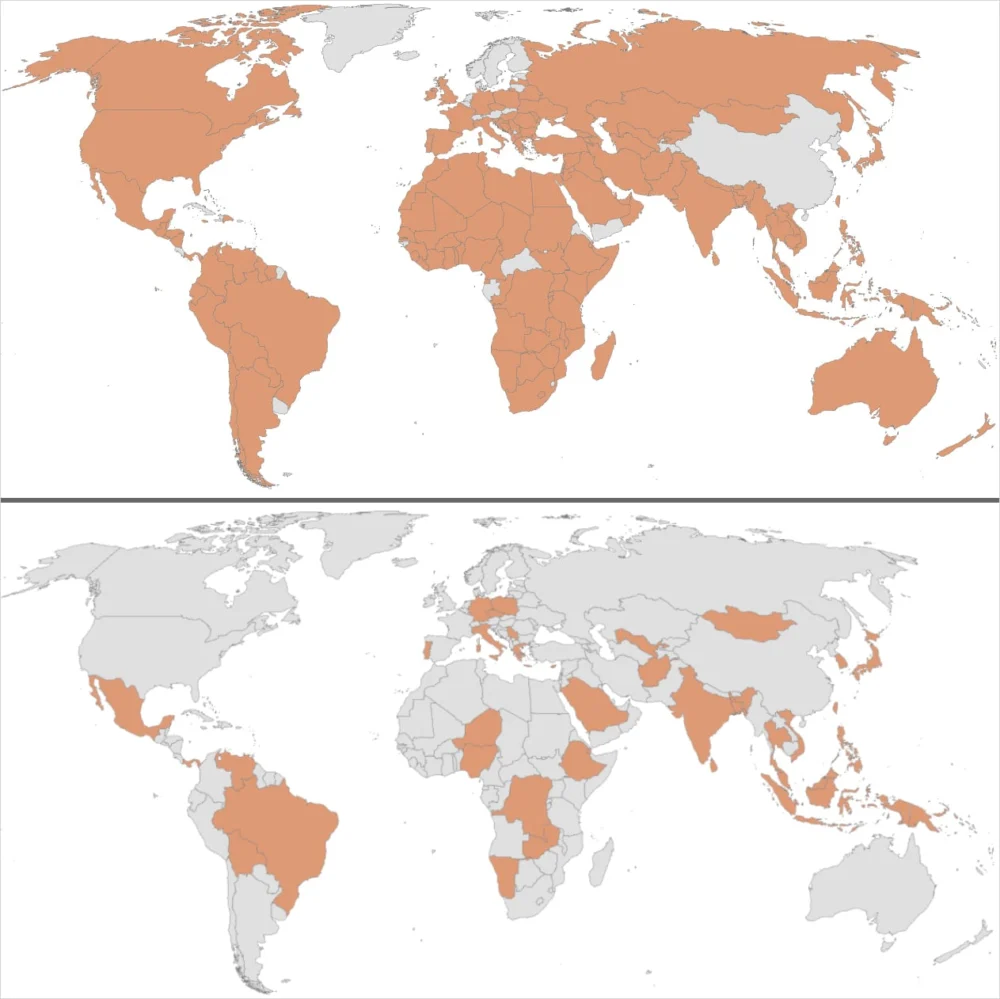
The cybersecurity landscape has been shaken by the disclosure of a highly sophisticated, state-sponsored espionage campaign, codenamed ‘Shadow Campaigns,’ which has successfully breached numerous government and critical infrastructure networks across 37 countries. Research conducted by Palo Alto Networks’ Unit 42 division indicates that this persistent threat actor, tracked provisionally as TGR-STA-1030/UNC6619, has been active since at least January 2024, demonstrating an operational footprint so expansive it touched entities connected to 155 nations through extensive reconnaissance activities observed between November and December of the preceding year. While definitive attribution remains pending, the high confidence assessment points toward an origin based in Asia, suggesting a nation-state prioritizing long-term intelligence gathering over immediate disruptive action.
