The digital backbone of Sapienza University of Rome, one of Europe’s most venerable and largest academic institutions, has been brought to a grinding halt following a significant and disruptive cyberattack. This incident underscores the growing vulnerability of large-scale educational ecosystems to advanced threat actors, posing critical questions about data resilience and national security in the digital age. The university, which educates over 112,500 students on its sprawling Roman campus, confirmed the breach earlier this week via public communication channels, signaling an immediate and drastic response to contain the digital contamination.
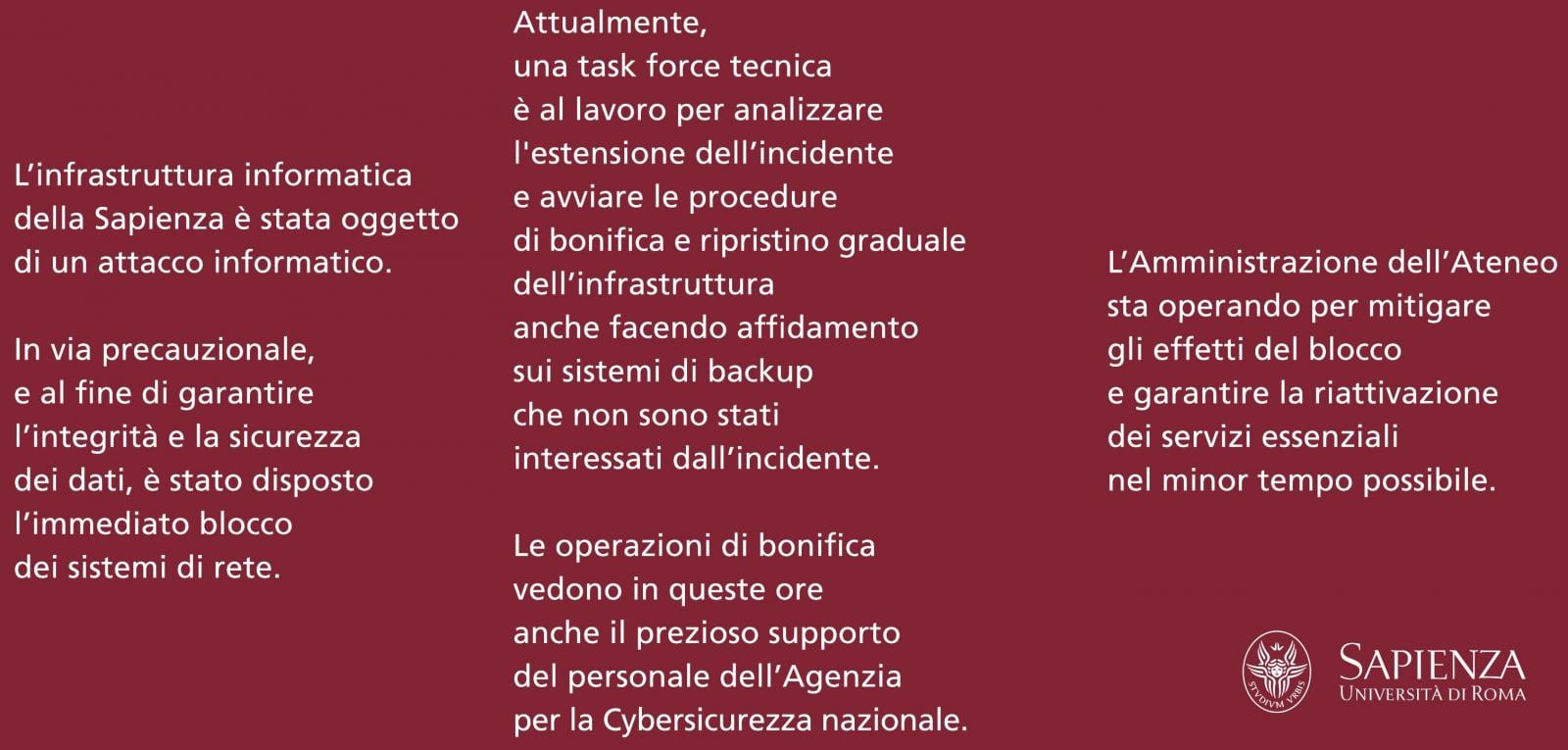
In a statement released across its social media platforms, the institution acknowledged that its entire IT infrastructure had been compromised. Crucially, the response was swift containment: "As a precautionary measure, and in order to ensure the integrity and security of data, an immediate shutdown of network systems has been ordered." This decisive action, while causing widespread operational paralysis—including rendering the main website inaccessible—is a standard, albeit painful, procedure designed to prevent further lateral movement of malware and potential data exfiltration before forensics can begin.
