A notable and concerning evolution in threat actor methodologies has been uncovered, focusing on highly targeted social engineering campaigns that exploit ubiquitous enterprise communication platforms. Security researchers have identified a coordinated effort specifically targeting employees within critical sectors, notably financial services and healthcare organizations, utilizing Microsoft Teams as the primary vector for initial contact and compromise. This operation pivots on deceiving end-users into facilitating remote access, which subsequently enables the deployment of a novel piece of malware dubbed A0Backdoor. The success of this attack hinges on a multi-stage deception that blends platform familiarity with technical exploitation of trusted system utilities.
The initial phase of the intrusion relies heavily on traditional, yet persistent, social engineering tactics. Threat actors first saturate an employee’s email inbox with a deluge of unsolicited spam. This spam, while perhaps seemingly benign or easily dismissed, serves a crucial preparatory function: to establish a context for subsequent contact. Once the target is sufficiently annoyed or distracted by the volume of unwanted messages, the attackers transition to Microsoft Teams. Within Teams, the adversary impersonates internal IT support personnel. This impersonation is highly effective because the context has already been set by the preceding email deluge; the employee is primed to accept assistance for the very issue that is plaguing them—unwanted communication noise.
Gaining the trust of the victim is paramount for the attackers to achieve their objective: remote desktop access. The attackers shepherd the unsuspecting employee into initiating a session using Microsoft Quick Assist. Quick Assist is a legitimate, built-in Windows remote support utility, frequently used by IT departments globally for troubleshooting. By steering the user toward this trusted tool, the threat actor bypasses many perimeter defenses that scrutinize external remote access software installations. Once the Quick Assist session is established, the attackers gain the necessary foothold to push their malicious payload onto the compromised endpoint.
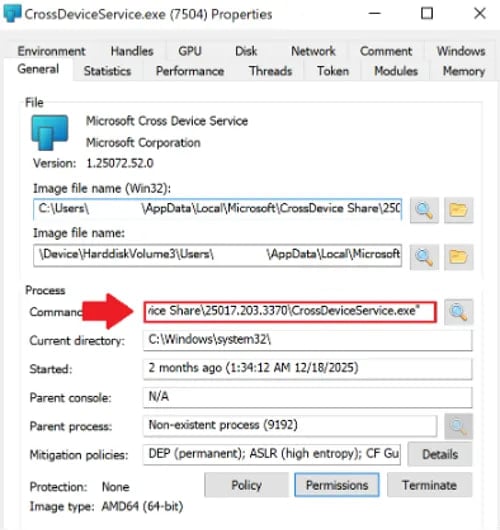
The deployment mechanism showcases a significant degree of technical sophistication. The malicious toolset deployed via the remote session involves digitally signed Microsoft Installer (MSI) packages. These installers are strategically hosted within a personal Microsoft cloud storage account, further leveraging the perceived trustworthiness of the Microsoft ecosystem. The MSI files are cleverly disguised, masquerading as essential components of the Microsoft Teams application itself, or as the legitimate Windows utility, CrossDeviceService.exe, which is associated with the Phone Link application. This deceptive packaging is crucial for evading rudimentary endpoint detection systems that might flag unfamiliar executables.

Upon installation, the attack shifts into a complex low-level execution phase utilizing established evasion techniques. The malicious MSI leverages DLL sideloading, a technique that exploits how Windows searches for and loads dynamic-link libraries. Specifically, the attack targets legitimate Microsoft binaries and tricks the system into loading a malicious library, identified as hostfxr.dll, instead of the expected, trusted version. This compromised DLL is not immediately executable code; rather, it acts as a container for compressed or encrypted data.
