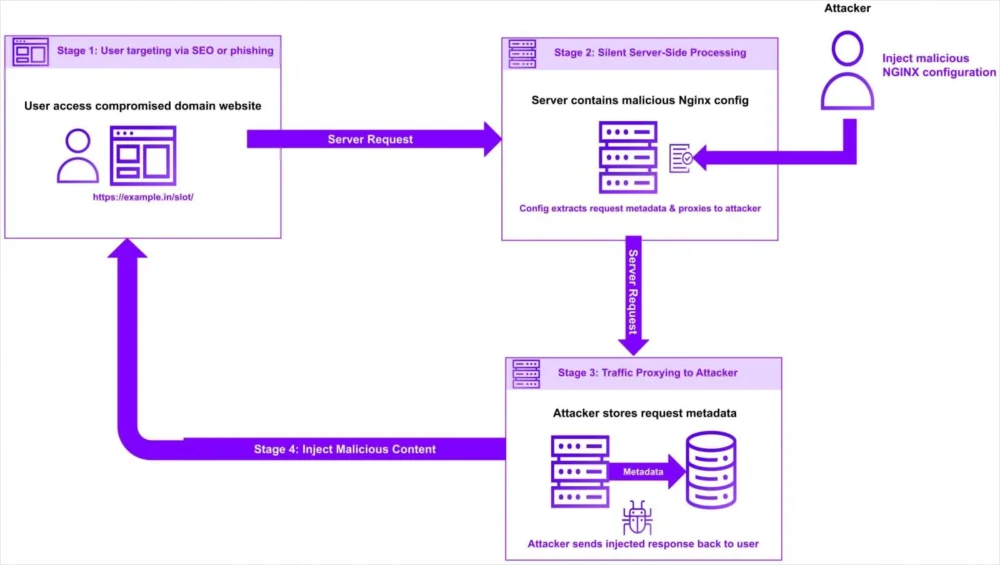
A sophisticated, ongoing cyber campaign is exploiting misconfigurations within NGINX web server installations to covertly intercept and reroute user traffic through attacker-controlled infrastructure. This method of compromise sidesteps traditional vulnerability patching cycles, relying instead on the obscurity and infrequent auditing of configuration files—a stealthy approach that presents a significant detection challenge for system administrators worldwide.
NGINX, a cornerstone of modern internet infrastructure, functions as a high-performance open-source platform for managing web traffic. Its versatility allows it to serve static content, act as a robust load balancer distributing incoming requests across multiple backend servers, perform content caching for speed optimization, and operate as a reverse proxy shielding origin servers. It is precisely this core function—mediating connections—that is being weaponized.
The discovery of this specific campaign was spearheaded by researchers at Datadog Security Labs, who identified a pattern targeting NGINX deployments, particularly those utilizing the Baota web hosting management panel. The initial scope of the observed compromise appears concentrated, focusing heavily on websites associated with Asian top-level domains, including those ending in .in, .id, .pe, .bd, and .th. Alarmingly, the threat actors have also set their sights on high-value targets such as government (.gov) and educational (.edu) domains, suggesting motives ranging from data exfiltration to surveillance or large-scale redirection for phishing or malware distribution.
The Mechanics of Configuration Subversion
The technical ingenuity of this attack lies in its direct manipulation of NGINX configuration files, avoiding the need to discover and exploit a zero-day vulnerability in the NGINX software itself. Instead, the attackers leverage legitimate, powerful directives within the configuration syntax.
Specifically, the threat actors inject malicious location blocks into existing, legitimate configuration files. The purpose of these injected blocks is to define specific URL paths or patterns that, when matched by an incoming user request, trigger the malicious action. Once a request matches the attacker’s defined path, the configuration is rewritten to capture the entirety of the original request details, including the full original URL.

The critical pivot point is the utilization of the proxy_pass directive. In standard operations, proxy_pass is a vital tool for load balancing and reverse proxying, instructing NGINX to forward requests to an alternative backend server group, often to improve performance, ensure high availability, or manage microservices architecture. The attackers exploit this by setting the proxy_pass target to a domain under their direct control.
Crucially, because the attackers are utilizing a built-in, functional directive—even if used maliciously—the activity often fails to raise flags in standard security monitoring tools configured to watch for protocol anomalies or outright configuration errors. Furthermore, the attackers meticulously preserve key HTTP request headers, such as Host, X-Real-IP, User-Agent, and Referer. By maintaining these headers, the rerouted traffic appears structurally legitimate to the destination server, even after traversing the adversary’s intermediary infrastructure. This preservation of context is designed to ensure the final user experience is largely seamless, preventing immediate suspicion from the end-user whose traffic ultimately reaches the intended website, albeit through an unauthorized middleman.
The Five-Stage Toolkit Orchestration
The execution of this traffic hijacking is not a manual process but is orchestrated via a multi-stage, scripted toolkit designed for automated persistence and deployment. Researchers have outlined a five-stage operational flow, indicative of a mature and professional threat group:
- Initial Access and Reconnaissance: The toolkit first establishes a foothold, likely via compromised credentials or an unpatched vulnerability in the hosting panel (like Baota), followed by comprehensive scanning of the server environment to confirm the presence and version of NGINX and identify existing configuration structures.
