A sophisticated, sustained cyber-espionage campaign, attributed with high confidence to North Korean threat actors, is systematically exploiting the software development ecosystem by embedding malicious payloads within seemingly legitimate coding challenges presented to job applicants. This operation, cataloged under the designation ‘Graphalgo’ by security researchers at ReversingLabs, represents a chilling evolution in supply-chain attacks, shifting the vector from broad infrastructure compromises to highly targeted social engineering aimed directly at individual developers. The campaign, active since at least May 2025, focuses specifically on engineers proficient in JavaScript and Python, luring them with the promise of employment at fictitious entities operating within the lucrative blockchain and cryptocurrency trading sectors.
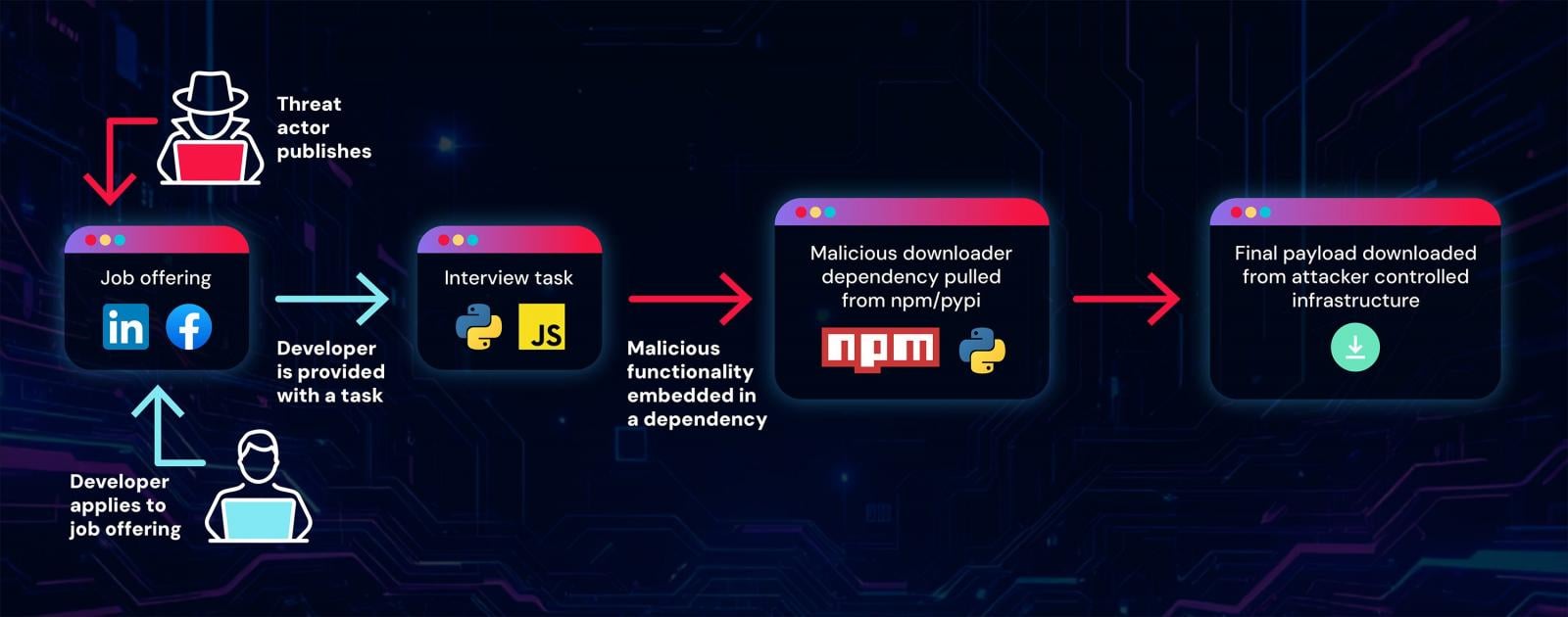
The operational methodology hinges on the trust inherent in the developer hiring pipeline. Threat actors meticulously construct fake corporate personas and post enticing job openings across professional networking sites like LinkedIn, as well as community platforms such as Facebook and Reddit. Once a developer engages with the recruitment process, they are inevitably presented with a technical screening task—a mandatory coding exercise designed to evaluate their proficiency. Crucially, these tasks are not self-contained; they require the developer to execute, debug, or integrate a provided project framework. This requirement serves as the Trojan horse. The core objective is not to assess skill, but to coerce the applicant into executing code that pulls down a malicious dependency from established, trusted public repositories.
