The ongoing international crackdown on cybercrime has registered another significant victory with the apprehension of a 21-year-old individual in Dordrecht, Netherlands. This suspect is alleged to have played a critical role in the distribution network for JokerOTP, a highly automated phishing-as-a-service (PhaaS) platform notorious for its ability to hijack user accounts by circumventing multi-factor authentication (MFA) safeguards. This arrest marks the third major capture stemming from a meticulous, three-year-long investigation aimed at dismantling the entire JokerOTP ecosystem.
The initial blow against the operation landed in April 2025, when authorities successfully detained the principal developer behind the platform. This was followed by a subsequent arrest in August, targeting a co-developer operating under the monikers ‘spit’ and ‘defone123’. The latest arrest of the alleged sales operative underscores the organized, multi-layered nature of these criminal enterprises, extending beyond just the core coders to the necessary infrastructure for commercializing the malicious tools.
The Scope and Impact of JokerOTP
JokerOTP distinguished itself in the threat landscape not merely as a simple credential-harvesting tool, but as a fully automated social engineering engine built on phishing infrastructure. Over its two-year operational lifespan, the service is estimated to have inflicted staggering financial damage, reportedly causing losses exceeding $10 million across more than 28,000 distinct attack incidents. These operations spanned 13 different countries, highlighting the borderless reach of cloud-based criminal services.
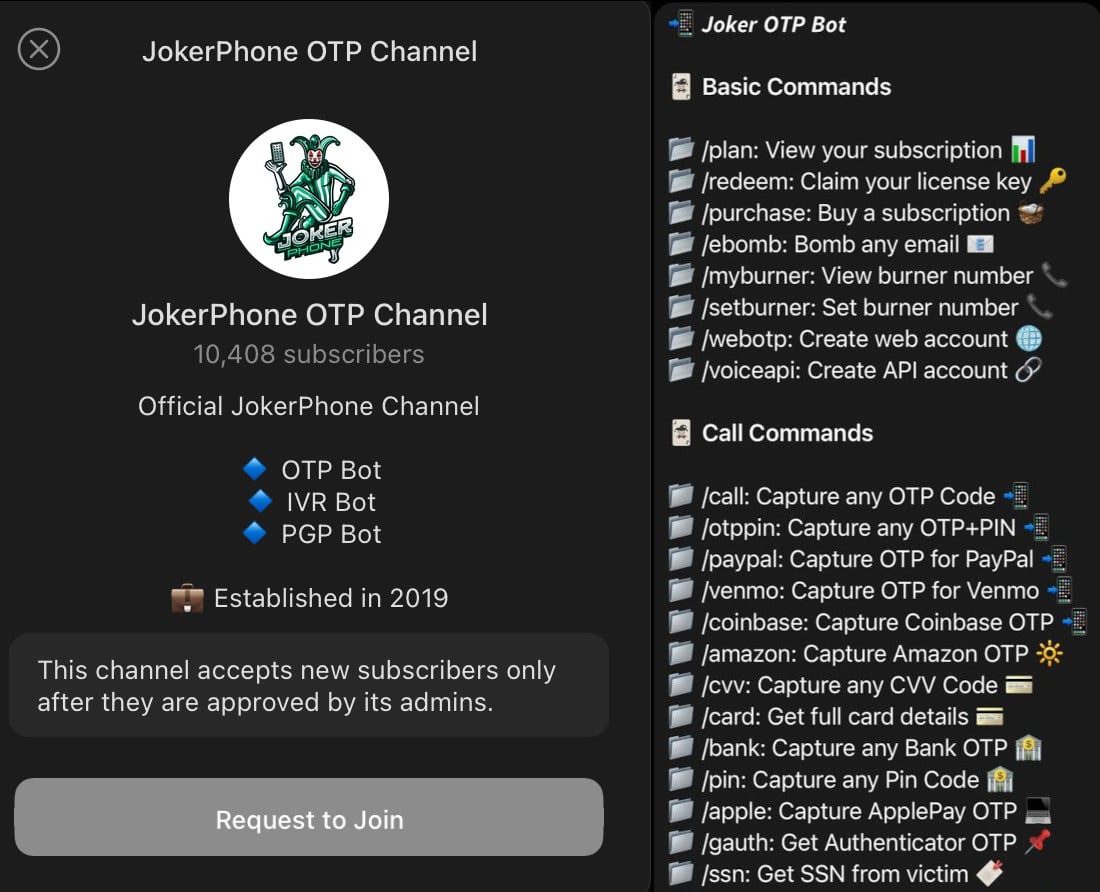
The current arrestee facilitated the service’s proliferation by marketing access licenses—essentially keys to operate the platform—via encrypted messaging channels, notably Telegram. This sales model, common in the PhaaS sector, allows individuals with moderate technical skill but significant criminal intent to leverage sophisticated malware infrastructure without needing to develop or maintain it themselves.
Subscribers to JokerOTP gained the capability to configure automated scripts designed to execute highly personalized, real-time attacks. The core functionality centered on exploiting the very mechanism designed to enhance security: the One-Time Password (OTP).

Expert Analysis: The Deceptive Brilliance of the Voice Phishing Vector
To fully appreciate the danger JokerOTP posed, one must understand the role of OTPs in modern security architecture. OTPs are time-sensitive verification codes—usually six to eight digits—sent via SMS, email, or generated by authenticator apps (like TOTP). They serve as the crucial second factor, ensuring that even if an attacker steals a username and password, they cannot access the account without possession of the unique, temporary code.
