The perennial complexity of the Windows operating system, particularly its legacy components, continues to provide fertile ground for security researchers to uncover subtle yet significant avenues for malicious manipulation. Recently, at the Wild West Hackin’ Fest, security researcher Wietze Beukema brought to light a suite of previously undocumented techniques leveraging the inherent structure of Windows LNK (shortcut) files. These methods enable sophisticated deception, allowing an attacker to display one target path to an end-user while the operating system executes an entirely different, malicious payload upon double-clicking the shortcut.
Beukema’s detailed exposition outlined four distinct vectors for this LNK spoofing, fundamentally rooted in how Windows Explorer parses and prioritizes conflicting information embedded within the shortcut file’s intricate binary format. Introduced with Windows 95, the LNK format is surprisingly verbose, incorporating multiple data structures to define target paths, working directories, and command-line arguments. It is the ambiguity and the specific order of operations during the parsing of these structures that malicious actors can exploit.
The Mechanics of Deception: Exploiting Parsing Precedence
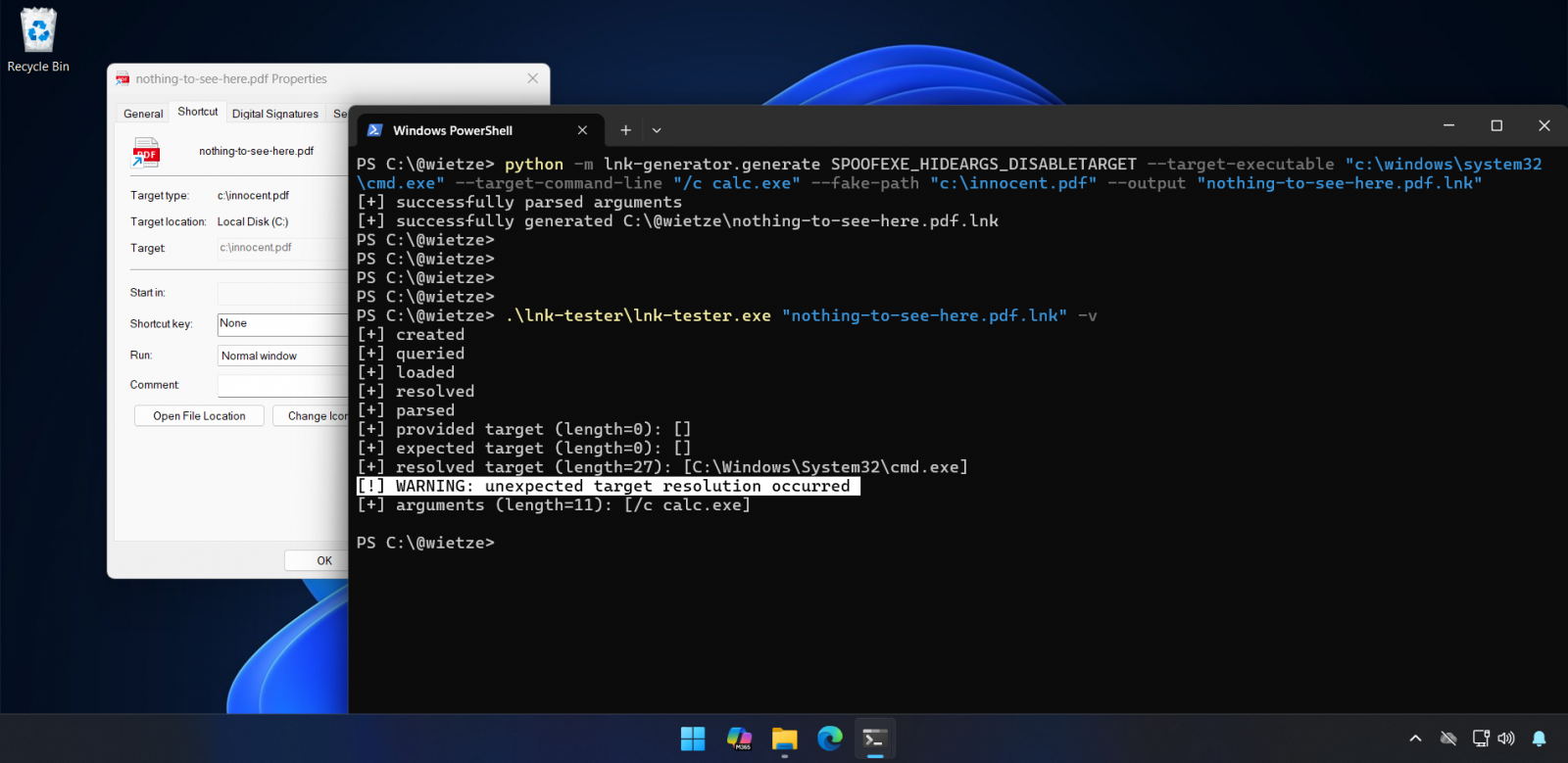
The core issue identified by Beukema revolves around the inconsistent handling of target specifications across various optional data blocks within the LNK file structure. When a user right-clicks a shortcut and examines its ‘Properties’ dialog, the displayed target path is drawn from one segment of the binary data. However, when the user executes the shortcut, the Windows shell may prioritize an executable path specified in a different, often less visible, data block.
