The persistent vulnerability of improperly configured MongoDB instances continues to be exploited by threat actors engaged in automated data extortion schemes. These attacks leverage fundamental security oversights—specifically, the failure to restrict public access to database servers—to compromise data, often demanding nominal ransoms for its purported return. This ongoing threat landscape highlights a critical gap in cloud and database security hygiene, where readily available, unauthenticated entry points become immediate targets for opportunistic cybercriminals.
This cycle of exploitation is not new. The database community has contended with widespread, large-scale attacks targeting exposed MongoDB deployments for several years. Previous waves, dating back to 2021, saw thousands of databases wiped clean, sometimes with ransom demands attached, and other times with the data simply destroyed without any financial request. The notoriety of these attacks, often linked to specific campaigns like the "Wormable" variants, established a pattern: if a MongoDB server is accessible over the public internet without proper authentication, it is highly likely to be compromised.
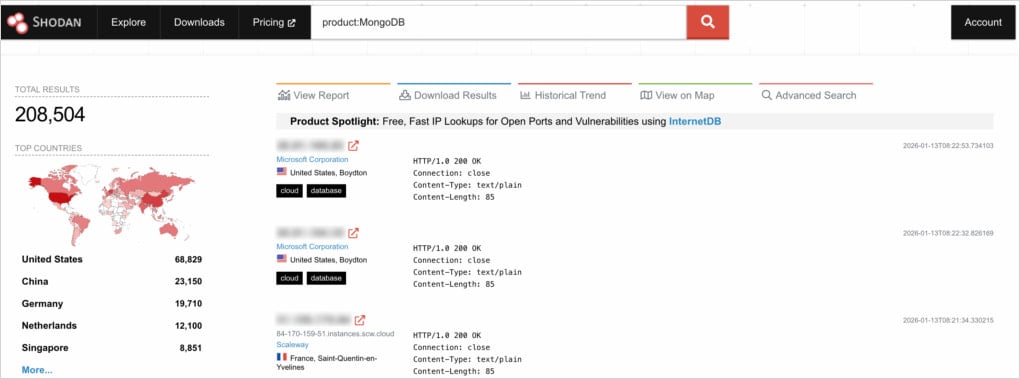
Recent investigative work by security researchers at Flare provides a granular, contemporary view of this enduring problem. Their comprehensive assessment of the global MongoDB footprint accessible via the internet revealed a staggering scale of exposure. The research identified over 208,500 publicly discoverable MongoDB servers. While many of these expose only operational metadata, a significant subset—approximately 100,000 instances—are leaking potentially sensitive operational details. More alarmingly, a subset of 3,100 servers were found to be completely accessible without requiring any form of authentication credentials.

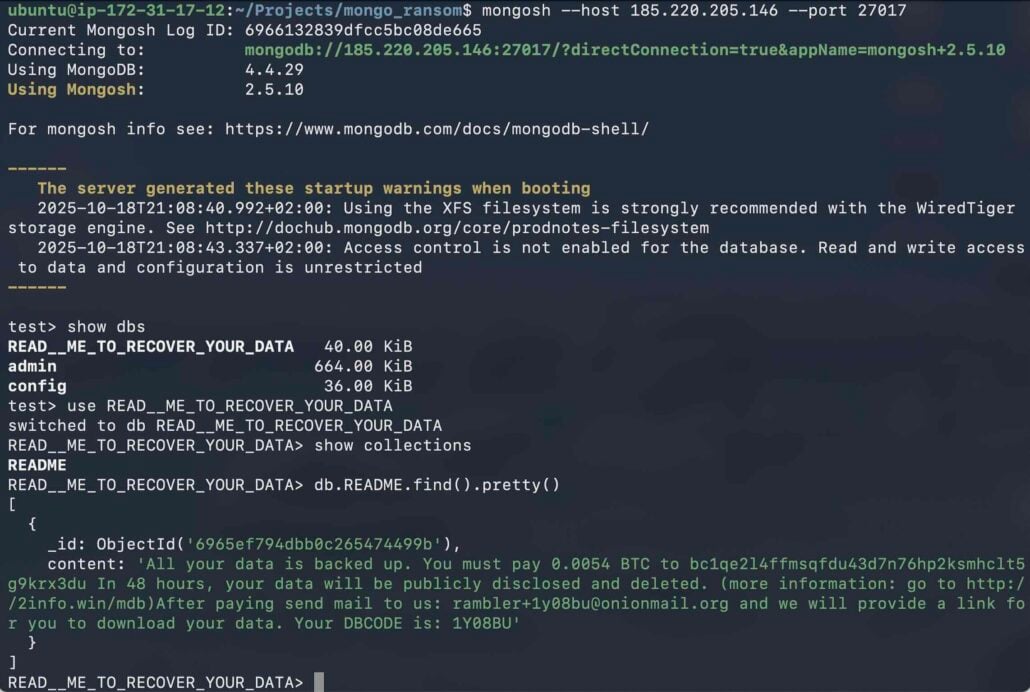
The research painted a grim picture regarding the current state of compromise among these easily accessible targets. Nearly half (45.6%) of the servers that lacked any form of access control had already been successfully targeted by extortionists. In these compromised instances, the data was systematically erased, replaced only by a digital ransom note detailing the required payment and recovery instructions.
The Mechanics of Low-Value Extortion
The current campaign under scrutiny appears highly streamlined and automated, characteristic of low-effort, high-volume cybercrime operations. Analysis of the ransom notes recovered from the compromised systems revealed a striking uniformity in demands. The overwhelming majority of attackers required a payment equivalent to approximately 0.005 Bitcoin (BTC), translating to roughly $500 to $600 USD at current market valuations. The payment window was typically strict, often demanding remittance within 48 hours.