JokerOTP bypassed this safeguard through a clever, orchestrated sequence of events. The typical attack flow began when a cybercriminal, having already acquired compromised credentials (often sourced from data breaches or malware), initiated a login attempt against a target service. As the legitimate service sent the mandatory OTP to the user, the JokerOTP bot immediately initiated an automated voice call to the victim.
This is where the psychological manipulation peaked. The bot, impersonating a trusted entity—perhaps a bank representative, an e-commerce security agent, or a social media moderator—would inform the victim that unauthorized login attempts were underway. Crucially, this automated alert call would perfectly coincide with the arrival of the actual verification code.
As Anouk Bonekamp, team leader of Cybercrime Oost-Brabant, noted, the victim, operating under high pressure and believing they were actively thwarting an attack, would be prompted by the bot to recite the newly arrived OTP to "verify their identity" or "cancel the suspicious transaction." In a state of panic, victims willingly surrendered the very code intended to protect them. This technique, known broadly as "vishing" (voice phishing) integrated with real-time MFA interception, exploits human instinct over digital security protocols.
The services targeted by JokerOTP were diverse and financially significant, including major payment processors like PayPal and Venmo, cryptocurrency exchanges like Coinbase, and large retailers such as Amazon and Apple. Success in compromising these accounts allowed threat actors to execute unauthorized purchases, drain linked financial assets, or seize control of high-value digital identities.
Industry Implications and the Phishing-as-a-Service Economy

The dismantling of JokerOTP underscores a critical trend in the cyber threat landscape: the increasing industrialization of cybercrime. Phishing-as-a-Service (PhaaS) models lower the barrier to entry for aspiring criminals, transforming complex technical exploits into accessible, subscription-based products.
The operational scale of JokerOTP—impacting users across 13 nations and generating millions in losses—demonstrates that these specialized tools are not niche exploits; they are scalable business models. The arrest of the developer, co-developer, and now the sales agent shows law enforcement agencies are adopting a holistic approach, targeting the entire supply chain from conception to distribution and utilization.
For security professionals, the JokerOTP saga serves as a stark warning about the limitations of SMS-based and basic email-based MFA when confronted with advanced, automated social engineering. While MFA is vastly superior to simple password protection, its reliance on channels susceptible to real-time interception (like phone calls) presents a persistent vulnerability that sophisticated actors will continue to exploit.
The Road Ahead: Future Trends in Authentication Security
The persistence of tools like JokerOTP is driving an urgent industry pivot toward more resilient authentication methods. The primary implication for the tech and finance sectors is the accelerated depreciation of SMS and voice-based OTPs as primary or secondary verification factors.
1. Move to FIDO Standards and Passkeys: The industry consensus is rapidly shifting toward phishing-resistant MFA technologies. The FIDO Alliance standards, particularly the adoption of Passkeys, represent the most significant countermeasure. Passkeys utilize public-key cryptography, binding authentication to the user’s device (phone, laptop) rather than a transferable code. Since the private key never leaves the device, it is fundamentally immune to phishing attacks where the attacker attempts to trick the user into handing over a code.
2. Enhanced Voice Biometrics and AI Detection: On the defensive side against vishing, telecommunication providers and service platforms must deploy more sophisticated real-time voice analysis. While JokerOTP used basic automation, future iterations will likely incorporate more convincing AI-generated voice cloning. Robust anti-fraud systems must evolve to detect patterns indicative of automated calls masquerading as customer support.
3. Continued Law Enforcement Collaboration: The success of the multi-year, multinational investigation highlights the necessity of transnational police cooperation, especially when targeting services advertised on global platforms like Telegram. Future efficacy against PhaaS networks will depend on intelligence sharing between jurisdictions regarding payment flows, infrastructure hosting, and user identity mapping.
4. Prosecution of Users: The Dutch police have indicated that dozens of buyers of the JokerOTP bot in the Netherlands have already been identified and face forthcoming prosecution. This focus on the end-users—the individuals actively committing fraud using the purchased tool—is a crucial deterrent. It signals a shift from solely pursuing the developers to holding those who operationalize the malware accountable, disrupting the demand side of the criminal marketplace.
Advice for Consumers and Organizations
As this investigation confirms, the sophistication of these traps can make even diligent users fall prey. Law enforcement officials correctly emphasize that victims should not carry the burden of shame. The psychological pressure exerted by real-time, coordinated attacks is designed to bypass rational thought.
However, vigilance remains paramount. Users must be educated to recognize red flags: any unsolicited communication (call or text) that creates a sense of urgency, demands immediate action, or requests the recitation of a security code is almost certainly fraudulent. The core principle remains: legitimate services will never call or message you unsolicited to ask for an OTP you just received.
Furthermore, the police recommendation to utilize breach notification services like Have I Been Pwned and regional equivalents like CheckJack is vital. If an email address is confirmed in a data leak, it immediately elevates the risk profile for that user, making them a prime target for highly customized attacks that leverage known personal data alongside stolen passwords. Securing accounts with non-SMS MFA methods should be an immediate priority for anyone whose credentials have appeared in public breaches. The takedown of JokerOTP is a significant step, but the underlying vulnerability in consumer behavior and authentication standards continues to necessitate aggressive mitigation strategies across the digital ecosystem.

