The gradual erosion of digital autonomy has spurred a significant, growing movement among technology users: the deliberate divestment from the Google ecosystem, often termed "de-Googling." This shift is not merely a matter of preference but a calculated response to evolving business models centered on data monetization. Google’s expansive suite of applications, while offering unparalleled convenience and integration, operates on a foundation where user data is the core commodity. Features like Smart Compose in Gmail or advanced photo categorization in Google Photos rely on sophisticated AI models that inherently require deep access and continuous scanning of user content. For a growing segment of the population, this centralized surveillance model, irrespective of its utility, presents an unacceptable risk to personal privacy and intellectual freedom.
This imperative for data sovereignty has fueled the rise of specialized, privacy-first technology providers. These smaller, often open-source-focused entities prioritize security through robust encryption and decentralized data handling, positioning themselves as direct philosophical and functional antagonists to the advertising-driven behemoths of Big Tech. For individuals seeking a foundational step away from this pervasive tracking infrastructure, transitioning core services represents the most impactful initial measure. This analysis focuses on five critical application categories where viable, privacy-enhanced alternatives not only exist but often surpass their commercial counterparts in terms of user control and data protection guarantees.
The Browser Battlefield: Moving Beyond Chrome’s Tracking Infrastructure
Google Chrome dominates the web browsing market, a dominance cemented by its seamless integration with the Android operating system and its vast library of extensions. However, this convenience is intrinsically linked to Google’s tracking mechanisms. Chrome’s architecture facilitates extensive data collection on browsing habits, site interactions, and user behavior, all channeled back to the company for profiling and targeted advertising initiatives. While users can tinker with settings, the core framework remains geared toward data aggregation.
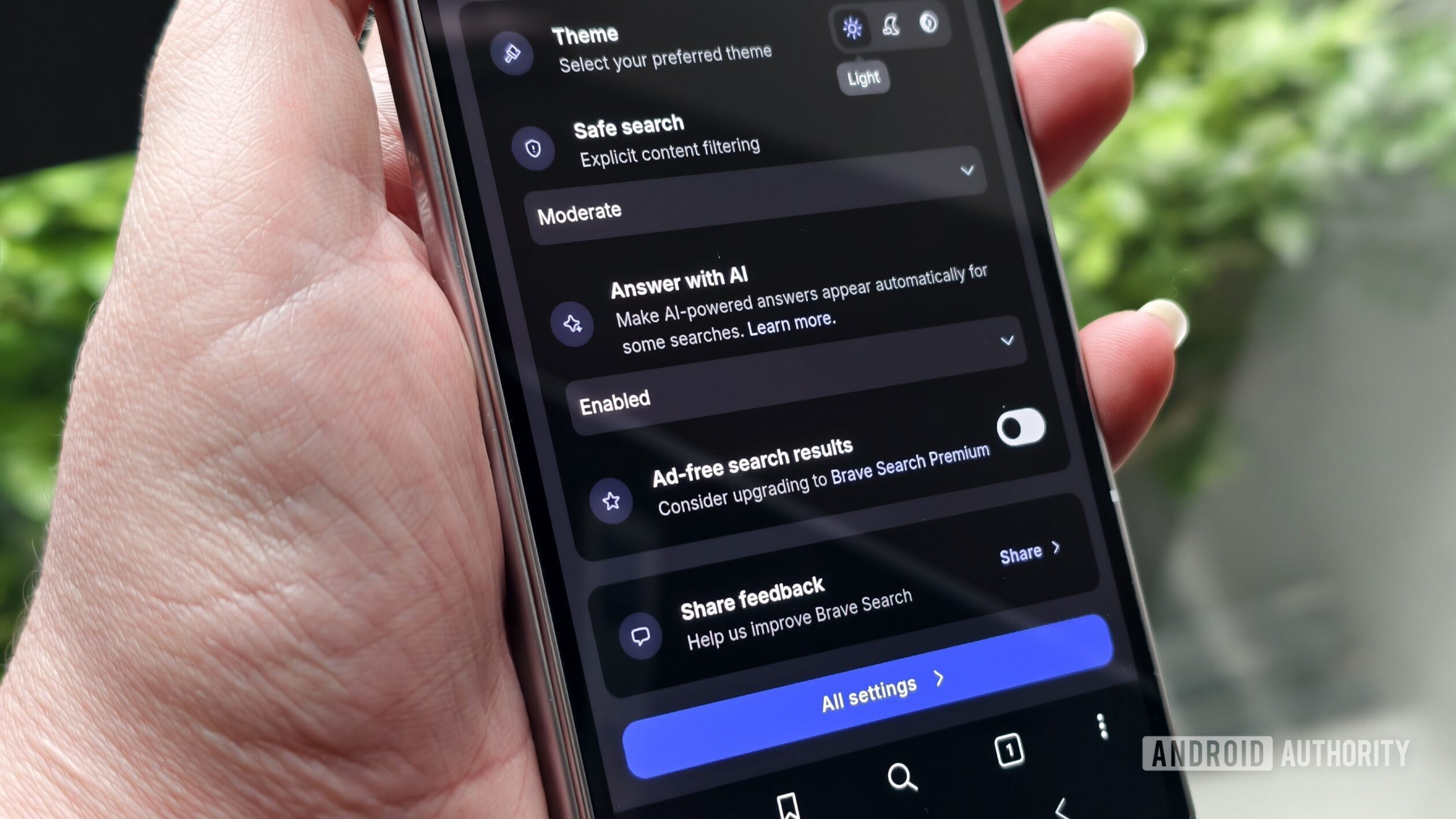
The most compelling counterpoint in this space is Brave. Crucially, Brave is also built upon the Chromium engine, eliminating the friction often associated with migrating from Chrome. Users retain compatibility with existing extensions and bookmark structures, smoothing the transition significantly. The fundamental divergence lies in Brave’s default posture: it is engineered for privacy. It aggressively blocks third-party trackers, fingerprinting attempts, and pervasive advertising networks by default, delivering a cleaner, faster browsing experience that is not predicated on user surveillance.
