The consumer digital safety and identity protection giant, Aura, has publicly acknowledged a significant security incident involving the unauthorized exfiltration of customer data. While the precise number remains subject to slight variation between internal reporting and third-party analysis, the breach impacts a substantial segment of marketing contacts, nearing the one million mark. This event serves as a potent case study in the multifaceted nature of modern cybersecurity risks, highlighting vulnerabilities stemming not only from technical oversights but also from human error and the lingering risks associated with mergers and acquisitions.
Aura, a firm positioning itself as a comprehensive shield against digital threats—offering identity theft protection, credit monitoring, fraud alerts, and anti-phishing tools—confirmed that the breach originated following a successful voice phishing (vishing) attack directed at an employee. This social engineering vector is increasingly favored by threat actors due to its high success rate against even well-trained personnel, bypassing traditional perimeter defenses that focus on email-borne malware or network intrusions. The compromised data primarily consists of contact information belonging to approximately 20,000 current customers and 15,000 former customers, though the total scope of exposed records approaches 900,000 when factoring in legacy marketing lists.
Crucially, Aura has asserted that the most sensitive data categories—specifically Social Security Numbers (SSNs), encrypted or plain-text account passwords, and core financial instruments—were successfully segregated and remained untouched by the intrusion. The exposed Personally Identifiable Information (PII) is limited to names, email addresses, residential addresses, and telephone numbers. However, the exposure of physical addresses alongside contact details significantly elevates the risk profile for targeted spear-phishing, physical fraud attempts, or sophisticated identity reconnaissance.
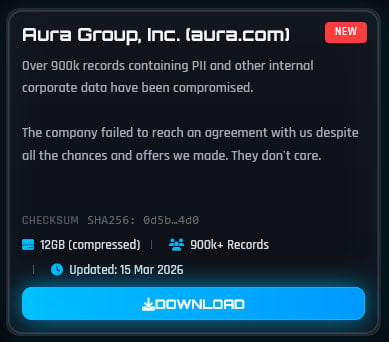
The timeline of disclosure was accelerated by the activities of the notorious data extortion collective, ShinyHunters. This group publicly claimed responsibility for the attack on their data marketplace, asserting they had successfully pilfered approximately 12 gigabytes of proprietary and customer information. Furthermore, ShinyHunters escalated the pressure by publishing samples of the alleged stolen files, claiming that negotiations had broken down despite their purported attempts to reach a settlement with Aura. This tactic of immediate public data leakage is characteristic of modern ransomware and extortion operations, designed to force rapid capitulation from victims by creating immediate reputational and compliance damage.
The Legacy Data Dilemma: Mergers and Technical Debt
A significant nuance in Aura’s official statement relates to the provenance of the bulk of the exposed data. The company clarified that a large portion of the affected records did not originate from their core, modern infrastructure. Instead, the data was inherited from a third-party marketing platform acquired during a corporate merger back in 2021.

This scenario underscores a critical industry implication: the enduring cybersecurity debt created by mergers and acquisitions (M&A). When organizations integrate, the acquired entity often brings with it disparate technology stacks, outdated security protocols, and legacy databases that may not meet the acquiring company’s contemporary security standards. In this instance, the marketing tool’s database, though containing records for only about 35,000 individuals directly linked to Aura’s current customer base, became the vector that ballooned the exposure count. The remaining volume likely consists of leads, prospects, or individuals from the acquired entity’s previous operations, now aggregated under Aura’s umbrella.
The discrepancy between Aura’s reported figure and the count derived by independent analysis services further illustrates the complexity of tracking data lineage post-acquisition. The Have I Been Pwned (HIBP) service, which cataloged the leaked information, identified slightly over 901,000 unique email addresses. While HIBP noted that approximately 90% of these addresses were already known from previous breaches, the exposure of the remaining 10% (or approximately 90,000 unique individuals) to this specific incident represents a novel risk vector for those users. HIBP analysis also indicated the exposure of customer service interaction logs and associated IP addresses—metadata that can be invaluable for threat actors seeking to map user behavior or bypass subsequent authentication steps.
