The German Federal Office for the Protection of the Constitution (BfV) and the Federal Office for Information Security (BSI) have issued a critical security advisory, signaling an escalating threat landscape targeting high-value individuals across the European political, diplomatic, military, and journalistic sectors. This threat involves state-sponsored advanced persistent threat (APT) groups employing highly refined social engineering campaigns aimed at compromising secure communication platforms, most notably Signal, but also potentially WhatsApp. The intelligence underpinning this warning suggests a targeted, persistent effort to infiltrate the private communications of key decision-makers, a tactic that bypasses conventional perimeter defenses by exploiting human trust and the inherent functionality of end-to-end encrypted applications.
A defining and alarming feature of this specific campaign, as detailed by the joint security bulletin, is the absolute abstinence from deploying conventional malware or exploiting zero-day vulnerabilities within the messaging application infrastructure itself. This "living off the land" approach focuses entirely on the user interface and the psychological manipulation of the target. By refusing to inject malicious code, the attackers maintain a lower detection profile, making traditional endpoint detection and response (EDR) systems largely ineffective against the initial compromise vector. The entire operation pivots on exploiting established trust relationships, or manufacturing convincing imposters thereof, to trick individuals into willingly surrendering access credentials or authorizing device linking.
The Mechanics of Trust Exploitation: Two Attack Vectors
The intelligence highlights two distinct, yet equally effective, methodologies used by these sophisticated actors. Both variants aim to achieve covert access to sensitive one-to-one and group chats, as well as the victim’s complete contact directory, effectively mapping out their professional and personal networks.
Vector One: The Full Account Takeover via Deception

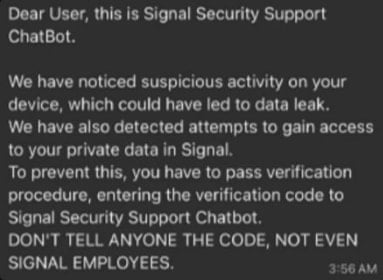
The first methodology mimics a direct interaction with the platform’s official support structure. Attackers initiate contact, often via the targeted messaging app itself, posing as representatives from the Signal support team or utilizing a highly convincing chatbot facade. The narrative employed is typically one of urgency—a fabricated security breach, an account suspension notice, or a required mandatory update requiring immediate verification. This manufactured crisis is designed to bypass critical thinking.
The goal of this phase is the extraction of two critical pieces of information: the user’s Signal PIN or a time-sensitive SMS verification code. The Signal PIN is a crucial security feature intended to protect account registration, while the SMS code is the standard mechanism for initial device authentication. Once an attacker obtains either of these, they can immediately initiate the registration process for the victim’s phone number onto a device under their direct control. The final step in this variant is often the swift disabling of the victim’s access, effectively locking them out of their own account while the attacker assumes full command and control.
Vector Two: The Malicious Device Pairing via QR Code Abuse
The second vector leverages a legitimate, convenience-oriented feature embedded within modern encrypted messengers: linked devices. Features like Signal’s "Linked Devices" or WhatsApp’s "Companion Mode" allow users to securely access their chats across multiple platforms, such as desktop clients or tablets, typically by scanning a dynamically generated QR code displayed on the primary device.
In this scenario, the attacker employs a more elaborate, contextual social engineering ruse. Instead of demanding immediate credentials, they persuade the target that scanning a specific QR code is necessary for a beneficial, security-related, or administrative purpose—perhaps migrating data, resolving a perceived sync error, or accessing a newly deployed, secure government portal. When the high-ranking individual complies and scans the code with their mobile device facing the attacker’s device (or a device controlled remotely by the attacker), the attacker’s device is instantly authorized as a linked client.

