A sophisticated and aggressive phishing operation is currently inundating global inboxes, leveraging the universal reliance on cloud storage services to induce panic and drive fraudulent purchases. This large-scale campaign centers on fabricated notifications concerning subscription failures or expired payment methods, falsely warning recipients that their accumulated digital assets—including irreplaceable photos, critical documents, and device backups—are slated for immediate suspension or permanent deletion. The sheer volume and repetitive nature of these communications suggest a highly automated, persistent threat actor coordinating a multi-pronged social engineering effort.
Analysis of the circulating malicious emails reveals a clear escalation in the campaign’s maturity over recent months. Victims are reporting receiving multiple, subtly varied versions of the same core threat daily, indicating a high-throughput infrastructure dedicated to maintaining pressure. The primary psychological lever employed across all variations is manufactured urgency. Whether framed as a payment gateway failure or an impending storage limit breach, the underlying message demands immediate user interaction to avert catastrophic data loss.
The Infrastructure of Deception: Analyzing the Attack Vectors
The technical footprint of this campaign is characterized by its opportunistic use of disposable infrastructure designed to evade immediate blacklisting. The originating email addresses present a chaotic facade, employing domains that appear randomly generated or heavily obfuscated, making traditional sender reputation checks unreliable. Samples collected from affected users reveal patterns utilizing random character strings appended to various generic top-level domains (TLDs), such as:
