The European digital home improvement and DIY powerhouse, ManoMano, is currently navigating the fallout from a significant data security incident that has potentially compromised the personal information of approximately 38 million customers. The incident, which the company confirmed was discovered in January 2026, did not originate from a direct compromise of ManoMano’s core infrastructure but rather through a security lapse at an external service provider. This scenario underscores a growing existential threat in the modern digital ecosystem: supply chain risk.
ManoMano, a prominent French e-commerce entity, commands a substantial presence across major European markets, including France, Belgium, Spain, Italy, Germany, and the United Kingdom. With reported monthly unique visitors hovering around 50 million, the scale of its customer base makes any security event a matter of considerable regulatory and public concern.
In a formal statement provided to technical reporters, a ManoMano spokesperson acknowledged the breach: “We can confirm that ManoMano has recently notified customers about a security incident involving one of our third-party customer service providers (a subcontractor).” The unauthorized access, which the company pinpointed to January 2026, led to what they describe as the "unauthorized extraction of certain personal data associated with customer accounts and customer service interactions."
This incident appears to align with claims surfaced earlier in the month on underground hacking forums. A threat actor operating under the alias "Indra" boasted of obtaining data relating to approximately 37.8 million user accounts, alongside thousands of support tickets and associated attachments. While details remain under official investigation, unconfirmed reports suggest the compromised entity was a Tunis-based customer support service provider, potentially utilizing a platform like Zendesk, which itself may have suffered a preceding security failure. Cybersecurity intelligence analysts, such as those from Hackmanac, have tracked the customer notification phase beginning this week, marking the public disclosure timeline.

The Anatomy of the Compromise: Supply Chain Risk Magnified
The crucial element distinguishing this event is the vector of attack. ManoMano, like countless other high-volume e-commerce platforms, relies on a complex web of subcontractors for functions ranging from customer relationship management (CRM) to logistics and technical support. When a primary vendor is secure, the perimeter seems robust; however, an exploited vulnerability in a lower-tier partner—a subcontractor’s subcontractor, for instance—can provide a critical pivot point into the main corporation’s data stores.
ManoMano has been meticulous in detailing what was, and critically, what was not, compromised. The company explicitly stated that no account passwords were breached, and there were no instances of data modification within ManoMano’s primary systems. This suggests the exfiltrated data was likely cached or stored by the third-party provider for service delivery purposes.
The range of exposed data is user-specific and dependent on the level of interaction an individual had with the platform. While the complete, definitive list is often withheld during active investigations, ManoMano confirmed that the exposed data types encompass:
- Full Names
- Email Addresses
- Physical Shipping and Billing Addresses
- Telephone Numbers
- Order Histories
- Dates of Birth (for some users)
Crucially, the exclusion of password data mitigates the immediate risk of mass account takeover via credential stuffing attacks. However, the inclusion of names, email addresses, physical locations, and order history creates a high-value target profile for sophisticated social engineering and phishing campaigns.
Regulatory Scrutiny and Remedial Actions
The scale of the exposure, touching customers across multiple EU jurisdictions, mandates immediate regulatory engagement. ManoMano confirmed it has notified the relevant supervisory authorities, including France’s data protection authority (CNIL) and the national cybersecurity agency (ANSSI). Compliance with the General Data Protection Regulation (GDPR) dictates stringent reporting timelines and necessitates a demonstrable commitment to remediation. Failure to adhere to GDPR standards following a breach of this magnitude can result in severe financial penalties, calculated as a percentage of global annual revenue.

ManoMano’s response centered on rapid containment. The spokesperson detailed decisive action: "Upon discovery, we took immediate steps to secure our environment, including disabling the relevant access, revoking the subcontractor’s access to customer data, and strengthening access controls and monitoring.”
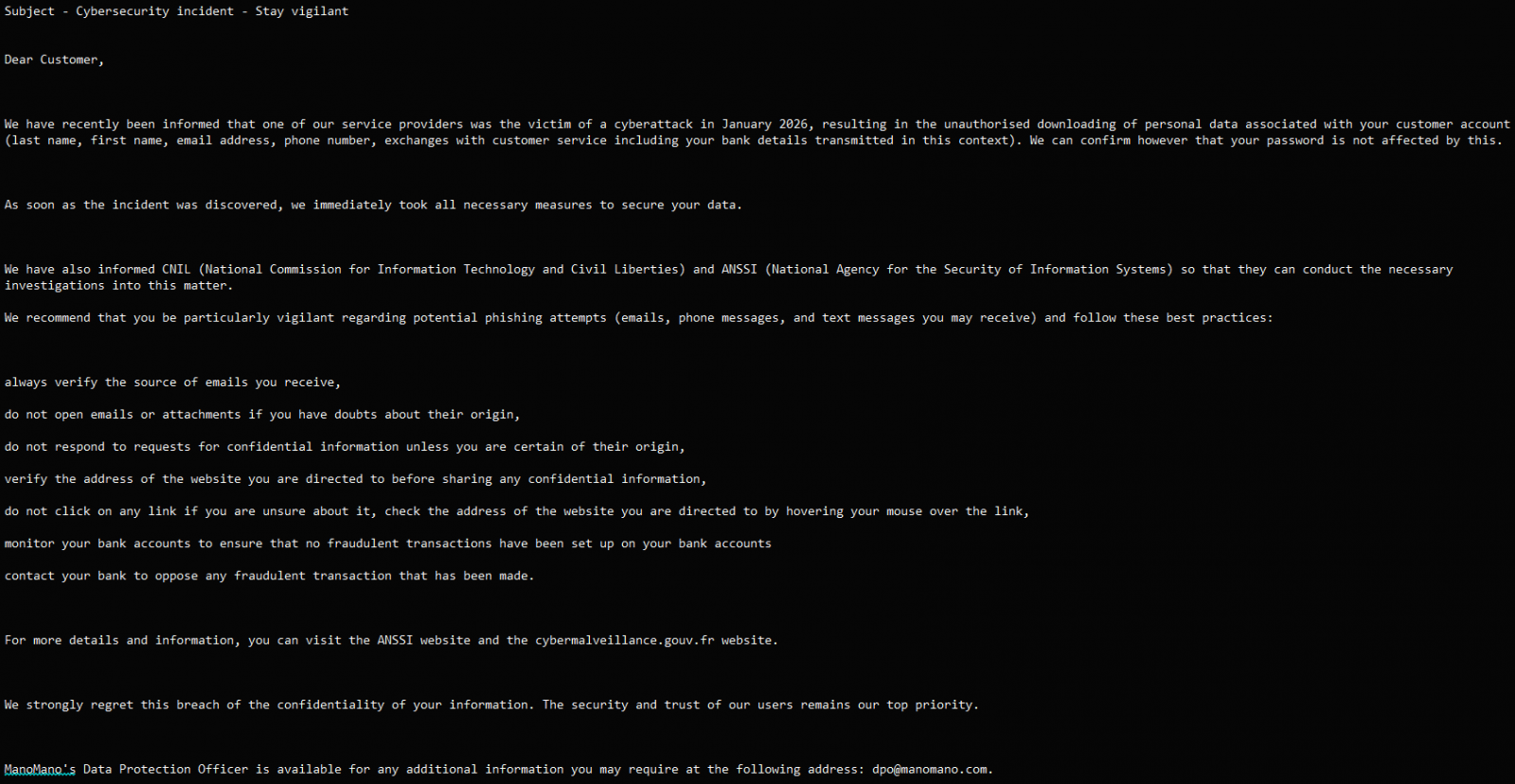
