The persistent threat landscape targeting the global digital asset economy has recently been illuminated by the activities of a highly specialized North Korean cyber espionage group, identified by security researchers as UNC1069. This actor, under continuous surveillance since 2018, has demonstrated a significant strategic pivot, integrating cutting-edge social engineering tactics—most notably the use of artificial intelligence-generated video content—to deploy a diverse arsenal of malware specifically tailored for Apple’s macOS ecosystem, alongside Windows counterparts, all aimed at illicit financial gain within the cryptocurrency sector.
The recent forensic analysis, conducted during an incident response engagement at a fintech organization, uncovered an alarming complexity in the threat actor’s operational methodology. The investigation revealed not just a single piece of malicious software, but a staggering array of seven distinct malware families deployed against a single target on macOS. This volume and diversity suggest an aggressive, high-value intelligence-gathering and exfiltration effort, far exceeding standard opportunistic attacks. The primary motivation underpinning UNC1069’s activities remains unequivocally financial, consistent with the broader objectives of many state-sponsored North Korean hacking units dedicated to generating hard currency for the regime.
The Anatomy of a Highly Targeted Social Engineering Attack
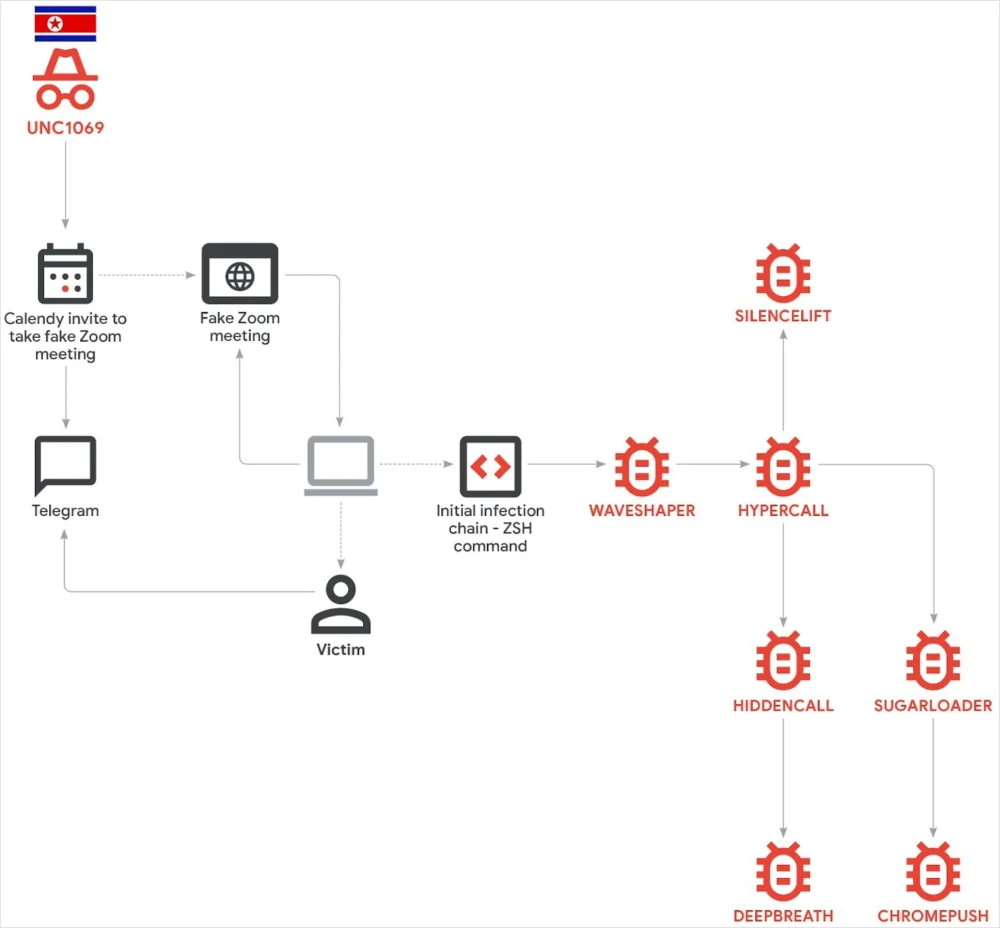
The initial infiltration vector utilized by UNC1069 exemplifies the evolution of digital deception. The operation commenced not with a phishing email, but through the Telegram messaging platform, leveraging a compromised account belonging to an executive within a target cryptocurrency firm. This established an immediate, trusted channel for communication.
