The digital security landscape has been jolted by the revelation of a far-reaching, sustained global espionage operation attributed to a suspected Chinese state-sponsored threat group, internally designated as UNC2814 by threat intelligence analysts. This sophisticated campaign, actively observed since at least 2023, successfully infiltrated the networks of at least 53 high-value organizations across 42 distinct nations, with indicators suggesting potential compromise in nearly 20 additional territories. The primary targets spanned the highly sensitive telecommunications sector and various government agencies, underscoring the strategic nature of the intelligence gathering.
The coordinated disruption of this network was spearheaded by Google’s Threat Intelligence Group (GTIG), in collaboration with Mandiant and several undisclosed partners. This intervention marks a significant victory in the ongoing cat-and-mouse game between defenders and advanced persistent threat (APT) groups, though the threat actor’s resilience suggests a swift re-emergence is probable.
The Stealth Mechanism: Abusing Legitimate SaaS Channels
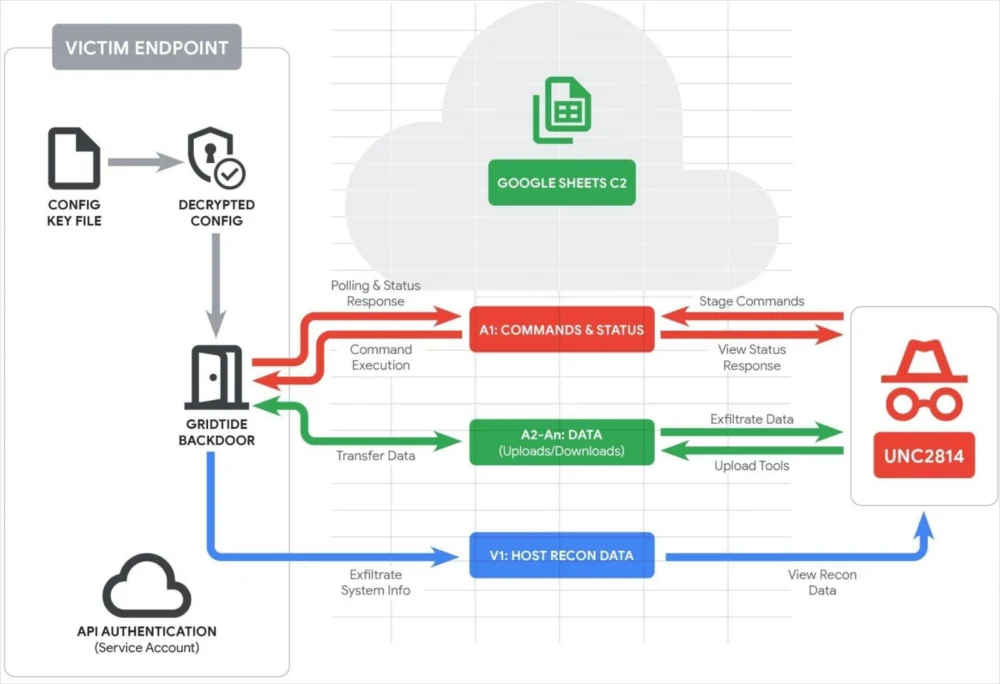
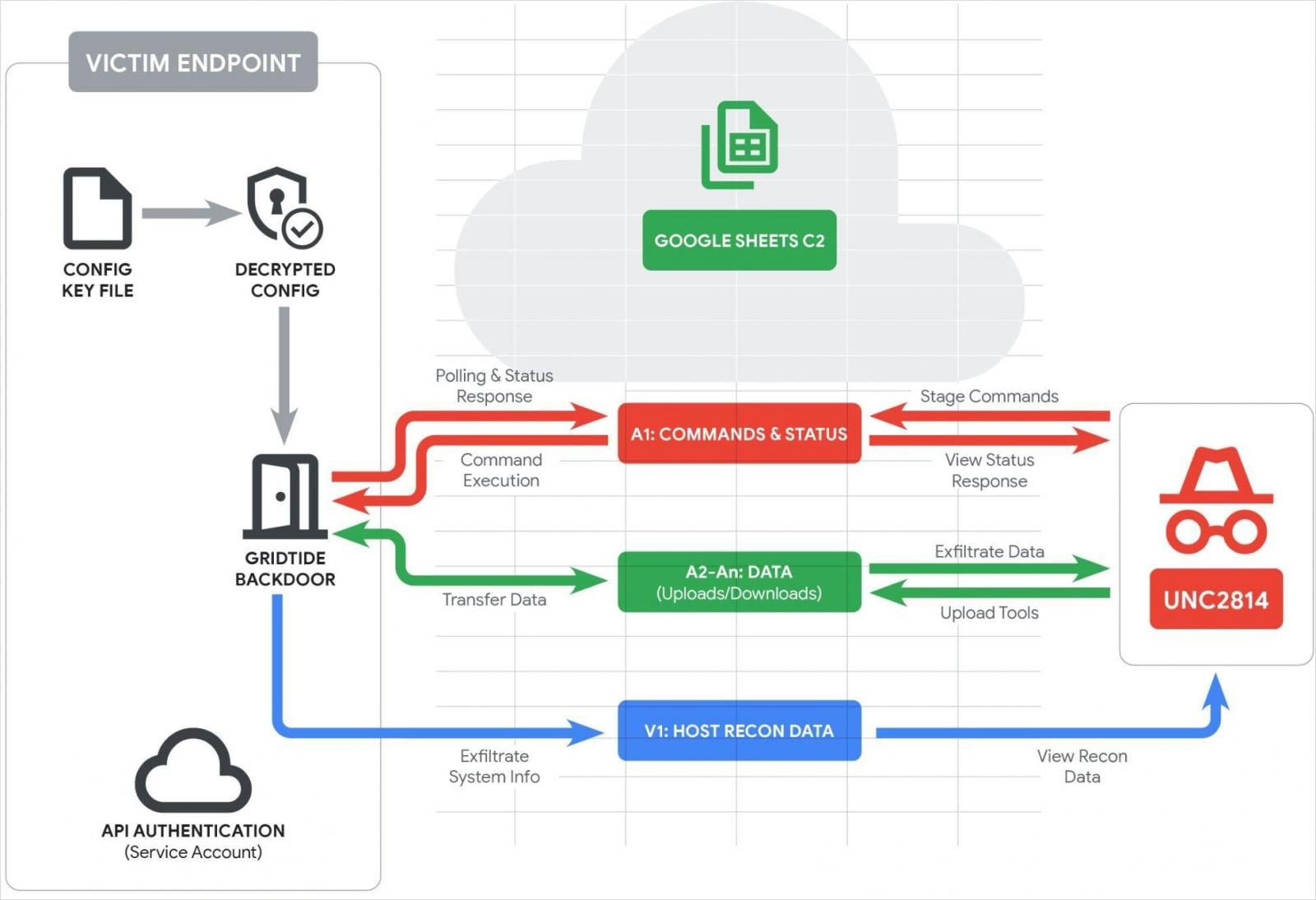
What sets this specific operation apart is the novel and highly evasive command-and-control (C2) methodology employed by UNC2814. Instead of relying on conventional, easily detectable C2 channels such as dedicated external servers or encrypted custom protocols, the attackers deployed a newly identified, C-based backdoor dubbed "GRIDTIDE." This malware ingeniously weaponized the Google Sheets Application Programming Interface (API) to mask malicious communications, effectively embedding its operational traffic within the routine flow of legitimate Software-as-a-Service (SaaS) interactions.

The technical elegance of GRIDTIDE lies in its reliance on a pre-configured Google Service Account. The malware authenticates using a hardcoded private key embedded within its structure, granting it necessary permissions to interact with the specified cloud spreadsheet environment. Upon initialization on a compromised host, GRIDTIDE immediately executes a self-sanitization routine, wiping the first 1,000 rows and columns A through Z of the target spreadsheet. This housekeeping action clears away any forensic residue or previous operational data, ensuring a clean slate for new commands.