Furthermore, customer notifications, which were shared in sample form, emphasized vigilance against subsequent cyber threats. The guidance provided to affected individuals is standard but essential in this context: verifying the identity of any incoming communication, closely monitoring financial accounts for anomalous transactions, and exercising extreme caution regarding unsolicited links or attachments. This proactive stance aims to shift the immediate defense burden to the end-user against phishing attempts that leverage the newly acquired personal data.
Industry Implications: The Third-Party Perimeter Erosion
The ManoMano breach serves as another stark reminder of the evolving threat landscape, shifting the focus from perimeter defense to vendor risk management (VRM). In the digital economy, a company’s security posture is often only as strong as its weakest link in the supply chain. For large e-commerce platforms handling millions of transactions and customer interactions, the reliance on specialized, often smaller, third-party service providers creates an expansive and difficult-to-audit attack surface.
This incident highlights several critical industry trends:
- Data Minimization Failure: The sheer volume of historical customer service interaction data retained by the subcontractor suggests a failure in data minimization policies. If the necessary data for ongoing support interactions had been purged according to a strict retention schedule, the impact of the breach would have been substantially lower.
- Over-Provisioning of Access: The unauthorized extraction implies that the third-party provider possessed more extensive data access rights than was strictly necessary for its designated function. Modern security architecture demands the principle of least privilege (PoLP), ensuring vendors only access the specific data fields required to perform their contracted tasks.
- Cloud Platform Vulnerabilities: If the underlying issue involved a compromised instance of a common SaaS platform used for customer service (like Zendesk, as speculated), it implies that configuration errors or inadequate security controls within that shared service environment were the entry point. This forces primary organizations to audit not just their contracts, but the actual security controls implemented by their vendors on shared software infrastructure.
From an expert perspective, the financial and reputational damage extends beyond the immediate notification costs. ManoMano faces potential litigation, increased insurance premiums, and a measurable decrease in customer trust—a critical asset for any consumer-facing brand. The 38 million affected records represent a massive pool for identity theft preparation, even without passwords, as threat actors can use this data to craft highly convincing spear-phishing attacks aimed at eliciting login credentials or financial information later.
Future Trajectories: Zero Trust and Continuous Vendor Auditing
The response to incidents like the ManoMano breach is driving significant investment in two key areas: Zero Trust Architecture (ZTA) implementation and enhanced supply chain due diligence.
For ZTA, the logic is simple: never trust, always verify. In a Zero Trust model, even an authenticated third-party service provider would face micro-segmentation, meaning its access to customer databases would be strictly limited to the necessary APIs and data subsets in real-time. Any attempt to extract bulk data—which is often necessary for a cybercriminal’s goal—would be flagged immediately by continuous authorization checks, likely terminating the session before mass exfiltration occurs.
Furthermore, the industry is moving toward continuous, rather than periodic, vendor auditing. Relying on annual SOC 2 reports is proving insufficient against dynamic threats. Future VRM programs will incorporate automated tools that monitor vendor security telemetry, looking for anomalies in access patterns, failed login attempts, or unusual data egress volumes originating from partner systems. For a platform like ManoMano, this means establishing real-time monitoring hooks into the data access logs of its critical subcontractors.
The fact that the investigation is ongoing means that the full scope and financial repercussions are yet to be determined. However, the 2026 ManoMano event will likely be categorized as a textbook example of third-party dependency failure, forcing e-commerce executives across Europe to re-evaluate the invisible digital pathways that connect their most sensitive customer data to external partners. The age of assuming a vendor’s security is sufficient is definitively over; the new paradigm demands verifiable, continuous proof of security control enforcement at every juncture of the digital supply chain. This incident serves as an expensive lesson in the interconnected fragility of the modern online retail environment.