Following the establishment of rapport—a hallmark of sophisticated human engineering—the threat actors transitioned the engagement to a scheduled meeting. They provided a Calendly link that redirected the victim to a meticulously crafted, spoofed Zoom meeting portal hosted on infrastructure controlled entirely by the adversary. This controlled environment set the stage for the most compelling element of the lure: the use of an AI-generated deepfake video featuring the CEO of an entirely different, ostensibly peer cryptocurrency company.
According to the victim’s account, the interaction proceeded as a genuine video conference. However, the deepfake video served a crucial, deceptive purpose: to simulate persistent audio difficulties. This ruse created the perfect pretext for the attacker to guide the victim toward troubleshooting steps. Researchers from Google’s Mandiant noted that this manufactured technical issue provided the necessary leverage for the attacker to direct the user to execute commands listed on a web page they controlled.

This technique—using technical malfunction as an excuse to force the victim to execute pre-written commands—is a highly evolved form of what is often termed the "ClickFix" or "Help Desk" scam, adapted for high-value targets and utilizing synthetic media. The malicious instructions found on the webpage were platform-agnostic, offering distinct command sequences to initiate the infection chain on both Windows and macOS operating systems.
This mirrors earlier documented tactics. Mid-2025 saw similar operations attributed to the BlueNoroff group (also known as Sapphire Sleet or TA44), another North Korean entity known for targeting macOS users with custom payloads, underscoring a shared playbook among Pyongyang-aligned cyber groups utilizing social engineering to breach Apple environments, which are often perceived as inherently more secure.
Unpacking the macOS Payload Delivery
Once the victim executed the prescribed commands, the infection process initiated on the macOS host. Mandiant researchers observed initial evidence pointing toward the execution of AppleScript, a scripting language native to macOS, suggesting a deliberate attempt to use built-in capabilities to mask initial stages. While the contents of the very first payload delivered via this mechanism could not be fully recovered during the engagement, the subsequent stage involved the deployment of a malicious Mach-O binary—the native executable format for Apple operating systems.
The critical finding was the subsequent deployment of seven distinct malware families onto the compromised host. This layered deployment strategy is indicative of a mature threat actor aiming for redundancy and comprehensive data capture. The identified malware families included:
- SUGARLOADER: This payload exhibited the highest number of detections on VirusTotal, suggesting it is a known, widely distributed piece of malware used by various threat actors, likely serving as a versatile initial access or information-gathering tool.
- WAVESHAPER: This binary showed significantly lower recognition, flagged by only two security products on the platform, indicating a more bespoke or recently developed tool.
- SILENCELIFT, DEEPBREATH, and CHROMEPUSH: Mandiant explicitly flagged these three components as representing a novel set of tooling for UNC1069. The introduction of new, proprietary malware components is a significant indicator of continued investment in custom infrastructure and evasion techniques by the threat group.
The deployment of seven unique malware families against an individual endpoint is described by security experts as highly unusual for typical espionage or generalized ransomware campaigns. This aggressive saturation strongly suggests a surgical focus on maximizing data extraction from a high-value target within the financial technology space.
Implications for Cryptocurrency Security and Data Exfiltration
The objective of this complex operation is twofold, as interpreted by Mandiant analysts. First and foremost is direct financial gain via cryptocurrency theft, likely involving the capture of wallet credentials, private keys, or access tokens. Second, and perhaps more insidious, is the leveraging of the victim’s identity and proprietary data to fuel subsequent social engineering campaigns. By harvesting internal communications, organizational charts, and personal details, UNC1069 can construct highly convincing, context-aware lures for future targets, creating a self-sustaining ecosystem of compromise.

