The digital fortress of cryptocurrency security, heavily reliant on hardware wallets like those manufactured by Trezor and Ledger, is facing an unexpected, tangible threat: malicious physical correspondence. Cybercriminals are pivoting from ubiquitous email phishing to highly targeted, sophisticated "snail mail" campaigns designed to trick users into surrendering the keys to their digital wealth—their recovery phrases. These attacks leverage official-looking letterhead and manufactured urgency surrounding mandatory security updates to lure victims toward fraudulent digital endpoints.
The Reemergence of Physical Social Engineering
The latest wave of attacks represents a significant escalation in threat actor methodology. While digital phishing—via email, SMS (smishing), or direct messaging—has become the baseline for crypto-related fraud, the deployment of physical letters injects a layer of perceived legitimacy and psychological pressure. The mere act of receiving official-looking mail, printed on high-quality stationery purportedly from the security or compliance departments of Trezor or Ledger, bypasses the standard digital spam filters and skepticism that seasoned crypto holders have developed.
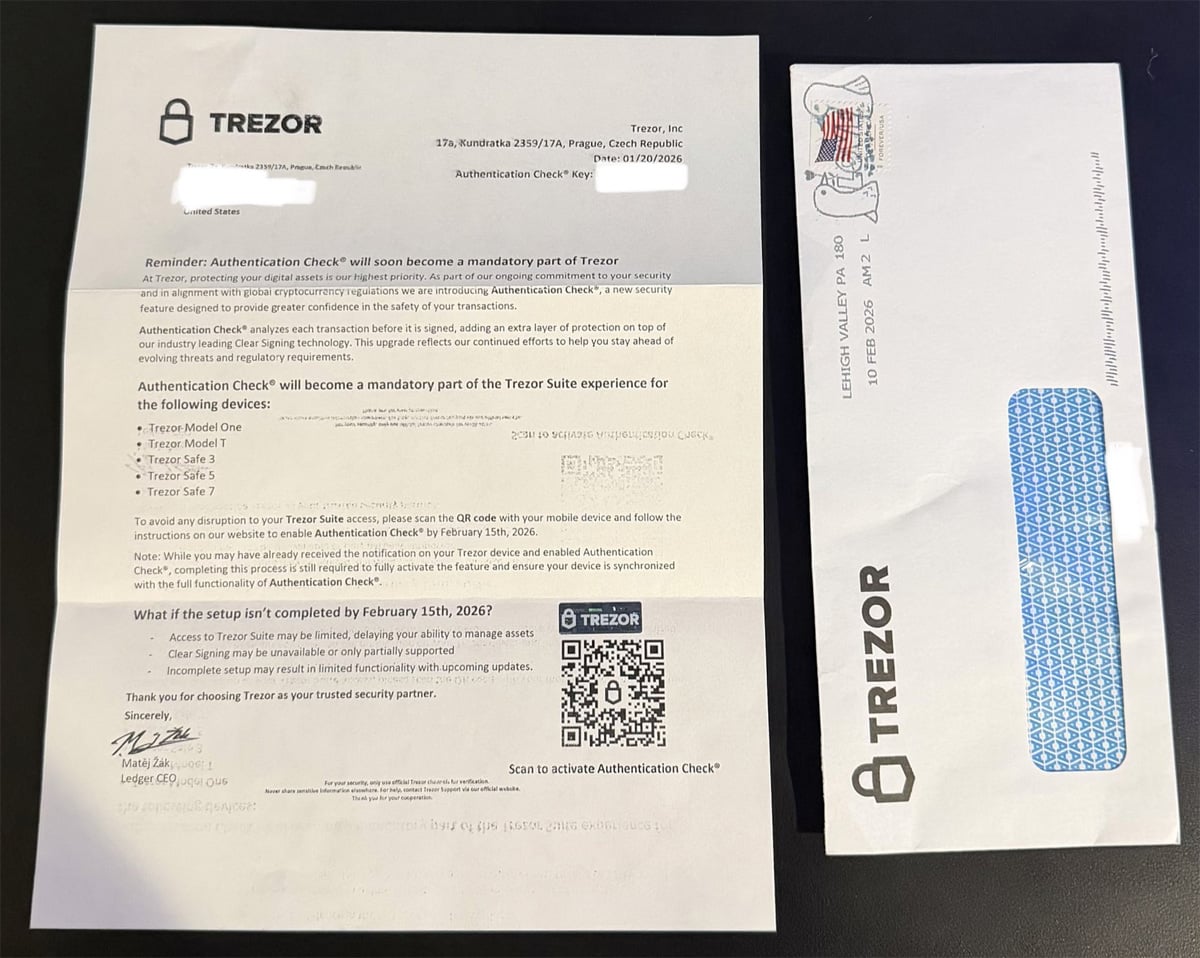
These letters employ common social engineering tactics, centering on fabricated requirements such as a mandatory "Authentication Check" or "Transaction Check." The implied threat is severe: failure to comply by a specific, impending deadline—as seen in reports citing dates like February 15, 2026, for a fake Trezor update—will result in the functional disruption or outright loss of access to their hardware wallet functionality, including the ability to sign transactions or receive future software updates.

