The ongoing lifecycle management of Windows 10, a platform that remains deeply embedded across enterprise and consumer infrastructures globally, has necessitated a recent, crucial corrective action from Microsoft. The software giant has deployed the KB5075039 update, specifically targeting a significant and frustrating regression within the Windows Recovery Environment (WinRE) for Windows 10 users running the 21H2 and 22H2 feature releases. This update is not merely a routine patch; it resolves an issue that fundamentally undermined the ability of system administrators and end-users to perform essential, last-resort system diagnostics and repairs.
The Windows Recovery Environment (WinRE) is far more than a simple boot menu; it is a dedicated, minimal operating environment provisioned on the system partition. Its architecture allows it to load independent of the main Windows installation, providing the necessary tools—such as System Restore, Startup Repair, Command Prompt access, and malware removal utilities—to troubleshoot scenarios where the primary operating system fails to boot correctly. In essence, WinRE is the digital equivalent of an emergency tow truck for a failed operating system installation. When this environment becomes inaccessible, the ability to self-diagnose and recover from catastrophic failures is severely curtailed, transforming manageable incidents into potential total system reinstalls.
The genesis of this specific problem traces back to the late 2025 Patch Tuesday cycle. While the immediate public focus often centers on high-profile usability issues, backend system stability can be silently compromised. In October 2025, updates deployed across Microsoft’s product line inadvertently introduced instability into recovery partitions. Notably, separate but contemporaneous issues were identified in the Windows 11 Recovery Environment where KB5066835 caused a complete failure of USB peripheral input (mice and keyboards), rendering the troubleshooting interface effectively unusable—a critical usability failure that Microsoft addressed relatively quickly.
However, the Windows 10 situation, stemming from the KB5068164 update, proved more insidious. While not immediately manifesting as a peripheral input failure, this update introduced a systemic error preventing the WinRE partition from initializing successfully altogether. Microsoft officially acknowledged this flaw in February, noting in the revised changelogs for the problematic October update that it contained a defect "that prevents the Windows Recovery Environment from starting successfully." For users experiencing boot failures following that October installation, the standard recovery path was blocked, leaving them stranded unless they possessed external recovery media or advanced knowledge of manual partition manipulation.
The deployment of KB5075039 directly addresses this specific failure point. The accompanying release notes are concise yet definitive: "[Windows Recovery Environment (WinRE)] Fixed: WinRE would not start after installing the October 14, 2025 update KB5068164." This confirms that the new patch successfully reverts or overwrites the corrupted elements introduced months prior, restoring the integrity of the critical recovery partition.

Industry Implications: The Perils of Partition Management and Update Sequencing
This incident highlights several critical considerations for IT operations, particularly concerning how operating system updates interact with the complex, often static, structure of disk partitions. The WinRE partition, typically small and residing adjacent to the main OS partition, is sensitive to changes in size and structure.
The requirement for the WinRE partition to be at least 256MB for the KB5075039 update to install successfully underscores a growing trend in OS maintenance: the necessity of sufficient overhead space in specialized system partitions. When the problematic KB5068164 was installed, it appears to have either corrupted the partition structure or required more space than was available, leading to the initialization failure upon invocation. This forces administrators into a multi-step recovery process: first, identifying the WinRE failure; second, consulting Microsoft’s guidance (such as the instructions provided in KB5028997) to manually resize the partition, a procedure inherently risky for inexperienced users; and finally, applying the corrective KB5075039 update.
From an enterprise perspective, this sequence introduces significant operational friction. If a major incident occurs—such as a failed feature update or a severe ransomware attack necessitating a clean rollback—the standard operating procedure is compromised. Security incident response teams rely on trusted, offline environments like WinRE to extract forensic data or perform secure eradication steps. A broken WinRE forces reliance on external bootable media, which may not contain the latest security patches or drivers relevant to the specific hardware environment, potentially slowing down response times and increasing the window of vulnerability.
Furthermore, the delay between the initial October 2025 update and the February disclosure, followed by the late deployment of the fix, raises questions about Microsoft’s internal regression testing procedures specifically targeting recovery pathways. While mainstream OS functionality tests are robust, niche environmental components like WinRE can sometimes slip through the cracks, especially when updates are cumulative or sequential, as they were in this case. For long-term servicing channel (LTSC) or highly controlled enterprise environments, this lag translates directly into prolonged exposure to a known recovery failure state.
Expert Analysis: The Stability Tax of Legacy Support
The fact that this issue pertains to Windows 10 21H2 and 22H2—versions nearing or past their mainstream support lifecycle—is highly relevant. Microsoft continues to support these releases primarily for enterprise and specialized industrial systems where frequent OS upgrades are impractical or impossible due to hardware certification requirements or regulatory compliance. Supporting these older builds requires backporting fixes from newer Windows versions, a process that carries an inherent risk of introducing unintended side effects, as demonstrated here.
The challenge lies in balancing the stability required by enterprise users with the rapid pace of security development. When a fix for a recovery component is introduced, it must be validated across all supported legacy builds. The initial failure suggests that the update mechanism deployed to fix the issue in Windows 11 (or a similar fix tested on a different baseline) was not perfectly translated or applied to the Windows 10 codebase, leading to the specific WinRE startup failure documented under KB5068164.
