The landscape of digital threat actors has undergone a profound metamorphosis, moving far beyond simple credential scraping. Modern infostealers—sophisticated malware designed for extensive data exfiltration—now function as digital identity constructors, assembling a comprehensive profile of a victim from disparate data fragments. This trend, accelerating over the last year, reveals a disturbing lack of discrimination in targeting; the line between an employee using a corporate VPN and an individual browsing personal finances has effectively vanished in the eyes of the attacker.
These pervasive infections routinely secure not only static login pairs (username/password) but also dynamic session tokens, extensive browsing histories, and contextual user activity metadata. This rich, multifaceted intelligence is then packaged, monetized by initial access brokers (IABs), and subsequently weaponized across an entire spectrum of criminal endeavors, impacting both consumer security and high-value enterprise networks.
To map the true architecture of this illicit trade, researchers at Specops undertook an extensive forensic analysis. Their investigation scrutinized more than 90,000 distinct infostealer data dumps, revealing an aggregation of over 800 million individual records harvested during active compromises. The breadth of the collected data was staggering, encompassing authentication secrets, persistent browser cookies, detailed navigational logs, and sensitive system artifacts residing within the local user directory structures of the compromised machines.
What this deep dive illuminates is a chillingly clear mechanism: infostealer payloads bridge the gap between abstract technical data and concrete, identifiable human beings. By correlating login information with established behavioral patterns and stored personal files, a single initial infection gains persistent, long-term value, far outstripping the short shelf-life of conventional network intrusions.
The Synthesis of Identity: From Credential to Dossier
The most significant danger inherent in these data caches lies in their capacity to weave a tapestry of activity linked inextricably to a single individual. These dumps are notorious for exposing systemic vulnerabilities born of user habit, such as the widespread practice of credential reuse across unrelated platforms. Furthermore, they lay bare Windows usernames, the contents of user-specific file directories, active session state data, and granular records of user interaction across multiple digital domains.
When these disparate data points converge, they provide threat actors with a crucial intelligence advantage. An attacker can transition seamlessly from possessing a single compromised login to definitively mapping an individual’s professional affiliation, their likely organizational role, and their established digital habits.
