The landscape of sophisticated cyber threats is undergoing a subtle yet significant transformation, with threat actors increasingly leveraging legitimate, widely-used infrastructure management tools to obfuscate their command-and-control (C2) networks and deployment mechanisms. Recent in-depth analysis by cybersecurity firm Sophos has illuminated a concerning trend: ransomware syndicates and other financially motivated malware operators are systematically abusing virtual machine (VM) provisioning capabilities offered by ISPsystem, a legitimate provider of virtual infrastructure management software. This tactic exploits inherent characteristics of the platform to achieve unprecedented scale, operational resilience, and anonymity in delivering malicious payloads.
The investigation, initially triggered by forensic analysis of recent "WantToCry" ransomware outbreaks, quickly unearthed a pattern of infrastructure reuse. Sophos researchers observed that the threat actors were deploying numerous Windows VMs, all exhibiting identical hostnames. This uniformity strongly suggests the automated use of default templates baked into ISPsystem’s flagship virtualization management application, VMmanager. In the highly fragmented and constantly evolving world of cybercrime, where infrastructure is routinely taken down by law enforcement or security researchers, the ability to rapidly deploy identical, disposable environments represents a critical operational advantage.
Deeper forensic correlation confirmed the breadth of this abuse. The exact same hostnames—the digital fingerprints of these compromised or rented environments—were discovered crisscrossing the infrastructure supporting several high-profile threat groups. This includes notorious ransomware strains like LockBit, Qilin, Conti, and the BlackCat/ALPHV collective, alongside established malware campaigns focused on data exfiltration, such as those distributing the RedLine and Lummar information-stealers. This shared infrastructure points not merely to isolated incidents but to a systemic vulnerability exploited across the cybercriminal spectrum.
ISPsystem and the Mechanics of Evasion
To understand the gravity of this exploitation, it is necessary to contextualize ISPsystem. The company develops essential control panels utilized globally by hosting providers, data centers, and resellers for the efficient management of virtual servers, operating system maintenance, and resource allocation. VMmanager, their virtualization management platform, is designed to streamline the rapid deployment of both Windows and Linux VMs for legitimate clients.

The critical vulnerability identified by Sophos lies in the default configuration of these deployment templates within VMmanager. When a new VM instance is spun up using these standard templates, the system reuses default hostnames and often retains identical system identifiers. This design feature, intended for administrative convenience in high-volume environments, becomes a perfect camouflage for malicious operations.
The primary beneficiaries of this technical oversight are what security professionals term "bulletproof hosting" providers. These entities deliberately offer infrastructure services that ignore takedown requests, lack robust abuse monitoring, and effectively serve as an untraceable base of operations for illicit activities. By allowing threat actors to provision VMs via VMmanager, these hosts enable the rapid establishment of C2 servers and payload distribution networks that are notoriously difficult to dismantle quickly. The identical hostnames function as digital camouflage, allowing malicious systems to blend seamlessly into the noise generated by thousands of legitimate, ephemeral VMs managed by the same software instance. This dramatically complicates attribution efforts, as investigators attempting to isolate a specific malicious server are confronted with an entire fleet sharing the same non-unique identifier.
The Geography of Illicit Hosting
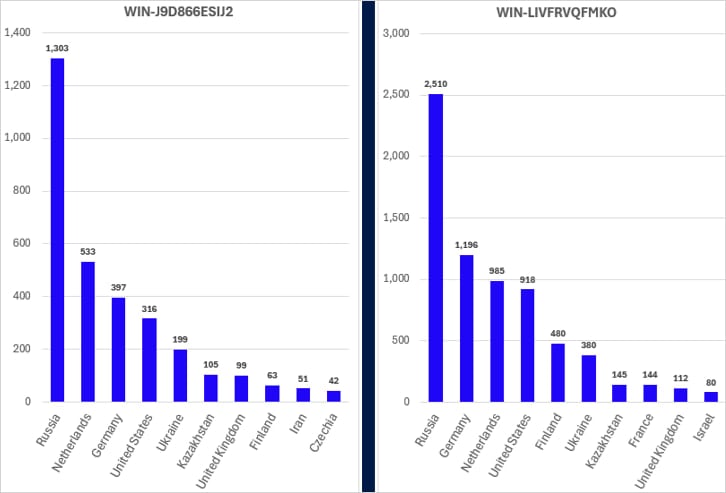
The distribution of these malicious VMs is not random. Sophos data indicates a heavy concentration within a small cohort of hosting providers already notorious for their poor compliance records or those operating under sanctions. Providers cited in the research, such as Stark Industries Solutions Ltd., Zomro B.V., First Server Limited, Partner Hosting LTD, and JSC IOT, represent a known element of the underground economy that facilitates cybercrime.
More alarming is the discovery of infrastructure providers like MasterRDP, which reportedly possess direct control over the underlying physical hardware. MasterRDP allegedly utilizes VMmanager specifically for evasion, offering Virtual Private Server (VPS) and Remote Desktop Protocol (RDP) services with a clear policy of non-compliance with international legal inquiries. For ransomware groups, this environment offers a low-risk staging ground for preparing multi-stage attacks or hosting zero-day exploits, knowing that the underlying infrastructure is protected by a non-cooperative entity.