As the Flare report detailed, the core proposition presented to the victims is straightforward: pay the small Bitcoin sum to a specified wallet address, and the threat actor promises to restore the wiped data. However, the inherent risk in engaging with such extortionists is exceptionally high. The report explicitly cautions that "there is no guarantee the attackers have the data, or will provide a working decryption key if paid." This underscores the non-recoverable nature of the loss for most victims who pay, as the primary motivation for these actors is often immediate, low-friction financial gain, not necessarily sustained data recovery services.
A key finding suggesting the involvement of a singular, focused entity was the concentration of cryptocurrency payments. Across all collected ransom notes, researchers identified only five distinct wallet addresses being utilized. One address dominated the landscape, appearing in approximately 98% of the observed extortion attempts. This statistical anomaly strongly implies that a single threat actor, or a tightly coordinated group, is responsible for this specific wave of attacks, refining a successful, low-cost playbook.

Furthermore, the security assessment raised intriguing questions about the remaining exposed, yet uncompromised, servers. Given the high success rate among the truly open databases, the researchers hypothesized that instances that remained untouched might have already succumbed to earlier extortion attempts and paid the ransom, or perhaps they contained non-valuable, easily replaceable data that the current automated scanner ignored.
Beyond Configuration: The Shadow of Outdated Software
While the immediate cause of data destruction is nearly always a lack of authentication—a configuration failure—the research uncovered a secondary, systemic vulnerability exacerbating the risk: software obsolescence.
The investigation into the internet-facing MongoDB servers revealed that nearly half—around 95,000 of the total exposed instances—were running outdated versions of the database software. These older versions are often riddled with known, public vulnerabilities (n-day exploits). While configuration issues provide the direct entry point for data deletion or exfiltration, outdated software introduces pathways for more severe compromises, such as remote code execution (RCE).
Although the direct data-wiping attacks observed primarily exploited open ports, the presence of vulnerable, unpatched systems represents a latent threat. Security experts note that an attacker who gains initial access via a misconfigured port could potentially pivot to leverage an RCE vulnerability in an older version to establish persistent command-and-control, elevate privileges, or exfiltrate data before deleting the database, thereby transforming a data extortion event into a full-scale data breach. The distribution map of Common Vulnerabilities and Exposures (CVEs) across these exposed instances clearly illustrates the widespread reliance on software that no longer receives official security patching.

