The enduring friction point in digital security architecture remains the user password. Security mandates, intended to fortify identity verification, frequently introduce friction, compelling end-users to revert to easily memorable, predictable character strings. In organizational settings, this often manifests as credentials deeply rooted in the enterprise’s own lexicon and public-facing identity. This behavioral tendency is not a flaw of the user alone, but a predictable outcome of poorly calibrated security policies that prioritize memorability over true entropy.
Cyber adversaries have astutely capitalized on this human factor for years. Crucially, many successful credential compromise operations do not hinge on complex, novel artificial intelligence algorithms or cutting-edge decryption methods. Instead, they frequently initiate with a far more elemental, yet devastatingly effective, strategy: the methodical harvesting of ambient organizational language and its transformation into hyper-specific password dictionaries.
The barrier to entry for this tactic is remarkably low, thanks to readily available, open-source utilities. Tools like Custom Word List generators (CeWL) streamline the collection and structuring of relevant vocabulary, making the process efficient, repeatable, and largely invisible to standard intrusion detection systems that look for noisy, broad-spectrum attacks. By focusing on contextual relevance rather than brute-force volume, attackers drastically increase their success metrics while minimizing the digital footprint associated with their efforts.
This pervasive attacker methodology underscores the rationale behind stringent guidance, such as that articulated in NIST SP 800-63B, which explicitly cautions against the incorporation of contextually derived words—including service designations, internal codenames, or user identifiers—into authentication secrets. However, the practical enforcement of such guidelines necessitates a granular understanding of how these targeted wordlists are assembled and operationalized against an organization’s defenses in the field.
The critical divergence in defensive planning arises because a significant portion of current security posture management still operates under the outdated assumption that password guessing relies primarily on massive, generic, publicly available datasets. This assumption leaves organizations vulnerable to attacks tailored specifically to their operational environment.
Deconstructing the Genesis of Contextual Dictionaries
The mechanism underpinning these targeted assaults often begins with the utilization of CeWL, a ubiquitous, open-source web crawling application. Its availability across mainstream penetration testing frameworks, such as Kali Linux and Parrot OS, democratizes the capability for both ethical hackers and malicious actors.
Attackers deploy CeWL to systematically map and ingest content from an organization’s externally visible digital footprint. This process is designed to extract terminology that accurately reflects the organization’s external communication patterns, internal nomenclature that has inadvertently leaked, and industry-specific jargon endemic to that sector. The resulting lexicon is markedly different from generic, pre-compiled password dictionaries because it is inherently relevant to the target.
The power of this derived wordlist is not derived from its originality, but from its intimate familiarity to the intended victims. These harvested vocabularies closely map to the terminology users encounter daily, increasing the statistical probability that such words—or slight variations thereof—form the core of their chosen passwords. For a specialized entity, like a financial institution or a pharmaceutical firm, this could include proprietary project names, service acronyms, or regulatory buzzwords that would never surface in a general-purpose dictionary file.

The Transformation Pipeline: From Public Data to Crackable Credentials
CeWL offers configurability, allowing operators to fine-tune parameters such as crawl depth and minimum word length, effectively filtering out low-signal noise. Once this targeted vocabulary set is established, it forms the bedrock for realistic password candidates through the systematic application of predictable mutation rules.
Consider a large aerospace contractor. Public-facing documentation, press releases, or even careers pages might reveal internal project designations (e.g., "OrionFlight," "ApolloRefit"), specific hardware components, or internal department names. These terms are rarely used as passwords in their raw form. Instead, they function as the foundational element onto which attackers layer established pattern modifications. These modifications include standard variations like numeric suffixes (e.g., "OrionFlight2024"), case changes (e.g., "orionflight"), or the appending of common special characters (e.g., "OrionFlight!").
