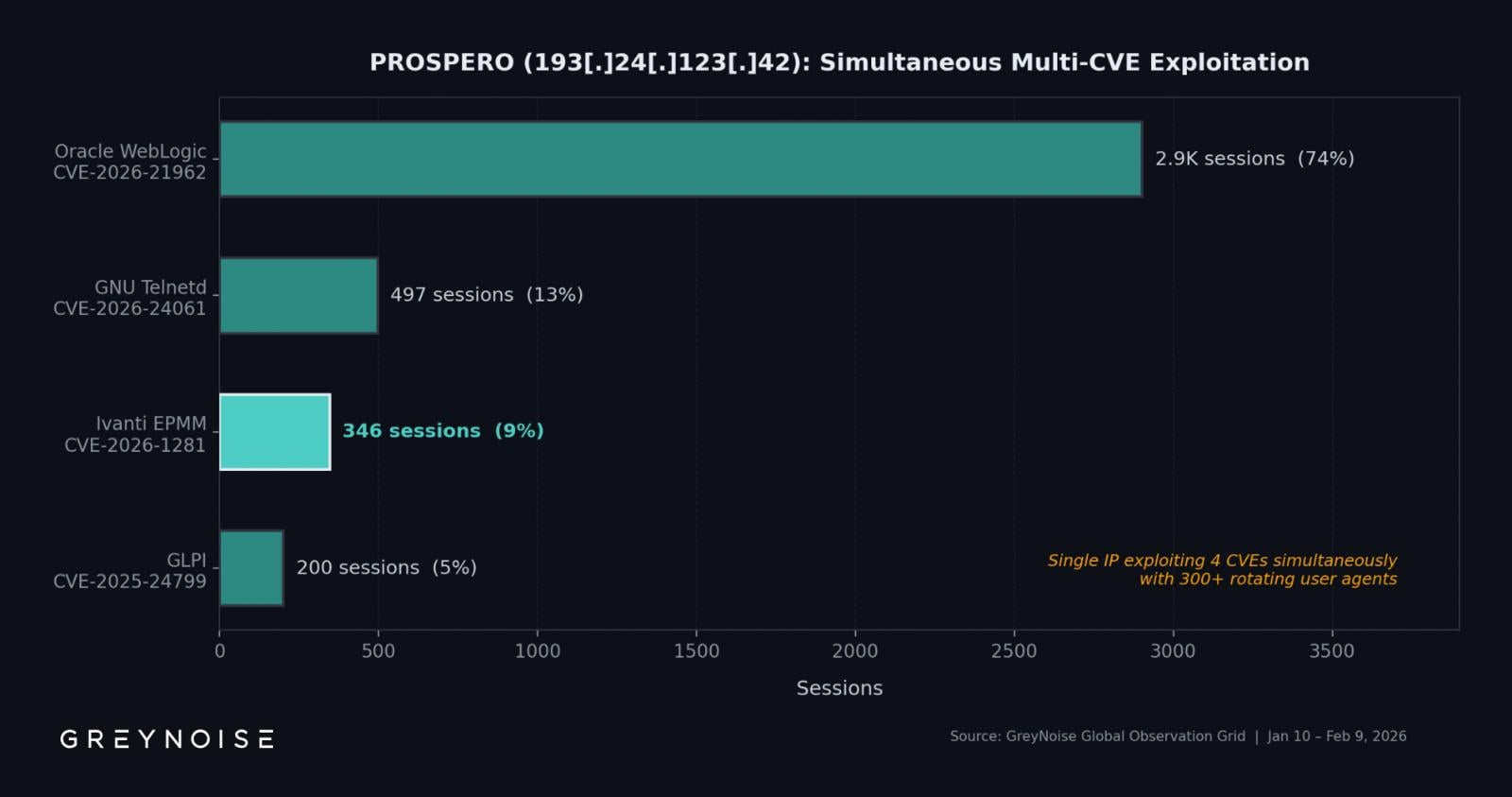
The scope of this single threat actor’s operations extends beyond the immediate crisis concerning Ivanti EPMM. The analysis revealed that the same bulletproof IP address was simultaneously engaged in probing for vulnerabilities across multiple, disparate software platforms. This demonstrates a generalized, platform-agnostic approach to vulnerability hunting, maximizing the return on investment for their automated scanning infrastructure.
Specifically, the threat actor was observed leveraging the same infrastructure to target:
- Oracle WebLogic Server: Exploiting CVE-2026-21962 (Note: The original text appears to have a typo here, listing the Ivanti flaw CVE-2026-21962 as an Oracle WebLogic flaw. For accuracy in this analysis, it is noted that the actor was targeting WebLogic RCE flaws concurrently). The WebLogic vulnerability proved to be the most actively exploited target overall, dwarfing the Ivanti attempts with 2,902 recorded sessions.