The mechanism of compromise is the inclusion of a QR code within the letter. This visual trigger directs the recipient, often using a mobile device, to a malicious website disguised perfectly as the legitimate setup or verification portal for their hardware wallet. This process effectively bridges the secure, offline environment of the physical hardware wallet with a compromised online vector, setting the stage for the final theft.
Tracing the Data Leakage Trail
While the technical execution of the QR code redirection is digital, the targeting relies on compromised personal data. It is critical to note that both Trezor and Ledger have, in recent years, been subjected to significant data breaches that exposed customer contact information, including physical mailing addresses.
For example, past security incidents affecting Trezor have resulted in the exposure of user data, and Ledger has also experienced high-profile data leaks revealing customer addresses. These breaches provide threat actors with the necessary intelligence—the recipient’s name and confirmed ownership of a specific type of hardware wallet—to craft convincing, personalized physical phishing material. The presence of specific, future-dated compliance deadlines (like the February 2026 date mentioned in one observed Trezor sample) suggests a sophisticated, long-term planning horizon by the criminal enterprises executing these campaigns.
Cybersecurity researcher Dmitry Smilyanets documented an example of a Trezor-impersonating letter that explicitly stated: "To avoid any disruption to your Trezor Suite access, please scan the QR code with your mobile device and follow the instructions on our website to enable Authentication Check by February 15th, 2026." The letter even included misleading reassurance, stating that even if the user had already seen an on-device notification, completing the physical mail instruction was "still required to fully activate the feature." This complexity is designed to sow doubt and force compliance.

A parallel campaign targeting Ledger users utilized similar psychological pressure, demanding a "Transaction Check" be completed by October 15, 2025, via a QR code scan to prevent service disruption.
Deconstructing the Phishing Funnel
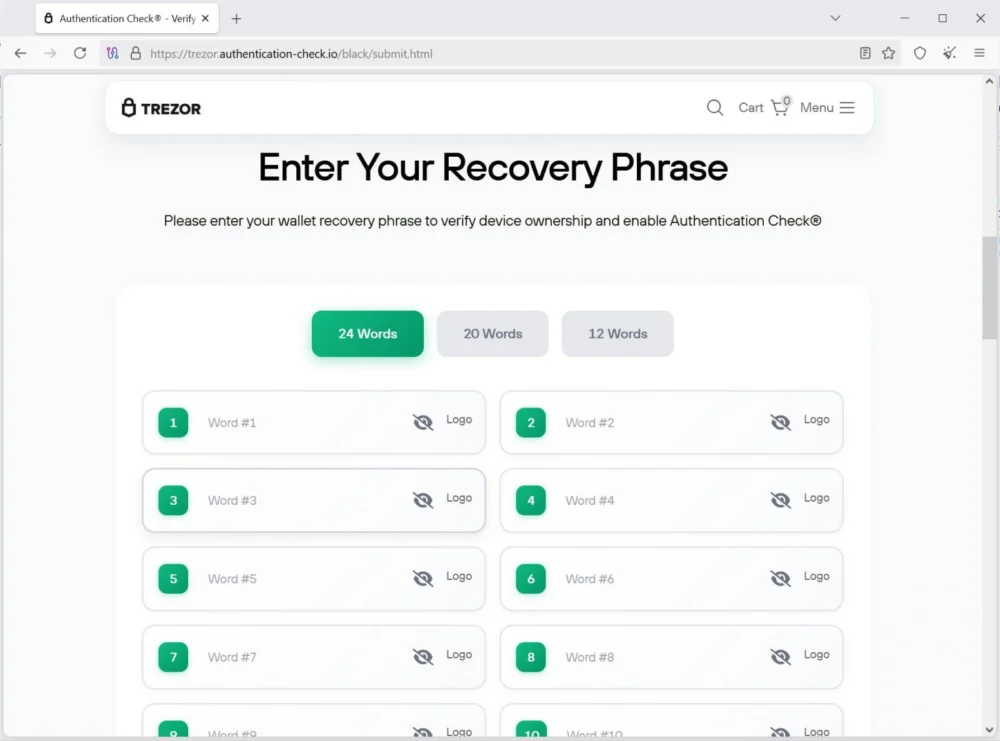
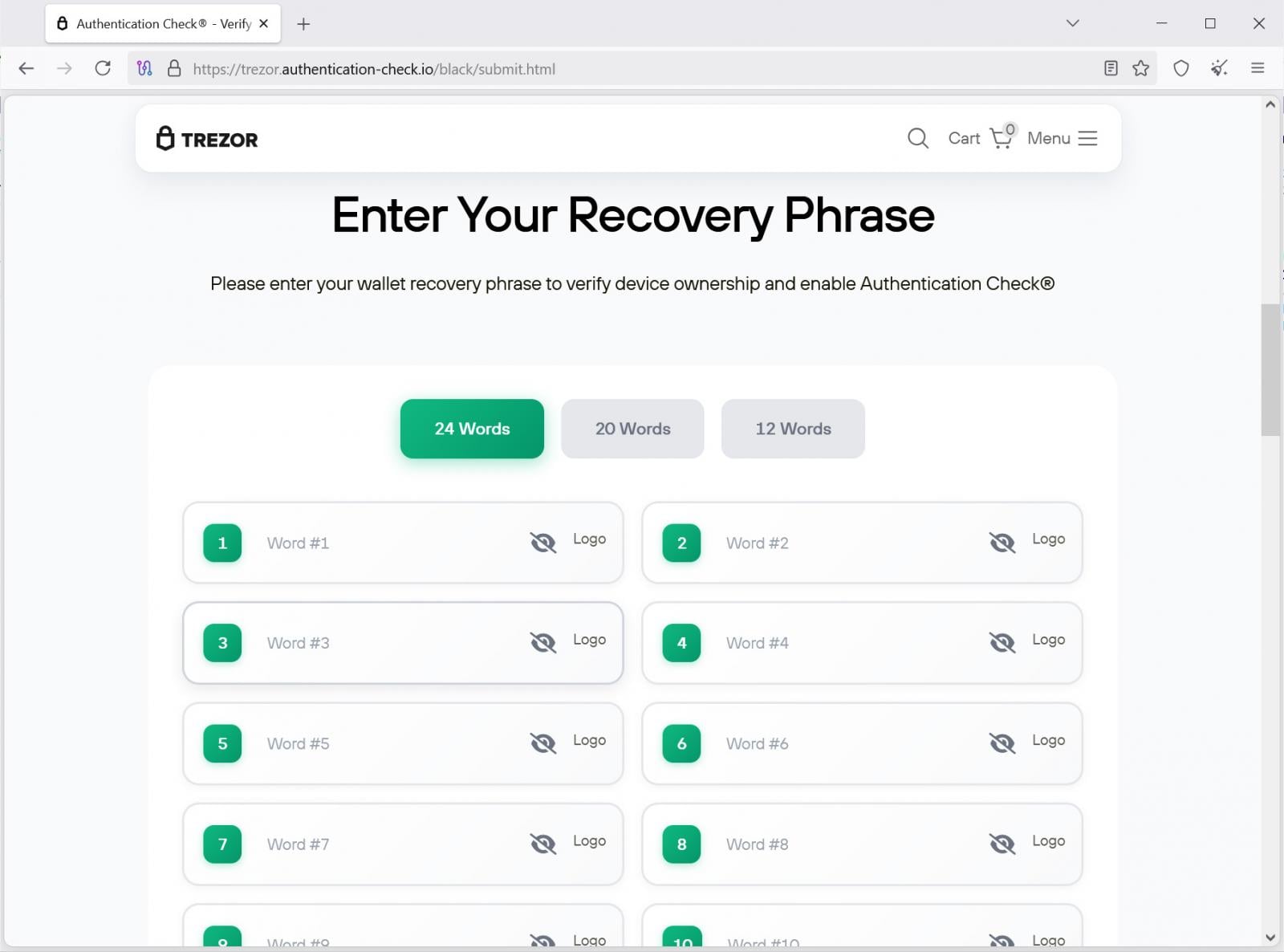
Once the victim scans the QR code, they enter a carefully constructed digital funnel designed to harvest the most sensitive credential: the seed phrase.
