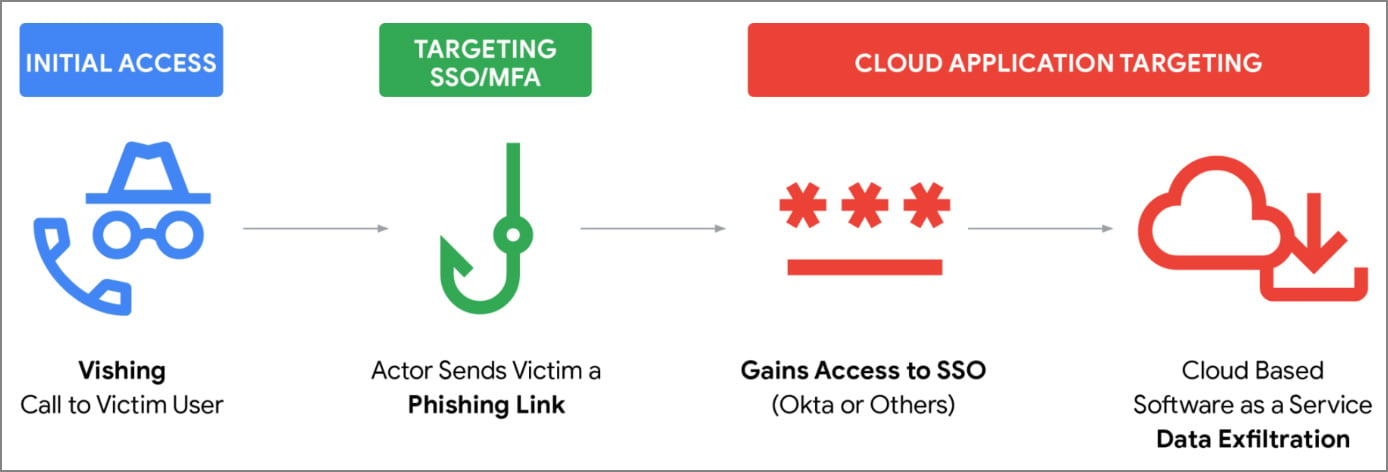
The cybersecurity landscape is currently grappling with an escalating threat vector where threat actors are weaponizing social engineering, specifically sophisticated voice phishing (vishing), to bypass robust multi-factor authentication (MFA) mechanisms and seize control of corporate single sign-on (SSO) environments. Mandiant, Google’s premier threat intelligence division, has documented a concerted campaign orchestrated by the ShinyHunters extortion group and associated clusters, demonstrating a highly coordinated attack chain that pivots directly on compromising identity providers like Okta, Microsoft Entra ID, and Google Workspace. This methodology marks a critical evolution in cybercrime, moving beyond traditional email-based credential harvesting to real-time, interactive deception.
The Genesis of the Attack: Real-Time Deception via Vishing
The foundational step in this campaign involves threat actors leveraging personalized social engineering tactics. Instead of relying on passive phishing emails, these adversaries adopt an aggressive, direct approach by impersonating internal IT support or helpdesk personnel. These calls are highly contextualized, often claiming an urgent need to update MFA settings or resolve a supposed security alert. This sense of corporate urgency, delivered via a human voice, immediately lowers an employee’s natural defenses.
The critical differentiator here is the integration of advanced phishing kits, as noted by security vendors like Okta. These kits are designed to mimic legitimate corporate login portals with extreme fidelity. Crucially, these kits are interactive, allowing the attacker on the phone to dynamically guide the victim through the login process in real time. As the unsuspecting employee enters their username and password on the fraudulent site, the credentials are instantaneously relayed to the attacker.

The true mastery of this technique lies in handling the MFA challenge. While the employee is still engaged in the seemingly legitimate phone call, the attacker triggers the legitimate MFA prompt on the victim’s device—be it an authenticator app push notification or a time-based one-time password (TOTP). The attacker then instructs the victim on precisely how to respond to this prompt, effectively coaching them into approving their own session takeover. This real-time coordination ensures the attacker gains immediate, authenticated access.
Establishing Persistence and the SSO Springboard
Upon successful authentication, the immediate objective shifts from initial access to establishing persistence and lateral movement within the cloud ecosystem. Once inside the user’s session, the attackers target the centralized identity management platforms—Okta, Entra ID, or Google—which function as the master keys to the kingdom.