The scope and targeting profile of Shadow Campaigns reveal a clear focus on strategic objectives. The threat actor’s primary interest lies in penetrating organizations deeply involved in governance, national security, and economic stability. This includes, but is not limited to, government ministries, law enforcement agencies, border control operations, financial institutions, trade regulators, energy sector assets, mining conglomerates, immigration departments, and diplomatic corps. Unit 42 confirmed tangible success, verifying the compromise of at least 70 high-value government and critical infrastructure organizations across 37 sovereign territories. The compromised targets span the geopolitical spectrum, encompassing entities involved in shaping trade policy and electoral processes in the Americas, legislative bodies and ministries across multiple European states, the Australian Treasury Department, and key governmental and infrastructure nodes within Taiwan.
The geographical distribution and temporal alignment of the reconnaissance activities offer crucial insights into the actor’s strategic calculus. Researchers noted a distinct escalation in scanning activity targeting infrastructure across North, Central, and South America during the U.S. government shutdown in October 2025. This period saw heightened probing of entities in Brazil, Canada, the Dominican Republic, Guatemala, Honduras, Jamaica, Mexico, Panama, and Trinidad and Tobago. A particularly telling instance involved intensive reconnaissance against "at least 200 IP addresses hosting Government of Honduras infrastructure" approximately 30 days prior to that nation’s general election. This surveillance coincided with a period where both leading candidates had publicly signaled intentions to potentially re-establish diplomatic relations with Taiwan, underscoring the operation’s likely focus on gathering intelligence relevant to shifting regional alliances and diplomatic leverage.
Beyond these confirmed breaches, evidence suggests attempted intrusions against entities such as the Australian Treasury Department, Afghanistan’s Ministry of Finance, and Nepal’s Office of the Prime Minister and Council of Ministers, often involving SSH connection attempts to critical infrastructure. The breadth of the observed probing is extensive. For instance, the threat group actively scanned infrastructure linked to the Czech government, targeting its Army, Police, Parliament, and Ministries of Interior, Finance, and Foreign Affairs, in addition to the presidential website. Furthermore, the campaign demonstrated an ambitious focus on European integration, initiating connections against over 600 IP addresses hosting domains under the *.europa.eu umbrella. Germany was a specific focus in July 2025, where the actor connected to more than 490 IP addresses hosting governmental systems, highlighting a sustained effort to map the digital landscape of major European economies.

The Shadow Campaigns Attack Lifecycle: Evasion and Sophistication
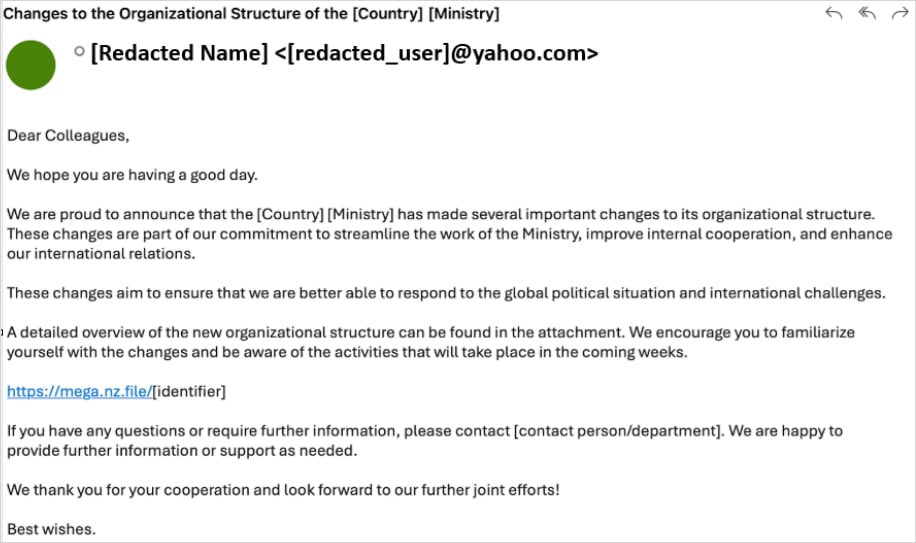
The initial access methods employed in Shadow Campaigns are hallmarks of mature, well-resourced espionage operations. Early vectors relied heavily on meticulously crafted spear-phishing emails directed at high-level government officials. The lures were highly context-aware, frequently referencing sensitive internal administrative topics such as ministry reorganization efforts to maximize the perceived legitimacy of the communication.
