The cybersecurity landscape has been confronted with the emergence of DKnife, a sophisticated, long-running Linux-based toolkit that has been actively deployed in targeted espionage operations since at least 2019. This framework represents a significant evolution in network intrusion techniques, functioning as a dedicated post-compromise platform engineered to achieve persistent adversary-in-the-middle (AitM) capabilities directly at the network edge—typically within routers or gateway devices. By compromising these critical junctures, DKnife achieves the unprecedented ability to monitor, intercept, and systematically manipulate data traffic destined for all connected endpoints, including workstations, mobile devices, and Internet of Things (IoT) hardware.
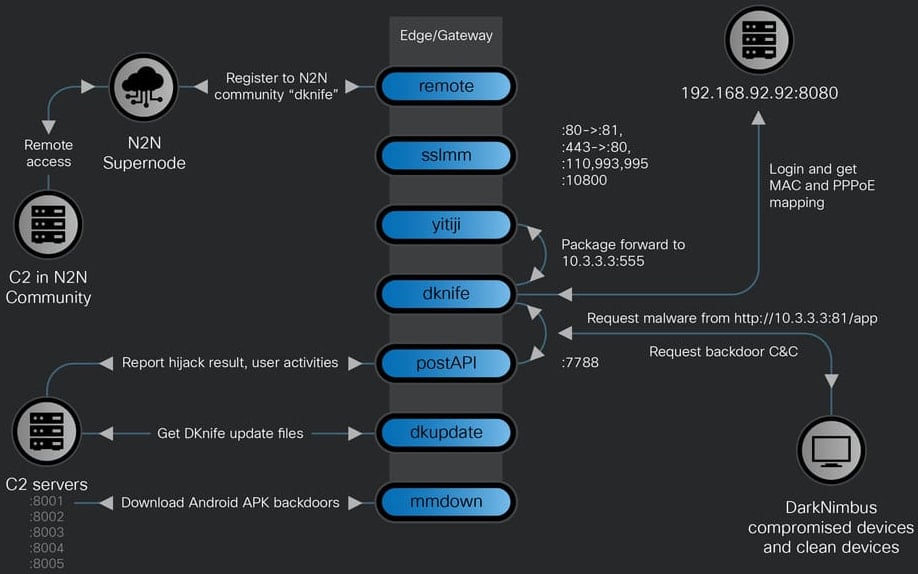
Analysis conducted by researchers at Cisco Talos reveals that DKnife is architecturally complex, built upon an Executable and Linkable Format (ELF) structure comprising seven distinct, interconnected Linux components. These modules are meticulously designed to execute core espionage functions: deep packet inspection (DPI), granular traffic modification, comprehensive credential harvesting, and strategic malware injection. The persistent nature of this toolkit, coupled with its depth of access, positions it as a formidable threat capable of executing long-term surveillance campaigns with minimal detection footprint.
Tracing the Nexus: Linguistic Artifacts and Attribution
A critical clue underpinning the attribution of the DKnife toolkit lies in its linguistic fingerprint. Security analysts have identified pervasive Simplified Chinese language artifacts embedded within component naming conventions and source code comments. Furthermore, the operational focus of the toolkit strongly suggests specific targeting, with observed activity pointing toward prominent Chinese-language services, including domestic email providers, mobile application ecosystems, various media domains, and, notably, intensive monitoring of WeChat user communications. Based on this confluence of technical evidence and operational targeting, Talos researchers have concluded with a high degree of confidence that the operators behind DKnife are associated with a state-sponsored or closely aligned China-nexus threat actor.
The seven specialized components of the DKnife framework work in concert to achieve seamless operational execution. These modules manage essential functions such as maintaining reliable communication channels with remote Command and Control (C2) infrastructure, executing DNS manipulation tactics, hijacking essential software update and binary download streams, deploying established secondary backdoors, selectively neutralizing security product communications, and reliably exfiltrating collected user telemetry back to the attackers.
Deep Dive into Operational Mechanics: The Bridged TAP Interface
The foundation of DKnife’s powerful AitM capability rests on its initial deployment vector and subsequent setup on the compromised network hardware. While the precise method of initial compromise for the target network equipment remains undisclosed by the researchers, once installed, DKnife leverages its component, typically named yitiji.bin, to establish a virtual network device. Specifically, it configures a bridged Transparent Access Point (TAP) interface, often assigning it the internal private IP address of 10.3.3.3.