This randomization strategy is a hallmark of modern, high-volume spam operations aiming for short lifespans before domain rotation is necessary.

Complementing the disparate sender addresses are equally diverse subject lines, all meticulously crafted to bypass simple spam filters and trigger an immediate emotional response. These subjects frequently incorporate personalization tokens—the recipient’s name or email address—alongside specific dates or fabricated reference numbers to mimic official correspondence, thereby boosting the perceived legitimacy of the alert.
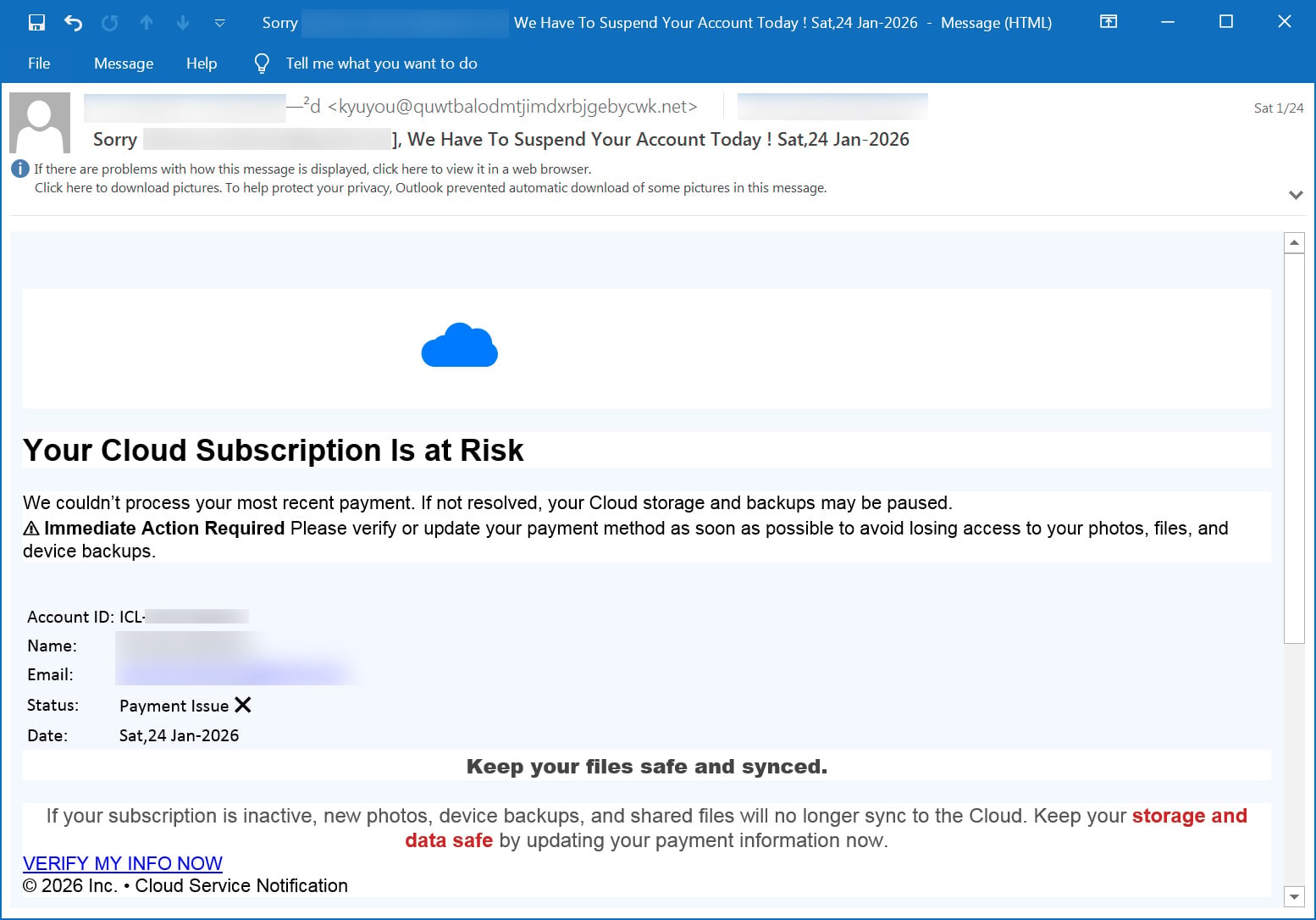
The narrative within the body of the emails consistently focuses on the imminent termination of cloud services due to billing anomalies. Phishing attempts detail failed renewal attempts or expired credit card details, warning that synchronization services will cease and that valuable user data—ranging from personal media to system snapshots—faces erasure. To further anchor this manufactured reality, the messages often embed entirely fictitious metadata, such as made-up account identifiers, transaction numbers, and future expiration dates, lending an air of bureaucratic accuracy to the fraud.
One representative message snippet illustrates the direct, fear-based appeal: "Your Cloud Subscription Is at Risk. We couldn’t process your most recent payment. If not resolved, your Cloud storage and backups may be paused. Immediate Action Required: Please verify or update your payment method as soon as possible to avoid losing access to your photos, files, and device backups."
The Redirect Chain: Exploiting Legitimate Cloud Services
