The conventional wisdom underpinning enterprise security for decades has centered on identity as the ultimate gatekeeper. The foundational security posture assumed that if a robust authentication mechanism—ideally incorporating multi-factor authentication (MFA)—could definitively confirm "who" was accessing resources, the subsequent "what" and "where" could be largely trusted. This paradigm, rooted in the era of clearly demarcated corporate perimeters and standardized, company-owned hardware, provided a coherent framework for access control. However, this structure is proving fundamentally inadequate against the realities of the contemporary digital workplace.
The shift to distributed operations, accelerated by global events, has permanently fractured the traditional perimeter. The modern workforce is a fluid ecosystem, operating across disparate geographical locations, utilizing heterogeneous network infrastructures, and frequently pivoting between managed corporate assets, personal (BYOD) devices, and various third-party contractor endpoints. Access is no longer a singular, predictable event originating from a known location; it is a continuous stream of interactions originating from environments that are inherently less controllable by the organization’s central IT apparatus.
This decentralization has forced security teams into an untenable position: they must simultaneously facilitate unprecedented operational flexibility while maintaining stringent security postures. The challenge is exacerbated because the signals available to inform access decisions—IP addresses, geolocation, time of day, device fingerprints—have become increasingly abundant, yet simultaneously less reliable and more susceptible to manipulation or compromise. Consequently, the burden placed upon identity verification systems has grown disproportionately heavy. While strong authentication successfully validates the claimant’s identity, it offers profoundly limited assurance regarding the risk associated with the connection itself once that initial validation occurs. The critical insight emerging in cybersecurity is that the industry has mistaken verified identity for inherent trust, a flawed substitution that attackers are now systematically exploiting.
Identity Confirms Presence, Not Posture: The Contextual Gap
The inherent limitation of identity-centric security lies in its static nature relative to dynamic threats. A user successfully presenting credentials and passing MFA represents a low-friction entry point for legitimate operations. Yet, the risk calculus changes dramatically depending on the state of the endpoint used for that access. A chief financial officer logging in from a fully patched, compliant, corporate-managed laptop presents a vastly different risk profile than that same officer accessing the exact same sensitive data from an unmanaged tablet running an outdated operating system known to harbor critical vulnerabilities.
Traditional access governance models often fail to sufficiently differentiate these scenarios, frequently defaulting to a static grant of access based predominantly on the successful authentication event. Device posture—the real-time health, configuration, and security compliance of the accessing endpoint—is relegated to a secondary or even tertiary check, often executed only once at the initial login.
This snapshot-in-time approach ignores the inherent volatility of endpoint security. Devices are not static entities; they are constantly evolving. Configurations can drift as users disable endpoint detection and response (EDR) tools to troubleshoot a minor issue, system updates can be deferred indefinitely, or, more dangerously, the device may become silently compromised between the initial authentication check and subsequent high-value transactions. If the access decision is locked to the state recorded at login, the system continues to extend trust long after the device’s risk profile has degraded into an active liability. This persistence of misplaced trust forms a significant blind spot in the modern security architecture.

This vulnerability is particularly pronounced in areas that have historically lagged in the adoption of modern conditional access frameworks. Legacy protocols, legacy Remote Desktop Protocol (RDP) connections, older VPN infrastructures, and non-browser-based application workflows often process access requests with minimal contextual metadata. In these opaque pathways, trust is established based almost entirely on the successful presentation of identity, often without continuous re-evaluation of the device’s integrity.
The Attacker’s New Playbook: Circumvention Over Confrontation
The industry’s investment in strengthening identity layers—especially MFA—has forced threat actors to pivot their strategies. Direct confrontation with strong authentication is resource-intensive and often detectable. A far more efficient strategy involves circumventing the need to break authentication entirely. If an attacker can obtain valid credentials (through phishing, credential stuffing, or dark web marketplaces) and leverage an already compromised, yet ostensibly “trusted,” endpoint, they can effectively bypass perimeter defenses designed to stop the initial intrusion.
This phenomenon, often summarized as "it’s easier to log in than break in," highlights the strategic failure of over-indexing on identity. Session hijacking, token theft, and the abuse of existing, authenticated sessions via compromised endpoints are becoming the preferred vectors. The goal is no longer to defeat the front door lock (MFA) but to exploit the fact that once the door is unlocked, the security system assumes everything inside the house (the session) is safe. This reliance on a validated identity coupled with a degraded device state represents one of the most reliable pathways for advanced persistent threats to maintain footholds within sensitive corporate environments.