Following this preparation, the backdoor initiates host reconnaissance, meticulously cataloging critical system information: user account names, machine hostnames, operating system details, local network IP addresses, system locale settings, and time zone data. This comprehensive host profile is then exfiltrated and stored specifically within cell V1 of the spreadsheet—a seemingly innocuous data point that serves as a crucial status report for the operators.
Command and Control via Spreadsheet Cells
The core of the C2 architecture revolves around the utilization of the spreadsheet’s cells as bidirectional communication channels. Cell A1 functions as the primary command and status exchange point. GRIDTIDE constantly polls this cell, awaiting operational instructions from the UNC2814 infrastructure. Upon receiving a valid command, the malware overwrites the cell content with a status string confirming execution or reporting an error. If the cell remains empty, the malware defaults to an aggressive polling rhythm—checking every second for 120 consecutive attempts. Should instructions remain absent after this initial burst, the polling interval deliberately broadens to randomized windows between five and ten minutes. This strategic throttling is a classic evasion technique designed to mimic low-level, intermittent background activity, thereby minimizing the "noise" that might trigger automated security alerts based on high-frequency external communication.
The communication protocol itself is engineered for maximum stealth. All data exchange between the infected endpoint and the C2 spreadsheet relies on a URL-safe Base64 encoding scheme. This particular encoding method is vital because it ensures that the payload data remains compatible with standard web requests and blends seamlessly with the expected formatting of legitimate API calls to Google services. Web monitoring tools, often configured to flag unusual characters or data patterns associated with known malware traffic, are thus effectively circumvented as the data stream appears structurally identical to routine application traffic.

