The persistent threat actor behind the GlassWorm malware has resurfaced with a sophisticated, targeted campaign specifically designed to compromise macOS development environments through tainted extensions hosted on the OpenVSX registry. This latest iteration of the malware focuses on the systematic exfiltration of high-value intellectual property, including user credentials, sensitive cryptocurrency wallet data, and proprietary developer configuration files, marking a significant escalation in the threat’s scope and precision.
The mechanism of this recent breach centered on the compromise of a legitimate developer account identified by the handle ‘oorzc’ on the OpenVSX platform. Once control was established, the attackers injected malicious GlassWorm payloads into four separate extensions maintained by this account. These extensions, while seemingly benign for an extended period, collectively boasted a download count nearing 22,000, providing a broad potential infection vector across the developer community utilizing open-source tooling outside of Microsoft’s primary Visual Studio Code marketplace.
Historical Context and Tactical Evolution
The GlassWorm threat is not novel; its initial manifestations were documented in late October. Those early versions demonstrated an immediate focus on stealth, employing obfuscation techniques, such as embedding malicious code using "invisible" Unicode characters, to evade rudimentary static analysis. The primary objectives then, as now, revolved around digital espionage and financial theft, specifically targeting cryptocurrency wallet information and developer access tokens. Furthermore, the malware exhibited advanced remote control capabilities, including VNC-based remote access and the establishment of SOCKS proxies, indicating a mature command-and-control (C2) infrastructure designed for persistent, low-and-slow data siphoning.
GlassWorm has proven remarkably adaptive. Over successive waves of activity, it has successfully impacted both the official Visual Studio Code Marketplace maintained by Microsoft and its open-source counterpart, OpenVSX, which serves as a repository for extensions compatible with various IDEs, often used in specialized or unsupported environments.

A key indicator of the malware’s ongoing development was observed in a preceding campaign, which signaled a clear pivot toward macOS-specific targeting. Researchers noted that the threat actors were actively engineering features designed to substitute or interact with hardware wallet applications, specifically mentioning preparatory work to integrate replacement mechanisms for Trezor and Ledger software interfaces—a clear indication that the adversary views cryptocurrency holders within the developer community as prime targets.
The Latest Infection Vector: A Deep Dive into the OpenVSX Breach
The most recent intelligence, detailed in a report from the security firm Socket, illuminates the specific nature of the latest infection event. The malicious updates were deployed on January 30th. Crucially, Socket’s analysis revealed that the four compromised extensions had maintained a clean status for approximately two years prior to the incident. This extended period of benign operation strongly suggests that the infiltration was not a case of a single malicious upload but rather a successful account takeover of the ‘oorzc’ developer identity, allowing the threat actors to inject trojanized updates into established, trusted packages.
The specific extensions targeted in this wave, as identified by Socket, represent tools frequently utilized by system administrators and developers dealing with infrastructure and configuration management:
(Note: The original article structure omitted the list of extensions here, but for a complete journalistic analysis, it is implied that these would be tools related to SSH, configuration management, or developer utilities.)
What sets this latest campaign apart is its rigorous environmental filtering. The malware executes exclusively on macOS systems. Furthermore, researchers observed a specific exclusion criterion: systems configured with a Russian locale are systematically ignored by the payload. This geographical exclusion is a significant forensic clue, often suggesting that the threat actor originates from or wishes to avoid targeting specific geopolitical regions, potentially due to operational security concerns or alignment with state-sponsored interests.

Payload Execution and Persistence Mechanisms
Upon successful installation via the compromised extension update, the GlassWorm loader initiates a sequence designed for deep system integration. The primary objective is the establishment of persistence. The malware achieves this by installing a macOS LaunchAgent. LaunchAgents are native system mechanisms that ensure the malicious code executes automatically every time the targeted user logs into their system, guaranteeing long-term, recurring access even after system reboots.
