The cybersecurity landscape is currently grappling with the emergence of SSHStalker, a novel Linux-based botnet whose operational backbone is a surprising throwback: Internet Relay Chat (IRC). This development signals a calculated pivot by threat actors away from the complexity and increasing scrutiny of modern Command and Control (C2) frameworks toward the time-tested simplicity and inherent resilience of a protocol dating back to 1988. While IRC’s heyday in mainstream consumer communication has long passed, its foundational characteristics—minimal bandwidth requirements, straightforward implementation, and inherent support for decentralized, channel-based communication—make it an unexpectedly robust choice for persistent, low-cost botnet management.
The rediscovery of IRC as a viable C2 mechanism, highlighted by threat intelligence analysis from Flare, underscores a cyclical pattern in cyber threat evolution: when advanced defense mechanisms make modern infrastructure too costly or noisy, adversaries often revert to robust, legacy systems that security tooling might overlook or deprioritize. SSHStalker is not attempting to be stealthy in its initial phases; rather, it prioritizes scale and operational reliability, creating a noisy, brute-force infrastructure built upon decades-old technology.
The Architecture of Archaism: SSHStalker’s Design Philosophy
SSHStalker’s operational model is explicitly anti-modern. Instead of leveraging sophisticated domain-fronting, encrypted tunnels, or domain generation algorithms (DGAs) common in contemporary botnets, it relies on classic IRC mechanics. This includes deploying multiple C-based bots that communicate across redundant server and channel configurations. This design choice offers inherent fault tolerance; taking down one C2 node or channel does little to disrupt the overall command structure, as the network inherently supports multiple pathways for instruction dissemination.
Flare researchers characterized the framework succinctly: "a loud, stitched-together botnet kit that mixes old-school IRC control, compiling binaries on hosts, mass SSH compromise, and cron-based persistence." This assessment points to a "scale-first" methodology. The goal appears to be rapid, widespread infection and resource acquisition, accepting that the initial compromise methods are conspicuous.

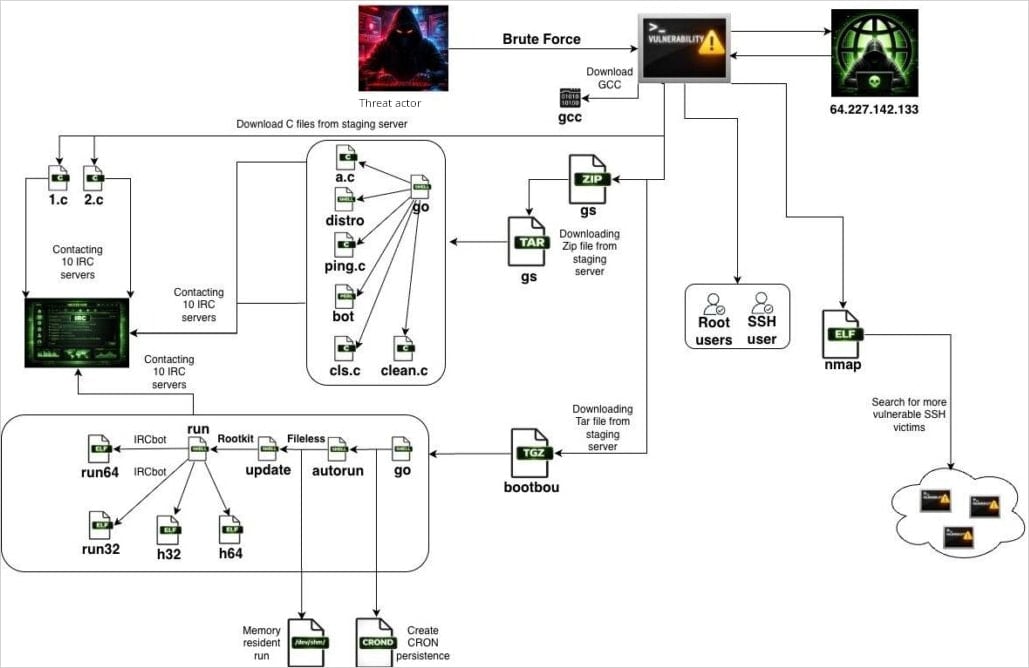
The initial vector for SSHStalker infection is aggressive and unsophisticated: automated scanning and brute-forcing of exposed Secure Shell (SSH) ports. The malware utilizes a compiled Go binary that deliberately mimics the legitimate and widely used network discovery utility, nmap. This deception aids initial execution and reconnaissance. Once a host is compromised, the infected system immediately turns outward, initiating its own SSH scans against other potential targets, effectively creating a worm-like propagation mechanism that accelerates the botnet’s expansion organically across vulnerable infrastructure.