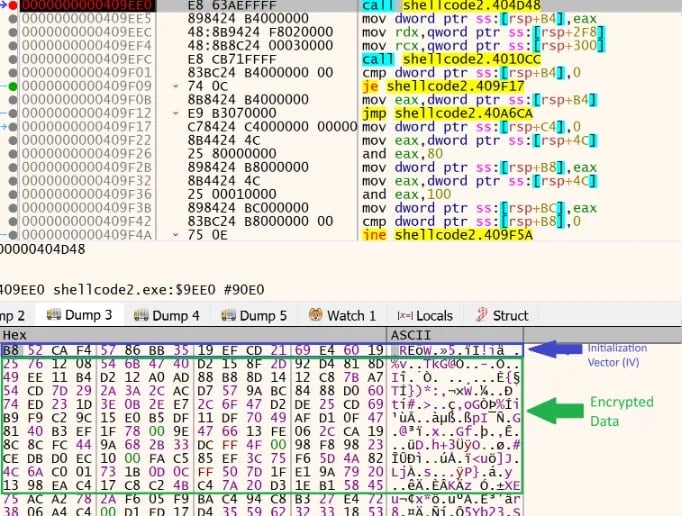
Once loaded into the operating system’s memory space, the malicious hostfxr.dll performs the first layer of execution: it decrypts the embedded data, transforming it into executable shellcode. Security analysis indicates that the threat actors incorporated specific measures to frustrate dynamic analysis efforts. The malicious library employs the Windows CreateThread function in an excessive manner. While researchers note that this high volume of thread creation does not typically impede normal execution on an end-user machine, it is a known method to induce instability or outright crashes in automated debugging environments and sandboxes designed for malware analysis. This acts as a rudimentary form of anti-analysis defense.
Following the creation of the shellcode, the malware undertakes further obfuscation and preparation. The shellcode first executes stringent sandbox detection routines to ascertain whether it is operating within a controlled analysis environment or a live target machine. Upon confirming a live execution environment, it proceeds to derive a key using a SHA-256 hash function. This derived key is then employed in an AES decryption routine to finally extract the core payload: the A0Backdoor malware itself.
The A0Backdoor, once decrypted in memory, exhibits further evasion characteristics. It employs memory relocation, moving its core routines to a fresh, clean region of memory, a technique designed to further confuse forensic investigators tracing execution paths. The malware then focuses on system fingerprinting. It systematically queries various Windows Application Programming Interfaces (APIs), including DeviceIoControl, GetUserNameExW, and GetComputerNameW, to gather comprehensive identifying information about the host system, effectively mapping out the compromised environment for potential future operations.
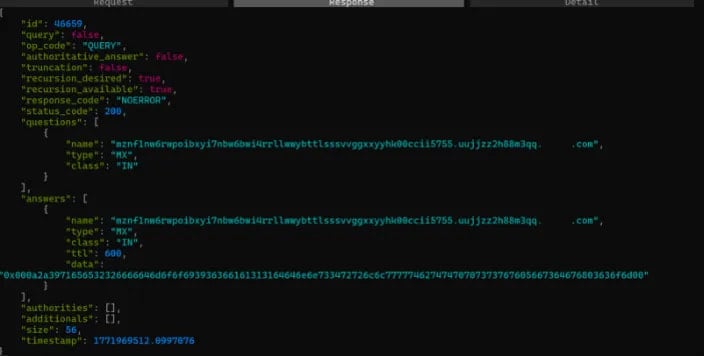
Perhaps the most technically novel aspect of this threat is its Command and Control (C2) communication mechanism. Instead of relying on conventional HTTP, HTTPS, or even common DNS tunneling methods (like TXT records), the attackers have engineered A0Backdoor to communicate exclusively via DNS MX (Mail Exchanger) queries. This method is highly effective for stealth. The malware encodes critical metadata and command requests within the subdomains of these MX queries, sending them out to public recursive DNS resolvers. The C2 server responds not with standard DNS records, but by embedding encoded command data within the MX records returned to the querying endpoint.
As explained by the researchers who documented this activity, this reliance on MX records allows the malware traffic to blend seamlessly into background network noise, as MX record lookups are less scrutinized by many security controls tuned to flag suspicious TXT-based DNS tunneling. The malware is programmed to examine the leftmost label of the received MX record response, where the actual command and configuration data are meticulously hidden and then decoded for execution. This DNS-based exfiltration and instruction retrieval system demonstrates a commitment to maintaining a low operational profile, even after initial system compromise.
The observed targets—a Canadian financial institution and a global healthcare entity—underscore the high-value nature of the actors behind this operation. These sectors are frequently targeted for financial gain, intellectual property theft, or disruption capabilities.
Cybersecurity experts monitoring this campaign have established a moderate-to-high confidence assessment linking this A0Backdoor activity to the historical Tactics, Techniques, and Procedures (TTPs) associated with the BlackBasta ransomware syndicate. BlackBasta was a highly active ransomware group that reportedly dissolved following significant internal data leaks. The persistence of these TTPs suggests that either remnants of the group have reformed under a new structure, or that their established playbooks have been adopted by successor or affiliated criminal enterprises.