One of the more subtle exploitation methods involves the strategic deployment of characters deemed "forbidden" within standard Windows paths, such as the double-quote character ("). By weaving these characters into the path definition in a manner that technically invalidates the displayed path but is nevertheless parsed by Explorer to resolve the execution target, a significant visual discrepancy is created. The user sees a path that appears benign—perhaps pointing to a seemingly legitimate document—while the underlying execution command points to a remote server or a locally staged malicious executable.
A more potent technique focuses on manipulating the LinkTargetIDList and LinkInfo fields. By constructing a non-conforming LinkTargetIDList value, the system is tricked into executing the path defined there, even if the human-readable LinkInfo field suggests an alternative destination.

"The result is a stark divergence between expectation and reality," Beukema noted in his documentation. "The user observes one definitive path listed in the Target field, but the moment execution is triggered, an entirely different, hidden path is invoked." Furthermore, because the visual target field is often rendered inert or read-only once spoofed, any associated command-line arguments meant to accompany the legitimate execution can also be effectively concealed from casual inspection.
The EnvironmentVariableDataBlock Apex
The most compelling and arguably dangerous technique centers on the manipulation of the EnvironmentVariableDataBlock structure. This specific block is designed to allow shortcut targets to dynamically resolve paths using environment variables (e.g., %APPDATA%). Beukema discovered that by selectively populating only the ANSI representation of the target path within this block while leaving the Unicode representation empty—or vice-versa, depending on the specific Windows build interpretation—a complete redirection of execution occurs.
In a powerful demonstration, an attacker could craft a shortcut that visually advertises itself as pointing to a file like "invoice.pdf" within the properties window. However, the active execution target defined in the EnvironmentVariableDataBlock could be set to invoke PowerShell.exe with encoded malicious commands, or launch a known staging utility.
Critically, this method executes the true target immediately upon the first click, bypassing the need for repeated actions or secondary confirmations. Beukema highlighted the compounded risk: "Because the spoofed target resides in the TargetIdList and the actual command in EnvironmentVariableDataBlock, the executed target gains the capability to utilize environment variables for dynamic payload staging, further obscuring forensic trails." The complete spoofing of the target program, file, or directory, coupled with the hiding of command-line arguments, renders standard user-level detection mechanisms nearly obsolete. This deception works because, fundamentally, Windows Explorer is designed to be lenient with malformed LNK files, prioritizing functional display over strict validation, a design choice that opens this persistent gap.
Industry Context: The Persistence of LNK Abuse
The focus on LNK files is not new; they have been a staple in the initial access phase for sophisticated threat actors for decades. Their danger lies in their ability to travel easily across network shares, email attachments, and removable media, often bypassing initial email gateway scrutiny because they are not recognized as executables themselves.
The current findings are especially relevant when viewed against the backdrop of historical LNK exploits, most notably CVE-2025-9491. This well-documented vulnerability allowed attackers to hide command-line arguments through excessive whitespace padding within the shortcut file structure. As Beukema pointed out, the enduring effectiveness of LNK files demonstrates a crucial behavioral pattern: users, conditioned by years of digital warnings, develop "click fatigue" and routinely dismiss the security prompts associated with opening downloaded shortcuts. If users routinely bypass the operating system’s default warnings for known risky file types, introducing new methods to mask the actual execution target only lowers the bar for successful compromise.

The history of CVE-2025-9491 provides a compelling precedent. Initially, Microsoft declined to classify that flaw as a critical vulnerability, citing the prerequisite of user interaction and arguing it did not cross established security boundaries. However, the extensive real-world exploitation—tracked by firms like Trend Micro as being utilized by at least 11 state-sponsored groups and cybercrime syndicates, including Evil Corp, APT37, and Mustang Panda—eventually forced a reassessment. Arctic Wolf reported Mustang Panda using this flaw to target European diplomats, deploying the PlugX RAT. Ultimately, Microsoft quietly patched the issue in June 2025, suggesting a pragmatic pivot under pressure from active zero-day abuse, despite earlier resistance to categorization as a true vulnerability.
