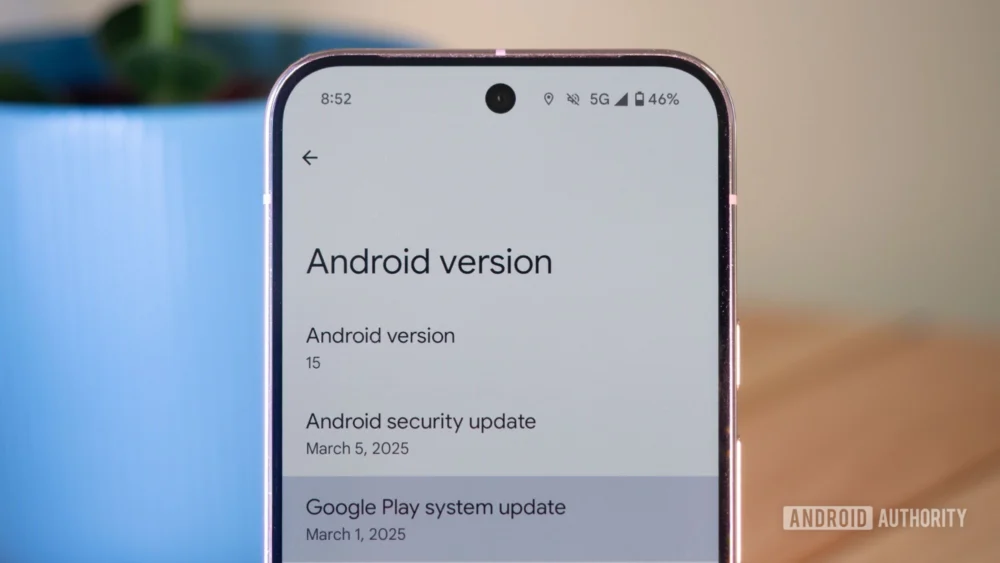
The intricate mechanisms governing Android operating system maintenance are undergoing a peculiar, potentially unintended reversion. Reports circulating across various enthusiast communities indicate a perplexing situation where the Google Play System Update (GPSU) pipeline appears to be functioning in reverse for some users. Specifically, devices that had successfully installed the expected January 1, 2026, component update are now showing a rollback to the preceding November 1, 2025, iteration after applying a subsequent system notification. This anomaly, observed across both Google Pixel hardware and other Android flagships, raises critical questions about the integrity and sequencing of Google’s modular OS delivery system.
To fully appreciate the significance of this temporal slip, one must first understand the architecture of the Google Play System Update. Introduced as a crucial initiative to decouple core operating system maintenance from the protracted cycles imposed by device manufacturers (OEMs) and mobile carriers, GPSU allows Google to push vital security patches, privacy enhancements, and foundational framework updates directly to the device via the Google Play Store infrastructure. This modular approach was designed precisely to mitigate the fragmentation headache that has historically plagued the Android ecosystem, ensuring faster deployment of essential software refinements. For instance, while a full Android OS upgrade might take months to propagate globally following its release, a critical security patch within the GPSU framework can reach billions of devices within weeks, sometimes days.
Historically, this system has seen hiccups, particularly in the early days of its implementation. Major manufacturers, including Samsung, have occasionally experienced synchronization issues, leading to temporary lags or inconsistencies in update delivery. However, these issues typically manifested as delays in receiving the newer update, not an active downgrade from a more recent version to an older one. The current reported scenario—moving backward from January 2026 to November 2025—suggests a deeper, perhaps logical, flaw within the update verification or deployment staging.
The evidence gathered points toward a widespread, albeit non-critical, software misconfiguration. Users running Google Pixel devices, spanning both the stable public release track and those participating in the Android beta programs, have documented this regression. Upon receiving an installation prompt, users confirm the installation process completes, only for the system settings to reflect the older, November 2025 timestamp as the active GPSU version. This is not an isolated incident confined to one hardware vendor; observations have extended to devices from other major OEMs, such as a OnePlus 13R, confirming the issue is systemic rather than specific to Google’s first-party hardware pipeline.