While the foundational social engineering steps echo previous ransomware approaches, the specific technical implementation of the A0Backdoor deployment represents an evolution. The consistent use of digitally signed MSIs, the complex DLL sideloading sequence involving trusted Microsoft components, the distinct A0Backdoor payload structure, and, critically, the pivot to MX-record-based C2 communication mark significant tactical deviations from standard ransomware deployment patterns. These advancements suggest an adversary actively refining their toolset to circumvent evolving enterprise security stacks.
Industry Implications and Contextualizing the Threat
The utilization of Microsoft Teams as the initial breach point is not inherently new, but its coupling with Quick Assist represents a dangerous normalization of internal administrative pathways into external compromise vectors. For organizations heavily invested in Microsoft 365 environments, Teams is the central nervous system of internal communication. Security teams must now confront the reality that the tools designed for seamless internal collaboration can be weaponized with alarming efficacy through targeted social engineering.
The financial and healthcare sectors face unique pressures. Financial institutions require absolute data integrity and uptime, making them high-impact targets for ransomware or data exfiltration. Healthcare organizations, dealing with Protected Health Information (PHI) and life-critical systems, are often susceptible to extortion due to the immediate, potentially lethal consequences of operational disruption. This campaign targets the very human element—the employee trusted to maintain operational standards—to bypass technical defenses.
The reliance on Quick Assist highlights a significant blind spot in many perimeter-focused security architectures. Quick Assist is typically whitelisted because it is a legitimate IT tool. Organizations must re-evaluate policies governing remote access tools, ensuring that even authorized tools are monitored for anomalous command-line arguments or unexpected payload delivery mechanisms, such as the installation of disguised MSI files.
Expert Analysis of Evasion Techniques
From an expert perspective, the combination of DLL sideloading and the anti-analysis thread creation demonstrates a layered defense mechanism designed to defeat automated security analysis. DLL sideloading is an effective stealth technique because the initial loading binary—the legitimate Microsoft application—is inherently trusted by the operating system. By injecting malicious code through a trusted path, the attacker ensures the payload executes in a high-trust context.
The anti-analysis measure, while not cryptographically sophisticated, is pragmatically effective against less robust sandbox environments. Modern malware often includes checks for virtual machines or debuggers. By flooding the system with threads, the malware forces the analysis tool to expend significant resources managing context switching or, in less optimized environments, simply crash or time out before the core payload is fully unpacked and executed in a detectable state.
The C2 infrastructure represents a significant leap in stealth. Traditional C2 detection relies on monitoring unusual outbound traffic patterns—connections to known malicious IPs, non-standard ports, or traffic anomalies in HTTP/S streams. DNS is often used for C2 (DNS tunneling), but security operations centers (SOCs) are highly attuned to spotting common indicators, such as high volumes of TXT or CNAME queries. MX record queries are far less frequently monitored for data exfiltration. Furthermore, the structure of the request—embedding encoded data in the subdomain label—forces analysts to inspect not just the query type, but the content entropy of the query itself, demanding a deeper level of network packet inspection capability than many organizations currently deploy at scale.
Future Impact and Emerging Trends
The A0Backdoor campaign serves as a potent indicator of future threat actor trends. We are likely to see an increased emphasis on "living off the land" techniques, where adversaries maximize the use of legitimate, digitally signed system tools (like MSI installers and Quick Assist) to minimize the introduction of novel, easily detectable artifacts onto the victim machine.
The sophistication of the C2 communication suggests a move away from easily identifiable Command and Control infrastructure toward leveraging fundamental, non-suspicious network protocols. Expect future malware families to explore other obscure protocols or even leverage obscure features within legitimate cloud storage platforms for command delivery, further blurring the line between authorized and malicious network activity.
For security vendors and enterprise defenders, this necessitates a fundamental shift in focus from perimeter defense to endpoint behavior monitoring and process lineage analysis. It is no longer sufficient to check if an application is digitally signed; security tools must validate the context and intent of the actions taken by that signed application, particularly when legitimate tools are invoked via unusual sequences or parameters, as seen with the Quick Assist initiation. The industry must adapt to assume that communication channels, even those secured and integrated like Microsoft Teams, are perpetually contested battlegrounds. Resilience will increasingly depend on robust employee training against advanced social engineering, coupled with security tooling capable of detecting complex, multi-stage execution chains hidden within trusted system processes.

