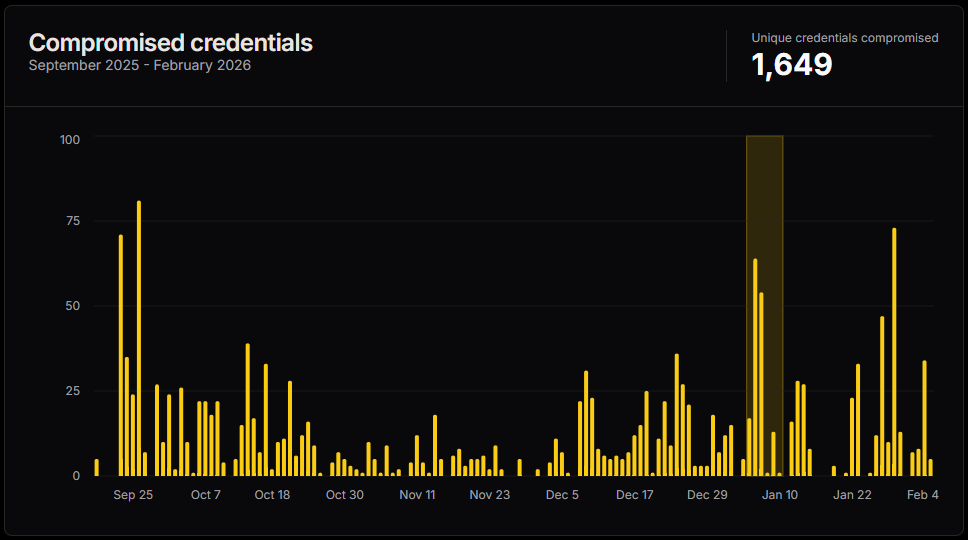
The global freight and logistics sector, the vital circulatory system of international commerce, is facing a persistent and highly organized cyber threat emanating from a financially motivated threat actor group identified as "Diesel Vortex." This operation, active since at least September 2025, has meticulously crafted an infrastructure utilizing 52 distinct domains to conduct widespread credential harvesting targeting operators across the United States and Europe. The scale of the compromise is significant, with forensic analysis revealing the theft of 1,649 unique credentials belonging to users of critical industry platforms.
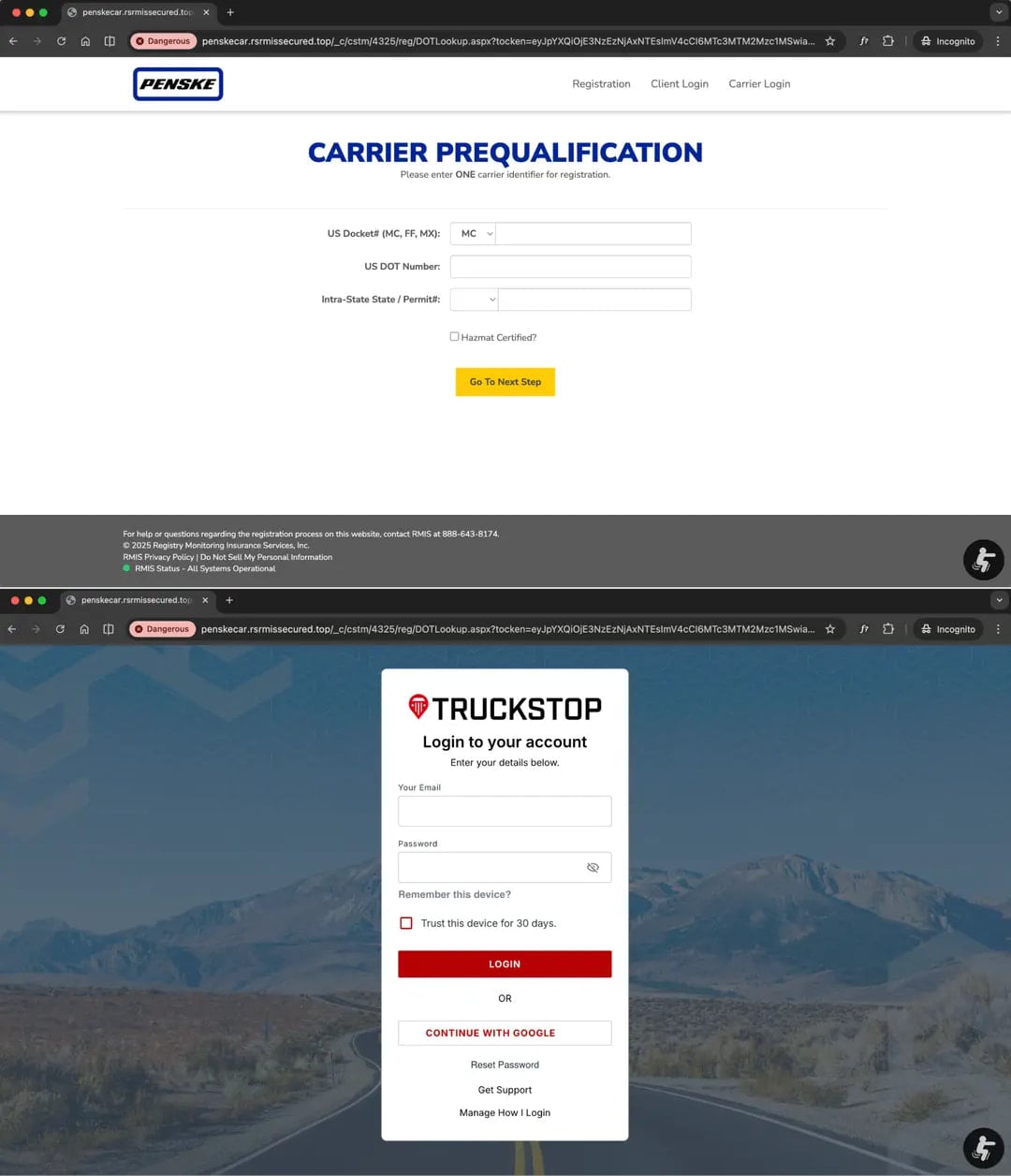
The list of compromised services underscores the depth of the attackers’ reconnaissance and targeting strategy. Entities such as DAT Truckstop, a key resource for load boards; TIMOCOM and Teleroute, significant European freight exchanges; major fleet operators like Penske Logistics and Girteka; and essential financial platforms such as Electronic Funds Source (EFS) have all been drawn into the phishing net. These targets represent the digital backbone of supply chain operations, suggesting the threat group is not merely interested in opportunistic data theft but in gaining deep, persistent access to transactional and operational data.
The uncovering of this campaign stemmed from an unexpected digital artifact: an exposed repository containing an SQL database associated with a phishing kit. This kit, developed by the threat actors, was marketed to other criminal enterprises under the moniker "MC Profit Always," while internally being referenced as "Global Profit." Researchers monitoring domain squatting, specifically the team at Have I Been Squatted, discovered this repository, which provided an unprecedented window into the operation’s mechanics. Further intelligence was gleaned from Telegram webhook logs embedded within the repository, exposing communications between the phishing service operators. Linguistic analysis of these communications strongly suggests that Diesel Vortex is an Armenian-speaking collective operating within the orbit of Russian cyber infrastructure, indicating potential transnational organizational ties.