This synthesis effectively dissolves the perimeter that many legacy security frameworks still rely upon—the artificial separation between personal and corporate digital lives. An initial breach, seemingly confined to a home computer or a personal cloud account, possesses the latent capability to cascade rapidly, translating into significant, tangible risk within the enterprise ecosystem. This breach of the personal-professional barrier demands a radical reassessment of internal security postures, as the endpoint is no longer the sole concern; the user identity itself is the compromised vector.
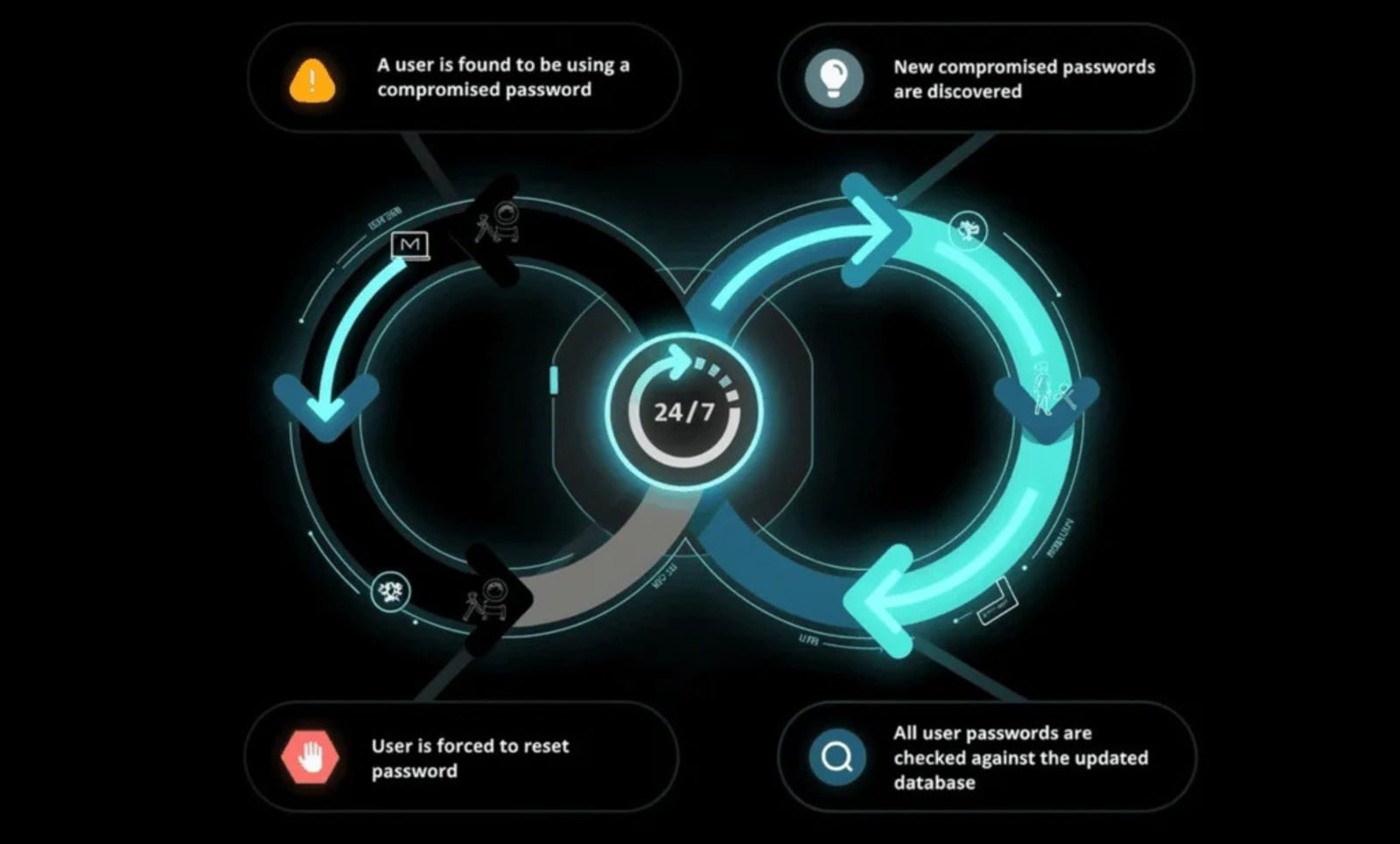
To actively sever this dangerous chain reaction, organizations must implement proactive measures that look beyond initial entry points. Solutions focused on identity governance, such as those continuously auditing Active Directory against vast repositories of known-compromised credentials (exceeding 5.4 billion records in some analyses), represent a vital shift. By enforcing checks not just at the moment of password creation or reset, but continuously throughout the credential lifecycle, security teams can preempt the reuse of already exposed secrets, even if those passwords superficially meet standard complexity mandates. This continuous validation interrupts the attacker’s primary method of operationalizing stolen data across siloed environments.

The Intelligence Supply Chain: Tracing the Data’s Origin and Application
The analyzed datasets reveal a panoramic view of the services targeted, demonstrating precisely how infostealer payloads monetize both personal identity markers and critical access tokens. The sheer variety underscores the comprehensive nature of the intelligence being gathered.
Enterprise and Professional Nexus Points
Significantly frequent inclusions involved credentials and session data tied to platforms vital to corporate infrastructure and professional networking. LinkedIn, GitHub, Microsoft Teams, Outlook, and various private corporate domain logins were consistently present. LinkedIn data alone provided hundreds of thousands of direct linkages between stolen credentials and verifiable data points: real names, precise job titles, and confirmed organizational structures.
For sophisticated threat actors, this professional data is gold. It fuels highly tailored spear-phishing campaigns, enables hyper-realistic social engineering attacks targeting colleagues or subordinates, and allows for the strategic prioritization of initial access points that promise the deepest penetration into target enterprises—especially where the attacker knows password reuse guarantees lateral movement.