These emails contained embedded hyperlinks directing victims to malicious archives hosted on the Mega.nz file-sharing service. This use of a legitimate, widely trusted cloud storage platform serves to bypass initial network security scrutiny. Upon extraction, the archive delivered a custom malware loader dubbed ‘Diaoyu,’ accompanied by a peculiar artifact: a zero-byte Portable Network Graphics (PNG) file named pic1.png.
The Diaoyu loader is engineered with significant anti-analysis capabilities. Researchers discovered that the payload execution is conditional, contingent upon meeting specific environmental criteria before deploying secondary stages, such as Cobalt Strike payloads or the VShell command-and-control (C2) framework. A primary evasion mechanism involves a hardware check: the malware requires a screen resolution greater than or equal to 1440 pixels horizontally. Crucially, it performs a file-based integrity check. The zero-byte pic1.png file, seemingly innocuous, acts as a digital tripwire. If this file is absent from the execution directory, the malware immediately terminates execution, preventing dynamic analysis environments or automated sandboxes from observing its true function.
Further hardening the loader against discovery, Diaoyu actively scans the victim’s process list for running instances of major commercial antivirus and endpoint detection and response (EDR) solutions, including Kaspersky, Avira, Bitdefender, SentinelOne, and Norton (Symantec). The presence of any of these indicates a likely security-aware environment, prompting termination or dormancy.
While targeted social engineering remains a key delivery mechanism, TGR-STA-1030/UNC6619 has demonstrated proficiency in leveraging known software vulnerabilities for initial foothold acquisition. The threat group exploited at least 15 distinct, previously disclosed vulnerabilities, targeting widely used enterprise software such as SAP Solution Manager, Microsoft Exchange Server, D-Link networking hardware, and various Microsoft Windows operating system components. This dual approach—exploiting human trust via phishing and exploiting technical debt via known CVEs—is characteristic of nation-state actors seeking multiple assured avenues of initial entry.

The Kernel-Level Concealment: Introducing ShadowGuard
The toolkit utilized throughout the Shadow Campaigns is extensive, incorporating industry-standard and bespoke espionage tools. This arsenal includes established webshells like Behinder, Godzilla, and Neo-reGeorg, facilitating persistent remote access and file manipulation. For establishing resilient C2 channels, the actor deploys sophisticated network tunneling tools, including GO Simple Tunnel (GOST), Fast Reverse Proxy Server (FRPS), and IOX, enabling traffic to traverse secured networks using seemingly legitimate protocols.
However, the most alarming technical discovery associated with this operation is the deployment of a custom-developed Linux kernel eBPF rootkit named "ShadowGuard." The use of eBPF (extended Berkeley Packet Filter) technology in offensive operations represents a significant escalation in stealth capabilities. eBPF programs are inherently trusted by the Linux kernel, allowing them to attach to various kernel subsystems to inspect, filter, or modify system calls dynamically, all while operating entirely within the kernel space.
As Unit 42 researchers emphasize, eBPF backdoors are exceptionally challenging to detect because they operate below the visibility layer of most standard security monitoring tools. This elevated privilege allows ShadowGuard to manipulate core system functions and audit logs before security applications or system monitoring agents can capture the true operational data.
ShadowGuard provides comprehensive stealth capabilities. It can conceal malicious process information directly at the kernel level. Specifically, it uses syscall interception to hide up to 32 Process IDs (PIDs) from conventional Linux monitoring utilities such as ps or top. Furthermore, it possesses the ability to make files and directories bearing the specific name swsecret entirely invisible to manual inspection commands like ls. The rootkit also incorporates a configurable whitelist mechanism, allowing the operator to define specific processes that should remain visible to system administrators, thereby reducing the anomaly profile created by hiding too many elements. This level of kernel-level evasion is rarely seen outside of the most advanced, well-funded state-sponsored groups, confirming the high operational maturity of TGR-STA-1030/UNC6619.
