A recent, highly coordinated digital reconnaissance effort specifically targeting Citrix NetScaler instances has unveiled a sophisticated approach to pre-exploitation mapping, utilizing an extensive network of compromised residential IP addresses. This activity, monitored between January 28th and February 2nd, demonstrated a clear intent to identify publicly accessible NetScaler login portals and precisely enumerate installed product versions across numerous global organizations. The methodical nature of the scans suggests a targeted campaign likely preceding an organized exploitation phase, moving far beyond the scope of typical opportunistic internet noise.
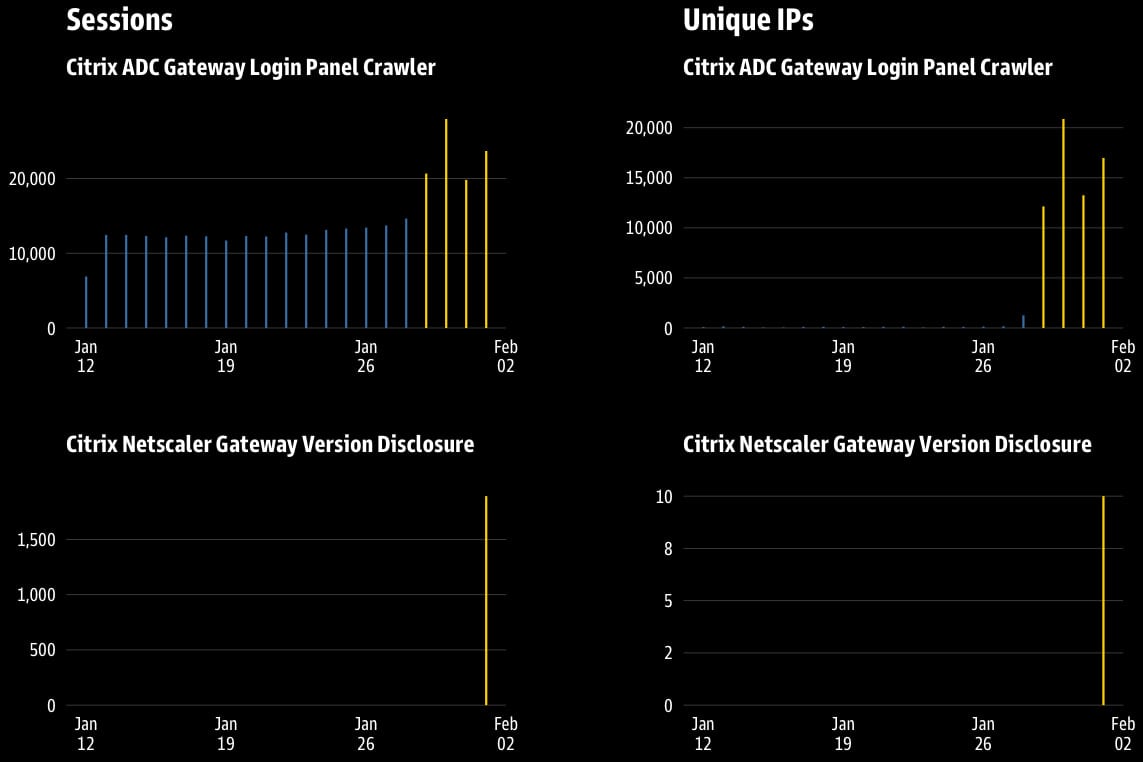
Threat intelligence specialists at GreyNoise, who tracked the anomalous traffic, reported a staggering scale of engagement. The reconnaissance was launched from over 63,000 unique IP addresses, collectively executing more than 111,834 distinct probing sessions. A significant majority—approximately 79% of this traffic—was directed specifically at known Citrix Gateway honeypots, indicating a deliberate attempt to test for active vulnerabilities or bypass basic defensive measures designed to trap low-effort scanners.
The defining characteristic of this campaign was the infrastructure used to mask its origins. Roughly 64% of the scanning payload originated from residential proxies. This tactic is highly effective in circumventing standard security defenses, such as IP reputation blacklists or geo-blocking rules, because the traffic appears to emanate from legitimate, everyday consumer or small business internet service provider (ISP) addresses distributed worldwide. This technique effectively launders the source of the attack, making attribution and automated blocking significantly more challenging for network defenders. The remaining 36% of the observed sessions were traced back to a single, centralized Azure cloud IP address, adding an element of hybrid infrastructure use to the operation.
The Mechanics of Organized Discovery
The analysis reveals two distinct, highly focused vectors of malicious intent within the observed traffic profile. The primary, high-volume vector was dedicated solely to asset discovery. This component generated nearly 110,000 sessions originating from over 63,000 different residential endpoints. Its objective was clear: to locate exposed Citrix authentication interfaces, specifically probing the common path /logon/LogonPoint/index.html. Successfully accessing this endpoint confirms the presence of an internet-facing Citrix login portal, marking the first crucial step in a potential compromise chain.

The second, more granular indicator of malicious intent occurred on February 1st, manifesting as a focused, six-hour sprint involving just 10 unique IPs that executed 1,892 sessions. This secondary effort pivoted from locating the login page to precise version enumeration. The scanners targeted the specific URL path /epa/scripts/win/nsepa_setup.exe. This file path is associated with the Citrix Endpoint Analysis (EPA) toolkit, often utilized in secure access workflows. By attempting to access or download artifacts from this directory, the attackers sought to determine the exact version of the NetScaler ADC (Application Delivery Controller) software running on the target system.