Expert Analysis: The Vishing Attack Vector
The confirmed cause—a voice phishing attack—demands heightened scrutiny. Vishing bypasses security awareness training focused on spotting malicious links or attachments in emails. Threat actors utilizing vishing often impersonate trusted internal IT support, high-level executives (whaling), or even external regulatory bodies. The goal is typically to coerce an employee into divulging multi-factor authentication (MFA) codes, resetting passwords, or granting remote access to a system.
In the context of an identity protection firm, the attacker may have specifically targeted employees with access to marketing databases, perhaps posing as a vendor requiring urgent credential verification or system maintenance. The success of this attack suggests a potential lapse in layered authentication protocols or inadequate monitoring of privileged access escalation initiated via voice command. For a company whose core business is mitigating digital risk, a breach originating from a basic social engineering tactic presents a significant reputational challenge, inviting skepticism regarding the robustness of their internal defenses.
Industry Implications and Regulatory Scrutiny
The repercussions of this incident extend beyond Aura’s immediate operational adjustments. For the identity protection sector, trust is the primary currency. Consumers subscribe to services like Aura precisely because they fear their data—often including highly sensitive financial or governmental identifiers—will be compromised. When the protector itself suffers a breach, even one confined to marketing contacts, it triggers a crisis of confidence across the entire industry. Competitors will undoubtedly leverage this event in their marketing, emphasizing their superior security postures, while regulators globally will be scrutinizing Aura’s incident response timelines and adherence to data protection statutes like GDPR or CCPA, especially given the inclusion of physical addresses.
The nature of the exposed data—contact information—also has profound implications for the future landscape of digital deception. While SSNs were spared, the combination of full names, addresses, and phone numbers is sufficient to execute highly effective "SIM-swapping" attacks, where an attacker convinces a mobile carrier to transfer a victim’s phone number to a device they control. Once a phone number is hijacked, the attacker can intercept one-time passwords (OTPs) sent via SMS, effectively bypassing MFA for accounts that rely on SMS verification, including banking, cloud services, and, potentially, Aura’s own customer portals if not strictly protected by stronger MFA methods.
Future Impact and Mitigation Trends
Aura’s immediate next steps—in-depth internal review with external experts and engagement with law enforcement—are standard and necessary. However, the long-term mitigation strategy must address both the immediate legacy data issue and the systemic vulnerability exploited.
Firstly, the company must complete a comprehensive audit of all inherited systems from the 2021 acquisition, isolating and modernizing or decommissioning any platform that lacks stringent security controls. This process, often termed "security harmonization," needs to prioritize data minimization: determining if the legacy marketing database is still necessary for business operations and, if not, securely purging it.
Secondly, the vishing vector requires an aggressive countermeasure. This typically involves mandatory, scenario-based training that simulates high-pressure social engineering tactics, coupled with stringent verification protocols for any request for credential changes or system access, regardless of the caller’s asserted authority. Furthermore, organizations in high-risk sectors like cybersecurity should consider migrating away from SMS-based MFA entirely, adopting hardware tokens (like YubiKeys) or time-based one-time password (TOTP) apps, which are inherently resistant to SIM-swapping and many vishing scenarios.
The incident serves as a stark reminder that cybersecurity is not a static achievement but a continuous process of risk management. Even when core, high-value assets are defended, the periphery—legacy systems, third-party integrations, and the human element—remains the most vulnerable seam, capable of exposing hundreds of thousands of records through a single, well-executed social engineering exploit. The industry must now watch how Aura manages the remediation and notification process to rebuild the trust essential for a company whose entire value proposition rests on digital safety assurance. The next few months will reveal the true cost, both financial and reputational, of failing to fully integrate security into corporate expansion.