A critical element of this specific campaign’s evasion technique involves the use of trusted infrastructure for the initial click. Rather than linking directly to known malicious domains, the spam emails contain hyperlinks that initially resolve to paths within https://storage.googleapis.com/, a subdomain belonging to Google Cloud Storage.
Threat actors have exploited this by hosting static HTML redirector files on these legitimate, trusted cloud endpoints. When a user clicks the link, the trusted Google URL executes the redirector, which instantly shunts the unsuspecting victim away from the legitimate domain and onto a completely separate, malicious phishing site hosted on a dynamically chosen, unrelated domain. This initial hop leverages the inherent trust associated with major cloud providers, potentially bypassing stricter outbound link scrutiny by email gateways.

The Phishing Lure: Impersonation and Escalation
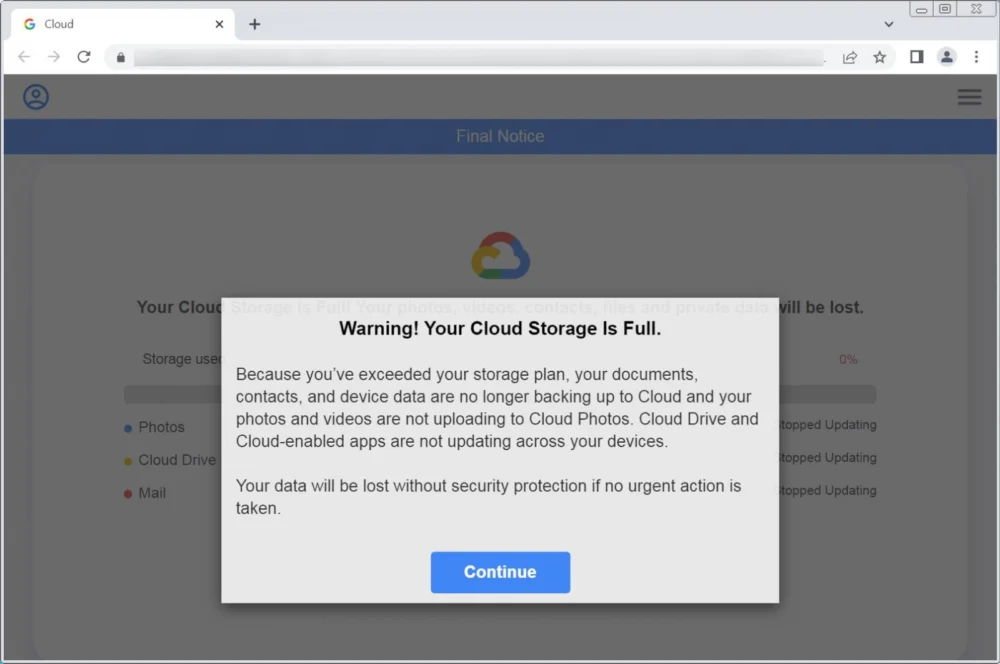
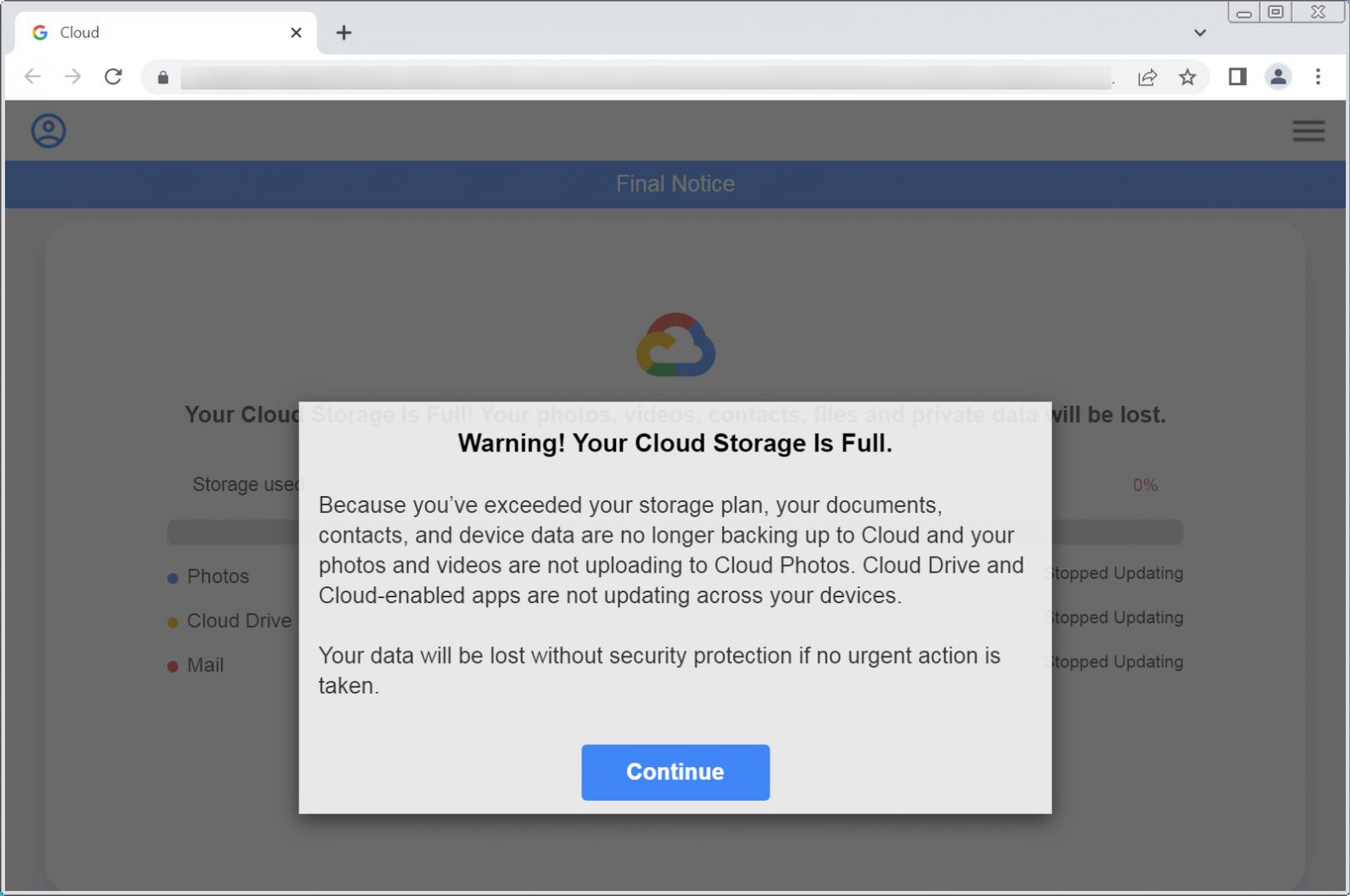
Once redirected, the user lands on a landing page meticulously designed to impersonate established cloud service portals, often prominently featuring familiar branding, including the Google Cloud logo. The immediate message shift pivots from a "payment issue" to a more visceral "storage capacity crisis."
The phishing pages assert that the user has critically exceeded their allocated storage plan. This triggers further alarm bells, stating that vital operations like document synchronization, photo uploads to Cloud Photos, and general application data updates across devices have halted. The message culminates with the threat: "Your data will be lost without security protection if no urgent action is taken."