This version-specific targeting is critical. Security vulnerabilities are frequently tied to narrow version ranges. As GreyNoise noted, the use of an antiquated User Agent string—specifically, one corresponding to Chrome 50, released in early 2016—further complicates automated behavioral analysis. This outdated header may be an attempt to mimic older, potentially unpatched systems or simply to bypass modern bot detection heuristics that flag newer browser signatures. The rapid commencement and cessation of this version enumeration sprint strongly suggest that the operation was triggered either by new intelligence regarding recently discovered, exploitable EPA configurations or by exploiting specific deployment windows known to the threat actor.
Industry Context: The Persistent Threat to ADC Gateways
Citrix NetScaler ADC and Gateway products serve as critical access points for enterprises globally, managing remote access, load balancing, and application delivery. Due to their position as the "front door" to internal corporate networks, they have become perennial high-value targets for threat actors. The history of vulnerabilities in these platforms underscores why continuous reconnaissance is prevalent.
For instance, the discovery and subsequent exploitation of critical flaws like CVE-2025-5777 (dubbed "CitrixBleed 2"), which allowed session hijacking, and the previously exploited zero-day vulnerability CVE-2025-5775 (a Remote Code Execution flaw), highlight the severe consequences of unpatched or misconfigured gateways. Attackers are keenly aware that a successful breach via the NetScaler often grants them a persistent foothold, bypassing perimeter defenses entirely.
This latest scanning wave fits squarely into the established pattern of "vulnerability hunting" that precedes major exploitation campaigns. Threat groups invest heavily in mapping the landscape of potentially vulnerable targets before deploying zero-day exploits or leveraging known, unpatched flaws at scale. The use of residential proxies suggests the actors are preparing for an operation where stealth and the ability to rotate through IP addresses rapidly are paramount to success—hallmarks of advanced persistent threat (APT) groups or highly organized cybercriminal enterprises.

Expert Analysis: The Implications of Residential Proxy Use
The widespread deployment of residential proxies moves this reconnaissance effort into a higher tier of operational security maturity for the attackers. In cybersecurity defense, the concept of "trust" is often assigned based on the source of traffic. Traffic originating from known cloud providers (like Azure, as seen in the 36% remainder) or established data centers can be subject to stricter scrutiny, rate limiting, or outright blocking based on threat intelligence feeds.
Residential proxies, however, leverage legitimate, dynamically assigned IP addresses belonging to home internet users. Defenses relying solely on IP reputation often fail against this traffic because, from the perspective of the target server, the request appears to originate from a legitimate, albeit geographically diverse, end-user. This forces security teams to rely more heavily on behavioral analysis, deep packet inspection, and application-layer monitoring, which are computationally more intensive and complex to deploy universally.
The dual focus on both login panels and EPA configuration files indicates a multi-pronged intelligence gathering strategy:
- Access Confirmation: Finding the
/logon/path confirms the appliance is exposed and actively serving authentication requests. - Version Pinpointing: Targeting
/epa/scripts/allows the attacker to fingerprint the exact build, enabling them to select the most effective exploit payload from their arsenal—whether it targets a known, patched flaw that the target organization failed to apply, or a newer vulnerability specific to that version.
The fact that 79% of the traffic hit honeypots is also informative. Honeypots are often configured to mimic slightly outdated or deliberately vulnerable versions to attract and analyze attacker TTPs (Tactics, Techniques, and Procedures). The high engagement rate suggests the automated scanning tool was not effectively distinguishing between production systems and decoys, or that the decoys were sufficiently realistic to warrant probing.
Industry Response and Future Security Posture
The immediate implications of this surveillance necessitate a swift and comprehensive hardening of Citrix infrastructure across the board. GreyNoise has provided actionable indicators of compromise (IOCs), which organizations should immediately integrate into their Web Application Firewalls (WAFs), intrusion detection systems (IDS), and SIEM platforms.
However, long-term mitigation requires architectural shifts beyond simple blocking:
-
Strict Access Restriction for Sensitive Directories: System administrators must rigorously review the necessity of external exposure for the
/epa/scripts/directory. If EPA functionality is required remotely, access should be restricted via strict source IP whitelisting (if possible) or layered authentication mechanisms that verify user identity before allowing access to these diagnostic paths. Disabling version disclosure in HTTP response headers is also a critical step to reduce fingerprinting opportunities. -
Zero Trust for Remote Access: The reliance on NetScaler Gateways as the sole perimeter must be re-evaluated. Modern security frameworks mandate a Zero Trust approach where even authenticated users are continuously verified. Organizations should prioritize adopting solutions that enforce least-privilege access, potentially moving away from blanket VPN-style access provided by some gateway configurations.
-
Advanced Anomaly Detection: Defenders must evolve their monitoring to focus on behavioral anomalies rather than static IP reputation. This includes flagging unusual traffic volume from legitimate residential ranges, especially when requests target configuration or setup file paths, or when user agents do not align with current enterprise usage patterns.
The widespread use of residential proxies in this NetScaler reconnaissance foreshadows a growing trend in high-stakes cyber campaigns. As defenders enhance their perimeter defenses against data center-based attacks, threat actors will increasingly turn to distributed, high-trust residential networks to mask their activities. This creates an arms race where the ability to rapidly correlate disparate, seemingly legitimate traffic streams into a cohesive attack pattern will become the defining capability of effective threat detection teams. Organizations managing high-value external-facing services like NetScaler must prepare not just for automated attacks, but for highly obfuscated, persistent mapping campaigns designed to operate beneath the radar of conventional security tooling. The goal for defenders is no longer just to stop the exploit, but to detect the meticulous planning that precedes it.