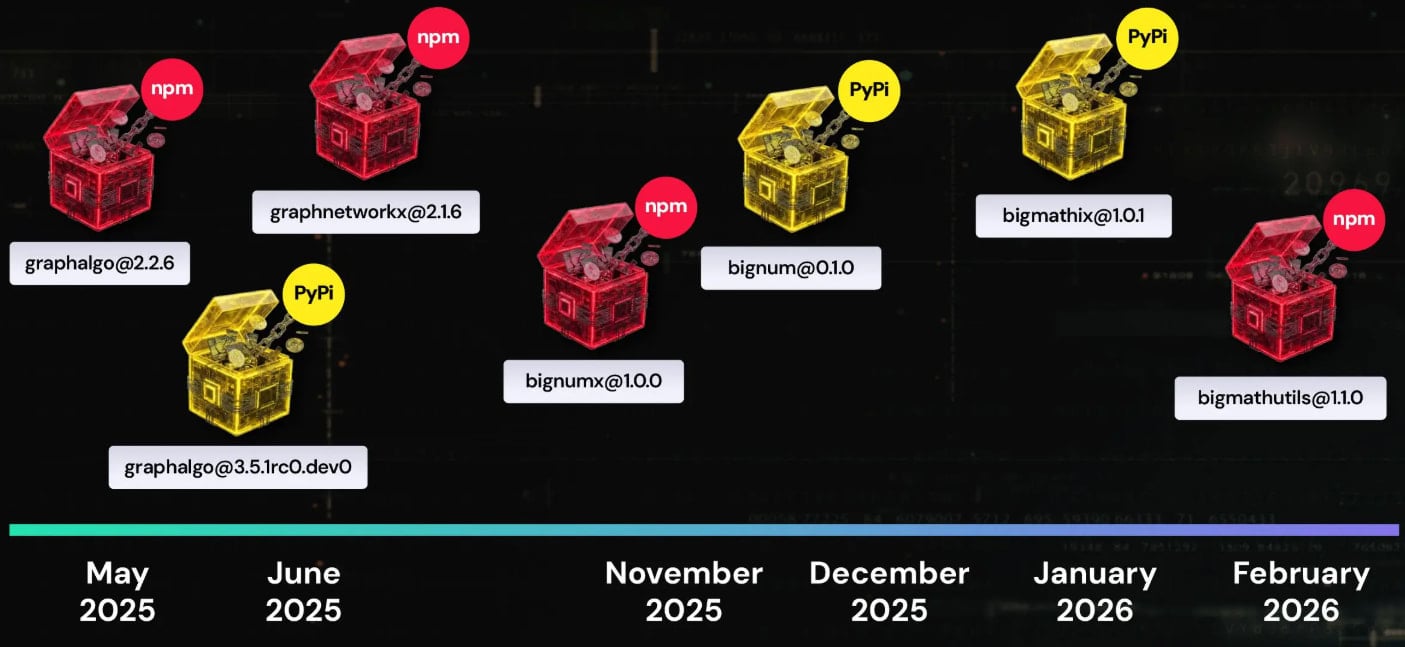
The reliance on the Node Package Manager (npm) for JavaScript and the Python Package Index (PyPI) for Python is a deliberate and effective evasion technique. By hosting their nefarious components on these canonical registries, the attackers camouflage the malware within the standard tooling developers use daily. Researchers have cataloged an extensive footprint for this operation, identifying no fewer than 192 distinct malicious packages linked to the Graphalgo campaign.

The modular architecture of the attack framework is a key indicator of a well-resourced and adaptable threat group. This modularity ensures operational resilience; even if one line of attack or a specific set of malicious packages is discovered and scrubbed from the registries, the actors can swiftly pivot and relaunch the campaign using alternate package names or infrastructure. This adaptability is crucial for state-sponsored operations that often maintain long-term objectives, such as intellectual property theft or espionage.
The researchers detail how easily these initial infection vectors are prepared. An attacker simply takes a functional, often minimal, open-source project template and injects a malicious dependency hook. When the unsuspecting developer runs the "test" or "setup" script as part of the interview process, the system unknowingly pulls the malicious package from npm or PyPi. This package, functioning as a sophisticated downloader, then establishes a persistent foothold.
A case study presented by ReversingLabs highlights the insidious nature of the package lifecycle management. The package named bigmathutils, for instance, maintained a clean public profile, accruing approximately 10,000 legitimate downloads. However, its update to version 1.1.0 suddenly introduced the malicious payloads. Following this brief period of infection, the package was swiftly yanked from the registry and marked as deprecated—a classic tactic of obscuration designed to minimize forensic exposure after the initial objective has been met or the payload has been successfully deployed on target machines.
The campaign’s nomenclature, ‘Graphalgo,’ originates from an earlier phase where the malicious packages frequently featured the string "graph" in their names, often impersonating legitimate, popular libraries like graphlib. However, analysis indicates a tactical shift commencing around December 2025, where the naming convention pivoted towards packages containing the string "big," exemplified by the aforementioned bigmathutils. While ReversingLabs has tracked the infrastructure for these later-stage packages, the precise social engineering front—the specific fake job postings—associated with this "big" iteration remains less clearly mapped, suggesting the actors may be testing parallel or automated recruitment funnels.

The compromise vector leverages GitHub Organizations as a façade. The actual Git repositories associated with the fake jobs often appear pristine, containing no overtly malicious code. The true threat is delivered through the dependency resolution process inherent in modern software development workflows. When a developer pulls the project and executes the installation commands (e.g., npm install or pip install), the build process innocuously fetches the compromised package from the public registry, effectively bypassing static code analysis performed solely on the initial repository clone.