Expert Analysis: The industry implication of Brave’s success is significant. It proves that a user base exists willing to trade certain high-level integrations for uncompromising privacy controls. Brave’s integrated ad-blocking feature is not just a convenience; it’s a direct economic disruption to the ad-tech industry that underpins Google’s profitability. Furthermore, the inclusion of a built-in, privacy-centric VPN service and the Leo AI chatbot signals a trend where privacy tools are becoming consolidated within the browser itself, reducing the need for multiple third-party security subscriptions. The blocking of ubiquitous cookie consent pop-ups further streamlines usability while reinforcing privacy boundaries—a subtle but powerful user experience win.
Securing Digital Correspondence: From Gmail’s Open Ecosystem to Encrypted Mail
Gmail remains the world’s dominant email service, yet its reliance on algorithmic content scanning—even for benign features like Smart Compose or sophisticated spam filtering—is a major concern for those prioritizing confidentiality. Email, by its nature, contains sensitive personal and professional data, and entrusting it to a platform whose primary business is data utilization is a fundamental conflict of interest.
The established, gold-standard replacement for privacy-conscious communication is Proton Mail. Originating from CERN scientists, Proton Mail is fundamentally built around end-to-end encryption (E2EE). This means that emails are encrypted on the sender’s device and can only be decrypted by the recipient’s device, rendering the contents completely opaque to Proton staff, network administrators, or any external interception.
Industry Implications and Future Trends: Proton Mail’s commitment to zero-access encryption sets a high watermark for email security. Unlike Google, where a legal mandate or data breach could expose user data, Proton’s architecture makes such exposure technically impossible for their servers. This E2EE standard is increasingly becoming a regulatory focus, particularly in Europe, and providers like Proton are positioned to benefit from stricter data protection legislation globally. Furthermore, the expansion of the Proton ecosystem (Mail, VPN, Drive, Calendar) demonstrates a viable business model where users willingly pay for security guarantees, contrasting sharply with the ad-supported model. The introduction of features like disposable email aliases further empowers users to shield their primary digital identity from marketing lists and data brokers.