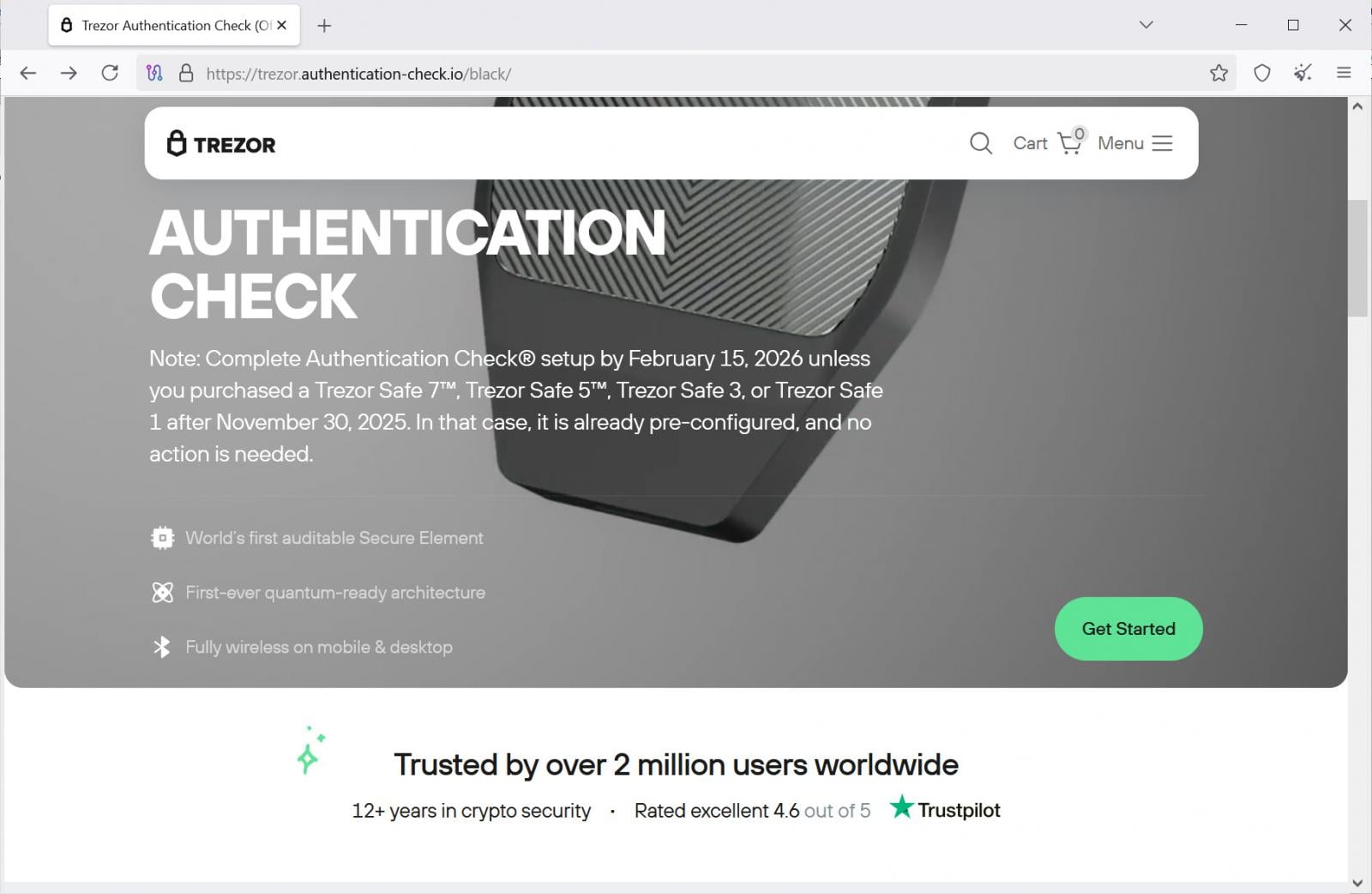
- Impersonation Landing Page: The initial destination mimics the clean, professional aesthetic of the official manufacturer’s setup interface. For the observed Trezor campaign, the phishing site displayed the required deadline and even included conditional logic about newer device purchases (e.g., Safe 7, Safe 5) to make the scheme appear contextually aware of recent product lines.
- Escalation of Urgency: Clicking "Get Started" typically leads to secondary warning screens. These pages amplify the perceived risk, detailing consequences such as "limited or blocked access to Trezor," "transaction signing errors," and incompatibility with "future Trezor updates." This continuous reinforcement of looming catastrophe prevents the victim from pausing to critically evaluate the request.