The technical investigation was bolstered by collaborative efforts with Ctrl-Alt-Intel, a provider specializing in tokenization infrastructure. By leveraging open-source intelligence (OSINT), Ctrl-Alt-Intel was able to map connections between the identified infrastructure, the operators, and real-world companies within the targeted vertical. The resulting technical dossier revealed the full scope of credential exposure, amounting to nearly 3,500 captured credential pairs, with 1,649 confirmed as unique logins.
Organizational Structure and Operational Sophistication
What distinguishes Diesel Vortex from common opportunistic cybercriminals is the apparent high degree of organization. Evidence recovered, including a mind map allegedly created by a group member, details a structured hierarchy reminiscent of a legitimate business. This structure reportedly includes dedicated roles for a call center, technical support, programmers, and specialized staff tasked with identifying and cultivating relationships with drivers, carriers, and logistics contacts.
The acquisition channels detailed in the mind map highlight a multi-pronged approach to infiltration, extending beyond simple email blasts. These channels reportedly included exploiting the DAT One marketplace, direct email campaigns, and—most critically for the logistics sector—rate confirmation fraud. The mapping also detailed revenue splits across various tiers of the operation, pointing toward a professionalized criminal enterprise focused on maximizing financial yield from stolen access.
Researchers confirmed that the group’s strategy centered on building bespoke phishing environments specifically tailored to the platforms used moment-to-moment by freight brokers, trucking firms, and broader supply chain managers. "Load boards, fleet management portals, fuel card systems, and freight exchanges were all in scope," noted the Have I Been Squatted researchers. They astutely observed that these platforms exist in a security blind spot: "These platforms sit at the intersection of high transaction volumes and the targeted workforce isn’t typically the primary focus of enterprise security programs, and the operators clearly knew it." This acknowledgment of where security spending and focus are typically concentrated allowed Diesel Vortex to operate with a significant degree of impunity.