Upon clicking the mandatory "Continue" button, the victim is subjected to a simulated, high-stakes diagnostic scan. This scan invariably reports that Photos, Cloud Drive, and Mail services are critically full. The narrative then introduces the solution: an urgent need to upgrade storage capacity. Crucially, the attackers offer an artificial sense of value, claiming the victim is eligible for a time-sensitive "loyalty" upgrade at a significant discount, often quoted around 80%.
The True Objective: Affiliate Marketing Fraud
This is the pivot point where the nature of the scam shifts from traditional credential theft (though that remains a risk in similar campaigns) to a highly profitable form of affiliate marketing fraud. Instead of leading to a legitimate payment portal for the cloud service, clicking the "Update Storage" button redirects the user not to Google, Microsoft, or any recognized cloud entity, but to third-party affiliate marketing landing pages.
The products aggressively promoted on these subsequent pages are entirely tangential to cloud storage management. The observed redirections point toward subscriptions for VPN services, niche security software of dubious provenance, and various other recurring subscription offerings. The final destination is typically a checkout form designed solely to harvest credit card information.
The threat actors profit not by stealing cloud account credentials directly, but by generating referral revenue for every unnecessary subscription the victim purchases under the false pretense of resolving their "storage crisis." This model capitalizes on the user’s panic, leading them to buy products they neither need nor understand, believing this purchase is the necessary remedy for their imminent data loss.
Industry Implications and Expert Analysis
This campaign highlights several critical vulnerabilities in the current digital ecosystem.
1. The Ubiquity of Cloud Trust: The success of this fraud hinges on the deep, ingrained trust users place in cloud providers. Attackers exploit this by borrowing brand recognition. Furthermore, the initial use of Google Cloud infrastructure for redirection demonstrates a sophisticated understanding of how security tools prioritize traffic originating from highly reputable domains.
2. The Efficacy of Fear-Based Social Engineering: In an era saturated with security warnings, threats targeting irreplaceable data (like family photos) remain highly effective. The threat of immediate, permanent data loss bypasses the rational evaluation process that users might apply to, for instance, a generic financial phishing attempt.
3. The Shift to Affiliate Fraud: While many phishing campaigns aim for direct account takeover or ransomware deployment, this specific operation indicates a strategic pivot towards affiliate monetization. This model is often lower risk for the attacker regarding legal traceability, as the primary transaction occurs outside the direct phishing ecosystem, making attribution more complex.
Best Practices and Institutional Response
For cybersecurity professionals and end-users, recognizing the deviations from standard provider behavior is paramount. Legitimate cloud providers adhere to strict protocols regarding account suspension and data retention:
- Grace Periods: Major providers like Google Drive and Microsoft OneDrive do not immediately delete data upon a failed payment. Google, for instance, provides a multi-month grace period (up to two years for Drive content after cancellation) before purging data. Immediate deletion is a hallmark of extortion or fraud.
- No Third-Party Upsells: Legitimate billing notifications direct users to the official platform or a dedicated, secure billing subdomain. They do not redirect users to perform system scans or offer deep discounts on unrelated security software or VPNs to rectify storage issues.
The recommended defense strategy against this pervasive threat is absolute vigilance regarding link inspection and process verification. Users must be trained to recognize the "bait-and-switch" redirection technique. If an email purports to be from a cloud service regarding an urgent billing or storage matter, the only safe course of action is to manually navigate to the service’s official website or open the dedicated mobile application to check the account status directly. Ignoring unsolicited alerts and verifying all critical account information through known, trusted channels remains the most effective mitigation against this financially motivated, anxiety-driven phishing wave.
Future Trends: Deeper Integration and Synthetic Identity
Looking forward, campaigns of this nature are likely to evolve in sophistication. We anticipate future iterations incorporating more advanced tactics:
- AI-Generated Content: The quality of the email prose and the impersonation of tone will likely improve further using generative AI, reducing linguistic errors that currently serve as minor indicators of compromise.
- Voice Phishing Integration: Following successful email engagement, attackers may attempt to leverage harvested names and account identifiers in subsequent vishing (voice phishing) attempts, claiming to be customer support agents attempting to "secure the account" over the phone.
- Targeted Metadata Use: As attackers gain access to larger data breaches, future scams might incorporate highly specific, real metadata (e.g., a real last transaction date or a specific device ID) harvested from past breaches to lend unprecedented credibility to their fraudulent notifications, making manual verification by the user even more difficult.
The ongoing proliferation of these affiliate fraud schemes underscores a permanent reality in the threat landscape: as digital reliance grows, so too does the ingenuity of those seeking to exploit user anxiety surrounding data accessibility and security.