The Zero Trust Paradox: Implementation Gaps at the Endpoint
Zero Trust Architecture (ZTA) promises the necessary paradigm shift: never trust, always verify. This principle is philosophically accepted across the security community. However, translating this philosophy into consistent, enforceable policy across the entire distributed workforce remains a significant hurdle. While identity controls, often managed via modern Identity Providers (IdPs), have seen considerable maturation and standardization, the enforcement mechanism often falters or ceases entirely at the endpoint layer.
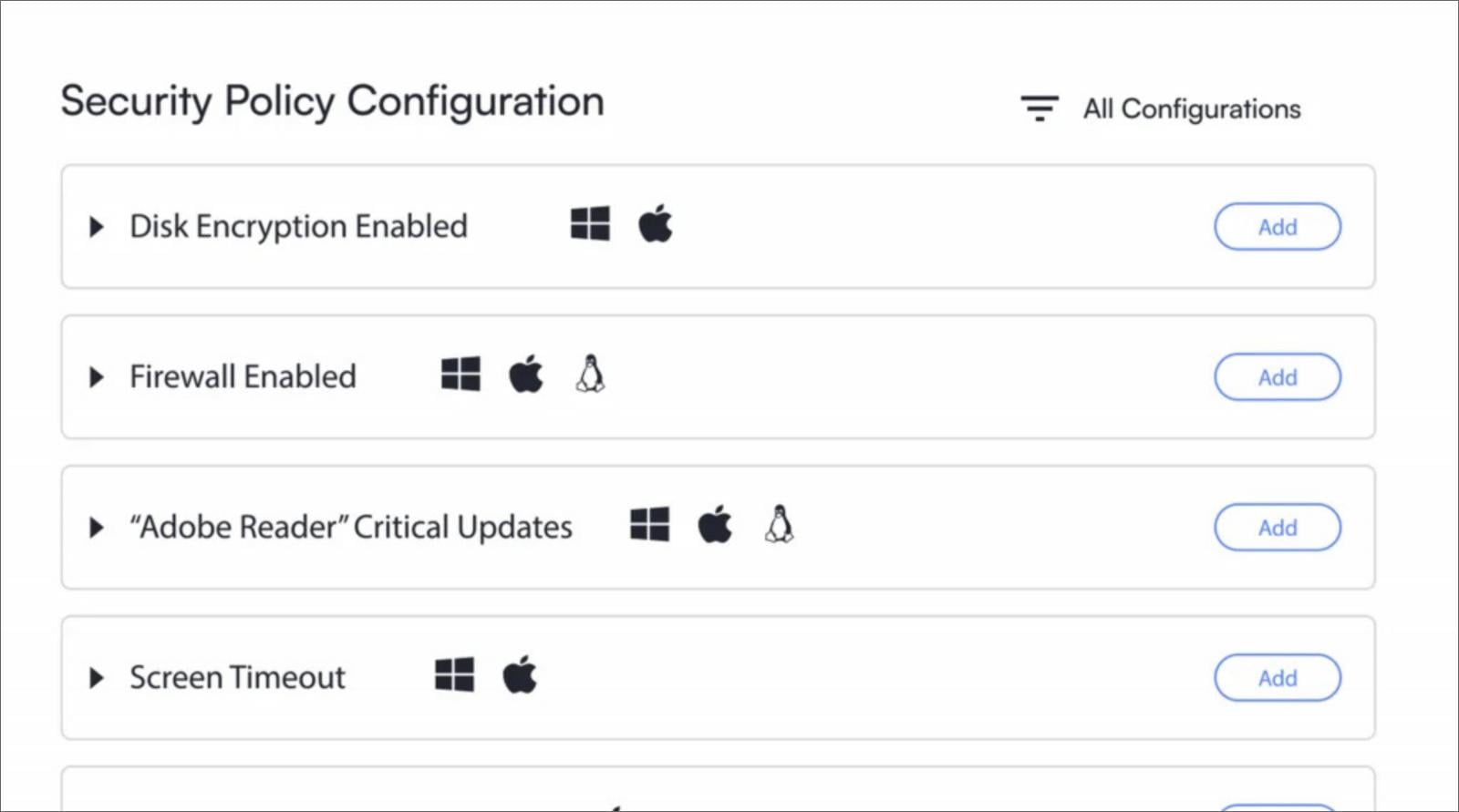
Progress frequently stalls when access pathways deviate from standard, browser-based interactions that benefit from established conditional access policies inherent in modern cloud applications. The difficulty in establishing and maintaining verifiable device trust for unmanaged or personal devices is a major impediment. Consistent, granular assessment of compliance—checking for firewall status, encryption enforcement, running processes, and patch levels—is complex to execute uniformly across diverse operating systems (Windows, macOS, Linux) and mobile platforms, especially when those devices are not centrally enrolled or managed by enterprise Mobile Device Management (MDM) solutions.
