The digital landscape for modern youth is dominated by immersive, interconnected platforms. Where previous generations coveted physical game cartridges or early PC titles like Red Alert or Zelda, today’s children are immersed in persistent online worlds such as Roblox, Minecraft, and competitive shooters like Call of Duty. This shift represents more than just evolving entertainment preferences; it marks a critical evolution in the cyber threat ecosystem, transforming casual gaming habits into a potent vector for sophisticated corporate compromise.
The historical narrative of illicit software acquisition—scouring bulletin boards or using early search engines for "Free [Game Title] Download"—has simply been updated for the digital age. For a young user seeking a competitive edge, a performance boost, or simply to access content their peers are enjoying, the temptation to bypass official channels remains potent. The initial motivation is often benign: making a favorite game run smoother, unlocking an exclusive cosmetic, or installing a community-developed enhancement. This search frequently leads down a well-trodden, yet treacherous, path paved with tempting titles promising free upgrades or cheats.
A typical user journey involves a search on video platforms or standard search engines for terms like "Ultimate Roblox FPS Unlocker 2025" or "Free Premium Server Access." This often directs them to an affiliated Discord server or a third-party repository hosting compressed archives, frequently delivered as ZIP files. The payload is deceptively simple: an executable file, perhaps named RobloxBooster.exe or LobbyInjector.exe. Upon execution, the user experiences the desired superficial result—the game launches, perhaps even slightly faster—creating a false sense of security.

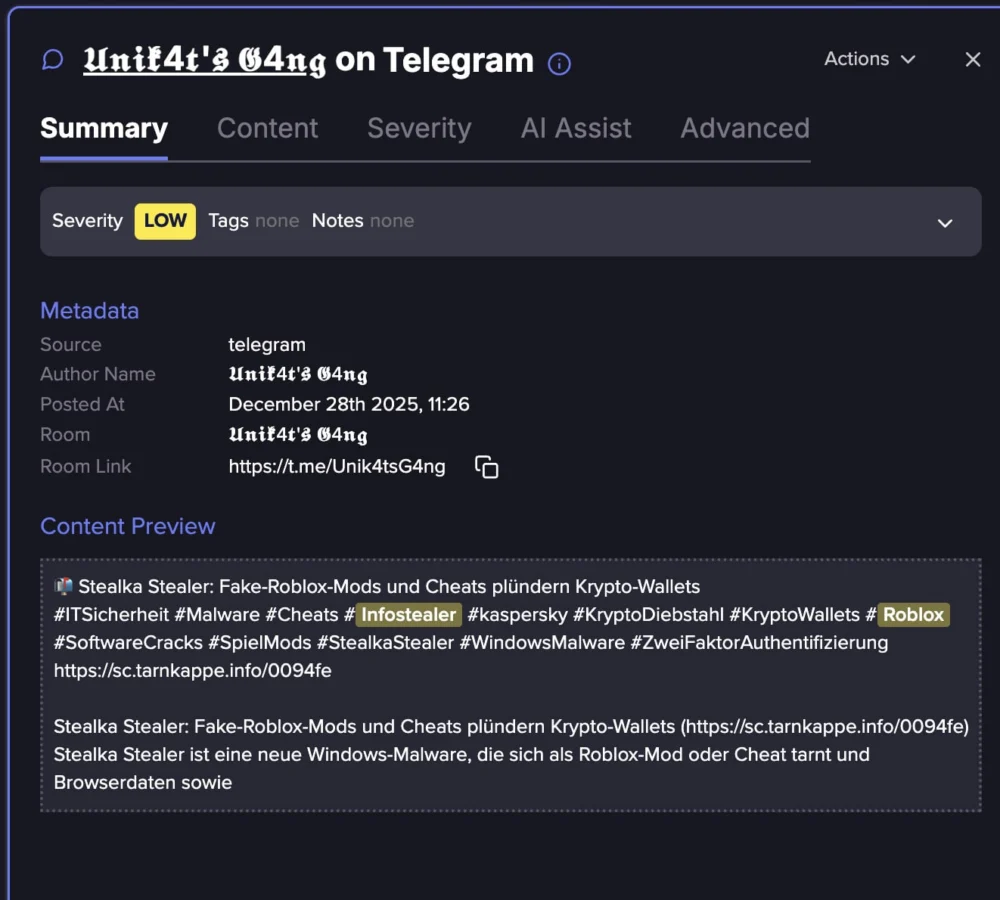
However, the execution of that seemingly harmless file initiates a silent, high-speed data exfiltration process. The deceptive application is, in reality, a highly evolved Infostealer Malware. These programs are engineered for stealth and efficiency, designed not to crash the system or trigger immediate antivirus alerts, but to systematically map and vacuum up sensitive identity artifacts residing on the compromised endpoint. This entire operation often concludes before the user even registers the application is running, leaving behind a fully cataloged digital footprint ripe for criminal exploitation.