Sophos quantified the prevalence of this technique by analyzing the most common ISPsystem hostnames found across their telemetry linked to confirmed criminal activity. Strikingly, four specific, frequently reused hostnames accounted for over 95% of all internet-facing ISPsystem virtual machines observed in cybercriminal contexts. The near-total reliance on a handful of default configurations underscores how effectively threat actors have standardized this evasion technique.

Industry Implications and Operational Advantage
The adoption of this technique presents significant ramifications across the cybersecurity and hosting industries.
For Defenders: The immediate impact is the increased complexity and time required for threat neutralization. Traditional indicators of compromise (IOCs), such as unique hostnames or specific network fingerprints, become unreliable when they are shared across legitimate and malicious deployments. Security teams must now employ more advanced, behavioral-based detection methodologies, focusing on traffic patterns, payload analysis, and establishing trust relationships with hosting providers—a process often hampered by the non-cooperative nature of the target hosts. Furthermore, the sheer volume of disposable infrastructure means that even if a C2 server is identified and taken offline, the threat actor can reconstitute the entire network within minutes using another pre-configured template.
For Legitimate Hosting Providers: This situation places undue pressure on the broader hosting ecosystem. Even providers using VMmanager ethically face potential collateral damage, as their infrastructure might inadvertently be misidentified or their reputation tarnished by association with known malicious tenants utilizing the same software stack. It underscores the critical need for better audit trails and mandatory unique identity assignment at the time of VM provisioning, regardless of the template used.
For Ransomware Actors: The operational benefit is clear: low cost, low barrier to entry, and turnkey deployment. VMmanager abstracts away much of the technical expertise required to set up resilient, multi-region infrastructure. Actors can rent access to these services through established underground marketplaces, paying minimal fees for infrastructure that mimics legitimate corporate environments, thus maximizing their profit margin while minimizing operational risk.
Expert Analysis: The Commoditization of Evasion
This trend highlights a broader phenomenon in cybercrime: the commoditization of evasion techniques. Sophisticated evasion tactics, once the domain of nation-state actors, are rapidly filtering down to financially motivated groups. The exploitation of default settings in widely deployed, legitimate software is a hallmark of this maturing threat landscape. It is functionally similar to past abuses of misconfigured cloud storage buckets or the weaponization of legitimate remote administration tools like Cobalt Strike.
From an architectural standpoint, this abuse targets the assumption of trust inherent in management software. VMmanager is designed for efficiency, but that efficiency—the ability to clone configurations rapidly—is precisely what makes it attractive for building disposable attack infrastructure. The fact that multiple, often competing, ransomware groups utilize the same underlying infrastructure fingerprint suggests a degree of infrastructural commonality within the cybercriminal supply chain. It is plausible that certain intermediary bulletproof hosting brokers are providing access to these pre-configured VMmanager environments as a specific service offering.
The identification of these specific hostnames serves as a powerful new vector for threat intelligence, allowing security vendors to pivot from tracking individual campaigns to monitoring the abuse of the underlying platform itself. This shift in focus is crucial because dismantling the platform abuse is a more sustainable security strategy than chasing individual compromised IPs.
Future Impact and Necessary Remediation
The future impact of this tactic will likely involve further entrenchment unless corrective action is taken by the software vendor and the hosting industry at large. If ISPsystem does not mandate unique system identifiers upon VM instantiation, this method of camouflage will continue to proliferate, potentially spreading to other management platforms that prioritize rapid deployment over granular identity management.
For ISPsystem, the immediate challenge involves balancing the needs of their legitimate clientele for fast provisioning against the security imperative to prevent misuse. Potential technical solutions could include:
- Mandatory Unique ID Generation: Forcing the automatic assignment of unique machine identifiers (beyond the default hostname) at the hypervisor level for every new deployment, irrespective of the template used.
- Template Versioning and Auditing: Implementing stricter controls or versioning for default templates, potentially allowing hosting providers to flag or audit deployments that rely exclusively on outdated or known-abused defaults.
- Platform-Level Abuse Monitoring: Developing mechanisms, perhaps integrated into VMmanager, that allow legitimate hosting providers to more easily detect and isolate configurations exhibiting patterns of known malicious activity (e.g., rapid deployment followed by known C2 beaconing).
The broader industry response must involve enhanced collaboration between threat intelligence providers, hosting registrars, and domain authorities. If hosting providers known to facilitate this abuse—like those identified by Sophos—are not subject to sustained pressure or sanctions, the incentive structure remains flawed. The exploitation of ISPsystem VMs is a potent reminder that the battle against cybercrime is increasingly fought not just against the malware itself, but against the legitimate, yet vulnerable, infrastructure that underpins its distribution. As virtualization technology becomes cheaper and more accessible, the sophistication of infrastructural evasion will only escalate, demanding proactive security engineering at the very foundation of cloud and virtualized service delivery.

