The era of the New Technology LAN Manager (NTLM) protocol, a foundational element of Windows networking security for over three decades, is drawing to a close. In a significant move aimed at hardening the security posture of its operating systems against modern cyber threats, Microsoft has formally declared that NTLM will be disabled by default in forthcoming iterations of Windows client and server operating systems. This decisive action targets the protocol’s inherent cryptographic weaknesses, which have long served as a significant entry vector for sophisticated attacks targeting enterprise environments.
NTLM, first introduced alongside Windows NT 3.1 in 1993 as the successor to the deprecated LAN Manager (LM) protocol, operated on a challenge-response mechanism. While revolutionary for its time, its architecture has proven unable to withstand contemporary adversarial techniques. Since the debut of Windows 2000, the industry standard for domain authentication has decisively shifted to Kerberos, a far more robust, ticket-based protocol that offers superior protection against credential harvesting. Despite Kerberos being the established default on domain-joined systems for years, NTLM has persisted, primarily serving as a critical, yet vulnerable, fallback mechanism for scenarios where Kerberos authentication fails or is unavailable. This persistent reliance on NTLM—even as a contingency—creates an unacceptable security overhang for organizations prioritizing a hardened digital perimeter.
The Anatomy of a Legacy Vulnerability
The persistence of NTLM is directly correlated with its widespread exploitation across the threat landscape. Security researchers and threat actors alike have weaponized the protocol’s design flaws extensively. The most notorious category of exploitation involves NTLM Relay Attacks. In these scenarios, an attacker compromises an intermediary network device or service and subsequently forces that device to authenticate to a target server using the compromised device’s existing NTLM credentials. This effectively allows an attacker to impersonate a legitimate network entity without ever needing to crack the actual password hash.
This vulnerability vector has been repeatedly exploited through a succession of escalating attacks that circumvent mitigation efforts. High-profile examples include PetitPotam, ShadowCoerce, DFSCoerce, and the later discovered RemotePotato0. These exploits demonstrated that even when Microsoft implemented defenses aimed at blocking NTLM relay, creative manipulation of the protocol’s handshake process could still force authentication, leading to privilege escalation and, in the most severe cases, complete compromise of the Windows domain infrastructure.

Furthermore, NTLM is the foundational target for Pass-the-Hash (PtH) attacks. Unlike traditional credential theft, PtH does not require attackers to crack the NTLM hash (the cryptographic representation of the password) into plaintext. Instead, the stolen hash itself is used to authenticate to other network services that still accept NTLM. This technique enables rapid lateral movement across a compromised network, allowing threat actors to escalate privileges stealthily and exfiltrate sensitive data far from the initial point of compromise. The continued presence of NTLM in the default configuration essentially keeps the front door unlocked for these legacy attack patterns.
The Phased Migration to Secure Defaults
Microsoft’s announcement, framed within a broader strategic mandate toward passwordless and phishing-resistant authentication, signals a decisive break from this legacy burden. The move is not an immediate removal of the protocol, which would undoubtedly cause immediate operational collapse in environments slow to modernize, but rather a structured transition to a secure-by-default posture.
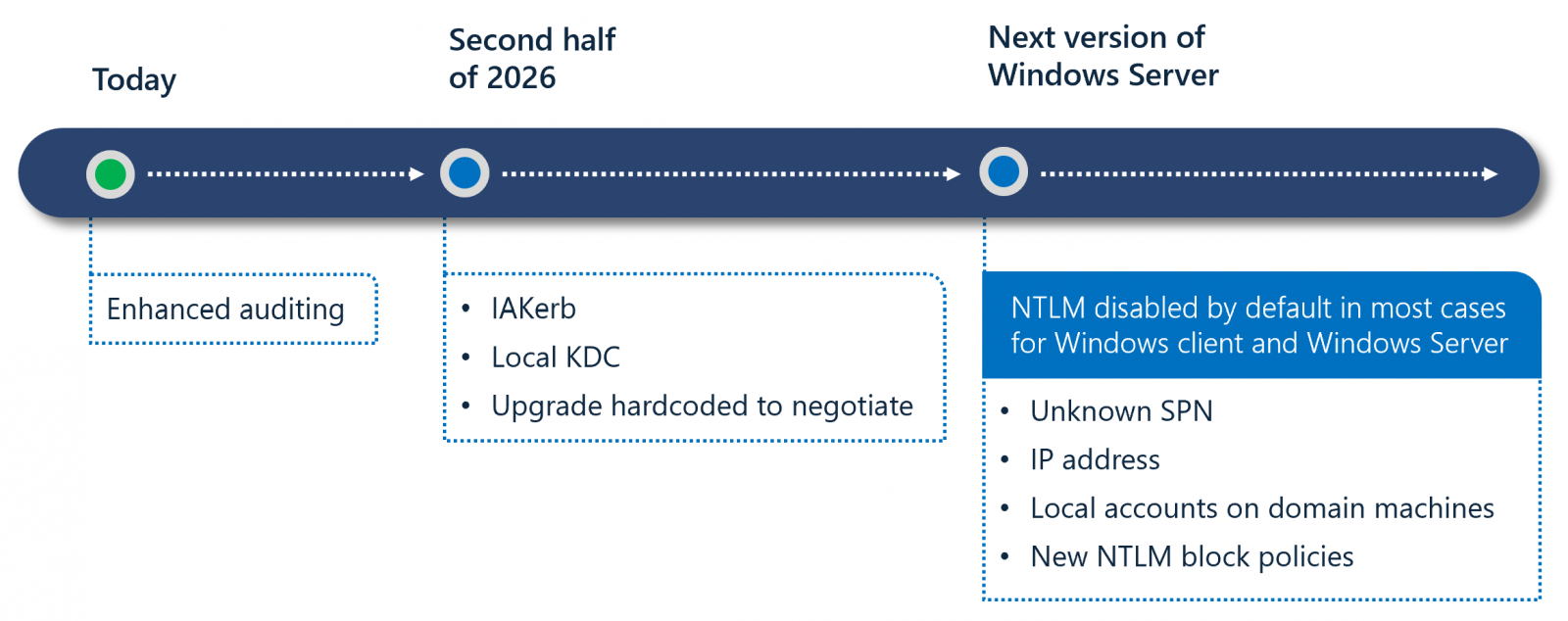
The plan is articulated across three distinct phases, designed to provide necessary visibility and remediation time for IT administrators:
Phase One: Enhanced Visibility (Current/Near Term)
This initial stage, active in Windows 11 version 24H2 and Windows Server 2025, focuses entirely on discovery. Microsoft is embedding advanced auditing tools directly into these operating systems. The primary goal for administrators is to leverage these tools to map out precisely where NTLM is still being invoked within their unique organizational ecosystems—identifying legacy applications, specific services, or third-party integrations that rely on it as a dependency.