Personal Identity and Social Graph Mapping
The data stream is equally rich in markers of personal life, with platforms like YouTube, Facebook, and other major social media services appearing in high volume. These services are rich sources of personally identifiable information (PII): real names, verified photographs, and established social connections. This PII serves a crucial verification function for the adversary; it allows them to confirm that the technical credentials belong to a living, identifiable person whose digital footprint can be further mapped and exploited. This cross-validation significantly streamlines subsequent targeted exploitation efforts.
High-Risk and Sensitive Sector Exposure
Perhaps most alarming is the presence of authentication material linked to highly sensitive sectors. The research surfaced credentials and active cookies associated with governmental and fiscal institutions, citing examples such as the Internal Revenue Service (IRS) and the Canada Revenue Agency (CRA), alongside credentials for adult content platforms.
The risk profile extends beyond mere account takeover when dealing with these services. Data harvested from sensitive portals can be used for financial fraud or identity theft. When combined with leverage derived from personal, potentially compromising data (such as that sourced from adult platforms), the potential for extortion, blackmail, and irreparable reputational damage skyrockets, particularly when the victim’s employer is identifiable through the same dataset.
The Paradox of Security Awareness
The presence of credentials for domains like Shodan (a search engine for internet-connected devices) and even military-affiliated domains (e.g., mil.gov) underscores a counterintuitive reality: high levels of technical literacy or engagement in security-conscious communities do not confer immunity against these pervasive malware families. Users who are diligent within their controlled corporate environments often fail to maintain equivalent vigilance on personal devices. Yet, because these personal systems frequently touch corporate resources (via cloud synchronization, shared documents, or reused passwords), the vulnerability created on the personal side immediately translates into an active, exploitable risk vector for the organization.
Underlying Drivers of Infostealer Efficacy
The sustained effectiveness of infostealer malware is not attributable to a single technological flaw but rather the compounding effect of widespread, ingrained user behavior patterns executed across millions of endpoints. These patterns include the casual installation of software from untrusted or illicit repositories, the ubiquitous practice of password recycling between professional and personal accounts, and the fundamental reliance on built-in browser password managers for convenience.
Browser-based credential vaults and stored payment information represent an apex target for these malware strains. Upon successful infiltration of a system, these native stores offer attackers immediate, high-fidelity access to critical, immediately actionable intelligence, dramatically amplifying the return on investment for a single, successful malware deployment.
Containment Strategy: Mitigating the Post-Compromise Reality
Once infostealer intelligence has been extracted, cataloged, and injected into the illicit marketplace, the defensive focus must pivot sharply from pure prevention to rapid, aggressive containment. The central challenge becomes neutralizing the data’s utility before it facilitates widespread lateral movement, significant account takeovers, or the deployment of ransomware payloads.
Given that infostealer caches frequently circulate within underground forums for weeks or even months prior to detection or widespread mitigation, security protocols must operate under the assumption that certain organizational credentials are already compromised.
Password reuse remains the single most reliable mechanism for adversaries to weaponize this harvested data. Credentials exfiltrated from a personal endpoint are systematically tested against corporate VPNs, cloud access gateways, SaaS applications, and internal network authentication services. This process frequently yields success even when the reused password conforms to basic complexity requirements set by the organization.
Therefore, the most potent countermeasure involves directly disrupting this reuse cycle. By systematically blocking the use of any password already flagged in global breach intelligence, organizations drastically diminish the operational currency of the stolen datasets and compress the window of opportunity for exploitation.
This active containment must be paired with robust, modern password policies that favor length and complexity over arbitrary character constraints—specifically supporting the adoption of strong, long-form passphrases. These controls transform password management from a static, once-a-year configuration task into a dynamic, ongoing containment strategy.
As the primary source of identity compromise increasingly originates outside the traditional corporate perimeter, the proactive management of credential reuse and the mitigation of downstream impact from external theft are paramount. This strategy is essential for dismantling the sophisticated, identity-driven attack chains fueled by modern infostealer malware. Organizations that fail to integrate continuous credential validation into their identity access management face an escalating and potentially catastrophic risk exposure derived from the compromised digital lives of their employees.
The future of enterprise defense hinges on recognizing that the user’s personal digital security footprint is now an inseparable component of the corporate security posture, demanding holistic, persistent protective measures against malware designed specifically to exploit that convergence.