Infrastructure Targets and Initial Foothold Analysis
The targeting profile identified by Flare is illuminating. Analysis of reconnaissance data revealed nearly 7,000 bot scans conducted in January alone, showing a pronounced focus on cloud hosting environments, particularly within Oracle Cloud infrastructure. This suggests the operators are targeting scalable, internet-facing server fleets rather than endpoints or traditional enterprise networks.
Gaining initial access through low-privilege SSH credentials is only the first step. A critical phase in the SSHStalker attack chain involves establishing persistence and elevating privileges. Upon successful compromise, the botnet dynamically downloads the GCC (GNU Compiler Collection) toolchain onto the victim device. This decision is strategically significant: compiling payloads directly on the compromised host improves portability across different Linux distributions and architectures, and it allows the malware to evade static signature detection based on pre-compiled binaries.
The initial C-based IRC bots, hard-coded with their designated C2 servers and channels, serve to officially enroll the new victim into the botnet’s communication infrastructure. Following this enrollment, the malware fetches secondary archives, labeled enigmatically as GS and bootbou. These archives house variant bot modules responsible for orchestration and the sequencing of subsequent malicious activities.
Persistence is achieved through a highly frequent, watchdog-style mechanism: cron jobs configured to execute every 60 seconds. This interval is exceptionally short, ensuring that if the primary bot process is terminated by security software or a system administrator, the cron job rapidly relaunches it, maintaining a constant presence.

Leveraging the Past for Privilege Escalation
Perhaps the most architecturally dated, yet potentially dangerous, component of SSHStalker is its reliance on kernel exploits dating back over a decade. The botnet payload incorporates exploits targeting 16 distinct Common Vulnerabilities and Exposures (CVEs) primarily affecting Linux kernel versions from the 2009–2010 era. This suggests the operators are banking on system administrators failing to patch or fully update older, often legacy, server instances that still run outdated kernel releases.
In the attack chain, this exploit package is deployed after the initial low-privilege SSH access is secured. This staged approach ensures that the privilege escalation occurs only after the bot has established its communication link and persistence mechanism, maximizing the chance of retaining control even if the initial brute-force entry point is discovered.
Monetization and Operational State
The ultimate objectives driving SSHStalker appear to be multifaceted, typical of large-scale botnets seeking diverse revenue streams. Flare observed evidence of AWS key harvesting—a lucrative tactic for accessing cloud resources or selling access—alongside routine website scanning activities. Crucially, the malware bundles cryptomining kits, specifically noting the inclusion of PhoenixMiner, a high-performance tool optimized for mining Ethereum and other GPU-intensive cryptocurrencies.
The botnet also possesses latent Distributed Denial of Service (DDoS) capabilities. However, researchers have not yet observed these functions being utilized. This current state—where bots check in to the IRC C2 and then enter an idle loop—strongly suggests that SSHStalker is either in an active testing and expansion phase, or the operators are "hoarding access" to deploy volumetric attacks or large-scale cryptomining operations when market conditions or infrastructure demands are optimal.
Industry Implications: The False Sense of Security
The adoption of IRC by SSHStalker carries significant implications for modern network defense strategies. Many contemporary security stacks are configured to aggressively monitor and alert on traffic patterns associated with newer C2 protocols—such as HTTPS callbacks, DNS tunneling, or specialized proprietary encrypted channels. IRC, by contrast, often falls outside the scope of high-priority alerting, particularly on internal or segmented networks, as it is frequently viewed as a legacy application or development tool.
