The landscape of software development security is undergoing a significant evolution, marked by the emergence of specialized tooling designed to combat one of the most persistent and dangerous vulnerabilities: accidental secrets exposure. Central to this development is the introduction of Betterleaks, a new open-source utility engineered to succeed the highly popular Gitleaks. Betterleaks is positioned not merely as an iterative update, but as a fundamental architectural improvement aimed at enhancing detection efficacy across diverse code environments. This tool is designed to methodically traverse directories, individual files, and expansive Git repositories, employing a sophisticated set of default and user-customizable rulesets to pinpoint sensitive artifacts.
Secrets scanning utilities, by definition, are critical defensive mechanisms in the modern Continuous Integration/Continuous Deployment (CI/CD) pipeline. They function as digital sentinels, actively searching vast quantities of source code—including configuration files, environment variables stored in plaintext, and development artifacts—for high-value targets such as proprietary credentials, encryption keys, access tokens, and API identifiers. The imperative for such tools stems from the reality that developers, under pressure to meet aggressive timelines, frequently commit these sensitive strings directly into version control systems. Once committed, especially within public repositories, these exposed secrets become immediate targets for automated reconnaissance by malicious actors. Threat actors continuously deploy advanced crawling mechanisms specifically tuned to ingest configuration files and commit histories, seeking exploitable entry points into corporate infrastructure. Proactive detection via tools like Betterleaks is therefore a non-negotiable step in mitigating the risk of unauthorized access, data exfiltration, and subsequent system compromise before attackers can monetize these exposures.
The genesis of Betterleaks is intrinsically linked to its predecessor, Gitleaks. Betterleaks is the product of the same core development team, spearheaded by Zach Rice, who serves as the Head of Secrets Scanning at Aikido Security. Rice is the original author of Gitleaks, a tool that achieved substantial traction, evidenced by its staggering download metrics—exceeding 26 million on GitHub alone and over 35 million pulls via Docker and the GitHub Container Registry (GHCR). This deep institutional knowledge informs the architecture of Betterleaks. The transition to a new project name and structure follows a critical inflection point: the original developer reportedly lost full administrative control over the established Gitleaks repository, prompting the creation of a dedicated, independently governed successor. Rice articulated the motivation behind the rebranding and relaunch succinctly: "Betterleaks is the successor to Gitleaks. We’re dropping the ‘git’ and slapping ‘better’ on it because that’s what it is, better." This sentiment underscores a commitment to technological advancement rather than mere maintenance.