Furthermore, where device checks are performed, they often remain static: a compliance check at the moment of connection, rather than a continuous, dynamic evaluation. This complexity drives organizations toward siloed solutions. Identity access management tools operate independently of endpoint security platforms, leading to fragmented visibility and the need for complex, brittle integration layers. When these signals are processed in isolation, the resulting access decisions lack the holistic context required for true risk-based authorization. Over time, security teams often revert to static, overly permissive policies to mitigate the friction caused by these complex, inconsistent checks, thereby inadvertently recreating the very weaknesses ZTA was designed to eliminate.
The Imperative Shift: From Static Authorization to Continuous Verification
To effectively close the security gaps created by the identity-centric hangover, organizations must transition from static authorization based on initial credentials to a model of continuous access verification. This requires an architecture where trust is not a binary state granted at login but a fluctuating score that is constantly re-evaluated throughout the duration of the session.
This architectural pivot demands solutions capable of bridging the persistent chasm between identity verification and real-time device posture assessment. The technology must integrate identity signals with endpoint telemetry—data reflecting the device’s current configuration, security status, user behavior, and network context—and apply policy enforcement dynamically.
Effective continuous verification models must address several critical requirements:
- Ubiquitous Signal Collection: The system must gather comprehensive security telemetry from all relevant endpoints (managed, unmanaged, mobile) regardless of the operating system or access method used.
- Dynamic Trust Scoring: Instead of a simple pass/fail upon login, a dynamic risk score must be calculated and updated in real-time based on changes in the environment (e.g., a critical patch failure detected mid-session, or the user attempting to copy data to an unapproved location).
- Granular Enforcement and Remediation: When risk escalates, access must be adjusted instantly—reducing privileges, demanding re-authentication, or immediately terminating the session. Crucially, for end-user productivity, this process should ideally be paired with automated, low-friction remediation tools that guide the user to restore compliance (e.g., one-click patching or firewall activation) without requiring IT intervention.
The future of secure access rests not on finding a better way to verify who is connecting, but on establishing an unshakeable method for continuously verifying how they are connecting. This approach operationalizes the core tenet of Zero Trust by ensuring that authorization is an ongoing process, tethered inextricably to the security health of the accessing agent, regardless of the user’s authenticated status.
Industry Implications and Future Trajectories
The failure to evolve beyond identity-as-trust has significant industry implications, particularly concerning regulatory compliance and data governance. Organizations subject to stringent regulations (like GDPR, HIPAA, or various financial industry standards) are accountable for the integrity of data wherever it resides or is accessed. If a compliance breach originates from a compromised endpoint accessing data under a persistent, yet invalid, grant of trust, the organization faces substantial liability, even if MFA was technically in use.
The market is responding to this reality by fostering the integration of Identity Access Management (IAM) and Endpoint Detection and Response (EDR) functionalities. Solutions that offer a unified control plane for both identity assertion and device compliance telemetry are becoming essential infrastructure, moving away from disparate, vendor-specific solutions that create visibility gaps.
Furthermore, the rise of remote and hybrid work mandates that security must become invisible to the end-user while being utterly rigorous in the background. Any security measure that introduces significant friction—forcing users through complex troubleshooting steps or lengthy compliance dialogues—will ultimately be bypassed or resented. The successful security framework of the next decade will be characterized by its context-awareness and its ability to enforce policy silently, intervening only when genuine, measurable risk emerges from the device or user behavior. By shifting focus from the initial authentication event to continuous session monitoring and contextual authorization, organizations can finally align their security architecture with the operational reality of the modern, borderless workforce.