The Gamer as the Prime Infection Pool
This phenomenon is not theoretical; it is a quantifiable reality underpinning a significant segment of current cyberattacks. Threat intelligence analysis consistently points to the gaming community as a disproportionately large and reliable source of compromised credentials and session data. Recent industry reports indicate that upwards of 40% of all successful Infostealer deployments can be traced back to gaming-related artifacts—be they purported cheats, modified game clients, cracked software, or performance utilities.
From the perspective of an adversarial operator, gamers present an optimal target demographic for several compelling reasons:
- High Propensity for Risk-Taking: Users engaging with game modification communities inherently demonstrate a higher tolerance for executing code from unknown or unverified sources. They are conditioned to trust community recommendations over official warnings.
- Privileged Access Needs: To function, many mods or cheats require elevated permissions, leading users to readily grant administrative rights that a standard application might not necessitate.
- Constant Re-engagement: Gaming communities are active 24/7, providing a continuous stream of potential victims executing new, freshly distributed malicious files.
- Behavioral Conditioning: Crucially, gamers are trained to execute untrusted code. This learned behavior—double-clicking an executable promising an in-game advantage—is precisely the mechanism that Infostealer purveyors exploit to bypass technical security controls.
The infection chain is remarkably straightforward, bypassing the need for complex zero-day exploits or intricate social engineering against hardened corporate targets. The attack begins with the simple, trusted action of a user—often a child, but increasingly, an adult gamer—executing a file they believe will enhance their leisure experience.
Deconstructing the Infostealer Execution Chain
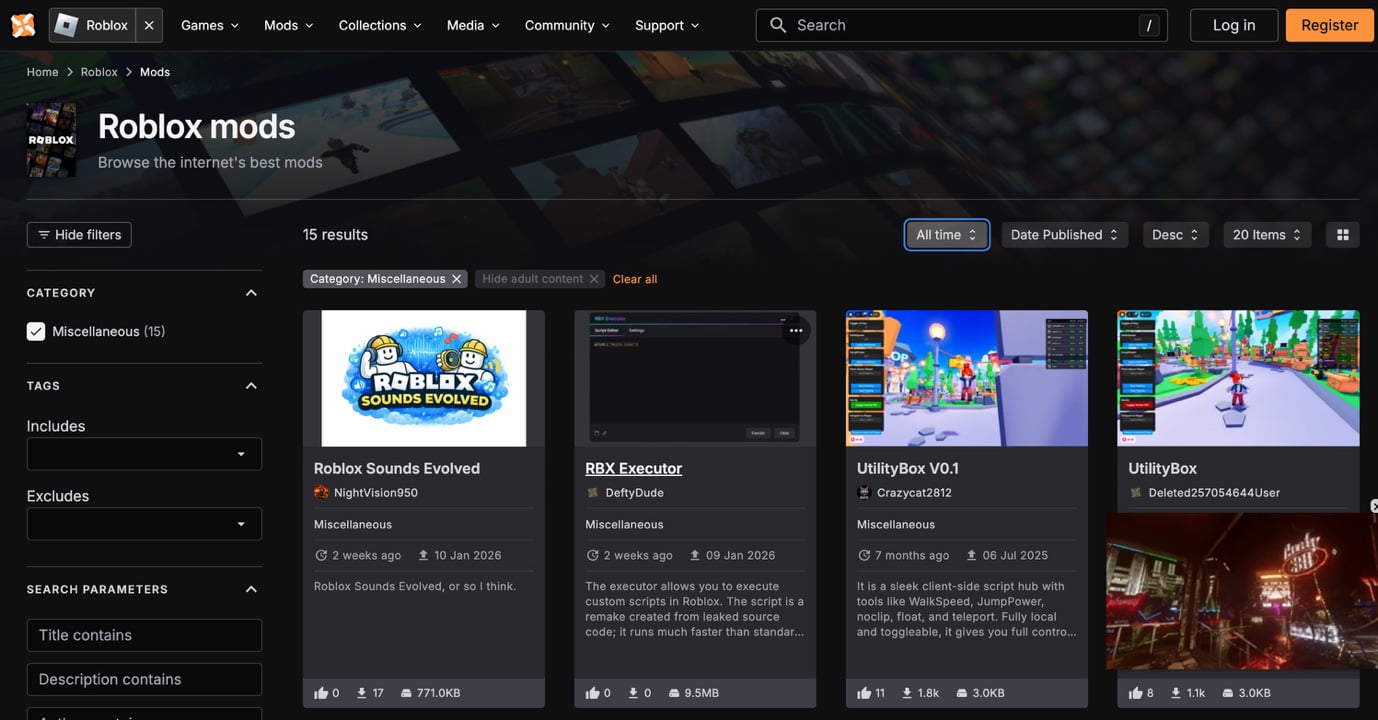
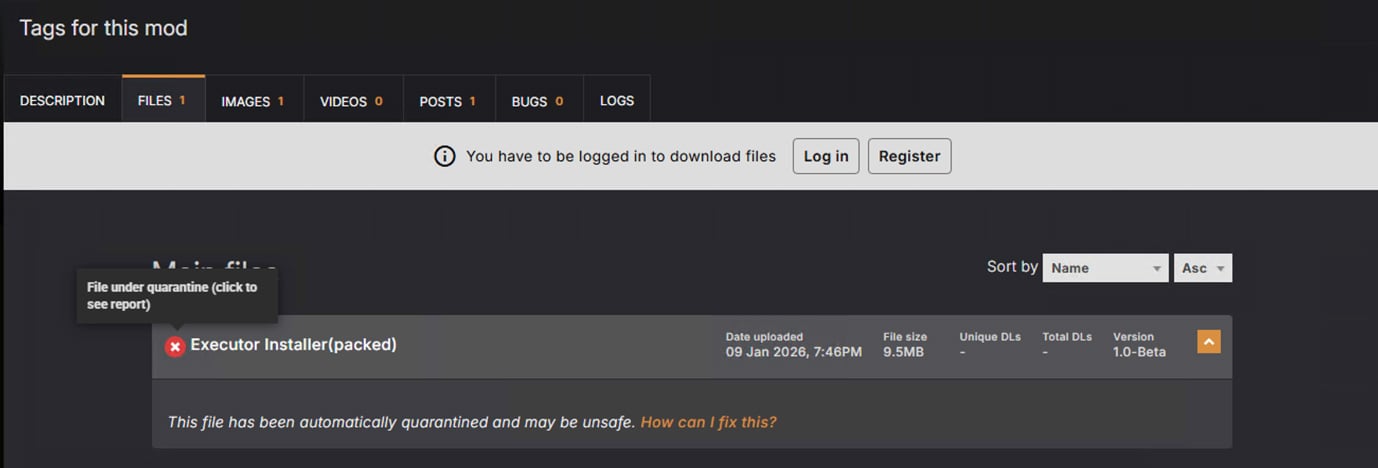
A common scenario involving a platform like Roblox highlights the mechanics of this infiltration. The attacker packages the malware within a seemingly legitimate archive:
Roblox_Turbo_Speed_v2.zip
readme.txt(Distraction/Instruction)injector.exe(The Malicious Loader)
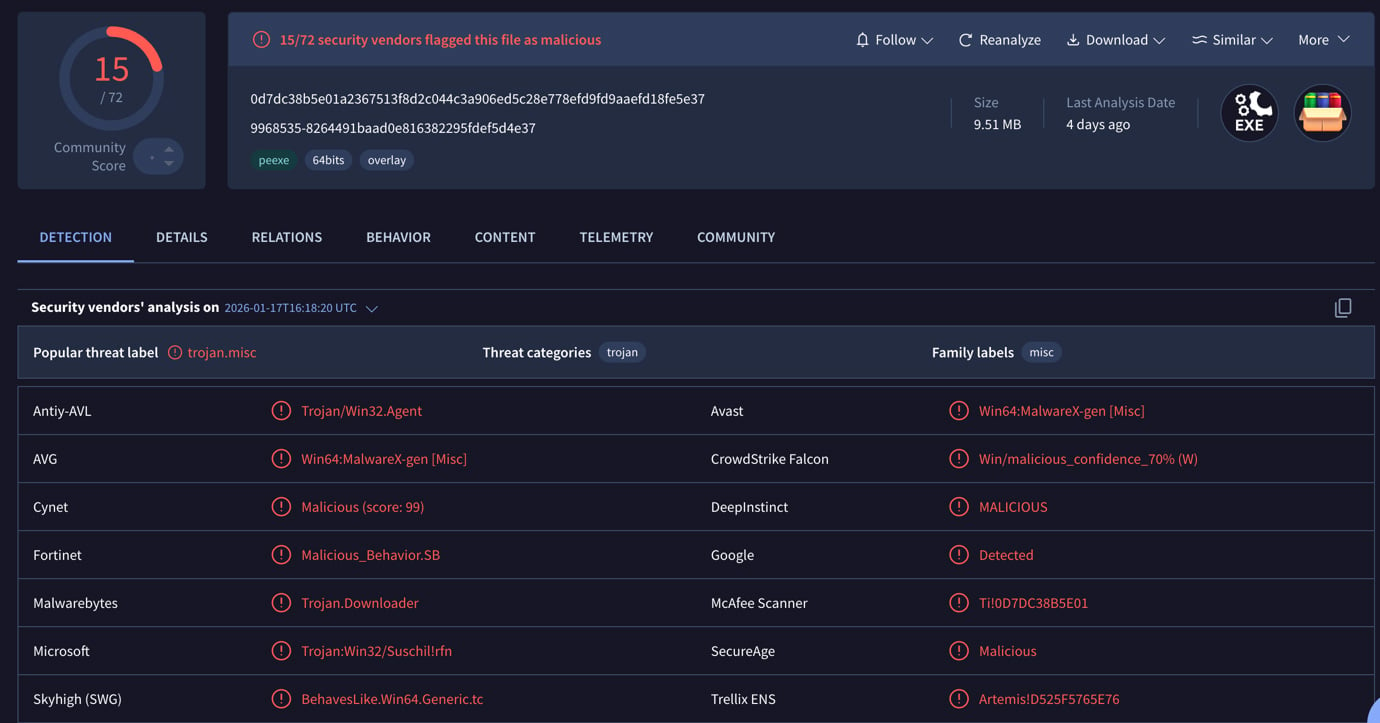
When the user runs injector.exe, the initial decoy application might launch correctly. Concurrently, the hidden payload executes. This payload is frequently one of the well-established, commercially available Infostealers, such as Lumma, RedLine, Vidar, or Raccoon Stealer.
These tools are not custom-built for each attack; they are modular, mature software-as-a-service (SaaS) offerings sold in cybercrime forums. They require no complex exploitation of software vulnerabilities (like buffer overflows or logic flaws). The exploitation is purely psychological: leveraging the user’s desire for immediate gratification to convince them to execute the initial payload themselves.
The Scope of Digital Pilfering
The term "Infostealer" describes software that harvests a broad spectrum of digital assets. Once activated, these tools perform an aggressive, automated sweep of the local machine, targeting specific directories and browser storage mechanisms. The speed of this operation is critical; modern Infostealers can map an entire system and compile a comprehensive data package in under five seconds.
The data harvested includes:
- Browser Artifacts: All saved login credentials, including usernames and passwords across major browsers (Chrome, Edge, Firefox, Brave).
- Session Cookies and Tokens: These are particularly valuable as they allow attackers to hijack active sessions without needing to know the actual password, bypassing Multi-Factor Authentication (MFA) protection that relies solely on credential input. This includes tokens for services like Discord, Steam, and various webmail providers.
- Cryptocurrency Wallets and Extensions: Access to browser-based wallet extensions (like MetaMask) can lead to direct theft of digital assets.
- System Information: Operating system details, hardware configuration, and network data useful for future, more targeted attacks.
- Saved Files and Documents: Searching for specific file extensions related to financial data or corporate documents stored locally.