Evasion Techniques and Advanced Phishing Mechanics
The attack methodology employed by Diesel Vortex demonstrates a clear commitment to bypassing standard email security measures. The initial vector involved phishing emails dispatched via the kit’s integrated mailer, leveraging legitimate, but often abused, services like Zoho SMTP and Zeptomail to enhance deliverability. Crucially, the threat actors incorporated Cyrillic homoglyph tricks within both the sender addresses and the subject lines. This technique manipulates the visual representation of characters, allowing malicious emails to appear legitimate to the untrained eye and evade simple string-matching security filters.
Beyond email, the group utilized social engineering across multiple vectors, incorporating voice phishing (vishing) and actively infiltrating Telegram channels where trucking and logistics personnel congregate. This demonstrates an understanding of the informal, rapid-communication ecosystems prevalent in the industry.
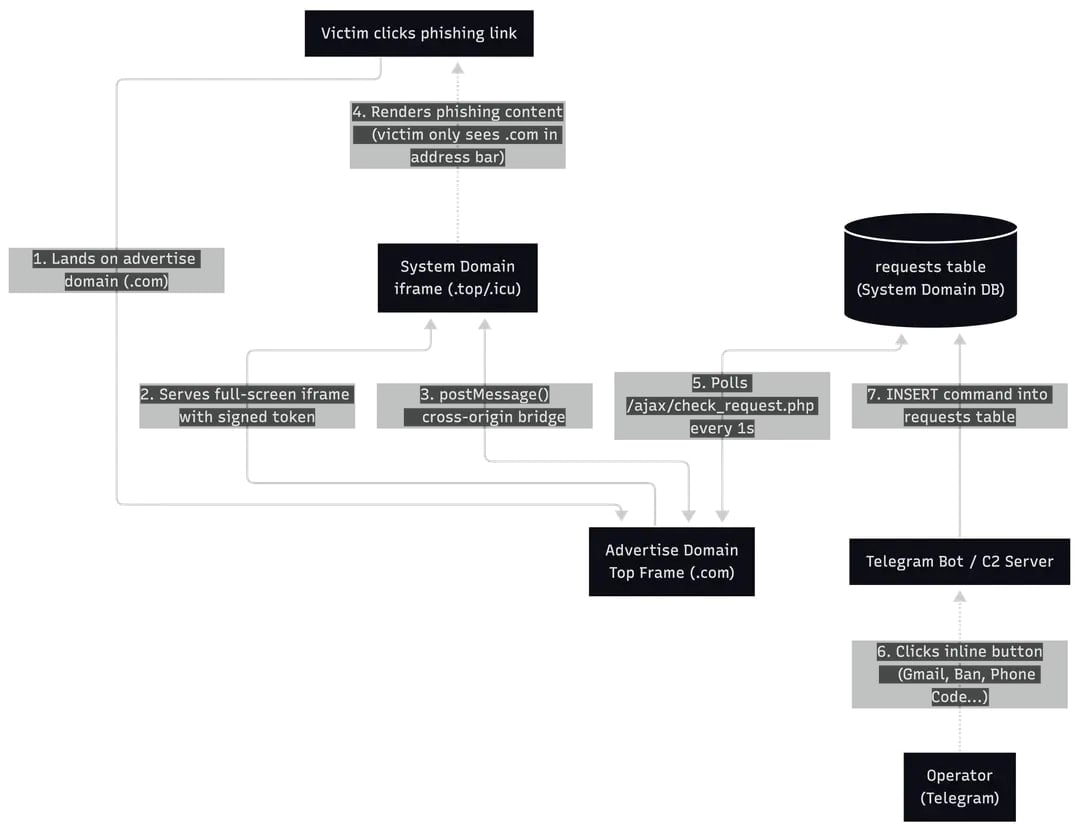
The technical execution upon clicking a link is equally elaborate. Victims are directed to a deceptive landing page hosted on a disposable ".com" domain. This initial page utilizes a full-screen iframe to load the actual malicious content—a pixel-perfect clone of the legitimate platform. This is followed by a complex, nine-stage cloaking process that utilizes less reputable system domains (such as those ending in .top or .icu) to obfuscate the true nature and persistence of the attack infrastructure.
The sophistication extends to the data harvesting process. Depending on the specific target platform being cloned, the phishing pages were configured to extract a comprehensive array of sensitive information: standard credentials, carrier permit data, essential regulatory identifiers like MC/DOT numbers, login details for RMIS (Risk Management Information Systems), user PINs, two-factor authentication (2FA) codes, security tokens, transaction details including payment amounts, payee names, and even specific check numbers.