Archiving Memories: Replacing Cloud Vision with Local Encryption
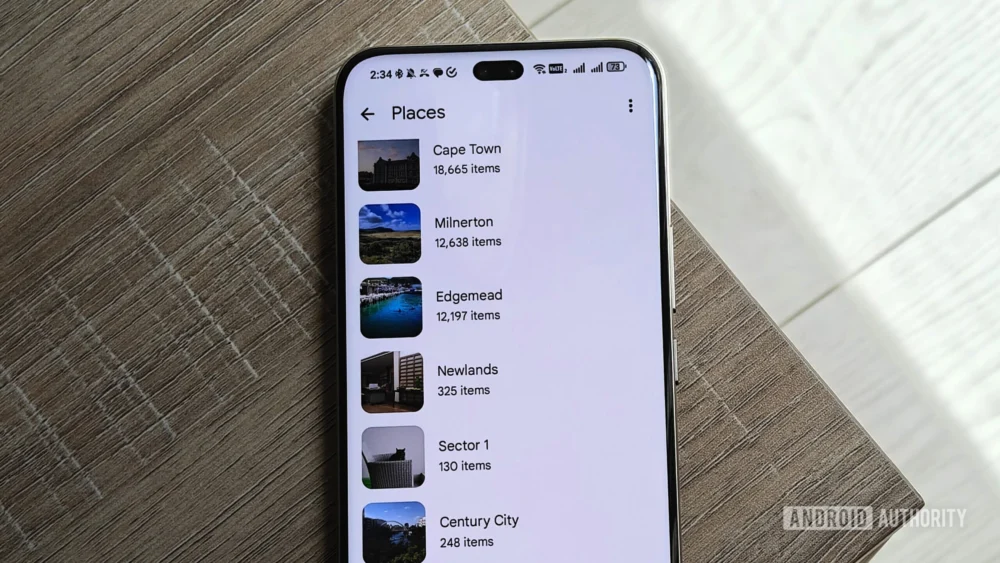
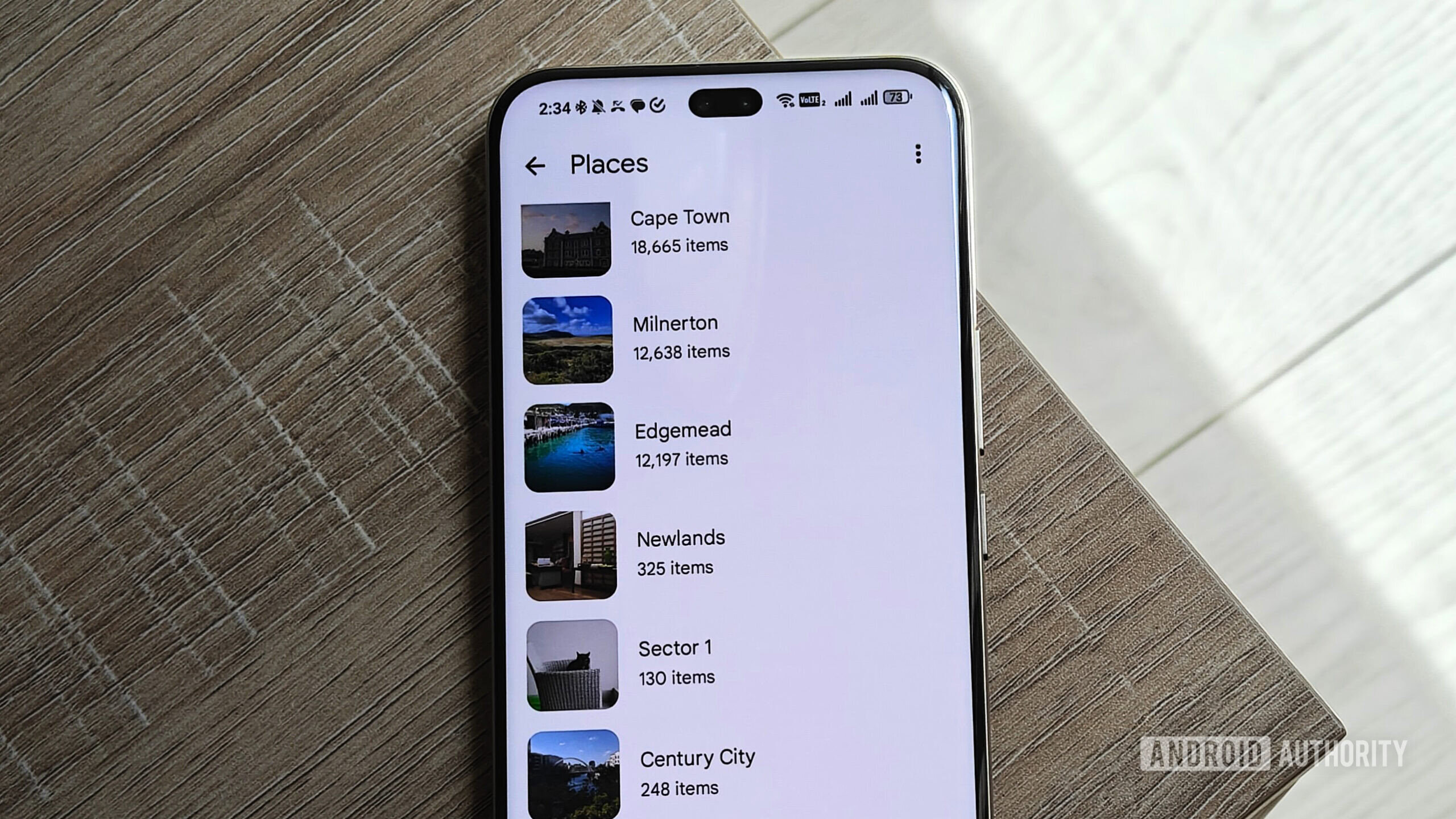
Google Photos offers unparalleled ease of use in photo backup and organization, leveraging powerful cloud AI for facial recognition, object tagging, and automated "memories." However, the trade-off is the surrender of complete control over one’s visual history. The scanning required for these AI features means that intimate moments are processed by Google’s algorithms, creating rich metadata profiles linked to location, time, and even the content of the images themselves.