Once an initial trove of password hashes is obtained—often via third-party data breaches, phishing campaigns, or the deployment of infostealer malware—high-performance cracking utilities like Hashcat are employed to execute these mutation rules across the tailored wordlist at massive scale. Millions of contextually relevant candidates can be generated and tested with extreme efficiency against the compromised hash material. Furthermore, this precise wordlist can be deployed against live authentication endpoints, where attackers leverage rate-limiting evasion tactics, timing analysis, or deliberately slow, "low-and-slow" guessing methodologies to circumvent automated lockout mechanisms designed to thwart less sophisticated, high-volume attacks.
The Failure Mode of Traditional Complexity Mandates
A fundamental challenge facing security architects is that many passwords constructed via this contextual methodology successfully adhere to traditional password complexity requirements. This often leads to a false sense of security.
Extensive analysis of billions of compromised credentials demonstrates a persistent organizational blind spot: even in environments with robust training and awareness programs, the inherent weakness introduced by contextual base terms undermines the perceived strength derived from length or character diversity. A password like "AeroDynamics2025!" might satisfy a mandate for 12 characters, mixed case, and a symbol, but if "AeroDynamics" is the company’s primary public identifier, the entropy is severely degraded. The organizational relevance acts as a massive shortcut for the attacker.
CeWL-generated lists are highly effective at identifying these organizationally significant nouns and abbreviations, enabling attackers to achieve high-probability password variations with minimal, systematic guessing effort. The resulting credential, while technically compliant, offers negligible resistance against an adversary armed with specific internal vocabulary.
Industry Implications: A Shift in Authenticator Policy
The reliance on contextual language highlights a systemic failure in treating passwords as static compliance checkboxes rather than dynamic security controls. This reality necessitates a pivot toward proactive management of password construction itself, rather than merely policing the resulting string’s characteristics.
The Blurring Line Between External Reconnaissance and Internal Compromise: The ease with which public data feeds credential stuffing efforts means that open-source intelligence (OSINT) gathering is now inextricably linked to credential cracking success rates. Security teams must treat their public-facing web presence not just as a marketing tool, but as a potential source for adversary intelligence.
The Inadequacy of Generic Blocklists: Relying on universally available blocklists (like those derived from large, older breaches) is insufficient. While blocking previously exposed credentials remains vital, it fails to address the novel yet contextually weak passwords created daily using current organizational jargon. The industry must adopt dynamic, organization-specific exclusion lists.
Future Impact and Trends in Defense: The trajectory suggests that defenses must move beyond simple password checking towards continuous identity hygiene monitoring. As AI models become more sophisticated at mimicking human language patterns, the distinction between "AI-generated" and "contextually derived" guesses will blur, but the foundational principle—that relevance trumps complexity—will remain true. Future authentication frameworks will likely incorporate real-time checks against proprietary knowledge graphs built from an organization’s own documentation (internal and external) to preemptively flag high-risk lexical combinations.
Architecting Resilience Against Contextual Exploitation
Mitigating the threat posed by context-derived wordlists demands a multi-layered defense strategy focusing on construction validation, proactive monitoring, and compensating controls.
1. Proactive Exclusion of Context-Derived Vocabulary
The most direct defense is preventing the creation of passwords founded on proprietary or organizational identifiers. This involves enforcing policies that actively reject terms identified through reconnaissance, including:
- Organizational Identifiers: Blocking company names, product lines, service acronyms, and historical project codenames.
- Industry Vocabulary: Excluding jargon specific to the sector (e.g., medical terms for healthcare, regulatory acronyms for finance).