The targeting consistency is noteworthy. Since 2018, UNC1069 has shown a clear pattern of adaptation to lucrative sectors. In 2023, the group shifted focus toward the burgeoning Web3 industry, concentrating on centralized exchanges, blockchain developers, and venture capital funds invested in digital assets. In the year preceding this investigation, the focus sharpened further, drilling down into the critical infrastructure supporting the digital economy: payment processors, brokerage platforms, and wallet infrastructure providers. This demonstrates a sophisticated understanding of where the highest concentrations of liquid digital wealth reside and how to target the weakest links in the security chain connecting them.
Expert Analysis: The Normalization of Deepfakes in Cyber Warfare
The integration of AI-generated video deepfakes marks a watershed moment in the evolution of state-sponsored cyber operations. While synthetic media has been anticipated as a future threat vector, its deployment by UNC1069 indicates that these tools are no longer theoretical but are actively integrated into real-world, high-stakes infiltration playbooks.
From an adversarial perspective, deepfakes solve a critical problem in social engineering: maintaining continuous, believable engagement without the risk of the target demanding a live video call with the actual executive. The fabricated audio issue provides a convenient technical excuse for the attacker—who is likely controlling the video feed remotely—to avoid unscripted conversation or verification checks. This elevates the "trust factor" far beyond what text-based phishing or even voice cloning (vishing) can achieve.
The focus on macOS is also significant. While Windows remains the dominant enterprise platform, the cryptocurrency and Web3 development communities often exhibit a higher affinity for Apple hardware. By developing and deploying novel, customized Mach-O payloads, UNC1069 is deliberately bypassing the security assumptions often held by Mac users. The discovery of new binaries like SILENCELIFT suggests the group is investing heavily in zero-day or custom evasion techniques specifically designed to evade signature-based detection systems prevalent in enterprise security stacks focused on Windows.
Furthermore, the deployment of seven distinct malware families suggests a modular, multi-stage approach to compromise. This strategy ensures that if one payload is detected or fails to execute correctly, others are waiting to perform different functions—be it establishing persistence, escalating privileges, sniffing network traffic, or exfiltrating specific file types relevant to crypto operations. This level of redundancy maximizes the chances of achieving the financial objective before detection and eradication.
Industry Implications and Future Trajectories
The implications of UNC1069’s latest campaign reverberate across the entire financial technology and cybersecurity industries.
.jpg)
For Cryptocurrency Firms: The attack highlights the critical vulnerability of personnel interacting with potential partners or investors. Traditional perimeter defenses are irrelevant when the breach originates from a trusted digital interaction facilitated by AI manipulation. Enhanced internal training must now move beyond identifying suspicious emails to training employees to verify video identities through secondary, out-of-band channels (e.g., calling the purported executive on a known, verified phone number).
For macOS Security Vendors: The proliferation of custom Mach-O payloads underscores the need for behavioral analysis and Endpoint Detection and Response (EDR) solutions tailored specifically for the macOS environment. Signature-based defense is clearly insufficient against actors who regularly introduce novel binaries. Security tooling must focus on monitoring anomalous process trees, unusual system calls (like the observed AppleScript execution), and suspicious file I/O operations inherent in the infection chain.
For AI and Security Convergence: This incident serves as a stark warning that generative AI is rapidly democratizing the capability to execute highly convincing, personalized social engineering at scale. The future threat landscape will be characterized by an "AI arms race" where defenders must deploy AI-powered tools to detect synthetic media, sophisticated automated lures, and evasive malware, while adversaries use similar technologies to refine their attack vectors.
UNC1069, as demonstrated by its sustained evolution since 2018, is a highly adaptive and well-resourced entity. Their methodical approach—identifying a high-value target vertical (crypto), mastering the social engineering required to breach it (deepfakes, Telegram), and developing custom, multi-layered payloads for preferred operating systems (macOS)—positions them as one of the most sophisticated financial threat actors globally. As the digital asset space continues to grow, the pressure on these entities to generate revenue through cybercrime will only intensify, guaranteeing further innovation in their offensive techniques. The next iteration of UNC1069’s toolkit will likely involve even more seamless integration of synthetic reality and increasingly obscure, low-level exploitation methods designed to remain dormant until the moment of maximum financial payout.