The success of this scheme is evidenced by the fact that researchers were able to identify and contact several developers who had unknowingly fallen victim to the elaborate recruitment trap. These individuals, seeking employment, had inadvertently installed the attacker’s Remote Access Trojan (RAT) onto their development workstations.
The deployed RAT is a multi-functional espionage tool designed for persistence and data exfiltration. Its capabilities include listing active processes, enabling the remote execution of arbitrary system commands dictated by a Command and Control (C2) server, and the capacity to systematically exfiltrate sensitive files or download further stages of malware.
A particularly telling indicator of the campaign’s ultimate financial motivation is the RAT’s specific check for the presence of the MetaMask cryptocurrency wallet browser extension. Detecting MetaMask strongly suggests the threat actors are primarily targeting developers with access to, or knowledge of, sensitive cryptocurrency wallets, private keys, or proprietary trading algorithms. This aligns perfectly with the campaign’s stated focus on the blockchain sector.
Furthermore, the RAT exhibits robust defensive measures against forensic analysis. Its C2 communications are secured with token protection mechanisms, designed to prevent unauthorized parties—such as security researchers or network defenders—from intercepting or analyzing the command traffic. This use of tokenized encryption is a signature characteristic frequently observed in previous operations attributed to North Korean state-sponsored entities.
The observed breadth of the RAT implementation, spanning multiple scripting languages including JavaScript, Python, and even Visual Basic Script (VBS), demonstrates a strategic effort to maximize compatibility across diverse development environments and operating systems, ensuring that no segment of their targeted demographic is overlooked.
Security researchers attribute the Graphalgo campaign to the Lazarus Group, a notorious advanced persistent threat (APT) syndicate operating under the direction of the Democratic People’s Republic of Korea (DPRK). This attribution carries a medium-to-high confidence rating, based on several converging factors. The tactical choice of using technical interviews as a direct infection vector is consistent with Lazarus’ history of exploiting developer tools and platforms. The intense focus on cryptocurrency targets further mirrors the DPRK’s well-documented, state-sponsored drive to illicitly acquire digital assets to fund national initiatives.
Adding weight to this determination is the observed patience encoded within the malware deployment. The delayed activation of malicious code within the compromised packages—a common characteristic noted by Lazarus in past operations—suggests a calculated approach designed to allow the malware to lie dormant until the victim is settled into a stable work environment, thereby increasing the likelihood of long-term data harvesting. Moreover, metadata analysis of Git commits associated with the development of these malicious components often reflects the GMT +9 time zone, which precisely corresponds to North Korea Standard Time (KST).
Industry Implications and Expert Analysis
The Graphalgo operation signifies a critical inflection point in software supply-chain security. Historically, supply-chain attacks focused on compromising major software vendors or popular libraries to achieve widespread, indiscriminate impact. This new approach weaponizes the hiring process itself, turning a routine professional activity into a direct pathway for espionage. For technology companies, this demands a radical re-evaluation of vetting procedures. Trusting an applicant’s local machine configuration or the integrity of code executed during a technical interview is now a demonstrable security liability.
From an industry perspective, the targeting of blockchain and crypto developers is strategic. These individuals possess specialized knowledge and often handle high-value digital assets or proprietary trading logic. Compromising one such developer can yield exponentially greater returns than compromising a generalist software engineer. The sheer volume of packages identified (192) suggests that the attackers are using an automated, perhaps even AI-assisted, process to rapidly generate and deploy these fake dependencies, overwhelming traditional manual review processes.
The use of public registries like npm and PyPI as the final delivery mechanism confirms that these repositories, despite extensive security enhancements, remain prime targets for infiltration. Developers must understand that dependency resolution is not just a function of convenience; it is a high-risk execution pathway. The threat actors exploit the implicit trust developers place in packages downloaded via official channels, even when those packages are introduced via a seemingly benign, external project setup script.
Future Impact and Evolving Defenses
The future trajectory of this type of attack suggests an increasing sophistication in social engineering coupled with deeper integration into CI/CD pipelines, should the attackers pivot from individual exploitation to enterprise compromise. As remote work and technical assessments remain the norm, the attack surface presented by coding challenges will only widen.
We anticipate seeing adversaries leveraging more advanced techniques to mask dependency calls, potentially utilizing obfuscated execution environments or exploiting weaknesses in containerization setups that applicants might use for their testing environments. Furthermore, as AI-powered development tools become more ubiquitous, threat actors may begin targeting the AI models themselves, perhaps by injecting subtly biased or malicious training data through similar poisoned projects.
For developers, the response must be rigorous. ReversingLabs’ advice to affected parties—rotating all credentials and reinstalling the operating system—underscores the severity of RAT infections. Proactive defense requires adopting a principle of least privilege even in development environments. Developers should utilize isolated, ephemeral testing environments (like disposable containers or virtual machines) for executing untrusted code, particularly code received from external sources, regardless of the context, be it a job interview or a collaboration request. Furthermore, organizations must invest in automated software composition analysis (SCA) tools that continuously monitor dependencies being pulled into development environments, looking beyond simple package names to behavioral anomalies and source provenance. The era where a coding challenge was purely a technical evaluation is over; it must now be treated as an active security audit.