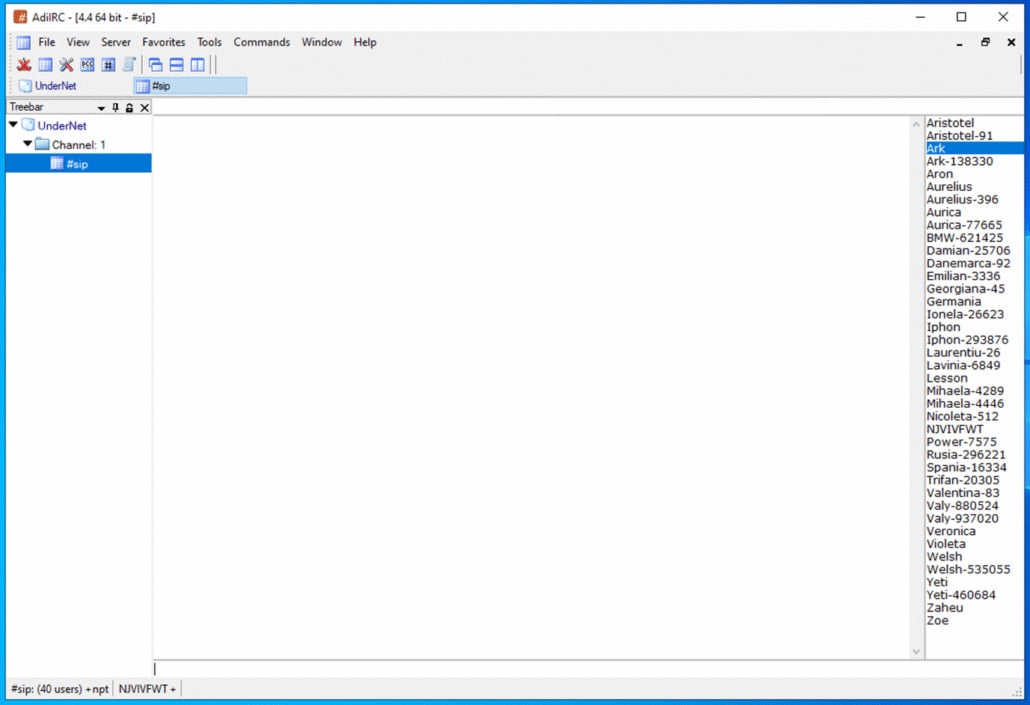
This reliance on IRC exploits an over-reliance on signature-based detection against cutting-edge threats. Security teams may be overlooking the subtle, plain-text chatter of IRC traffic, which, in this context, functions as a direct instruction pipeline. The simplicity of IRC communication means that network traffic analysis tools might log the connection without flagging the activity as inherently malicious, provided the target IRC ports (like 6667) are not explicitly blocked by default firewall policies.
Furthermore, the use of on-host compilation via downloaded GCC tools highlights the danger of allowing development toolchains onto production servers. In a hardened cloud environment, the presence of a full compiler suite should be an immediate anomaly worthy of investigation, yet many containerized or virtualized environments may inadvertently include these tools, treating them as necessary dependencies rather than potential malware enablers.
Expert Analysis and The Echoes of Past Threats
While Flare has not definitively linked SSHStalker to a specific Advanced Persistent Threat (APT) group, the technical indicators point toward established infrastructure. The researchers noted thematic similarities with the Outlaw/Maxlas botnet ecosystem, a known entity operating in the cryptomining and DDoS space for years, often associated with Romanian threat activity. This suggests SSHStalker may be a successor, a new iteration, or a direct fork of existing, resilient malware infrastructure adapted for current cloud targets.
The selection of decade-old kernel exploits is a fascinating strategic choice. While bleeding-edge exploits attract immediate patching efforts, older, unpatched flaws in legacy systems or specialized environments (like older Kubernetes nodes or specific IoT gateways) provide a stable, long-term attack surface. Threat actors recognize that the cost and complexity of patching deeply embedded or hard-to-reach infrastructure often lead to permanent vulnerability windows.
Future Impact and Defensive Posture
The SSHStalker campaign serves as a stark reminder that cyber resilience is not solely about defending against the newest zero-day; it also requires robust defense against persistent, low-tech, high-scale threats. The future impact of this botnet will depend on the operators’ ability to transition from the testing/hoarding phase to active monetization. If large-scale cryptomining or DDoS operations commence, organizations relying on Oracle Cloud or similar providers could face significant resource drain or service disruption.
From a defensive standpoint, the recommendations provided by Flare are foundational but essential in this context:
- Disable SSH Password Authentication: Mandating public-key cryptography for SSH access immediately nullifies the botnet’s primary initial access mechanism (brute-forcing).
- Compiler Removal: Strict security policies must ensure that development toolchains (like GCC) are entirely absent from production operating system images and containers. If compilation is necessary, it should occur in isolated, ephemeral build environments.
- Egress Filtering: Enforcing strict egress filtering is paramount. By defining precisely which external IP addresses and ports are permitted outbound traffic, organizations can immediately block unauthorized connections to hard-coded IRC C2 servers.
- Runtime Monitoring: Continuous monitoring for unusually short cron job cycles (e.g., 60-second loops) originating from non-standard system paths is a critical behavioral indicator.
- Network Anomaly Detection: Security Operations Centers (SOCs) must update network monitoring solutions to flag and deeply inspect plain-text outbound connections utilizing common IRC ports, even if the traffic profile doesn’t match modern encrypted standards.
SSHStalker’s choice to use IRC is a calculated strategic maneuver—a blend of old tactics achieving new objectives against modern infrastructure. It forces defenders to look beyond the cutting edge and reinforce the fundamentals of system hardening and network segmentation against threats that value endurance over elegance.