The operational command set supported by GRIDTIDE, though not exhaustively detailed, appears tailored for typical espionage tasks, including file staging, command execution, and data exfiltration. Cells ranging from A2 onward are reserved for transmitting command output, packaging and preparing files for exfiltration, and facilitating the uploading of additional tools or modules onto the compromised system.
While Google researchers confirmed the presence of GRIDTIDE on at least one system containing sensitive Personally Identifiable Information (PII), direct evidence of mass data exfiltration during this phase of the operation was not explicitly observed. This suggests the actors may have been in the early stages of reconnaissance or were utilizing a secondary, separate exfiltration mechanism not tied directly to the Sheets C2 channel, or perhaps were prioritizing the establishment of persistent access over immediate data theft.
Industry Implications: The Erosion of SaaS Trust
The implications of this attack vector extend far beyond the immediate breach count. The successful weaponization of a widely used, trusted SaaS platform like Google Sheets for C2 communication represents a significant evolution in APT tradecraft. In the modern, cloud-centric enterprise environment, security teams are increasingly focused on monitoring north-south (inbound/outbound perimeter) and east-west (internal lateral movement) traffic. However, the reliance on legitimate cloud APIs introduces a challenging blind spot.
For organizations, particularly those in the telecommunications sector—which manage vast quantities of critical national infrastructure data and customer records—the exposure is acute. Telecoms are often prime targets for nation-state actors seeking intelligence on foreign communications or economic activity. Compromising these networks provides access to an intelligence jackpot.
.jpg)
This incident forces a fundamental reassessment of cloud security postures. It demonstrates that "zero trust" architecture must extend beyond network segmentation and identity verification to encompass the behavior of API interactions. If an application or service account begins querying large numbers of cells, executing unusual shell commands, or consistently transmitting encoded data packets, standard monitoring might miss it because the underlying transport layer—the Google Sheets API call—is inherently considered "safe." Security teams must now implement stricter contextual analysis on SaaS application telemetry, looking for anomalies in data volume, cell access patterns, and command execution sequences rather than solely focusing on the IP addresses or domain names involved.
Background Context: UNC2814 and Evolving Tradecraft
UNC2814 is not a newcomer to sophisticated operations. Researchers note that this actor has historically favored exploiting vulnerabilities within public-facing web servers and edge computing systems to achieve initial access. This pattern—leveraging known weaknesses in internet-exposed devices—remains a bedrock tactic for many APT groups due to its high success rate and relative ease of execution compared to targeted phishing campaigns.
The shift toward leveraging SaaS APIs, however, signals a maturation in their tradecraft, moving beyond simple exploitation to deep operational camouflage. This evolution is likely driven by increased defensive pressure on traditional C2 infrastructure. As organizations deploy better domain blacklisting, sandbox analysis, and encrypted traffic inspection, threat actors are compelled to seek out established, whitelisted communication pathways that are difficult for security tools to scrutinize without generating overwhelming false positives. By embedding C2 within a service like Google Sheets, UNC2814 effectively launders its malicious command structure through one of the most frequently accessed and least suspicious application layers available.
The Coordinated Response and Future Outlook
The response undertaken by Google and its partners was rapid and comprehensive. The disruption involved terminating all Google Cloud projects known to be controlled by UNC2814, effectively decommissioning the infrastructure the threat actor had provisioned for C2 operations. This included disabling known command servers, revoking the specific Google Sheets API access credentials used by GRIDTIDE, and sinkholing both current and historical domains associated with the campaign. Direct notification and remediation support were provided to the impacted organizations to assist in the complete removal of the GRIDTIDE implant.
Security vendors have disseminated specific detection rules and Indicators of Compromise (IoCs) to aid the broader security community in hunting for residual activity.
Despite the comprehensive nature of this takedown, the expectation among intelligence analysts is that UNC2814 will rapidly rebuild and relaunch its operations using fresh infrastructure. This is characteristic of resilient, state-sponsored entities with significant operational funding and strategic objectives. The disruption merely forces a temporary pause and a tactical reset.
Looking ahead, the future impact of this incident points toward several critical security trends. First, the use of legitimate cloud services for malicious C2 will become increasingly normalized. Security platforms must integrate deeper contextual awareness of cloud service usage, treating API calls not just as legitimate traffic but as potential command vectors that require behavioral analysis. Second, the focus on telecom and government targets confirms that geopolitical tensions continue to manifest directly through cyberspace, targeting the foundational elements of national communication and governance. Defenders must adopt a "assume breach" mentality, focusing heavily on post-exploitation detection techniques, particularly those that monitor process behavior and memory artifacts, as perimeter defenses prove insufficient against deeply embedded, evasive implants like GRIDTIDE. The persistent threat posed by UNC2814 underscores that cybersecurity is an enduring arms race, where adaptation to novel evasion techniques is the only path to sustained defense.