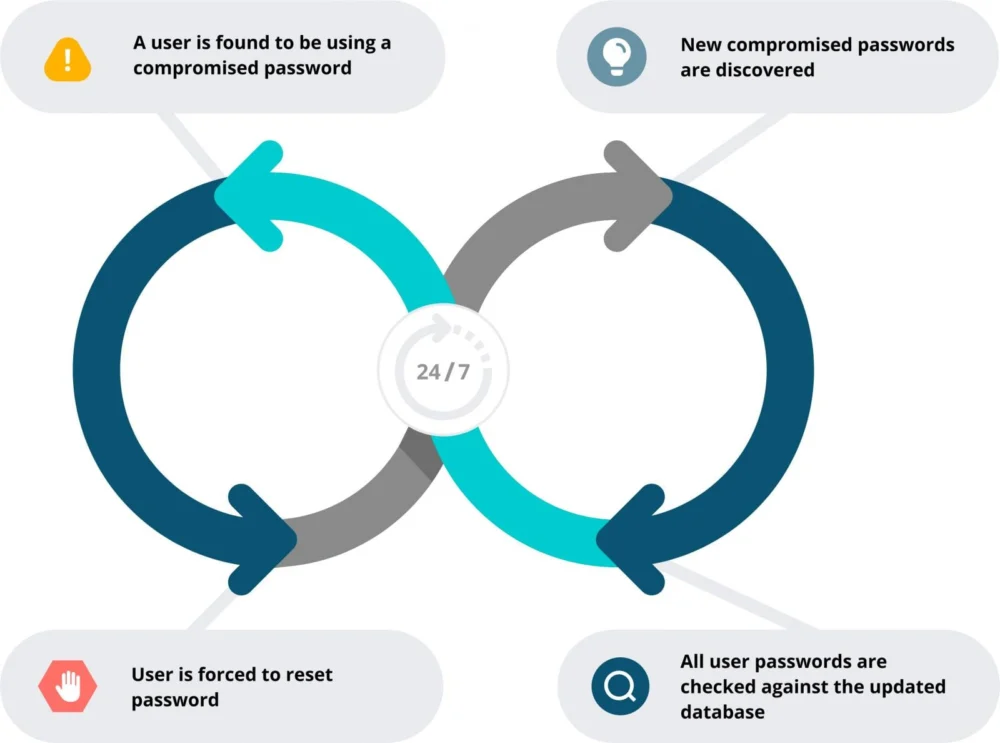
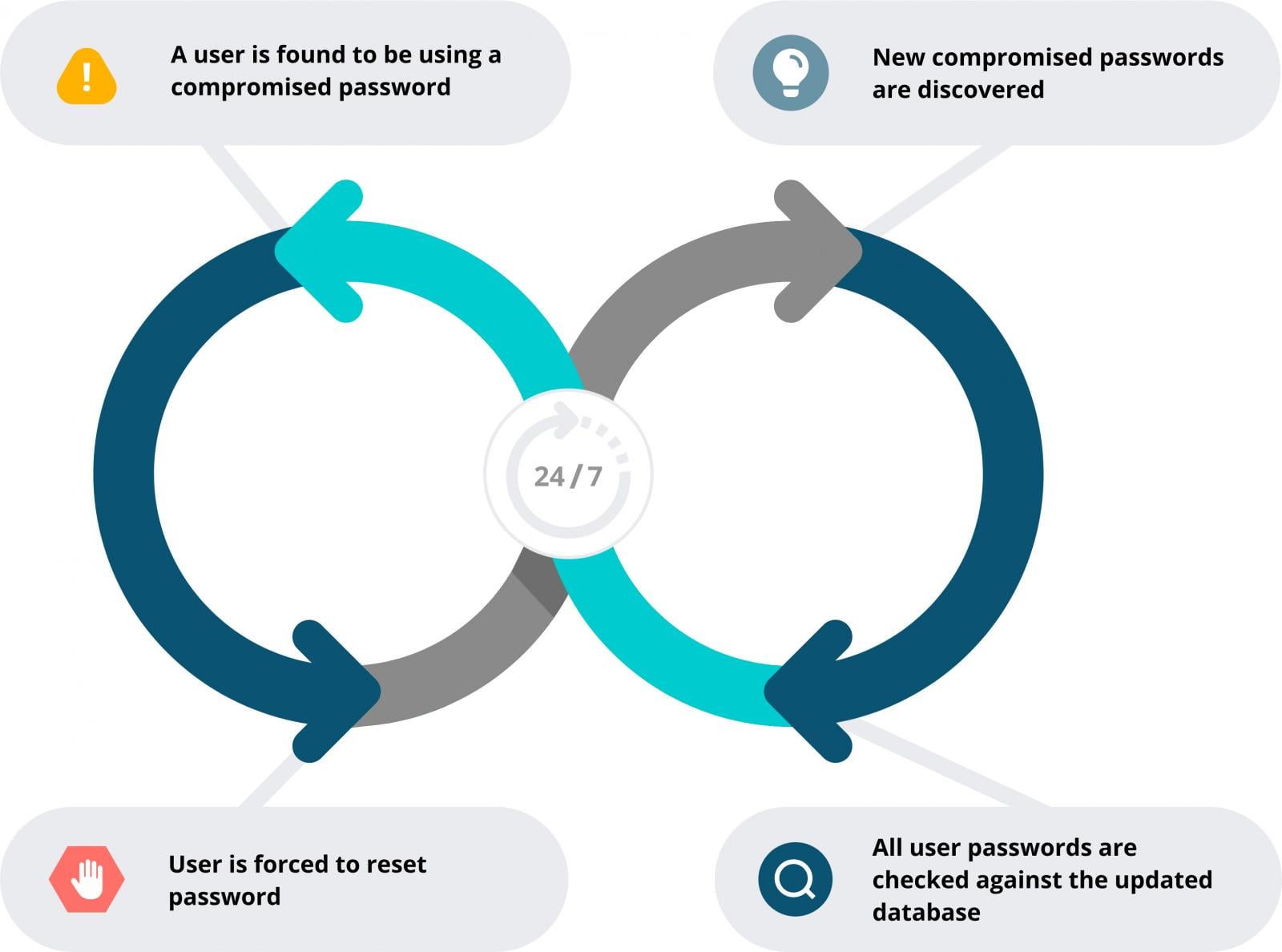
- Known Compromised Sets: Implementing continuous scanning against vast, continuously updated databases of globally breached credentials. This prevents the reuse of exposed secrets, which often overlap with high-probability guesses even when users attempt modification.
Advanced password policy enforcement tools can now integrate custom exclusion dictionaries, which security teams can populate with intelligence gathered from their own threat intelligence feeds or automated reconnaissance sweeps. This turns the organization’s knowledge of its own internal language into a defensive weapon, directly neutralizing the efficacy of CeWL outputs.
2. Prioritizing Length and Passphrase Construction
While context is the primary weakness, entropy remains the ultimate safeguard against brute-force. Modern security frameworks must aggressively pivot user behavior toward long, unstructured passphrases, ideally requiring a minimum length of 15 characters or more. Passphrases inherently introduce greater randomness than short, complex strings, as users naturally incorporate more words, making dictionary attacks against the entire string exponentially harder, even if one component word is contextually relevant. The cognitive load for users to remember a long, memorable sentence structure is often lower than remembering a complex, arbitrary string of characters.
3. Mandatory Multi-Factor Authentication (MFA) as the Safety Net
MFA deployment must be treated as a foundational, non-negotiable requirement, not an optional enhancement. While MFA does not prevent the initial compromise of a password hash, it effectively severs the link between a compromised credential and unauthorized access. By requiring a secondary factor (such as a hardware token, FIDO2 key, or mobile authenticator), the utility of a perfectly guessed password is reduced to zero unless the second factor is also compromised—a significantly more difficult hurdle for the adversary. The implementation should be comprehensive, covering not just cloud applications but also legacy access vectors like Windows logon, VPNs, and remote desktop protocols (RDP).
Realigning Authentication Strategy with Adversarial Realities
The modern security paradigm demands that password policy be treated as an active, living security control, continuously calibrated against observed attacker tactics. When policies fail to account for how easy it is to build a targeted dictionary from public exposure, they are effectively guaranteeing the success of these low-tech, high-relevance attacks. By enforcing construction rules that eliminate context-derived terms, actively blocking known exposed credentials, and layering MFA across all access points, organizations can construct an authentication architecture that is substantially more resilient and reflective of current threat landscapes. This integrated approach diminishes the return on investment for adversaries relying on simple web crawling and systematic mutation, forcing them toward more resource-intensive, easily detectable methods.