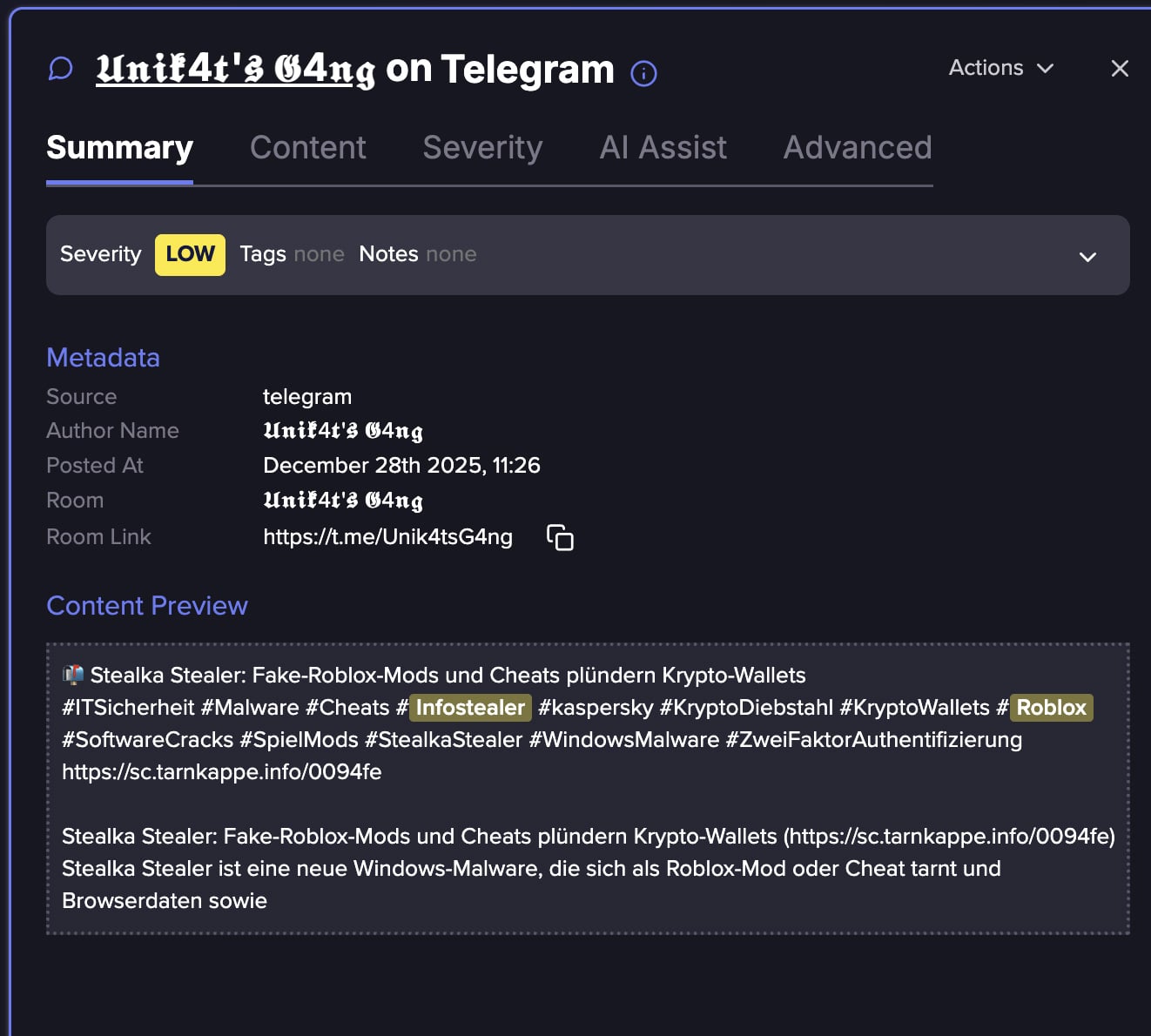
The output of this process is the "stealer log"—a compressed, structured archive containing a complete digital profile of the infected user. This log is then exfiltrated, typically uploaded to a designated command-and-control (C2) server hosted on bulletproof infrastructure or encrypted channels like Telegram, ready for monetization on dark web marketplaces.
The Unforeseen Enterprise Impact
The critical disconnect often missed by individuals focusing solely on the "kid" aspect is the resulting enterprise impact. While a child’s personal laptop is a high-value target for credential theft, the threat escalates dramatically when that user also accesses corporate resources from the same device, or when the malware successfully harvests credentials belonging to an employee who works remotely.