- Configuration Discovery and Backup: The script locates the primary NGINX configuration files (e.g.,
nginx.confor site-specific configuration snippets). It then performs a critical step: backing up the original, legitimate configuration files. This backup ensures that if the attack is discovered and reversed, the immediate operational state can be restored, complicating forensic analysis. - Malicious Injection: This stage involves the programmatic insertion of the weaponized
locationblocks, utilizing the identified attacker-controlled domains within theproxy_passstatements. The injection logic is often designed to target paths less frequently accessed by administrators or specific API endpoints. - Traffic Redirection Validation: After injection, the toolkit likely performs validation checks—perhaps sending test requests to ensure traffic is successfully flowing through the attacker’s intermediary servers before concluding the deployment phase.
- Persistence and Cleanup: The final stage focuses on maintaining access, potentially establishing web shells or secondary backdoors, and erasing evidence of the toolkit’s execution, leaving only the subtle configuration changes behind.
Industry Implications: The Configuration Blind Spot
This attack vector highlights a critical security blind spot pervasive across the web hosting industry: the assumption that configuration files are inherently safe or infrequently modified. While endpoint security focuses heavily on patching operating systems and application binaries, configuration management, often handled by lower-privilege users or automated panels, receives less intense scrutiny.
For organizations relying on NGINX for high-volume traffic management, the implications are severe. The primary risk is not necessarily data theft from the server itself, but rather man-in-the-middle (MITM) capabilities applied to user sessions. Depending on the attacker’s ultimate goal, this rerouting could facilitate:
- Credential Harvesting: Intercepting sensitive login attempts made by users to the legitimate site.
- Session Hijacking: Stealing session tokens or cookies.
- Malware Delivery: Injecting malicious scripts or downloading drive-by malware onto the user’s device as the traffic passes through the proxy.
- Censorship or Redirection: Forcing users to specific, malicious landing pages, particularly concerning for government or educational sites where maintaining integrity is paramount.
The targeting of specific TLDs and institutional domains suggests a level of geopolitical or economic motivation, rather than opportunistic mass compromise. Targeting .gov and .edu sites, for instance, often points toward state-sponsored espionage or intellectual property theft operations.

Expert Analysis: The Elegance of Subversion Over Exploitation
From an expert security standpoint, the elegance of this attack lies in its decoupling from software vulnerabilities. Traditional security advice centers on timely patching of CVEs. However, when an adversary exploits the intended functionality of a piece of software through malicious configuration, patching the NGINX binary offers no defense.
"This is a classic example of ‘living off the land’ applied to infrastructure configuration," notes one security architect specializing in cloud infrastructure. "The system administrator trusts the configuration file because it defines the server’s operational parameters. When those parameters are weaponized, detection mechanisms designed for code execution or buffer overflows are entirely bypassed. You are looking for anomalies in traffic flow, not vulnerabilities in the core application layer."
The use of the Baota panel adds another layer of complexity. Hosting management panels, while simplifying server management for less technical users, often aggregate administrative permissions. If the panel itself is compromised (perhaps through its own outdated components or weak authentication), it grants the attacker a golden key to modify the underlying NGINX settings without needing direct SSH access to the server, making the breach trail colder and harder to follow.
Future Impact and Defensive Trends
The emergence of this NGINX configuration hijacking campaign signals a shift in threat actor methodology toward infrastructure configuration layers. This trend is likely to accelerate as major web servers become more hardened against traditional exploitation techniques. Future defensive strategies must evolve accordingly:
1. Configuration Integrity Monitoring (CIM): Security teams need to implement rigorous Configuration Integrity Monitoring. This involves continuously hashing or cryptographically signing critical configuration files (like NGINX’s .conf files) and alerting immediately if the hashes change outside of scheduled, audited deployment windows. This moves beyond simply checking file modification dates.
2. Traffic Flow Anomaly Detection: Advanced network monitoring systems must look beyond simple packet inspection. They need to establish baseline traffic flows for each legitimate Host header and flag any requests that are unexpectedly proxied or routed through external, unapproved IP ranges, even if the headers remain intact. This requires deep packet inspection capabilities focused on the application layer routing logic.
.jpg)
3. Least Privilege for Configuration Access: The compromise often originates from access to the hosting panel or server management tools. Adopting a strict principle of least privilege for configuration editing is crucial. Only specific, highly monitored automation accounts should have the right to modify NGINX configuration files, separating the roles of content deployment and infrastructure definition.
4. Regular Configuration Audits: Organizations must move beyond periodic manual checks. Automated tools capable of parsing NGINX syntax and identifying suspicious patterns—such as unfamiliar proxy_pass destinations embedded within specific location blocks—should be integrated into continuous compliance pipelines.
In conclusion, the campaign targeting NGINX configurations serves as a potent reminder that security posture is only as strong as its weakest, least-monitored component. For any organization relying on NGINX as a reverse proxy or load balancer, immediate internal audits of configuration files for unauthorized proxy_pass directives are warranted to prevent silent, pervasive traffic redirection. The battleground is shifting from the application code itself to the very instructions that govern how that application interacts with the world.