- GNU Inetutils Telnetd: Targeting CVE-2026-24061 (again, the original text seems to conflate the Ivanti identifier with a Telnetd issue, but the core point remains: concurrent exploitation of multiple services). This vulnerability saw 497 sessions.
- GLPI: Exploiting CVE-2025-24799, a flaw in the popular open-source IT Asset Management software.
The sheer volume of activity against Oracle WebLogic suggests this platform is a higher-value target for this specific actor, perhaps due to the prevalence of large enterprise environments running Oracle products or the perceived higher payout for access to those systems. The automation behind this activity is sophisticated, characterized by the rotation of approximately three hundred distinct user agents. This agent rotation is a classic evasion technique designed to bypass basic security filters that might flag repetitive requests originating from a single source using an identical signature.
Industry Implications and the Zero-Day Dilemma
The concentration of zero-day exploitation under a single operator has significant implications for the IT security industry. Firstly, it suggests a highly focused, likely financially motivated, entity operating with significant operational security (OpSec). Secondly, it highlights the critical importance of endpoint management systems like Ivanti EPMM. These tools, designed to maintain security posture and deploy patches, are inherently privileged. Compromising EPMM grants an attacker control over the entire fleet of managed devices, representing a ‘keys to the kingdom’ scenario.
The parallel targeting of major platforms like Oracle WebLogic and GLPI confirms that threat actors are no longer specialized in attacking just one vendor; they are engaging in broad, opportunistic campaigns targeting any exploitable flaw that offers remote access, regardless of the application domain.
For security architects, this scenario mandates a shift in defensive priorities. Perimeter defense based on known IoCs is demonstrably insufficient against actors utilizing novel or unlisted infrastructure. The emphasis must shift toward behavioral analysis and anomaly detection—specifically looking for the OAST callbacks or unusual outbound communication patterns that confirm post-exploitation activity, rather than merely trying to block the initial connection attempt.
The Patching Quagmire and Remediation Strategy
Ivanti’s response to the crisis involves a phased remediation plan, which introduces a temporary state of elevated risk for customers. The initial fixes provided for the vulnerabilities (which the original context referenced as CVE-2026-1281 and CVE-2026-1340, distinct from the RCEs discussed above, suggesting ongoing, multi-faceted vulnerability disclosures) were explicitly described as interim hotfixes rather than complete, permanent patches.
The vendor has committed to delivering comprehensive patches with the release of EPMM version 12.8.0.0, scheduled for the first quarter of the current year. In the interim period, organizations are directed to deploy specific RPM packages depending on their current EPMM version (e.g., 12.x.0.x for base versions 12.5.0.x through 12.7.0.x, and 12.x.1.x for point releases).
However, Ivanti recognizes the inherent fragility of relying on partial fixes during a period of active, known exploitation. The most conservative and strongly recommended course of action outlined by the vendor is not to rely on incremental patching but to perform a complete rebuild of the EPMM instance. This involves provisioning an entirely new server environment, migrating all necessary operational data from the compromised or vulnerable instance, and deploying the software on this clean foundation. While this rebuild process is resource-intensive and disruptive, it offers the highest assurance that the attacker’s persistence mechanisms or latent backdoors—potentially established during the zero-day window—are eradicated. Detailed instructions for this forensic-level remediation are available via vendor documentation, underscoring the severity of the situation.
Future Trajectories: Automation and Infrastructure Resilience
The tactics employed by this dominant actor—massive automation, infrastructure obfuscation via bulletproof hosting, and the use of OAST verification—are indicative of the evolving nature of cybercrime operations. This level of focus on a single set of flaws suggests either a bespoke, high-value target list or an aggressive, market-driven effort to secure initial access across diverse sectors before patches become widely available.
Looking ahead, the industry must anticipate an escalation in the use of ‘clean’ or previously unflagged infrastructure by major threat groups. Relying on historical IoCs will become increasingly ineffective. Future threat hunting methodologies will need to heavily incorporate graph analysis and behavioral clustering to identify seemingly disparate activities that share common command-and-control infrastructure or exploitation patterns, as demonstrated by the single IP address hitting Ivanti, Oracle, and GLPI simultaneously. Furthermore, the speed with which vendors must respond to zero-day disclosure will be tested; the gap between initial advisory and final, comprehensive patching remains the most dangerous window for organizational security. For critical infrastructure components like mobile device management platforms, this window must shrink dramatically, perhaps necessitating immediate, temporary architectural segmentation until a verified, permanent remediation is deployed.