If an employee uses their personal machine for work, or if the malware infects a device that has ever been used to access corporate assets, the consequences are severe. An Infostealer log can contain:
- VPN Credentials: Allowing direct access to the corporate network perimeter.
- Cloud Service Tokens: Access to Microsoft 365, Google Workspace, or other SaaS platforms.
- Enterprise Authentication Data: Credentials for Single Sign-On (SSO) providers like Okta or Azure AD, or collaboration tools like Slack and GitHub.
The resulting security incident report often reads: "Breach caused by the use of valid credentials." This is the hallmark of an Infostealer attack. The organization was not defeated by a sophisticated zero-day vulnerability; it was compromised because an employee’s personal digital identity—stolen via a gaming mod—was used to authenticate into a secure system.
This underscores a fundamental shift in the initial access landscape. Security teams are increasingly shifting focus from patching perimeter vulnerabilities to hardening identity access, precisely because credential theft via endpoints has become the dominant initial access vector.
Expanding the Attack Surface Beyond Gaming
While gaming remains the highest-volume vector, the methodology of packaging malware into desirable, free utilities is universally applied. Attackers understand that users, regardless of age, will bypass security warnings for perceived value. This extends far beyond gaming:
- Productivity Tools: Fake "premium" versions of PDF editors, video converters, or image manipulation software.
- Software Cracks: Modified installers for expensive professional software, promising legitimate functionality without a license.
- AI Tools: Mock versions of popular, cutting-edge AI interfaces or local LLM installers.
- System Utilities: Falsely advertised "system cleaners" or "driver updaters."
If a piece of software is free, runnable, and promises a significant advantage over the paid or official version, it is a potential delivery mechanism for an Infostealer.
The Dark Market Commodification of Identity
The monetization of stolen data is as industrialized as the malware distribution itself. Infostealer logs are a foundational commodity in the cybercrime supply chain. Threat actors can purchase:
- Raw Logs: Unfiltered archives containing thousands of harvested credentials, sold in bulk.
- Targeted Access: Logs pre-filtered for specific high-value targets (e.g., users with specific corporate email domains or cryptocurrency holdings).
- Stealer-as-a-Service (STaaS): Fully managed subscriptions where the malware operator handles the C2 infrastructure, exfiltration, and delivery of logs for a recurring fee.
Advertisements in underground forums often detail access to specific stealer families, pricing based on the perceived quality of the credentials (e.g., "Verified Corporate Emails" fetching a premium). While some ads promising access to high-profile stealers might be scams targeting other criminals, the underlying market for legitimate, functional logs remains robust and highly competitive. The availability of detailed tutorials further lowers the barrier to entry, teaching novice criminals how to effectively parse and weaponize these harvested logs for subsequent attacks like Business Email Compromise (BEC) or identity fraud.
Analysis: The Identity-Centric Attack Paradigm
The rise of Infostealers signals a strategic pivot in cybercrime: moving away from resource-intensive vulnerability research toward identity exploitation. Exploiting a software bug requires deep technical skill, time, and carries the risk of being patched quickly. Stealing a valid credential, however, allows the attacker to utilize the organization’s own, established, and often trusted access pathways.
This transition is reflected in incident response reporting. The frequent declaration that breaches occurred via "valid credentials" is the digital fingerprint of an Infostealer attack chain, whether the initial compromise happened on a corporate machine or a home desktop used by a family member.
For enterprise security architects, this necessitates a move toward Zero Trust principles as a foundational defense, not merely a buzzword. If an endpoint can be compromised by a non-technical user action (clicking a malicious link), the network must assume the endpoint is hostile regardless of the user’s intent. Stronger MFA enforcement, especially phishing-resistant methods like FIDO2 hardware keys, and rigorous session monitoring become paramount.
The evolution from simple game piracy to mass identity harvesting demonstrates that the digital playground, once perceived as a low-stakes environment, is now deeply integrated into the global threat matrix. The simple act of seeking an unfair advantage in a video game can inadvertently provide a threat actor with the keys to a corporate kingdom, making digital literacy and endpoint hygiene a necessity across all household devices, not just those used for professional tasks. The line between a child’s innocent download and a major corporate security incident has never been thinner.