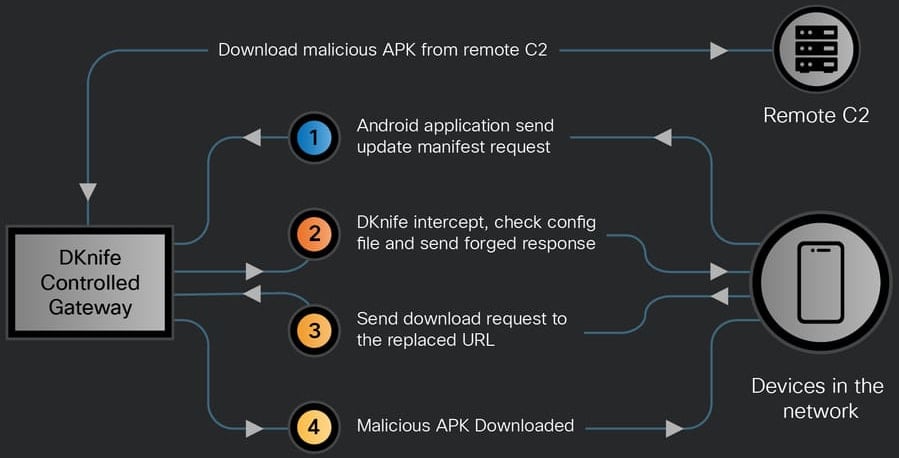
This TAP interface configuration is technically significant. By operating at this layer, DKnife essentially positions itself as an invisible man-in-the-middle on the local network segment. It gains the ability to capture, inspect, and crucially, rewrite any network packet as it transits between the router/gateway and its final destination endpoint. This level of packet manipulation enables dynamic payload injection. For instance, DKnife can intercept legitimate software update requests originating from an endpoint and substitute the legitimate download URL with a link pointing to a malicious executable or installer crafted by the threat actor.
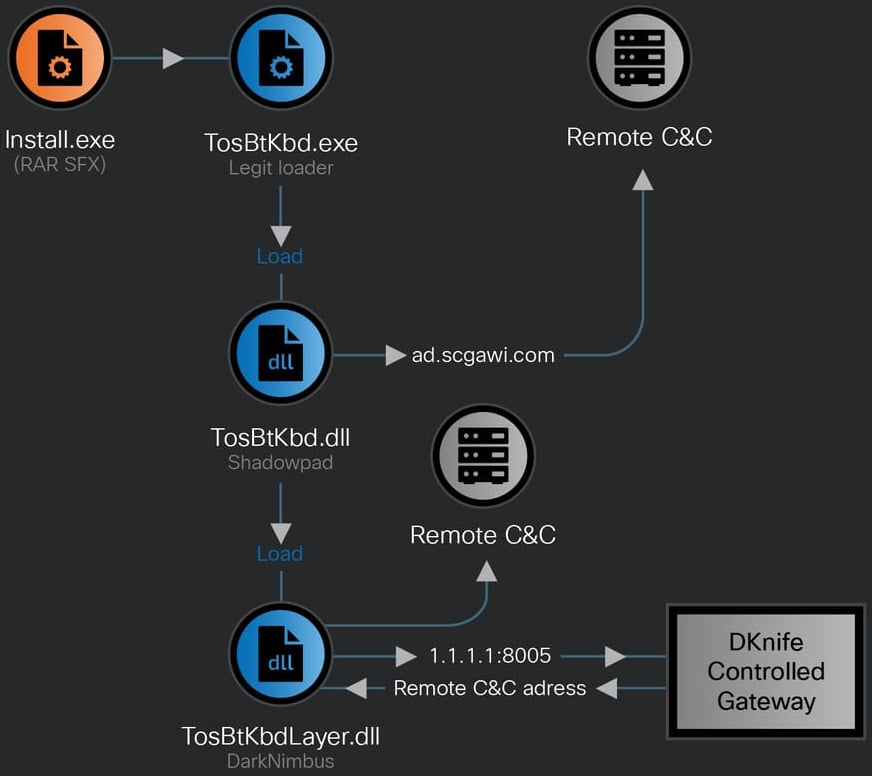
This capability was observed in practice: Cisco researchers documented DKnife deploying the infamous ShadowPad backdoor onto Windows systems. In a highly advanced maneuver, the dropped ShadowPad executable was even signed using a digital certificate belonging to a legitimate Chinese enterprise, significantly boosting its trustworthiness in the eyes of endpoint security solutions. Following this initial compromise, the DKnife framework facilitated the subsequent deployment of the DarkNimbus backdoor. For Android devices connected to the compromised network, the delivery mechanism was more direct, with DKnife injecting the necessary malicious Android Package (APK) files straight into the device’s update or download stream.
The infrastructure associated with DKnife activity has also hosted other notable malware, including the WizardNet backdoor. WizardNet was previously cataloged by other security firms (such as ESET) as a component of the Spellbinder AitM framework, suggesting potential overlap or shared infrastructure among sophisticated espionage groups operating under the same nexus.