Sapienza’s scale amplifies the severity of the operational fallout. As the continent’s largest university by enrolled students, the disruption impacts thousands of academics, researchers, administrative staff, and students reliant on digital platforms for everything from registration and course materials to sensitive research data management. The immediate aftermath saw the rapid mobilization of internal technical teams, who immediately engaged with national cybersecurity authorities. Collaboration is underway with the Italian Computer Security Incident Response Team (CSIRT), specialists from the Agenzia per la Cybersicurezza Nazionale (ACN), and the specialized cybercrime unit, the Polizia Postale, to manage the crisis response and orchestrate recovery efforts.
The immediate focus remains on systemic restoration. Crucially, preliminary reports suggest that the organization’s essential data backups may have survived the encryption event, a critical differentiator between a recoverable incident and a potentially catastrophic data loss scenario. However, the process of bringing complex, interconnected university systems back online—ensuring integrity at every stage—is inherently protracted. In the interim, the university has established temporary physical "infopoints" across campus to disseminate essential information, acting as analog conduits for data flow when digital systems are offline. This reliance on manual, in-person support highlights the immediate regression in operational efficiency caused by such attacks.
While the university has maintained a tight-lipped official posture regarding the specifics of the attack vector or the identity of the assailants, investigative reports emanating from major Italian media outlets point toward a highly specific and aggressive ransomware operation. Reports suggest the attack is attributable to a pro-Russian threat group identified as "Femwar02." This attribution, based on observed malware characteristics and operational patterns, links the incident to the infamous Bablock/Rorschach ransomware strain.
Rorschach is not a novice player in the cybercrime landscape. Emerging in 2023, it quickly garnered notoriety within security circles for its exceptional operational speed. Cybersecurity analysis, including assessments by firms like Check Point, has characterized Rorschach as a modular construct, seemingly leveraging components derived from the source code leaks of previously prominent ransomware families such as Babuk, LockBit v2.0, and DarkSide. Its defining technical feature is its blistering encryption speed, enabling rapid compromise across large network segments before defensive measures can be fully deployed. This speed suggests a highly motivated and technically proficient adversary targeting high-value, slow-moving institutional networks.
The implication of a ransom demand, as suggested by media sources, adds another layer of geopolitical and ethical complexity. Allegedly, a ransom note exists, demanding payment, but university administrators have reportedly taken the highly strategic, though risky, step of not engaging with the communication to prevent the activation of a specified 72-hour countdown timer associated with the threat actors. The precise monetary figure sought remains undisclosed, which is standard practice while negotiations (or the decision not to negotiate) are underway. The decision to withhold engagement is often predicated on institutional policy, national law, and an assessment of backup viability, as paying ransoms is widely discouraged by law enforcement globally due to the incentive structure it creates for further criminal activity.
Industry Implications: Higher Education as a Prime Target
The targeting of Sapienza University carries significant weight within the broader cybersecurity landscape, particularly concerning the higher education sector. Universities are increasingly recognized as "soft targets" with high data value. They manage vast repositories of sensitive personal data (student records, financial information), valuable intellectual property (cutting-edge research), and often possess sprawling, legacy IT infrastructures riddled with unpatched vulnerabilities—a perfect storm for ransomware groups.
For many institutions, maintaining state-of-the-art security across disparate departments—research labs, administrative offices, student housing, and library systems—is an ongoing budgetary and logistical nightmare. The attack on Sapienza serves as a potent, real-world case study demonstrating the fragility of this security posture when confronted by state-sponsored or ideologically motivated ransomware affiliates.