Microsoft’s Response: The "User Interaction" Defense
When Beukema reported the newly discovered EnvironmentVariableDataBlock issue (tracked internally as VULN-162145) to the Microsoft Security Response Center (MSRC) in September, the corporation adopted a familiar stance: the findings did not meet the threshold for immediate servicing as a security vulnerability.
Microsoft’s official rationale centers on the established principle that any successful exploitation necessitates a direct, deliberate action by the user—in this case, opening the file. A spokesperson articulated this position: "These techniques do not meet the bar for immediate servicing under our severity classification guidelines as they require an attacker to trick a user into running a malicious file."
The vendor emphasizes existing defensive layers. They point to Microsoft Defender’s capabilities to detect and block such threat activity, and the proactive protection offered by Smart App Control, which is designed to halt unverified malicious files downloaded from the internet. Furthermore, Windows itself flags .lnk files originating from the internet with a prominent security warning, urging users to exercise caution.
However, this defense often overlooks the efficacy of social engineering combined with technical obfuscation. The very existence of Beukema’s research proves that attackers are highly motivated to engineer scenarios where the visual cues align with user expectation, thereby nullifying the impact of the general security warning. If a user trusts the visual display of the file properties, they are far more likely to click through the initial OS prompt.
Expert Analysis: Boundary Erosion in File Handling
From an expert security perspective, the debate hinges on the definition of a "security boundary." Traditionally, a boundary breach involves bypassing user consent or escalating privileges without permission. Microsoft’s position argues that tricking a user into consenting to run something—even if that something is not what the user thinks they are consenting to run—does not breach the boundary.
However, researchers argue that the integrity of user consent is itself a security boundary. When the operating system intentionally displays one instruction (Path A) while executing another (Path B), the operating system has failed to uphold the integrity of the user interface as a reflection of system action. This is not merely a cosmetic bug; it is a deliberate mechanism for deception that leverages deep-seated parsing logic flaws.
The creation of the open-source tool suite, lnk-it-up, by Beukema, underscores the community’s need for validation and detection capabilities. This tool allows security professionals to generate these deceptive shortcuts for controlled testing and, crucially, to analyze existing LNK files by cross-referencing the displayed target against the actual execution target derived from the binary structure. This capability is essential for incident response teams tasked with rapidly triaging suspicious files that bypass static signature analysis.
Implications for Defense and the Future Trajectory
The long-term implication of Microsoft’s current classification strategy is the potential for these LNK spoofing techniques to become codified zero-days, similar to the trajectory of CVE-2025-9491. If a technique remains unpatched because it requires user interaction, it becomes a reliable, cost-effective tool for threat actors who specialize in phishing and social engineering.
For enterprise security architects, this highlights the necessity of moving beyond reliance on end-user vigilance. Mitigation strategies must focus on preventing the execution of non-standard or internet-sourced LNK files outright, rather than depending on users to interpret complex security warnings correctly. Strategies include:
- Application Control Hardening: Implementing strict application control policies that restrict the execution of shells or interpreters launched via shortcut files originating from untrusted zones (e.g., the Downloads folder or network shares).
- Content Filtering: Enhancing email and web filtering to automatically quarantine or strip
.lnkfiles attached to incoming communications, treating them with the same suspicion level as executable files. - Endpoint Detection and Response (EDR) Behavioral Analysis: Tuning EDR solutions to monitor for anomalous process chains, such as
explorer.exespawningcmd.exeorpowershell.exeimmediately after an LNK file execution, irrespective of the visual path displayed.
The continued evolution of these LNK manipulation methods suggests that the underlying parsing logic for these legacy file types remains insufficiently robust against adversarial input. As operating systems integrate more complex features—including potential future interactions with AI agents or advanced scripting environments—the demand for absolute fidelity between the user interface representation and the underlying system execution path will only intensify. Until Microsoft revises its classification criteria to account for the manipulation of user trust through interface deception, these subtle flaws in the LNK specification will remain a persistent, low-cost vector for high-impact security compromises across the ecosystem. The industry must treat these "non-vulnerabilities" as real-world threats, leveraging tools like lnk-it-up to proactively audit and defend against deception that leverages the operating system’s own trust in its display mechanisms.