The goal is not merely to use the existing session, but to enroll the attacker’s own device or security factor into the victim’s MFA profile. This grants the threat actor long-term, persistent access, independent of the original victim’s credentials or awareness.
With this persistent foothold, the SSO dashboard transforms into the ultimate springboard. This dashboard aggregates permissions across the entire Software-as-a-Service (SaaS) stack utilized by the organization. Mandiant has observed exploitation across a broad spectrum of high-value targets, including Salesforce—which ShinyHunters has historically prioritized—as well as Microsoft 365, SharePoint, DocuSign, Slack, Atlassian suites, and various cloud storage platforms like Dropbox and Google Drive. For an extortion group focused on data exfiltration, compromising the SSO gateway offers a single point of compromise to harvest data from dozens of disparate, critical business applications.

Attribution and Threat Cluster Differentiation
Mandiant’s analysis segments the observed activity into distinct, though potentially collaborating, threat clusters: UNC6661, UNC6671, and UNC6240 (identified as ShinyHunters). While the end goal—data theft and subsequent extortion—is shared, the operational execution reveals subtle but important distinctions.
UNC6661, the primary cluster linked to the documented vishing campaigns, impersonates IT staff and uses domains registered via NICENIC, often employing naming conventions like <companyname>sso.com or <companyname>internal.com. Their post-compromise activity reveals a keen interest in obscuring their tracks. In a notable instance involving an Okta customer, UNC6661 deployed the "ToogleBox Recall" Google Workspace add-on. This tool, designed for email search and recall, was weaponized to proactively locate and permanently delete the security notification email sent by Okta confirming the enrollment of a new MFA device. This calculated step aims to blind the victim to the persistence mechanism established by the attacker. Following the data theft, the extortion demands were delivered explicitly under the ShinyHunters branding, often including a specific Tox messenger ID known to be used by that group.
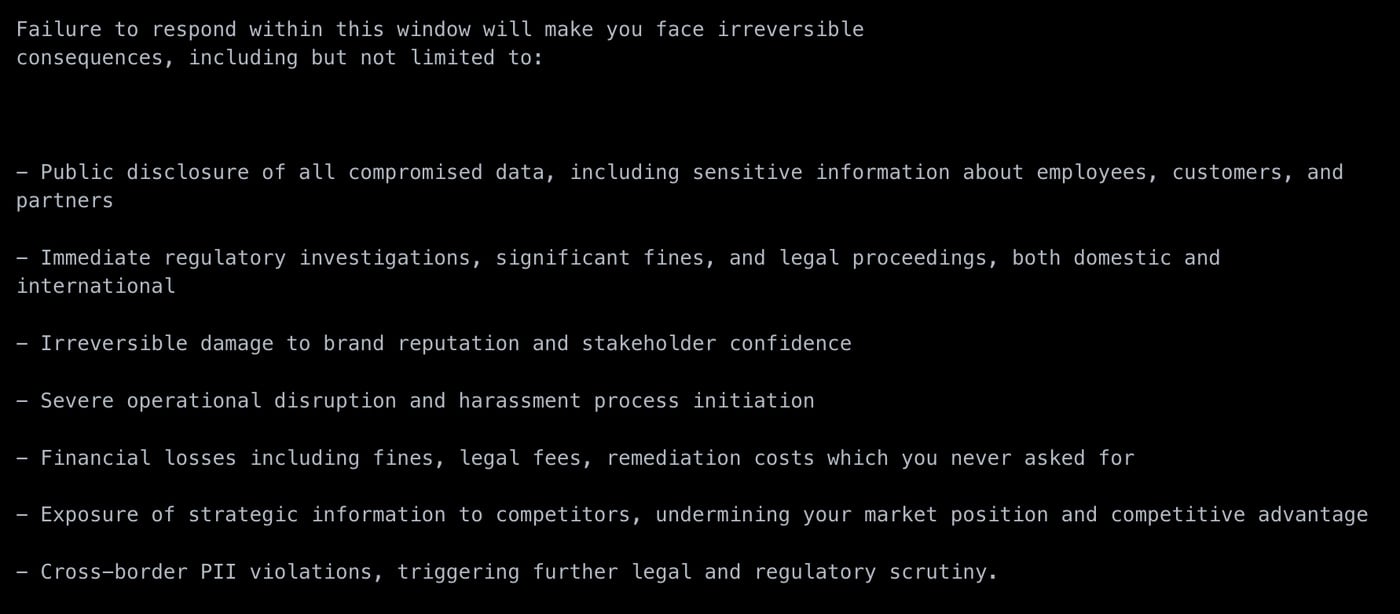
UNC6671 employs a parallel vishing methodology but exhibits operational differences. Their phishing infrastructure utilizes domains registered through Tucows. Furthermore, their extortion tactics diverge; demands are not explicitly branded as ShinyHunters, they use a different Tox ID for communication, and Mandiant observed these actors employing more aggressive pressure and direct harassment tactics against company personnel. Their domain naming conventions also mimic corporate portals, as evidenced by the use of domains like matchinternal[.]com in the recent high-profile compromise affecting Match Group properties (Hinge, Tinder, etc.).