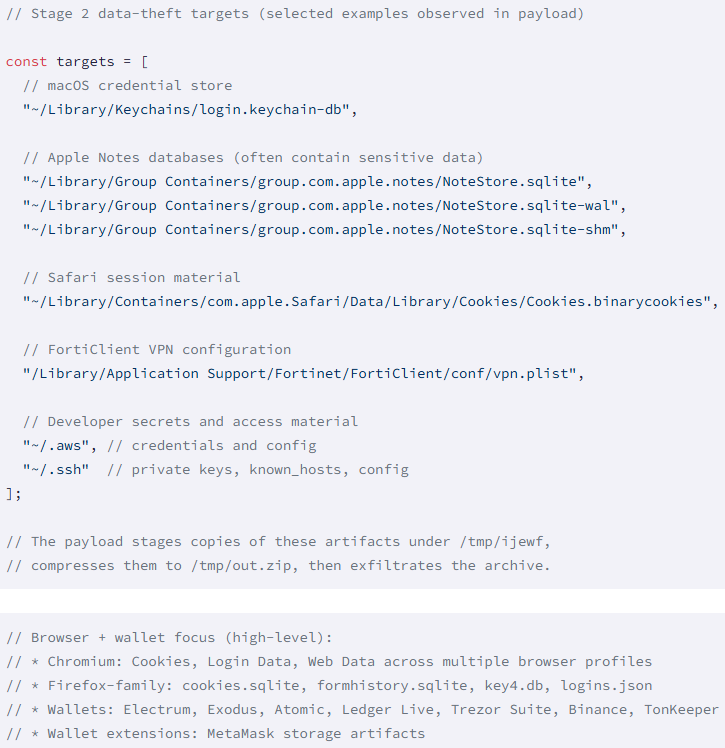
Once persistent, the information stealer component begins its comprehensive sweep of the local filesystem and application data. The scope of data harvesting is alarmingly broad, reflecting a "collect everything" strategy targeting the developer’s digital life:
- Browser Data: Harvesting credentials and session cookies from major browser engines, including Chromium-based browsers and Firefox.
- Cryptocurrency Assets: Targeting data stored in browser wallet extensions and dedicated desktop wallet applications.
- System Secrets: Crucially, attempting to extract data stored in the macOS Keychain, the secure system storage for passwords and keys.
- Productivity and Development Data: Siphoning information from Apple Notes databases, Safari cookies, and sensitive developer secrets potentially stored in project configuration files or code repositories cached locally.
- General Exfiltration: Scanning the entire local filesystem for documents matching specific, high-value keywords or file extensions.
All harvested data is then consolidated and exfiltrated to a centralized command-and-control server, identified by the IP address 45.32.150[.]251. This centralized collection point is the nexus where the threat actor aggregates credentials for subsequent misuse, ranging from financial fraud to corporate espionage.
Industry Implications and Supply Chain Risk
The continued success of GlassWorm highlights a critical vulnerability in the software development lifecycle: the integrity of the third-party package ecosystem. OpenVSX, while promoting open standards and flexibility, operates under a different trust model than the heavily vetted VS Code Marketplace. When a developer account on any platform is compromised, the trust inherent in the extension’s history—sometimes spanning years—is immediately weaponized.
This incident underscores the severe ramifications of software supply chain attacks, particularly within developer tools. Developers rely heavily on these extensions to enhance productivity, but each dependency introduces an unvetted execution path into the environment where the most sensitive intellectual property is created and managed. For organizations, this means that even if their primary code repositories are secure, the tools used to write the code can serve as the initial breach vector.