- The Final Lure (Seed Phrase Input): The climax of the attack involves presenting a screen that ostensibly requires the user to "verify device ownership" or "enable the authentication feature" by inputting their recovery phrase. The site accommodates standard phrase lengths (12, 20, or 24 words).
In the compromised scenario, the entered recovery phrase is instantly transmitted via an API endpoint to the threat actor’s infrastructure (e.g., https://trezor.authentication-check[.]io/black/api/send.php). With the 12, 20, or 24 words, the attackers gain complete, irrevocable control over the victim’s cryptocurrency holdings, allowing them to instantly import the wallet onto their own controlled device and drain the assets.
Industry Implications and Threat Evolution
The shift towards physical phishing, sometimes termed "smishing-by-mail," carries profound implications for the hardware wallet sector and the broader cryptocurrency industry.
1. The Trust Barrier Breach: Hardware wallets succeed because they enforce the principle of "never trust the connected device." By physically mailing documents, attackers exploit the real-world trust associated with postal services and official documentation. This blurs the line between secure offline storage and the digital attack surface, challenging the fundamental security model users believe they employ.
2. Data Monetization and Sophistication: The effectiveness of this attack hinges on the monetization of stolen customer data from previous breaches. It indicates that criminal syndicates are now sophisticated enough to not only acquire massive datasets but also to cross-reference this data with historical hardware wallet ownership records to execute highly personalized, high-value attacks. This level of operational planning surpasses opportunistic cybercrime.
3. Regulatory Scrutiny: As these attacks target the most secure storage methods available to retail crypto users, it may invite increased scrutiny from regulators concerned with consumer protection in the self-custody space. While manufacturers cannot control malicious third-party mail, the perception of vulnerability around customer data management will increase pressure on compliance frameworks.
4. Rare but High-Impact Events: While email and digital phishing remain the most common vectors, physical campaigns are historically rarer but often yield higher returns per successful attack because the social engineering barrier is harder to resist when presented physically. Previous physical attacks have included mailing compromised, factory-reset hardware devices intended to steal the phrase during the initial setup phase, but the current QR code/mandated update approach is a modern refinement.
Expert Analysis and Future Defenses
From an expert security perspective, the core vulnerability exploited here is user behavior and misplaced trust, not a flaw in the cryptographic security of the hardware wallet itself. The device remains secure; the user is tricked into circumventing its security protocols externally.
The critical analysis points revolve around the language used: "mandatory," "authentication check," and the implied threat of service termination. These are classic hallmarks of high-pressure social engineering, designed to bypass rational thought.
Defense in Depth for Self-Custody Users:
The industry standard for defense against seed phrase theft remains absolute: Never divulge the recovery phrase digitally.
- Manufacturer Protocol Adherence: Trezor, Ledger, and all reputable hardware wallet providers maintain a unified security stance: the recovery phrase (seed phrase) is the master key, and it is never requested via email, website, or mobile application for verification, updates, or feature activation. Recovery phrases are entered exclusively via the physical buttons and screen of the hardware device itself during a legitimate device restoration process.
- Verification Protocol: Any communication suggesting a required "check" or "update" involving an external digital input (like a QR code leading to a website) must be treated as fraudulent. Users should independently verify any such claims by navigating directly to the official manufacturer’s website—by typing the URL manually—and checking official security announcements, bypassing any links provided in external communications.
- Physical Mail Skepticism: Users must extend their digital skepticism to the physical world. If a letter demands immediate action regarding a security feature, the first step should be contacting the manufacturer’s official, published support channel (not a number or email listed in the suspicious mail).
Future Trends in Physical Social Engineering
We anticipate that these physical phishing campaigns will become more prevalent as digital defenses mature. Threat actors will likely integrate more advanced physical tactics:
- Supply Chain Interception: Attacks may move beyond mere mailing to intercepting packages containing new hardware wallets, tampering with the packaging, and inserting compromised setup instructions or even compromised devices, mirroring the 2021 activity but with more sophisticated forgery.
- Hyper-Personalization: Leveraging AI to generate highly convincing, grammatically perfect, and contextually relevant letters that reference specific device models or even recent, publicly disclosed minor issues to enhance believability.
- Multi-Vector Attacks: A physical letter might be paired with a follow-up phishing email referencing the mailer, creating a synchronized, multi-channel assault designed to overwhelm the victim’s critical assessment faculties.
For the crypto community, the message is clear: the security perimeter now extends beyond the firewall and into the mailbox. Vigilance regarding the sanctity of the recovery phrase remains the ultimate, non-negotiable line of defense against even the most tangibly executed criminal enterprise.