UNC6240 (ShinyHunters) acts as the overarching extortion entity, often taking over the final communication and financial demands, even if the initial intrusion was executed by an affiliate like UNC6661. This separation of labor—intrusion by one cluster, extortion by another—is a common tactic in modern cybercrime syndicates to enhance operational security and plausible deniability.
Industry Implications: The Failure of MFA as a Silver Bullet
This campaign fundamentally challenges the industry’s reliance on MFA as an ultimate security control. While MFA successfully thwarts password spraying and brute-force attacks, this vishing strategy exploits the weakest link in any security chain: the human user. The successful circumvention of MFA through real-time manipulation underscores a critical shift in attacker methodology.
The Erosion of Trust in Identity Systems: When an employee trusts a voice on the phone—especially one claiming to be from internal IT—they are psychologically coerced into overriding security protocols. This highlights the necessity of shifting defense focus from technical barriers (MFA) to behavioral security hygiene.
SaaS Sprawl and Centralized Risk: The reliance on centralized SSO hubs exacerbates the impact of a single successful compromise. A breach that might have previously been contained to one application now yields access to the entire cloud portfolio. This demands that organizations audit their least-privilege model not just within individual SaaS apps, but at the SSO provisioning layer. If a user has access to 50 applications via SSO, the risk profile of that user account is exponentially higher.
Stealth and Persistence: The use of tools like Google Workspace add-ons to delete forensic artifacts is particularly alarming. It indicates that these actors are not just opportunistic smash-and-grab thieves; they are sophisticated enough to actively manage their operational security within the compromised environment, delaying detection for extended periods. Furthermore, the use of commercial VPNs and residential proxy networks (Mullvad, Oxylabs, NetNut) by the threat actors complicates traditional IP-based blocking strategies, further masking their origins.
Future Impact and Defensive Imperatives
The evolution demonstrated by ShinyHunters and their affiliates signals a trend toward highly personalized, multi-channel attacks that blend traditional phishing with direct human interaction. This style of attack is expensive and resource-intensive compared to automated campaigns, suggesting that the data stolen is of exceptionally high value, justifying the investment.
For enterprise security teams, the path forward requires a multi-layered defense strategy that complements existing MFA infrastructure:
-
Behavioral Monitoring and Anomaly Detection: Organizations must prioritize monitoring post-authentication behavior. Mandiant recommends specific behavioral detection logic focused on activities immediately following successful SSO logins, such as the enrollment of new MFA methods, changes to security settings, or the deployment of unexpected third-party plugins/add-ons within cloud services like Google Workspace.
-
Strengthening Identity Workflows: Security hardening must extend to the authentication reset process itself. Policies should mandate out-of-band verification (e.g., requiring a call back to a known corporate number or an established secondary email) for MFA changes, rather than relying solely on a single communication channel initiated by the user or an unknown caller.
-
Security Awareness Training Overhaul: Standard password training is insufficient. Training must specifically address vishing scenarios, teaching employees to verify the identity of callers claiming to be IT support through an established, internal verification channel (e.g., calling a known internal IT desk number back) rather than trusting the incoming caller ID or the context of the call itself. The mantra must become: Never trust an unsolicited call requesting immediate security action.
-
Telemetry and Logging: Robust logging across identity providers (Okta, Entra ID) and target SaaS applications is paramount. This includes logging all API calls related to MFA configuration changes and third-party application authorizations. Mandiant has provided actionable guidance and specific detection rules, particularly for Google SecOps environments, underscoring the immediate need for security teams to ingest and analyze this specific telemetry to catch the subtle indicators of compromise before widespread data exfiltration occurs.
The convergence of social engineering expertise and advanced phishing technology in these vishing attacks represents a high-water mark in identity compromise. Success against these threats hinges on recognizing that identity protection today demands vigilance across both the digital interface and the telephone line.