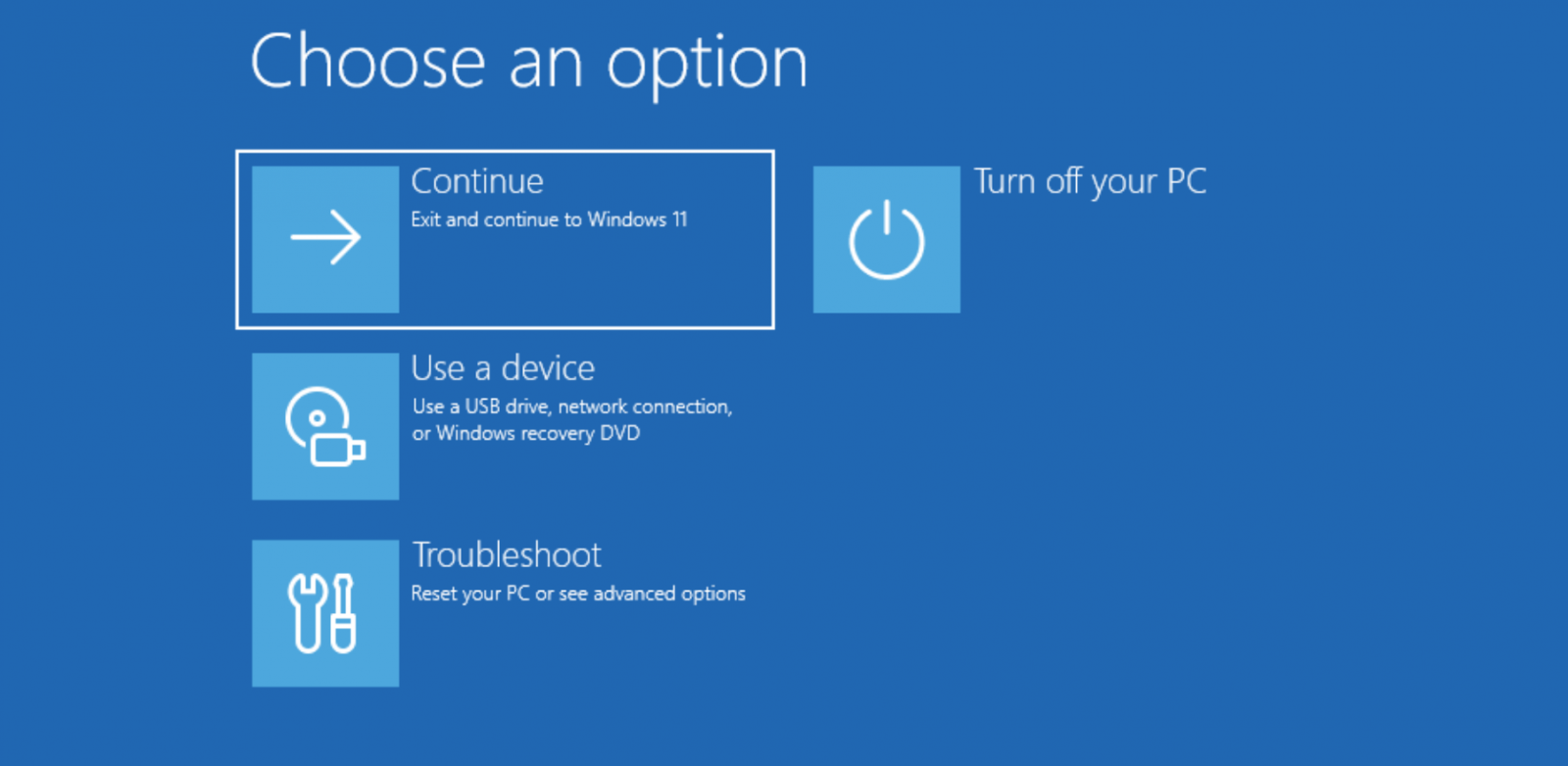
Security experts often advise against relying solely on the built-in WinRE partition for critical repairs in highly sensitive environments, preferring verified, immutable external media. However, for the vast majority of organizations and home users, the convenience of the local WinRE is paramount. The KB5075039 release serves as a necessary, if late, reminder that maintaining the integrity of the recovery infrastructure is just as vital as securing the running OS kernel.
Future Impact and Trends: Towards Resilient Recovery Architectures
This incident sets a precedent for future servicing strategies, pushing Microsoft toward more resilient and potentially more modular recovery mechanisms. One emerging trend involves containerizing or isolating the recovery environment even further, perhaps leveraging technologies similar to Windows Sandbox but dedicated solely to pre-boot diagnostics. This isolation could prevent a faulty mainline update from corrupting the recovery components by ensuring they reside on entirely separate, read-only volumes or utilize independent update mechanisms.
Another significant trend is the increased emphasis on proactive partition health checks during the update process. Future cumulative updates might incorporate a mandatory pre-installation check specifically verifying the integrity and minimum size requirements of the WinRE partition, automatically flagging potential installation failures before the main update sequence begins. This proactive validation, coupled with clearer error codes specific to partition exhaustion or corruption, would empower users to address prerequisites before an update is attempted.
For system administrators, the lesson is clear: regularly audit the health and size of the WinRE partition, especially following major cumulative updates. While Microsoft’s documentation offers guidance on resizing, any manual intervention involving partition manipulation carries inherent data loss risk. Therefore, the inclusion of a strong warning—advising data backup prior to any partition resizing—is a necessary, if regrettable, prerequisite for installing this essential fix. KB5075039 resolves a significant functional gap, but the process required to apply it underscores the complexity inherent in maintaining a stable, multi-layered operating system environment like Windows 10 in its twilight years of extended support. The focus now shifts to ensuring that the recovery mechanisms remain robust until the final sunset of support for these legacy builds.