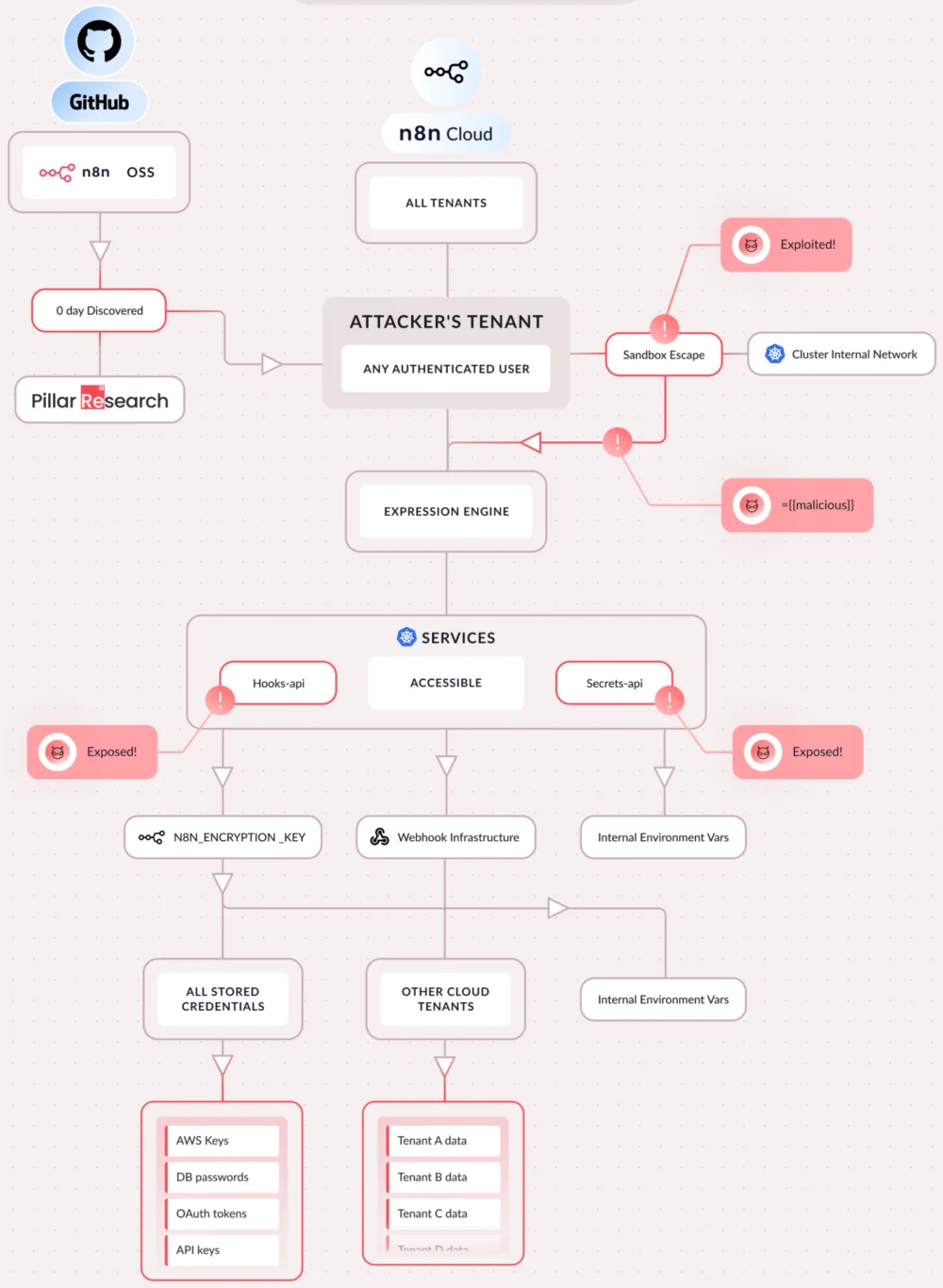
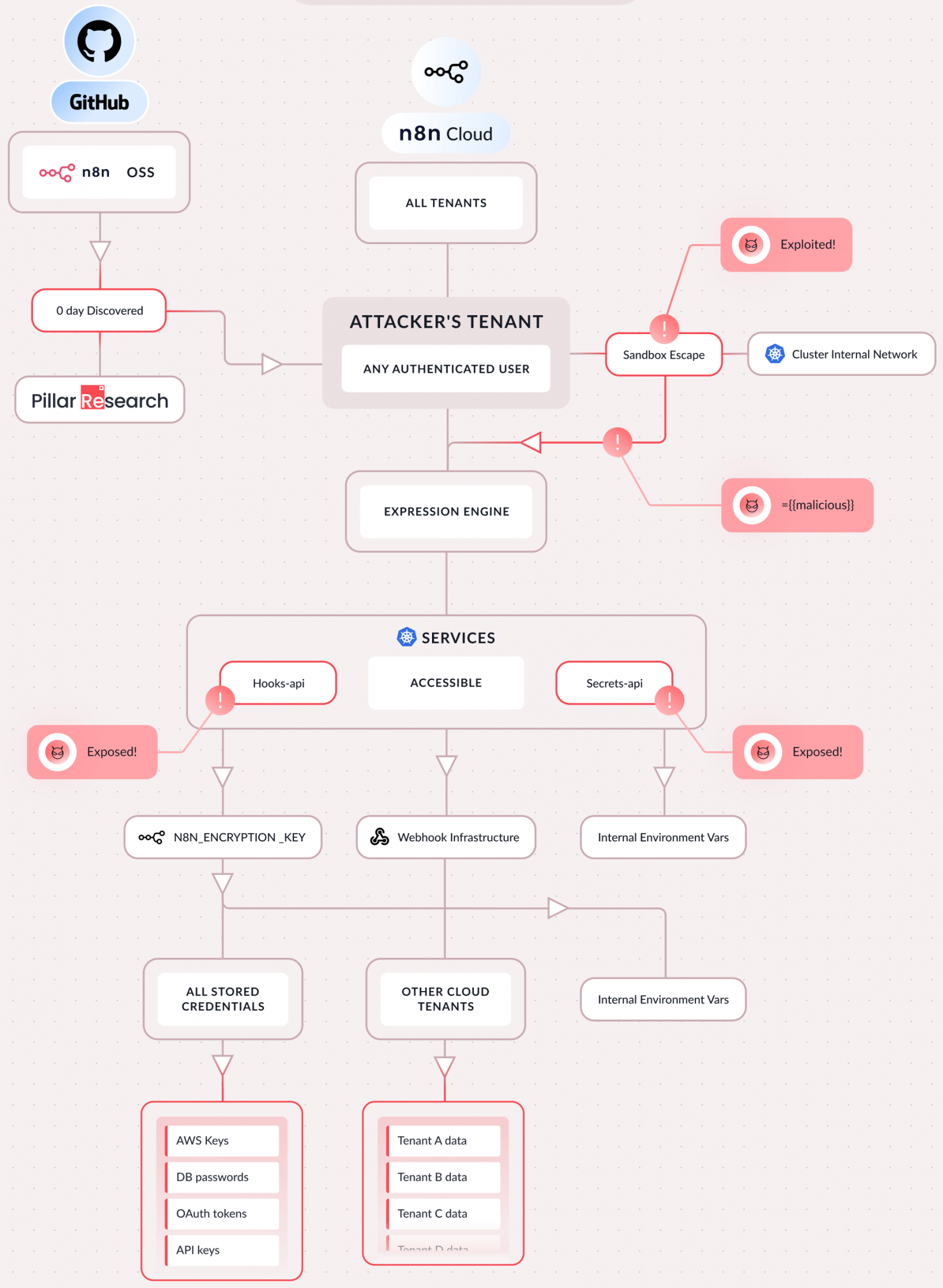
The digital ecosystem is currently grappling with the fallout from the disclosure of a severe vulnerability chain within n8n, the widely adopted open-source platform for workflow automation. Designated as CVE-2026-25049, this critical set of flaws permits any authenticated user with standard workflow creation or editing privileges to execute arbitrary code remotely, effectively achieving complete command and control over the hosting server. This represents a significant escalation in security risks for organizations relying on n8n to orchestrate critical business processes, particularly those involving sensitive data and AI integration.