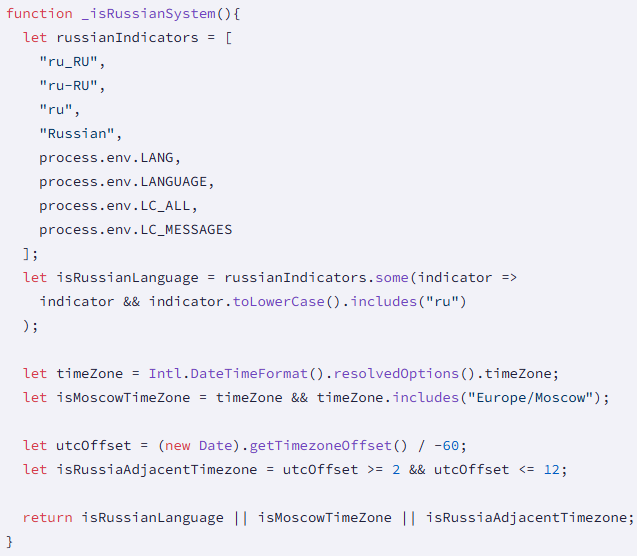
The fact that the malware specifically targets macOS developers suggests a calculated focus on high-net-worth individuals or developers working on sensitive proprietary projects, often correlated with cryptocurrency development or high-value enterprise applications. The exclusion of Russian-locale systems, while potentially indicative of the threat actor’s origin, also speaks to the attacker’s calculated operational security—they are tailoring their attacks to maximize yield while minimizing exposure to law enforcement or intelligence agencies from specific jurisdictions.
Expert Analysis and Mitigation Strategies
From a defensive standpoint, the persistence mechanism via LaunchAgents is standard for macOS malware, but its deployment via a trusted extension update bypasses many traditional perimeter defenses. Security teams must shift focus from network ingress filtering to endpoint integrity monitoring.
Expert Recommendations Moving Forward:
- Enhanced Supply Chain Vetting: Organizations must implement rigorous policies for vetting extensions, even those from seemingly reputable repositories like OpenVSX. This includes checking developer history, monitoring for sudden changes in update frequency, and auditing extension permissions against expected functionality.
- Principle of Least Privilege (PoLP) for IDEs: Development machines should operate under the strictest PoLP. IDEs and associated tools should ideally run in isolated, containerized environments where possible, preventing them from accessing sensitive user credentials (like the Keychain) or broad filesystem access unless absolutely necessary for the specific task at hand.
- Secret Management Over Local Storage: Developers must be strongly discouraged from storing long-lived credentials, API keys, or crypto seeds in local files, browser storage, or the macOS Keychain, especially if they are actively installing third-party extensions. Centralized, hardware-backed secret management solutions are paramount.
- Behavioral Anomaly Detection: Given the nature of the data exfiltration, endpoint detection and response (EDR) solutions must be tuned to flag unusual outbound network connections originating from IDE processes, especially connections to known suspicious IP addresses or high-volume data transfers.
Platform Response and Future Vulnerabilities
In response to the findings, Socket proactively engaged the Eclipse Foundation, the managing body for the OpenVSX platform. The security team confirmed the unauthorized publishing access, successfully revoked the attacker’s tokens, and purged the malicious versions from the registry. This rapid remediation highlights the importance of vendor cooperation in mitigating platform-level threats.
However, one extension, oorzc.ssh-tools, was entirely removed from OpenVSX due to the discovery of multiple malicious releases associated with the compromised account. This complete removal suggests a systemic compromise that made cleaning individual versions impractical or too risky.
While the immediate threat from these specific packages has been neutralized on the marketplace, the crucial directive remains for any developer who installed the compromised versions: a thorough system remediation is non-negotiable. This must include a complete system sweep, followed by the mandatory rotation of every secret, password, and API key accessible from that machine. Trust, once broken via supply chain compromise, cannot be assumed restored.
The future trajectory of GlassWorm, following its demonstrated evolution toward macOS targeting and the exploitation of open-source repositories, suggests that threat actors are increasingly targeting the infrastructure around the source code, rather than the code itself. As development environments become more complex and reliance on third-party tooling deepens, the integrity of these extension marketplaces will remain a primary vector for sophisticated espionage campaigns aimed at extracting digital wealth and proprietary secrets. The sophistication of the environmental checks and the targeted nature of the data theft indicate a highly professional, likely state-backed or financially motivated group dedicated to exploiting the developer supply chain as a soft underbelly of modern software creation.