The involvement of a pro-Russian group adds geopolitical tension. Such groups often operate with relative impunity, leveraging national ambiguity or operational sanctuaries to target Western infrastructure, particularly entities perceived as symbols of Western academic or governmental influence. In the context of ongoing global tensions, an attack on a premier European university can be viewed as a form of digital signaling or low-level kinetic action, aiming to sow discord and demonstrate capability without escalating to direct military confrontation.
Expert Analysis: The Rorschach Modus Operandi and Data Exfiltration Risk
From a technical standpoint, the alleged use of Rorschach demands close scrutiny. The ransomware’s architecture, being a composite of successful predecessor strains, suggests a highly refined encryption mechanism optimized for speed and persistence. While the immediate threat is data encryption rendering systems unusable, the more insidious long-term danger in modern ransomware attacks is dual extortion: the encryption and the exfiltration of data prior to encryption.
Even though Rorschach does not appear to utilize a public dark web "leak site" (a common tactic among groups like LockBit), this does not eliminate the risk of data exposure. The threat actors could still sell the exfiltrated data privately to other criminal syndicates specializing in data brokerage or identity theft. Furthermore, if the data is sensitive—such as proprietary research findings, sensitive personal health information of staff, or confidential administrative contracts—its leakage could result in severe regulatory penalties under data protection frameworks like GDPR, irrespective of whether a ransom is paid.
The decision to rely on backups, while prudent, introduces the challenge of data synchronization and corruption. Restoring from backups requires meticulous validation to ensure that the restored data is clean and that the original intrusion vector has been completely neutralized. A failure to isolate the root cause means that restored systems could be immediately reinfected, leading to a disastrous loop of compromise. This recovery process requires rigorous forensic analysis to map the attacker’s path of least resistance across the network.
Future Impact and Resilience Trends
The Sapienza incident will undoubtedly prompt a significant reassessment of cybersecurity strategies across Italian and European universities. We can anticipate several immediate and longer-term shifts in institutional focus:
-
Increased Investment in Endpoint Detection and Response (EDR): To counter fast-moving threats like Rorschach, reactive patching is insufficient. Institutions must deploy advanced EDR solutions capable of detecting anomalous behavior (like mass file access or rapid encryption initiation) at the endpoint level, allowing for micro-segmentation and automated isolation before network-wide impact occurs.
-
Mandatory Immutable Backups: The current reliance on backups must evolve towards immutable, air-gapped, or geographically diverse storage solutions. If backups are accessible to the same network credentials used by the compromised servers, they remain vulnerable. True resilience demands backups that cannot be modified or deleted by the production environment.
-
Enhanced Geopolitical Threat Modeling: Universities engaged in sensitive international research or critical technology development must now incorporate geopolitical threat actors into their risk matrices. Security policies need to reflect the likelihood of state-sponsored or politically motivated attacks, demanding higher security standards for specific research silos.
-
User Vigilance as a Primary Defense: The human element remains the weakest link. The advisory issued to Sapienza staff and students regarding heightened phishing awareness is vital. Threat actors often gain initial access through spear-phishing campaigns targeting faculty or administrative staff with legitimate-looking emails. Continuous, high-fidelity training is essential to fortify this perimeter.
For the thousands of individuals connected to Sapienza, the immediate future involves navigating a digital blackout. Access to academic records, library resources, and secure communication channels is severed. The establishment of temporary information points is a necessary stopgap, but the prolonged absence of digital services impedes research continuity and the fundamental administrative functions of a major public service organization. The successful remediation of this incident will not just be a technical victory; it will be a measure of the institution’s commitment to protecting the core academic mission in an increasingly hostile digital environment. The fallout from this attack will reverberate through campus policies and IT budgets for years to come, serving as a stark reminder that digital defense is no longer ancillary to education, but foundational to its very operation. The restoration process, involving collaboration between national agencies, will serve as a benchmark for crisis management in the European academic sector.