Phase Two: Bridging the Gap (Scheduled for H2 2026)
This phase centers on engineering solutions to eliminate the technical rationale for NTLM fallback. Microsoft plans to introduce critical new features designed to satisfy the requirements of legacy communication flows using modern protocols. Key among these are the planned debut of IAKerb (Interactive Authentication Kerberos) and the Local Key Distribution Center (KDC). The Local KDC, for instance, aims to allow domain-joined machines to negotiate Kerberos tickets locally, thereby removing the dependency on network connectivity to the primary domain controller for authentication handshakes that often defaulted to NTLM when connectivity was intermittent or delayed.

Phase Three: The Secure Default (Future Releases)
This is the culmination of the initiative. In subsequent major releases following the preparatory phases, network NTLM authentication will be disabled out-of-the-box. The protocol binaries will remain technically present within the OS—a necessary concession to potential deep-seated legacy requirements—but their activation will require explicit administrative intervention via policy controls. In essence, organizations will have to actively opt-in to using the insecure protocol, rather than administrators having to remember to opt-out.
As Microsoft stated, this transition ensures that "Windows will be delivered in a secure-by-default state where network NTLM authentication is blocked and no longer used automatically." The operating system will prioritize modern, Kerberos-based, or other advanced authentication mechanisms.
Industry Implications and the Burden of Remediation
The decision carries significant weight for IT departments managing heterogeneous or aging IT infrastructure. While the security benefits are undeniable, the practical implementation requires substantial effort. Microsoft has been issuing warnings about NTLM’s obsolescence since 2010, and formally deprecated the protocol in July 2024, urging developers to migrate to Kerberos or the more flexible Negotiation protocol. However, many enterprises still operate under the assumption that legacy systems, particularly in specialized manufacturing, legacy financial services, or on-premises industrial control systems (ICS), will function correctly.
The primary implication is a potential, albeit manageable, service disruption wave if Phase One auditing is ignored. Any application, print spooler, network share access, or inter-process communication (IPC) that implicitly falls back to NTLM when Kerberos negotiation fails will cease functioning correctly when the default is flipped in Phase Three.
From an architecture perspective, this move accelerates the industry-wide trend toward Identity as the New Perimeter. As organizations move workloads to the cloud and adopt zero-trust models, reliance on traditional network-centric authentication like NTLM becomes anachronistic. Kerberos, tied to Active Directory domain structures, is already undergoing modernization (e.g., with Azure AD integration), but NTLM’s removal solidifies the commitment to context-aware, strong authentication.
Expert Analysis and Future Security Trajectory
Security architects view this development as long overdue. Dr. Eleanor Vance, a principal security consultant specializing in identity infrastructure, noted: "NTLM has been technical debt codified into the OS for too long. The fact that exploits like PetitPotam and DFSCoerce could consistently subvert mitigations proves the fundamental weakness of its design. For CISOs, the calculus is simple: the risk of a domain takeover via NTLM relay far outweighs the administrative inconvenience of migrating an old line-of-business application."
The introduction of the Local KDC is a particularly insightful engineering decision. It suggests Microsoft recognizes that environmental factors—such as latency, temporary network segmentation, or reliance on older domain controller configurations—are often the proximate causes for NTLM fallback in corporate settings. By providing a local, self-contained KDC capability, Microsoft is engineering resilience into Kerberos, rather than relying on the inherently weak NTLM safety net.
The timeline also reflects a maturing regulatory environment. As governments and compliance bodies increasingly mandate strong authentication standards (like NIST 800-63B), maintaining default settings that rely on 1990s cryptography becomes an active liability rather than a passive risk. Organizations lagging in migration face not only technical risk but also increased audit scrutiny.
Looking ahead, the complete eradication of NTLM is the ultimate goal. While Phase Three disables it by default, its continued presence, even as an opt-in, suggests that Microsoft anticipates some fringe scenarios—perhaps isolated test labs or highly specialized embedded systems—will require its temporary use until final decommissioning can be achieved. The critical shift is moving the burden of proof: security must now be the default state, and insecurity must require explicit, documented justification. This move aligns Windows security frameworks with contemporary best practices seen across other major enterprise platforms that have already deprecated their own legacy authentication protocols. The next few years will be characterized by a significant, but ultimately beneficial, refactoring of domain authentication practices across the enterprise IT landscape.