For users seeking an offline-first or self-hosted solution without sacrificing modern organization, Ente emerges as a strong contender. Ente champions end-to-end encryption for photo libraries and is also open-source, allowing for community auditing of its security claims. The critical difference is how it handles artificial intelligence. While Ente employs AI capabilities—such as facial grouping—these processes are executed locally on the user’s device, ensuring that biometric data and image content never leave the user’s control unencrypted.
Expert Analysis: The Ente model addresses the philosophical objection to cloud-based photo analysis directly. While Google Photos offers a "Locked Folder," this is a rudimentary silo within an insecure environment. Ente’s architecture suggests a future where on-device processing becomes the norm for sensitive data operations, mitigating the risks associated with mass data centralization. The 10GB free tier provides a compelling starting point, but as with most specialized services, scaling requires a subscription, reflecting the operational costs of maintaining secure, private infrastructure rather than harvesting advertising revenue.

Securing Digital Keys: Moving Beyond Single Point of Failure Password Management
Relying on Google’s built-in Password Manager binds the security of one’s entire digital life to the status of a single Google account. The risk profile here is twofold: dependency on a centralized entity for recovery, and the fact that the security of the manager is only as strong as the security surrounding the main Google account credentials. A compromise of the primary account grants access to every saved credential.
The definitive open-source, zero-knowledge alternative is Bitwarden. Zero-knowledge encryption ensures that the vault is encrypted locally before transmission to the cloud, meaning Bitwarden servers only hold encrypted blobs of data; they cannot decrypt the contents. This architecture is vital for true digital resilience.
Future Impact and Trends: Bitwarden’s open-source nature fosters trust through transparency. Its free tier is remarkably generous, supporting unlimited devices and offering the essential security features required by modern digital hygiene. Premium tiers, which add features like integrated two-factor authentication (2FA) code generation, target users who seek a fully integrated security suite. The industry trend is moving toward decoupling essential security services from primary ecosystem providers. Password managers like Bitwarden are becoming the new digital bedrock, offering portability and cryptographic guarantees that centralized solutions cannot match, especially in scenarios involving account lockouts or geopolitical access restrictions.
Cloud Storage Sovereignty: Transitioning from Drive to Proton Drive
Google Drive, alongside Google Docs and Sheets, forms the backbone of many users’ productivity workflows. The recent implementation of Gemini features that automatically summarize documents stored in Drive highlights the inherent tension: convenience derived from deep data inspection versus user expectation of privacy for stored files. If an AI can summarize a document, it has necessarily read, parsed, and indexed its contents.

Proton Drive, the cloud storage sibling to Proton Mail, offers a direct, encrypted migration path. It mirrors the robust security philosophy of the email service, applying zero-access, end-to-end encryption to all files stored in the cloud. This means that documents, spreadsheets, and backups remain cryptographically inaccessible to Proton itself.
Expert Analysis and Industry Perspective: The move from Drive to Proton Drive signifies a shift in how users perceive "cloud service." For Google, the cloud is a processing utility; for Proton, it is a secure vault. Proton Drive’s ability to generate encrypted, password-protected, and time-limited sharing links addresses the necessity of collaboration without sacrificing security. While the 5GB free tier may require scaling for heavy users, the cost reflects the operational expense of secure hosting, not the exploitation of user data for profile building. This service is particularly important for professionals dealing with sensitive intellectual property or individuals concerned about government data access requests, as the encryption layer provides a significant legal and technical barrier. Furthermore, Proton Drive is positioned to absorb users migrating away from Google Photos, offering a unified, encrypted storage solution for both documents and media, provided users accept the trade-off in AI-driven automation features.
Conclusion: Architecting a Digital Fortress
The five applications discussed—Brave, Proton Mail, Ente, Bitwarden, and Proton Drive—represent foundational replacements across the most frequently used categories of digital life. The transition away from Google is not about rejecting technology; it is about choosing technology whose underlying business model aligns with user interests rather than corporate data aggregation goals.
This movement is forcing a broader industry reckoning. As more users migrate, competitors are compelled to enhance their own privacy features or face irrelevance in high-value demographics. The future of digital services appears to be bifurcating: one path dominated by hyper-integrated, data-rich convenience, and the other defined by decentralized, cryptographically secured sovereignty. For those initiating this journey, these alternatives provide the necessary infrastructure to build a digital fortress, one service at a time. Should there be further interest in migrating from Google Keep, Calendar, or other specialized utilities, the underlying principles of open-source validation, E2EE, and zero-knowledge architecture will continue to guide the selection of the most robust replacements.