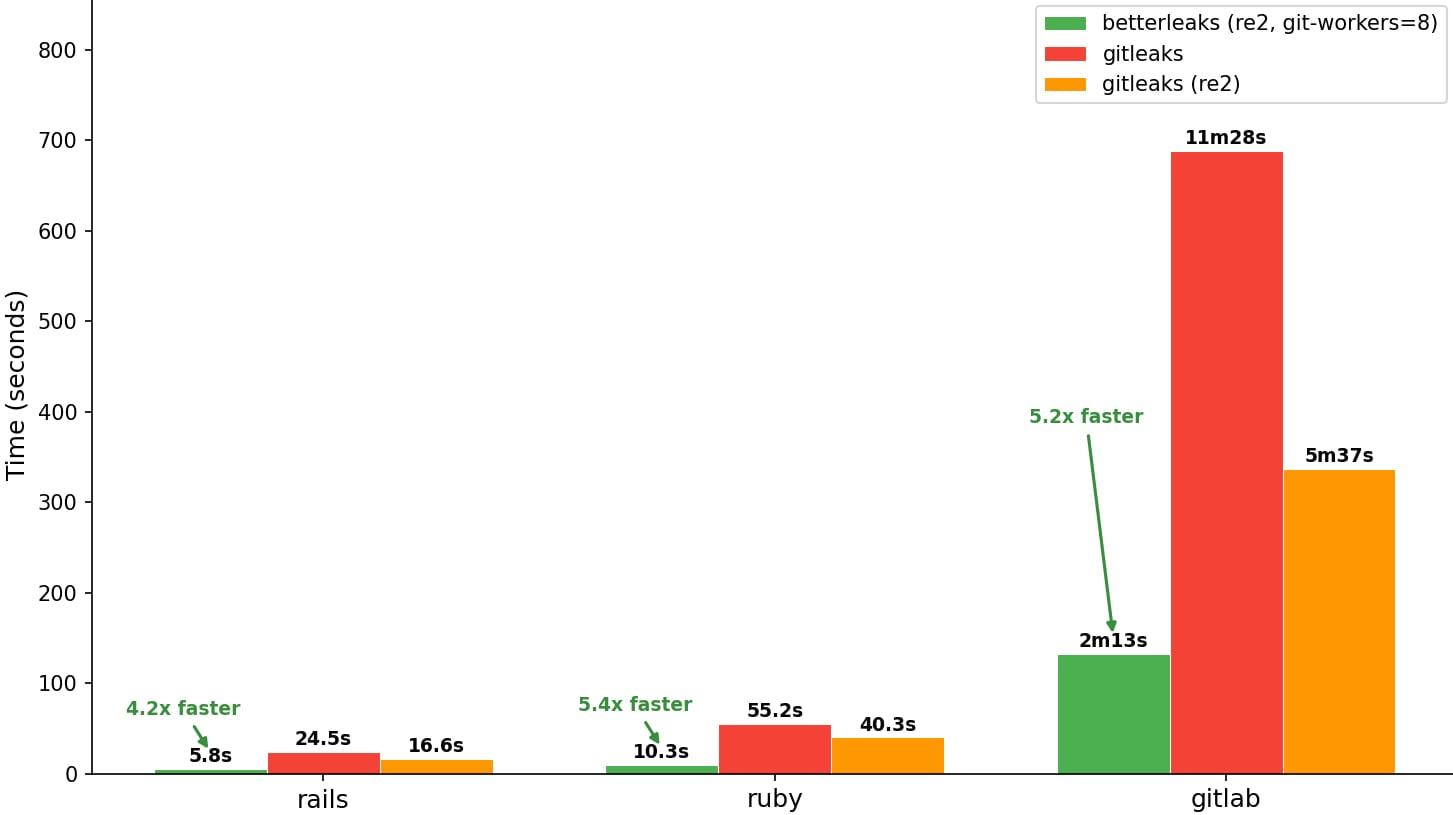
The engineering philosophy behind Betterleaks prioritizes tangible performance gains and expanded utility. Early comparative data, disseminated through the project’s public documentation, suggests significant improvements in scanning throughput when contrasted with legacy tools. This performance enhancement is vital as codebase sizes continue to swell and the velocity of commits accelerates across large engineering organizations. Beyond raw speed, Betterleaks is being architected with an eye toward future development paradigms, notably the increasing integration of Artificial Intelligence (AI) in coding workflows.
Industry Context and Architectural Evolution
The proliferation of secrets exposure is not just a development oversight; it represents a systemic risk that impacts compliance, reputation, and financial stability across virtually every industry utilizing modern software practices. Historically, secrets scanners relied heavily on sophisticated Regular Expressions (regex) patterns—long strings designed to match the known formats of various keys (e.g., AWS Secret Access Keys, GitHub Personal Access Tokens, various JWT structures). While effective for known patterns, regex-based scanning suffers from two primary limitations: high false-positive rates (detecting patterns that aren’t actual secrets) and an inability to catch novel or proprietary secrets formats until rules are manually updated.
Betterleaks appears to be addressing these inherent limitations through a multi-faceted approach. While the precise, granular feature set of the initial release may evolve, the roadmap indicates a clear trajectory toward more context-aware analysis. The explicit mention of planned features such as LLM-assisted analysis for better secret classification signifies a paradigm shift. By integrating Large Language Models (LLMs), the scanner can potentially move beyond simple pattern matching to evaluate the context in which a potential secret appears—for instance, analyzing surrounding code comments, file names, and data structure usage—to assign a more accurate confidence score to a potential finding. This transition from syntactic detection to semantic understanding is crucial for reducing alert fatigue among security teams.

Furthermore, the scope of scanning is expanding beyond the traditional boundaries of Git history. The planned support for additional data sources beyond Git repositories and files suggests an ambition to secure artifacts generated throughout the entire software supply chain, potentially including container images, build artifacts, and cloud infrastructure-as-code (IaC) templates. This holistic approach aligns with broader DevSecOps trends that emphasize security visibility across the entire application lifecycle, not just the source code repository stage.