Industry Implications and the Cloud Native Challenge
The continued targeting of MongoDB is emblematic of a broader industry challenge concerning the security posture of NoSQL databases, particularly within sprawling cloud environments. MongoDB’s flexibility, ease of deployment, and default configurations often clash with the rigorous security mandates required for production systems. Developers prioritizing speed and agility sometimes bypass essential security hardening steps, such as binding MongoDB to internal network interfaces (e.g., localhost or private subnets) or implementing robust access controls via SCRAM authentication or network firewalls.
The implications for businesses are severe. Even if the ransom demand is small—$500 is trivial compared to the cost of downtime or regulatory fines—the loss of data integrity and the operational interruption are significant. For organizations handling sensitive customer data, the incident triggers mandatory disclosure requirements under regulations like GDPR or CCPA, leading to reputational damage far exceeding the cost of the Bitcoin payment.
Furthermore, the rise of automated scanning tools, often powered by services like Shodan, means that the window between a new instance being deployed insecurely and it being discovered by an attacker is virtually instantaneous. This necessitates a shift from reactive remediation to proactive, automated security governance.
Expert Analysis and Mitigation Strategies
Security architects emphasize that the solution to this persistent problem lies not in advanced threat detection, but in fundamental security hygiene. The narrative must pivot away from mitigating active extortion attempts toward preventing the initial exposure.
Flare’s recommendations provide a bedrock for database administration best practices:
- Eliminate Public Exposure: The primary defense is to ensure MongoDB instances are not reachable from the public internet unless absolutely necessary for specific operational requirements. This is achieved by restricting binding addresses to internal or private network interfaces.
- Mandatory Strong Authentication: All accessible instances must employ robust authentication mechanisms (e.g., SCRAM). Default, null, or easily guessed credentials must be strictly prohibited.
- Network Segmentation and Firewalls: Strict enforcement via network policies, whether traditional firewalls or cloud-native security groups/Kubernetes network policies, should whitelist access solely to known, trusted application servers and administrative jump boxes. Any connection attempt originating from an untrusted IP range should be automatically blocked.
- Configuration Discipline: Organizations must avoid the dangerous practice of copying deployment guides verbatim without contextual security review. Configuration templates, especially those designed for quick local testing, often leave default security settings dangerously wide open.
Beyond these preventative measures, continuous vigilance is essential. Database administrators must implement continuous monitoring solutions designed to detect external connectivity to sensitive ports like MongoDB’s default (27017). If an instance is found to be exposed, immediate triage must involve: rotating all associated credentials, isolating the compromised server from the broader network, and performing a deep forensic analysis of access logs to determine the extent of data access or exfiltration prior to the wipe.
The Future Trajectory of Database Attacks
Looking forward, the targeting of easily accessible databases like MongoDB will likely evolve rather than disappear. We can anticipate several trends:
First, threat actors will increasingly integrate initial compromise with data exfiltration before deploying the destructive payload. Instead of merely wiping the database and demanding a small ransom for restoration, future attacks might first siphon off valuable data (PII, intellectual property) and then demand a ransom for the deleted files, effectively conducting a double extortion scheme on the same vulnerable asset.
Second, as organizations adopt more sophisticated orchestration tools like Kubernetes, misconfigurations in network policies (e.g., overly permissive Ingress or Egress rules) will replace simple firewall errors as the primary vector for exposure. Securing containerized environments requires a granular understanding of network segmentation within the cluster, a skillset that remains less mature than traditional perimeter defense.
Finally, the prevalence of outdated software suggests a significant lag in patching cycles for operational data stores. As new zero-day vulnerabilities are discovered in MongoDB versions still in widespread use, the severity of attacks targeting these exposed servers will dramatically increase, moving beyond mere data destruction to potentially achieving full system compromise via RCE. For the foreseeable future, ensuring MongoDB instances are secured, patched, and firewalled remains a foundational requirement for modern data security.