Infrastructure and Geopolitical Signaling
The infrastructure supporting Shadow Campaigns is deliberately layered to obscure the actor’s origin and intent. The command and control architecture relies on a mix of victim-facing servers hosted with legitimate Virtual Private Server (VPS) providers in jurisdictions known for robust privacy protections, including the U.S., Singapore, and the UK. These frontline servers act as jump points, with traffic subsequently relayed through a complex chain involving additional relay servers designed for obfuscation, and often terminating via residential proxies or the Tor network to further mask the final destination.

A notable tactic involves the strategic selection of C2 domain names designed to blend into the target environment. For French-speaking nations, the actor utilized domains incorporating the .gouv top-level domain extension, a move designed to trick local security personnel into trusting the destination. In the European theater, the domain dog3rj[.]tech was observed. Researchers speculate this could be a subtle reference to "DOGE Jr.," potentially alluding to the U.S. Department of Government Efficiency (DOGO) or even the cryptocurrency Dogecoin, suggesting a level of operational chatter or cultural signaling within the group.
Industry Implications and Expert Analysis
The ‘Shadow Campaigns’ disclosure is far more than a catalog of compromises; it represents a significant indicator of evolving geopolitical cyber strategy. The targeting pattern—heavy on economic levers (finance, trade, energy) and political infrastructure (elections, diplomacy)—suggests that the primary objective is strategic intelligence accumulation aimed at influencing or anticipating major policy shifts globally.
The immediate implication for the cybersecurity industry is the urgent need to re-evaluate Linux security postures, particularly for organizations running high-value workloads on commodity hardware or virtualized environments where eBPF is increasingly leveraged for performance and observability. Traditional endpoint security, which relies on monitoring user-space activity, is fundamentally insufficient against a kernel-level rootkit like ShadowGuard. Defenders must invest heavily in kernel integrity monitoring (KIM) solutions and advanced behavioral analysis tools capable of detecting anomalous syscall interception patterns, rather than merely relying on signature matching for known malware binaries.
From an intelligence perspective, the actor’s calculated targeting around specific geopolitical events, such as the Honduran election and the U.S. government shutdown, suggests sophisticated planning that integrates kinetic or diplomatic timelines with cyber operations. This demands that national security agencies adopt a more integrated threat intelligence framework, correlating cyber activity with real-world political calendars.
The reliance on Mega.nz for initial malware delivery also signals a trend where threat actors exploit the integration points between legitimate cloud services and enterprise networks. Security teams must enforce strict egress filtering and scrutinize traffic patterns to and from known file-sharing platforms, treating any unexpected download of compressed executables from these sources with extreme suspicion, irrespective of the sender’s perceived identity.
Future Trajectory and Defense Recommendations
TGR-STA-1030/UNC6619, characterized by Unit 42 as an "operationally mature espionage actor," signals a future where state-sponsored attacks prioritize deep persistence and undetectable data exfiltration over noisy disruptive actions. The integration of highly customized tooling like ShadowGuard alongside widely used C2 frameworks like Cobalt Strike demonstrates a sophisticated blend of proprietary advantage and off-the-shelf efficiency.
For organizations worldwide, especially those in government and critical infrastructure sectors, the defense strategy must evolve beyond perimeter defense. Future resilience hinges on three core pillars:
- Zero Trust Architecture (ZTA) Reinforcement: Given the actor’s ability to compromise internal systems via phishing and vulnerability exploitation, network segmentation and the principle of least privilege must be rigorously enforced, limiting lateral movement even after initial compromise.
- Advanced Kernel Monitoring: Implementing security solutions specifically designed to detect anomalies within the Linux kernel, moving defenses closer to the operating system’s core functions to counter eBPF threats.
- Contextualized Threat Hunting: Security teams must proactively hunt for the unique indicators described, particularly the environmental checks performed by Diaoyu (the 1440px resolution check and the zero-byte file dependency), and establish protocols for rapidly analyzing compromised infrastructure based on geopolitical sensitivities.
The ‘Shadow Campaigns’ operation serves as a stark reminder that global espionage is characterized by patience, technical prowess, and a willingness to invest significant resources in achieving long-term strategic intelligence advantages across a vast array of international targets. The ongoing tracking and remediation efforts, supported by the comprehensive indicators of compromise provided by Unit 42, are crucial steps in mitigating the lingering threat posed by this highly capable adversary.