Governance and Community Commitment
A key differentiator for any successful open-source project is its governance model and the diversity of its contributor base. Betterleaks is operating under the permissive MIT License, fostering maximum adoption and modification potential. Crucially, the project is not solely dependent on its original author. Rice confirmed the active involvement of three additional core maintainers, bringing expertise from significant players in the enterprise technology and financial sectors, including contributors affiliated with the Royal Bank of Canada, Red Hat, and Amazon. This distributed maintenance structure provides resilience and ensures that the tool’s development incorporates diverse, real-world enterprise security requirements.
The project’s design philosophy explicitly targets the dual nature of modern development: human-centric workflows and the burgeoning domain of AI agent workflows. As developers increasingly rely on generative AI tools (like GitHub Copilot or specialized coding assistants) to draft boilerplate or complex functions, the risk of those assistants inadvertently suggesting or inserting sensitive information rises exponentially. Betterleaks’ commitment to CLI features optimized for automated tools that scan AI-generated code indicates an understanding that security scanning must adapt to how code is being written, not just where it is stored. This foresight positions Betterleaks to address security blind spots introduced by generative coding technologies.
Expert Analysis: The Imperative for Validation and Remediation
The utility of a secrets scanner is intrinsically tied to its ability to validate the findings it reports. A scanner that reports thousands of non-functional tokens is effectively useless. The planned feature of automatic secret revocation via provider APIs represents a significant leap forward in automated remediation capabilities.
Currently, when a secret is discovered, the standard workflow is:
- Scanner identifies potential secret.
- Security analyst manually verifies if the secret is active and what resources it grants access to.
- Analyst navigates to the respective provider console (e.g., AWS IAM, Azure Portal, Salesforce).
- Analyst manually revokes the specific credential.
This process is slow, error-prone, and often results in delayed remediation, leaving the secret active for hours or days. Integrating direct API revocation allows for near-instantaneous nullification of compromised credentials upon verification. This capability transforms the scanner from a passive alerting tool into an active defensive mechanism, drastically reducing the "dwell time" of exposed secrets—the critical window of opportunity for attackers.
Furthermore, the inclusion of permissions mapping suggests a move toward risk-based prioritization. Not all secrets carry equal weight. An API key with read-only access to public telemetry data poses a far lower threat than a root account access key with full administrative rights over a production cloud environment. By mapping discovered secrets to their associated permissions levels (a process requiring integration with cloud identity and access management systems), Betterleaks can empower security teams to triage findings based on actual blast radius, ensuring critical vulnerabilities are addressed first.
Future Trends and The Road Ahead
The trajectory of secrets management is moving toward elimination and abstraction rather than detection and cleanup. While scanners like Betterleaks remain essential for legacy code, configuration drift, and third-party dependencies, the long-term industry goal is the widespread adoption of secure credential injection mechanisms.
Ephemeral Credentials and Identity Federation: The next major trend, which Betterleaks’ advanced feature set seems designed to complement, is the increased reliance on short-lived, identity-based access rather than long-lived static keys. Technologies like AWS IAM Roles Anywhere, managed identities in Azure, and federated identity solutions mean that applications authenticate using verifiable digital identities rather than embedded secrets. When static secrets must be used—for compatibility or specific legacy systems—they should be managed exclusively through dedicated, audited Vault systems (like HashiCorp Vault or cloud-native secrets managers) and never committed to source control.
Shift-Left Security Integration: The focus on optimizing CLI features for automated scanning workflows suggests Betterleaks is being tailored for deep integration into pre-commit hooks and automated build checks. The goal is to prevent the commit itself, rather than detecting the secret minutes later in a centralized repository scan. This "shift-left" philosophy mandates that security tools must be fast, lightweight, and provide immediate feedback to the developer at the point of error.
The planned release schedule hints at a continuous integration cycle, leveraging the community engagement fostered by the MIT license. The promise of more sophisticated detection filters will be essential for fine-tuning scans within massive enterprise codebases that use proprietary internal token formats. Without effective filtering, even the fastest scanner can be overwhelmed by noise.
In summary, Betterleaks represents a significant evolutionary step in the specialized domain of code secrets detection. By leveraging performance optimizations, incorporating context-aware analysis via emerging technologies like LLMs, and focusing heavily on automated remediation pipelines, the project aims to establish a new benchmark for defending against credential leakage—a vulnerability that remains a leading initial access vector for sophisticated cyberattacks. Its success will depend on rapid adoption and continuous refinement driven by its diverse, enterprise-backed contributor base.