The control mechanism governing this multi-stage theft is notable. The entire phishing workflow remains under the direct, real-time control of the operator via Telegram bots. This interface allows the threat actor to dynamically dictate the progression of the session. For example, after initial credential capture, the operator can decide whether to immediately prompt for 2FA codes, request passwords for ancillary services like Google or Microsoft Office 365, or simply redirect the victim to the legitimate site to avoid suspicion. In cases where the victim exhibits hesitation or abnormal behavior, the operator retains the ability to terminate or block the session mid-process, ensuring the extraction process is tightly managed.
Disruption and Real-World Criminal Impact
The coordinated nature of the discovery led to a significant, albeit partial, disruption of the Diesel Vortex infrastructure. A collaborative effort involving domain registrars and security providers—specifically GitLab, Cloudflare, Google Threat Intelligence, CrowdStrike, and the Microsoft Threat Intelligence Center—resulted in the takedown of key components, including panel domains, phishing domains, and associated GitLab repositories.
However, the concurrent OSINT investigation by Ctrl-Alt-Intel provided crucial context regarding the group’s ultimate objectives, which extended beyond mere credential accumulation. By tracing communications from the Telegram chats—which were often conducted in Armenian—and cross-referencing an email address found in the phishing panel’s source code, researchers uncovered links to individuals and corporate entities registered in Russia involved in wholesale trade, transportation, and warehousing. Alarmingly, the researchers noted that the same email address used to provision the criminal infrastructure appeared in Russian corporate filings for logistics companies operating directly within the targeted sector.
This evidence strongly suggests that Diesel Vortex was employing stolen credentials not just for direct financial gain but as a means to facilitate more complex, high-value criminal activities. The evidence pointed toward coordinated operations involving freight impersonation, mailbox compromise, and, most damagingly, double-brokering or cargo diversion.
Double-brokering is a particularly insidious form of logistics fraud. It involves using the compromised identities of legitimate, trusted carriers to secure high-value shipping contracts. Once the load is booked, the perpetrators then covertly reassign or divert the freight cargo to illicit pickup points controlled by the criminal network. This process effectively allows the theft of the physical goods, often bypassing the traditional security layers designed to protect the freight itself, because the initial booking appears legitimate.
Industry Implications and Future Security Outlook
The Diesel Vortex operation serves as a stark warning regarding the evolving threat landscape confronting the supply chain industry. Historically, enterprise security budgets have prioritized protecting core IT assets, financial systems, and customer data. The logistics sector, characterized by distributed operations, reliance on third-party brokers, and a workforce often utilizing disparate, less centrally managed platforms (like load boards and fleet apps), presents a tempting, low-resistance target for financially motivated actors.
The success of Diesel Vortex highlights several critical industry vulnerabilities:
- Platform Over-Reliance: The industry relies heavily on a small number of centralized digital platforms for daily operations. Compromising these gateways effectively grants access to the ecosystem.
- Human Factor Exploitation: The combination of sophisticated phishing, vishing, and infiltration of informal social platforms like Telegram demonstrates an advanced understanding of where the human element of logistics communication resides.
- Lack of Unified Security Posture: The targeted workforce (drivers, small fleet managers, dispatchers) often lacks the robust security training and endpoint protection afforded to corporate IT staff, making them susceptible to credential harvesting tactics that bypass standard email gateways.
For the freight and logistics industry moving forward, the focus must shift toward a "zero-trust" approach applied specifically to operational technology (OT) and logistics software access. This necessitates:
- Mandatory Hardware-Backed MFA: Moving beyond simple SMS-based 2FA to phishing-resistant methods (e.g., FIDO2 security keys) for all critical logistics platforms, including load boards and fuel card systems.
- Enhanced Domain Monitoring: Implementing rigorous, continuous monitoring for typosquatted domains that specifically mimic industry-standard service providers, extending protection beyond the traditional corporate perimeter.
- Contextual Access Control: Implementing controls that flag or block access requests originating from unusual geographic locations or employing high-risk credentials, especially when accessing sensitive data like MC/DOT numbers or payment authorizations.
The coordinated takedown demonstrates that collaboration between threat intelligence firms and platform providers can neutralize active campaigns. However, given that the infrastructure was marketed as a reusable phishing kit ("MC Profit Always"), the underlying tooling will almost certainly be adopted by other actors. The financial incentive derived from cargo theft and fraudulent transactions ensures that cyber threats against the physical movement of goods will only intensify, requiring the logistics sector to urgently mature its digital defenses to match the sophistication of groups like Diesel Vortex. The full indicators of compromise, including network artifacts, Telegram identifiers, and associated financial trails, provide immediate tactical data points for industry defenders seeking to harden their perimeters against this specific, highly organized threat methodology.