The key to unlocking the nature of this regression lies in the system’s recovery mechanism. Recent updates to the Android framework have empowered users with the ability to manually uninstall specific GPSUs, offering a granular level of control previously unavailable. When affected users deliberately uninstalled the reported November 2025 version, the system, seeking the next valid available component, immediately reverted to the January 2026 version. This behavior strongly suggests that the January 2026 package is functionally present and valid on the device; the problem lies entirely in the metadata or the deployment manifest that instructed the system to install the November 2025 version over the January 2026 version.
Expert analysis leans toward a simple but impactful labeling error within Google’s distribution servers or the accompanying manifest files. If the February 2026 GPSU was prepared for deployment but incorrectly tagged with the version identifier corresponding to November 2025, devices checking for the "latest" update would logically pull the incorrectly labeled file. Since the November 2025 version is chronologically older than the January 2026 version already installed, the installation process effectively overwrites the newer build number with the older one, creating the illusion of a downgrade, even if the underlying security and framework components might not have regressed significantly, or perhaps even received minor, unstated fixes bundled under the old label.
The industry implications of such a discrepancy are worth noting, particularly concerning security audit trails. For enterprises and security professionals managing large fleets of Android devices, accurate version reporting is paramount for compliance and vulnerability management. If the reported version number does not align with the actual installed components, it creates a blind spot. Imagine a scenario where a critical zero-day vulnerability is patched in the January 2026 update, but subsequent erroneous updates continue to report the device as being on the November 2025 patch level. Auditors might flag the device as vulnerable, even if the necessary code is present, leading to unnecessary remediation efforts or, worse, a failure to spot genuine vulnerabilities due to corrupted reporting chains.
Furthermore, this incident highlights the delicate balance Google maintains between modularity and OS integrity. While GPSU is a powerful tool, every time a system component is updated, the system must ensure that the new component is compatible with the base OS version and all other installed modules. A rollback suggests a failure in the dependency checking layer or an oversimplified version comparison algorithm that prioritized the identifier over the actual build timestamp or cryptographic signature of the package contents.
Looking ahead, the future trajectory of Android maintenance relies heavily on the robustness of the GPSU framework. As Android evolves toward even greater componentization—potentially breaking down the system further into smaller, more frequently updated units—the tolerance for versioning errors diminishes drastically. Future iterations of this system will need more sophisticated versioning schemes, perhaps utilizing semantic versioning (Major.Minor.Patch) not just for the release month, but for internal component dependencies, ensuring that a rollback is only possible if the system explicitly identifies the older version as having superior compatibility or a necessary prerequisite feature.
The immediate advice for end-users remains pragmatic: no immediate action is required. Since uninstalling the seemingly older version restores the January 2026 version, it confirms that the system retains the more advanced code. The current situation appears to be a cosmetic bug in the reporting layer, not a functional degradation of security or performance. Users should continue to accept any subsequent GPSU notifications, trusting that Google will eventually issue a corrective update that rectifies the metadata display error. Any attempt to manually force the older version is unnecessary and potentially counterproductive if the subsequent updates rely on the mislabeled version as a temporary checkpoint.
The very fact that users are so attuned to tracking these monthly updates underscores the success of Google’s transparency efforts. The community engagement on platforms where these issues are being reported serves as an invaluable, real-time quality assurance layer that often catches subtle bugs before internal testing pipelines flag them comprehensively. This collective vigilance is crucial for maintaining the high standards expected of a global operating system platform. While this specific incident is minor in terms of user impact, it serves as a potent reminder of the complexity inherent in patching billions of heterogeneous devices across diverse hardware and software configurations on a monthly cadence. Resolving this temporary confusion will be a small but important step in solidifying user confidence in the reliability of the Play System Update mechanism as the primary vehicle for Android evolution. We await clarification from Google regarding the specific technical cause behind this temporal displacement in the update manifests.