Sophisticated Surveillance and Data Exfiltration
Beyond simple payload delivery, DKnife’s primary objective appears to be comprehensive, persistent surveillance. The toolkit’s modules are designed to actively monitor and harvest highly sensitive user data:
- DNS Hijacking: Redirecting domain name lookups to attacker-controlled servers, allowing the threat actor to steer users to phishing sites or malicious download portals even if the intended destination is legitimate.
- Application Update Interception: As noted, hijacking Android application updates and binary downloads ensures that compromised endpoints are systematically infected or re-infected with the latest attacker tooling.
- Security Product Evasion: The framework exhibits the capability to selectively disrupt traffic associated with known security products (antivirus, EDR agents), effectively blinding local defenses to the ongoing malicious activities.
- Exfiltration: All collected user activity data is routed internally among DKnife’s modules before being packaged and exfiltrated via encrypted HTTP POST requests targeting specific, pre-configured C2 API endpoints.
The level of analytical depth applied to user monitoring is particularly concerning, especially regarding the WeChat application. DKnife is engineered to meticulously track a wide array of user interactions within this platform. This includes logging metadata and content related to voice and video calls, capturing the entirety of text-based messaging exchanges, archiving all images sent and received, and cataloging the specific media articles consumed by the target user. Because DKnife operates at the gateway level, reporting events in near real-time as packets traverse the network, it facilitates continuous, low-latency data collection across the entire local environment.
Industry Implications and The Evolution of Network Defense
The discovery of DKnife underscores a critical shift in the operational focus of advanced persistent threats (APTs). The traditional attack vector—compromising individual hosts via phishing or exploit kits—is being supplemented, or in some cases superseded, by attacks targeting the network infrastructure itself. Compromising a router or gateway device yields exponential returns, granting access to every device on the network without needing to breach each one individually. This "edge compromise" strategy bypasses many perimeter defenses designed to protect hosts.
For Managed Security Service Providers (MSSPs) and enterprise network administrators, DKnife presents a paradigm shift in incident response and threat hunting. Traditional host-based forensic tools are rendered partially blind because the initial compromise and the delivery mechanism reside outside the endpoint’s visibility perimeter. Defending against such threats requires a renewed emphasis on securing network infrastructure—particularly routers, firewalls, and edge switches—which are often treated as static, trusted components. Hardening these devices against unauthorized firmware modification, implementing rigorous integrity checks on operating systems, and employing network traffic analysis (NTA) tools capable of detecting anomalous DPI or packet rewriting behaviors become paramount.
The reliance of DKnife on established backdoors like ShadowPad and DarkNimbus also highlights the modularity and persistence strategies employed by state-backed actors. These groups often leverage a ‘tool-sharing’ or ‘tool-adaptation’ methodology, integrating proven malware components into new delivery frameworks to maximize efficacy and reduce development overhead.
Future Trajectories: The Ubiquity of Linux-Based Gateway Threats
The technical foundation of DKnife—being an ELF framework designed for Linux environments—is reflective of the expanding attack surface presented by modern networking hardware. As industrial control systems (ICS), IoT devices, and consumer networking equipment increasingly rely on stripped-down Linux distributions, the efficacy of Linux-based malware toolkits like DKnife will only grow.
Looking ahead, we can anticipate several trends emerging from this discovery:
- Increased Focus on Firmware Integrity: Defenders will need to integrate hardware root-of-trust verification and continuous firmware attestation into their security postures, ensuring that the base operating environment of gateway devices has not been maliciously altered.
- Encrypted Traffic Analysis: Since DKnife operates beneath the application layer to intercept raw packets, threat actors will continue to refine techniques to manipulate traffic even when it is TLS/SSL encrypted, perhaps by injecting malicious certificates or exploiting vulnerabilities in the handshake process (though DKnife’s DPI suggests capability against unencrypted flows primarily).
- Supply Chain Vulnerability in Networking Gear: The unknown initial compromise vector strongly suggests potential exploitation of zero-day vulnerabilities in common router operating systems or weaknesses in the device supply chain itself, demanding greater scrutiny of hardware sourcing and deployment.
As of the latest reporting, the C2 infrastructure supporting DKnife remains operational, indicating that ongoing espionage activities reliant on this tool are likely still in progress. The public dissemination of associated Indicators of Compromise (IoCs) is a crucial step, but organizations must proactively hunt for the subtle signs of deep packet manipulation and bridged interface configurations within their own network fabrics to mitigate the lingering threat posed by this highly invasive, edge-level espionage framework.