A sophisticated and coordinated cyber-espionage campaign is currently exploiting the standard technical recruitment process within the software development industry, weaponizing seemingly benign coding challenges built around the popular Next.js framework. Security researchers have uncovered malicious repositories disguised as legitimate project assessments, designed not merely to evaluate skill, but to infiltrate and compromise the machines of prospective developers. The ultimate objective of this highly targeted operation is the establishment of persistent remote code execution (RCE) capabilities, the large-scale exfiltration of sensitive intellectual property and credentials, and the subsequent deployment of persistent, multi-stage malware payloads onto compromised host environments.
The Nexus of Recruitment and Compromise
Next.js, an indispensable component of the modern JavaScript ecosystem, serves as the foundation for countless high-performance web applications, leveraging React for the frontend and Node.js for server-side operations. This ubiquity makes it an ideal vector for attackers seeking high-value targets—namely, active software engineers entrusted with proprietary codebases.
The discovery, initially flagged by the Microsoft Defender research team, centers on the deceptive packaging of malware within environments developers are compelled to interact with under professional duress. These malicious artifacts masquerade as typical starter kits or technical evaluation tasks provided during the late stages of a job interview process. While initial analysis focused on a single compromised repository hosted on Bitbucket, subsequent forensic investigation revealed a pattern: multiple repositories exhibiting identical code structures, standardized loader logic, and consistent naming conventions, strongly suggesting a singular, well-resourced threat actor orchestrating a widespread campaign rather than isolated incidents.
The attack hinges on exploiting the trust developers place in local execution environments. Upon cloning the repository—a mandatory first step for any coding assessment—and initiating the project locally (often via standard commands like npm install followed by npm start or similar framework-specific runners), the developer unwittingly triggers a chain of malicious JavaScript execution. This initial execution chain is specifically designed to fetch and inject a more potent, secondary payload—a fully functional JavaScript backdoor—directly into the memory space of the running Node.js process. Because the code executes within the context of an already trusted Node.js runtime, bypassing many traditional endpoint security measures that focus on file-system writes or launching unknown executables, it achieves immediate RCE capabilities on the developer’s workstation.

Deep Dive into Multi-Stage Execution
The efficacy of this attack vector is significantly amplified by the attackers’ use of layered execution triggers and a multi-stage C2 (Command and Control) architecture. This layered approach ensures persistence and stealth, adapting to potential defensive measures encountered during the initial infection phase.
Stage 1: Initial Foothold and Profiling
The initial JavaScript payload, dropped upon the legitimate execution of the cloned project, serves primarily as an informant. Its immediate actions are reconnaissance-focused:
- Host Profiling: Gathering essential system metadata, identifying the operating system, installed software, network configuration, and potentially IDE/editor versions (crucial for tailoring subsequent exploits).
- C2 Registration: Establishing a low-frequency beacon back to the primary command-and-control server. This initial registration is designed to be quiet, often involving passive polling at long, irregular intervals to avoid tripping network monitoring tools looking for rapid, persistent connections.
This stage effectively tags the compromised machine and reports its existence back to the adversary without immediately escalating privileges or downloading large, easily detectable files.
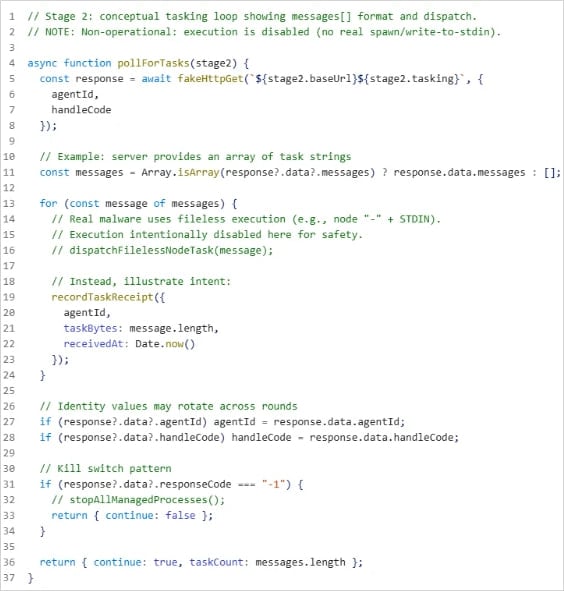
Stage 2: The Tasking Controller and Persistence

Once the host is registered and deemed stable, the Stage 1 payload upgrades the infection by fetching the Stage 2 component—the true tasking controller. This secondary payload establishes a more robust connection to a different, often dedicated, C2 server. The Stage 2 controller is significantly more capable:
- Dynamic Tasking: Instead of relying on static code, Stage 2 actively polls the C2 server for specific instructions. These instructions are executed dynamically within the memory of the running Node.js process, minimizing forensic artifacts on the disk.
- Process Monitoring: The payload possesses the capability to track and potentially manipulate other processes running on the system, a critical step for privilege escalation or moving laterally within the network, should the developer’s machine possess elevated network access.
- Data Staging and Exfiltration: The controller is equipped with functions for file enumeration across accessible directories, directory browsing to map out the local file system structure, and the ability to stage files for eventual exfiltration back to the attacker’s infrastructure. The use of staged exfiltration—breaking large data sets into smaller, encrypted chunks sent over time—further enhances stealth.