The consequence is severe: the attacker gains persistent, real-time access to all incoming and outgoing messages and the entire contact list. Crucially, this method often leaves fewer immediate red flags for the victim. While Signal meticulously logs all linked devices under Settings > Linked devices, intelligence suggests that users, particularly those operating under high cognitive load, rarely audit this section proactively. This allows the malicious link to persist undetected for extended periods, facilitating long-term intelligence gathering.
Broader Industry Implications and the Erosion of Trust
The explicit mention that WhatsApp supports identical device-linking functionality underscores a significant systemic risk across the encrypted messaging ecosystem. While Signal often carries a reputation for superior security protocols, the attack highlights that the security model is only as robust as the weakest link—in this case, user interaction protocols.
This pattern of abusing device linking is not novel, but its elevation to state-sponsored operations targeting senior political and military figures marks an escalation. Previous reports, including those from Google’s threat intelligence teams, linked the QR code pairing technique to Russian state-aligned actors such as Sandworm. Furthermore, Ukrainian CERT-UA has also documented similar methodologies targeting WhatsApp accounts attributed to Russian hackers.
The democratization of this technique is evident. The successful deployment by nation-state actors has lowered the barrier to entry for lower-tier adversaries. Cybercriminal syndicates are now actively weaponizing this method in campaigns like ‘GhostPairing’ to facilitate widespread scams, financial fraud, and identity theft. This diffusion transforms a targeted espionage tool into a generalized cybercrime enabler.
The implications for the security industry and corporate governance are profound. Secure messaging platforms, once viewed as immutable bastions against corporate espionage or state surveillance due to their end-to-end encryption, are now revealed to have exploitable front doors accessible through psychological manipulation. This shifts the focus of defense from purely technical intrusion detection to comprehensive social engineering defense training.
Expert Analysis: The Human Layer as the Ultimate Vulnerability
From an expert analysis standpoint, these attacks represent a successful pivot away from resource-intensive cyber warfare toward cost-effective, high-yield espionage. Developing an exploit for a complex protocol like Signal requires significant technical investment and risks rapid patching by the vendor. Conversely, manipulating a human being to perform an action (like scanning a QR code or typing a PIN) costs virtually nothing and yields immediate results, often without triggering automated security alarms.
The success of these campaigns hinges on two key psychological principles: Authority Bias and Urgency Bias. By impersonating official support channels (Authority), the attackers induce a rapid response (Urgency), overwhelming the target’s natural skepticism. For high-ranking officials whose roles demand rapid decision-making and adherence to protocol, these fabricated scenarios are exceptionally difficult to dismiss without recourse.
Furthermore, the very strength of these platforms—their commitment to user privacy and minimal administrative overhead—creates an inherent security gap. Because the platform administrators cannot intervene or verify user actions for security reasons (maintaining end-to-end integrity), any action authorized by the user, even under duress or deception, is treated as legitimate by the system.
Mitigation Strategies and Future Trends
The German authorities have provided pragmatic, immediate countermeasures, which must now form the baseline for security hygiene among high-risk users.
Immediate User Protocols:

- Zero Trust for Support Interactions: Users must adhere to a strict policy of never responding to unsolicited support messages, regardless of how authentic they appear. Signal, like most E2EE providers, relies on users initiating contact for support; they do not proactively message users regarding security issues. All such messages should be immediately blocked and reported.
- Mandatory Registration Lock Activation: The most powerful technical countermeasure available to Signal users is the "Registration Lock" feature found under Settings > Account. When activated, this requires a user-defined PIN for any attempt to re-register the phone number on a new device. This effectively neutralizes the account takeover vector (Vector One), as the attacker cannot complete registration without the secret PIN. However, the critical trade-off—the risk of permanent account loss if the PIN is forgotten—necessitates secure, off-platform storage for this PIN.
- Vigilant Device Auditing: Regular, perhaps daily, review of the Settings > Linked devices list is non-negotiable for high-value targets. Any unrecognized device pairing must be immediately revoked.
Future Impact and Technological Evolution:
The future trajectory of secure messaging defense will likely focus on incorporating behavioral analytics directly into the application layer. Future iterations of these secure platforms may need to implement contextual awareness:
- Behavioral Anomaly Detection: The system could flag a device pairing request originating from an unusual geographic location or one occurring immediately after an unsolicited inbound message from a "support" handle.
- Multi-Factor Confirmation for Linking: While QR scanning is fast, perhaps critical actions like linking a new device should require a secondary, out-of-band confirmation, such as a biometric check or a temporary code sent via SMS (if the SMS service is deemed less compromised than the in-app communication channel).
- Enhanced Identity Verification: The platforms may need to develop subtle, non-intrusive mechanisms for users to verify the authenticity of inbound communication from "official" accounts without compromising the end-to-end encryption structure.
The security alerts from Germany serve as a potent reminder that in the modern threat environment, the encryption layer is merely a component of overall security. When state actors target senior figures, they invariably choose the path of least resistance. Currently, that path leads directly through human psychology, leveraging the trust placed in modern, essential communication tools. Securing encrypted communications now requires not just strong cryptography, but rigorous, institutionalized skepticism.