The discovery, coordinated across multiple independent cybersecurity research entities, highlights a fundamental weakness in n8n’s security architecture, specifically related to the handling and sanitization of user-defined server-side JavaScript expressions embedded within automated workflows. Alarmingly, CVE-2026-25049 represents a direct circumvention of a recent patch addressing CVE-2025-68613, a prior critical vulnerability that the n8n development team had only managed to address on December 20th of the previous year. This rapid regression underscores deep-seated challenges in securing execution environments that dynamically process user input.
The Severity of Unrestricted Remote Code Execution
The implications of a successful exploitation of CVE-2026-25049 are catastrophic for an affected n8n instance. As detailed by researchers at Pillar Security, the vulnerability grants attackers the capability to achieve total compromise of the platform. This includes the unfettered ability to execute system commands at the host level, leading directly to the exfiltration of all stored secrets. This encompasses proprietary API keys, sensitive OAuth tokens, database credentials, and critical configuration files that underpin the organization’s operational continuity.
Beyond data theft, the exploit grants deep access to the underlying filesystem and internal network topology connected to the n8n server. Crucially, in modern infrastructure where automation platforms often serve as central nervous systems, this access can be leveraged for lateral movement. Researchers demonstrated the ability to pivot into connected cloud accounts and, most disturbingly in the current technological climate, hijack integrated AI workflows. This hijacking capability means an attacker could intercept sensitive user prompts intended for large language models, silently modify model responses, or redirect outbound traffic to malicious endpoints, fundamentally compromising data integrity and privacy associated with AI services.
Furthermore, n8n is frequently deployed in multi-tenant architectures, where different business units or external partners might utilize the same deployment instance. The ability to access internal cluster services via this sandbox escape raises the specter of cross-tenant data contamination and unauthorized access to data belonging to unrelated entities sharing the same computational substrate. As Pillar Security succinctly summarized the severity, "The attack requires nothing special. If you can create a workflow, you can own the server." This low barrier to entry—requiring only basic authenticated access—amplifies the risk profile exponentially.

Technical Deep Dive: The Flaw in Sandboxing Logic
The root cause of CVE-2026-25049 lies in what Pillar Security describes as an "incomplete AST-based sandboxing" mechanism. Workflow automation tools often rely on executing user-defined scripts (in this case, JavaScript) within a restricted environment, or sandbox, to prevent malicious code from interacting with the host operating system. The sophistication of this vulnerability lies in its ability to break out of this intended isolation.
The initial chain of exploitation, demonstrated to the n8n team on December 21, 2025, involved a chained bypass that successfully escaped the sandbox and gained access to the Node.js global object. Gaining access to this object is tantamount to achieving Remote Code Execution (RCE), as it exposes core JavaScript execution capabilities that can be manipulated to invoke underlying system functions. While an initial patch was deployed two days later, the subsequent analysis revealed that this fix failed to address equivalent operations achievable through different procedural pathways. A second, distinct escape mechanism persisted, confirming the patch’s inadequacy. Confirmation of this second bypass was provided to n8n developers on December 30th, leading to the final, comprehensive fix rolled out in version 2.4.0 on January 12, 2026.
Independent verification of the RCE potential came from Endor Labs, whose researchers developed a straightforward Proof-of-Concept (PoC) exploit. Cristian Staicu of Endor Labs pinpointed a specific failure in runtime enforcement: "In all versions prior to 2.5.2 and 1.123.17, the sanitization function assumes keys in property accesses are strings in attacker-controlled code." This assumption, while perhaps reflected in the higher-level TypeScript definitions used during development, was demonstrably not enforced rigorously at the actual JavaScript runtime level. This disparity created a classic type-confusion vulnerability, allowing attackers to slip past the intended security guardrails entirely and invoke arbitrary code execution pathways.
SecureLayer7 researchers also independently validated the vulnerability, focusing on achieving "server side JavaScript execution using the Function constructor." Their investigative journey, which involved over 150 iterative attempts to refine a working bypass after analyzing the failed patch for CVE-2025-68613, underscores the difficulty in correctly securing dynamic code execution environments. Their detailed report provides comprehensive technical documentation and a working PoC, laying bare the steps required to transition from a standard user to a full server administrator.