The consistent architecture across multiple identified repositories—shared naming conventions, identical loader sequences, and reliance on overlapping staging infrastructure—paints a clear picture of a highly organized, non-opportunistic threat group.
Industry Implications: Eroding Trust in Standard Workflows
This campaign represents a significant escalation in software supply chain attacks, moving beyond tampering with third-party libraries (like the well-documented incidents involving dependency confusion or malicious package uploads) to directly compromising the developer’s local environment via socially engineered delivery mechanisms.
The Erosion of Developer Trust: For decades, the software development lifecycle (SDLC) has relied on the premise that code executed in a controlled, local testing environment is relatively safe, provided the source repository is ostensibly trusted. By weaponizing the very act of technical vetting—the interview coding exercise—attackers are subverting a critical trust relationship. Developers are professionally incentivized to clone, run, and debug unfamiliar code quickly; this campaign exploits that inherent operational necessity.
High-Value Target Acquisition: Developers are uniquely positioned within an organization’s security perimeter. They possess elevated access rights to source code repositories (GitHub, GitLab), cloud infrastructure credentials, internal documentation, and secrets management systems. Compromising a single developer workstation can grant access equivalent to a low-level insider threat, bypassing perimeter defenses entirely. The targeted nature of these Next.js assessments suggests the threat actor is specifically hunting for engineers working at companies utilizing modern JavaScript stacks, often associated with high-growth tech firms or those handling sensitive IP.
.jpg)
Framework Specificity as a Vector: The choice of Next.js is telling. It indicates a deep understanding of current technology trends. Attackers are moving away from general-purpose malware deployment toward framework-specific exploitation, knowing that tailoring the payload to the runtime (Node.js execution context) provides superior evasion techniques compared to platform-agnostic malware.
Expert Analysis: Bypassing Endpoint Defenses
From a security engineering perspective, this attack brilliantly leverages blind spots in modern Endpoint Detection and Response (EDR) systems.
In-Memory Execution and Fileless Persistence: The core evasion technique is the execution of the malicious code directly in memory (exec in memory). By avoiding writing the Stage 2 payload to the disk, the attack circumvents signature-based detection and many file-integrity monitoring tools. While modern EDR solutions monitor process memory, distinguishing between legitimate Node.js script execution initiated by a trusted user (the developer running their test) and malicious execution is challenging without deep behavioral analysis.
Exploiting Trust Boundaries in IDEs: The reliance on standard development workflows exposes the inherent weaknesses in Integrated Development Environment (IDE) security models, specifically around workspace trust. When a developer accepts a coding challenge, they often grant broad permissions to the project environment. Microsoft’s recommendations to enforce VS Code’s Workspace Trust or Restricted Mode are crucial countermeasures. These modes limit the extent to which project files can interact with the host operating system, effectively sandboxing the environment and preventing the malicious Node.js process from reaching out to download external payloads or enumerate the entire file system.
The Role of Node.js Runtime Security: The vulnerability highlights the need for stricter runtime security policies within development environments. Standard Node.js execution inherits the permissions of the user running it. Future security hardening must involve sandboxing the Node.js runtime itself for untrusted code execution, potentially utilizing containerization technologies or specialized V8 isolates for assessment environments, treating any code originating from an external, unverified source with extreme prejudice.
Future Impact and Mitigation Strategies
The propagation of job-themed social engineering campaigns targeting developers signifies a shift toward highly personalized, low-volume, high-impact cyber operations. This model is more resource-intensive than mass phishing but yields significantly better returns by compromising prime targets directly.
Proactive Defense Posture: Organizations must immediately re-evaluate their developer onboarding and assessment procedures. Relying solely on the candidate’s integrity during a technical interview is no longer tenable.
- Containerized Assessments: The most robust defense involves isolating all technical assessments within ephemeral, strictly controlled environments, such as dedicated Docker containers or virtual machines that have zero network access to production or internal corporate resources. These environments should be provisioned with boilerplate dependencies and destroyed immediately after the assessment window closes.
- Credential Hygiene Enforcement: The advice regarding minimizing secrets and using short-lived tokens takes on critical importance. Developer endpoints should be treated as highly privileged access points requiring continuous, risk-based authentication monitoring (e.g., Entra ID Protection). Hardcoded API keys or long-lived credentials in local project files must be eliminated through automated scanning tools integrated into pre-commit hooks or CI/CD pipelines.
- Behavioral Monitoring Over Signatures: Security teams need to prioritize behavioral analysis. Unusual network connections originating from processes typically confined to code execution (like
node.execonnecting outbound to unknown IPs or initiating file enumeration patterns) should immediately trigger high-severity alerts, irrespective of the file’s origin. Attack Surface Reduction (ASR) rules remain a vital layer, blocking common RCE tactics like script execution via Office macros or blocking suspicious process creation.
This Next.js campaign serves as a stark warning: the modern software supply chain vulnerability extends beyond publicly distributed packages to the very interfaces used to hire and integrate new talent. As attackers continue to refine their social engineering tactics to mirror legitimate professional interactions, the security community must adapt by enforcing zero-trust principles even within the developer’s most trusted local workspace. The battleground for supply chain security is increasingly moving from the public repositories to the individual developer’s machine.