Industry Implications: The Trust Deficit in Workflow Automation
The proliferation of platforms like n8n is a direct consequence of the growing need for rapid, low-code integration across disparate enterprise systems. These platforms democratize automation, allowing non-developers to stitch together complex operational sequences. However, this very flexibility—the ability to execute arbitrary code derived from user input—is the source of the current crisis.
This incident forces a crucial industry reckoning regarding the security model of "sandboxed" execution in open-source automation tools. Historically, sandboxing mechanisms for user-supplied code, especially JavaScript running server-side, have proven notoriously difficult to implement perfectly. Languages that permit extensive metaprogramming or dynamic object manipulation, like JavaScript, present an environment where subtle misconfigurations in access control or type checking can lead to catastrophic escape scenarios.

For enterprises, the immediate implication is a crisis of trust in the tools they have deployed to enhance efficiency. If an automation platform—which inherently requires access to the most sensitive parts of the IT estate (e.g., CRM data, financial APIs, infrastructure management)—can be compromised by a low-level authenticated user, the entire security perimeter built around that platform is rendered moot. The focus shifts from perimeter defense to internal integrity, demanding rigorous validation of any code that runs within the platform boundary.
The impact on CI/CD pipelines and DevOps practices is also noteworthy. As n8n workflows increasingly replace manual steps in deployment and operational verification, a compromised n8n instance becomes a high-value target for supply chain attacks, allowing an adversary to inject malicious code or configuration changes upstream before deployment.
Contextualizing the Threat: A Pattern of Escalation
It is important to view CVE-2026-25049 within the broader context of recent security challenges facing n8n. The platform’s rising popularity—driven by its flexibility and open-source nature—has inevitably attracted heightened scrutiny from threat actors.
This most recent critical flaw follows closely on the heels of the "Ni8mare" vulnerability (CVE-2026-21858), a flaw that also allowed for severe server hijacking. Security intelligence firms, such as GreyNoise, have already begun documenting reconnaissance activity targeting exposed n8n endpoints vulnerable to Ni8mare. Reports indicate monitoring of at least 33,000 requests directed at vulnerable webhooks between late January and early February, with scanning patterns indicative of searching for sensitive filesystem artifacts like the /proc directory—a classic indicator of post-exploitation reconnaissance aimed at privilege escalation or persistence.
While there are currently no confirmed public reports of active exploitation targeting CVE-2026-25049, the immediate availability of public PoCs suggests that exploit development is likely already underway in underground channels. The combination of a high-severity RCE vulnerability tied to standard user privileges, coupled with active scanning for adjacent vulnerabilities on the same platform, creates an urgent remediation scenario.
Expert Recommendations and Future Trajectories
For all organizations utilizing n8n, immediate action is paramount. The primary defense vector remains updating the platform to the patched versions: 1.123.17 or 2.5.2, depending on the deployment branch utilized. Beyond patching, security teams must assume a potential compromise may have already occurred.
Pillar Security strongly advises an aggressive remediation posture that includes:
- Credential Rotation: Immediately rotating the primary
N8N_ENCRYPTION_KEY, as this key is used to decrypt secrets stored within the platform database. Simultaneously, all API keys, tokens, and credentials stored or accessed by n8n workflows must be regenerated. - Workflow Audit: A comprehensive security audit of all existing workflows must be undertaken to identify any suspicious or overly permissive JavaScript expressions that might have been introduced prior to the patch.
For environments where immediate patching is technically infeasible—such as during highly controlled maintenance windows—the n8n team has provided a temporary mitigation strategy. However, security professionals must treat this workaround as a stopgap, not a permanent solution, as it is designed to restrict access patterns rather than eliminate the underlying type-confusion flaw.
Looking forward, this incident serves as a powerful case study on the inherent security challenges of "bring-your-own-code" automation environments. The future of secure workflow automation will likely pivot toward solutions that either employ more robust, language-agnostic execution environments (like WebAssembly or highly constrained containerized runtimes) or mandate a more declarative approach to workflow definition, minimizing the need for developers to write raw server-side JavaScript within the platform’s execution context. The industry must prioritize deep runtime introspection and verifiable security guarantees over simple textual sanitization to prevent future bypasses of this critical nature. The era of relying on simple Abstract Syntax Tree (AST) checks for code safety in dynamic environments appears to be rapidly concluding.