The persistent threat posed by state-sponsored espionage actors continues to manifest through the aggressive exploitation of critical software vulnerabilities. Intelligence indicates that APT28, the highly sophisticated threat cluster widely attributed to Russia’s Main Intelligence Directorate (GRU), is actively weaponizing a severe security defect within the Zimbra Collaboration Suite (ZCS) specifically to penetrate and compromise Ukrainian governmental systems. This calculated campaign underscores a persistent, strategic focus by Moscow on degrading or gaining insight into Ukrainian state operations.
The vulnerability at the heart of this latest intrusion vector is cataloged under CVE-2025-66376. This high-severity flaw resides within the architecture of the Zimbra platform and was addressed via a patch released in early November. Technically, the issue stems from a stored Cross-Site Scripting (XSS) weakness. Crucially, this flaw permits unauthenticated attackers to potentially escalate privileges to achieve Remote Code Execution (RCE) on the targeted Zimbra server. Successful exploitation not only compromises the underlying server infrastructure but also grants direct access to the compromised user’s associated email accounts, presenting an ideal scenario for intelligence gathering and system disruption.
The gravity of this exploitation was formally recognized by U.S. federal authorities. On Wednesday, the Cybersecurity and Infrastructure Security Agency (CISA) moved swiftly to include CVE-2025-66376 in its Catalog of Known Exploited Vulnerabilities (KEVs). The addition of any zero-day or actively exploited vulnerability to the KEV list triggers mandatory compliance requirements for all Federal Civilian Executive Branch (FCEB) agencies. Under the authority of Binding Operational Directive (BOD) 22-01, issued in November 2021, these agencies are now required to remediate the vulnerability across all affected assets within a strict two-week deadline, reflecting the immediate and tangible risk posed by the exploit.
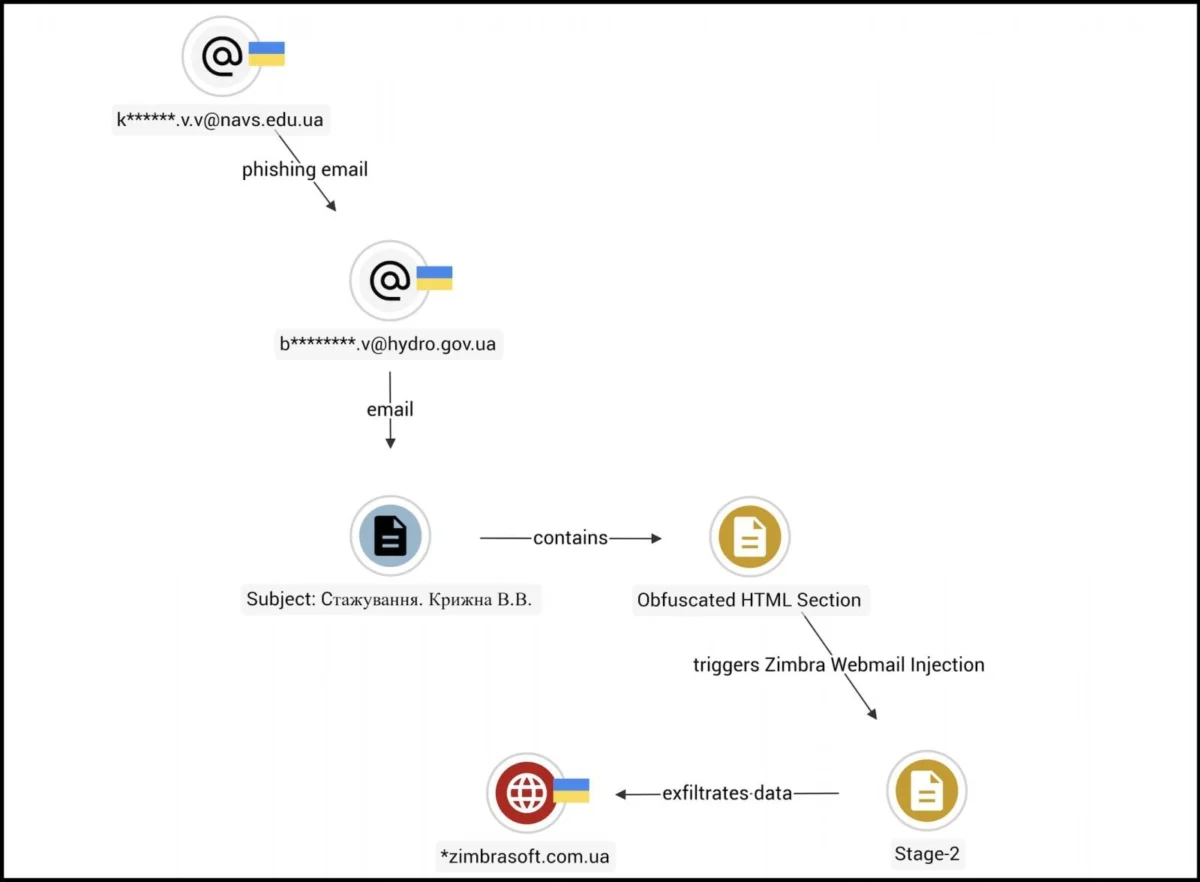
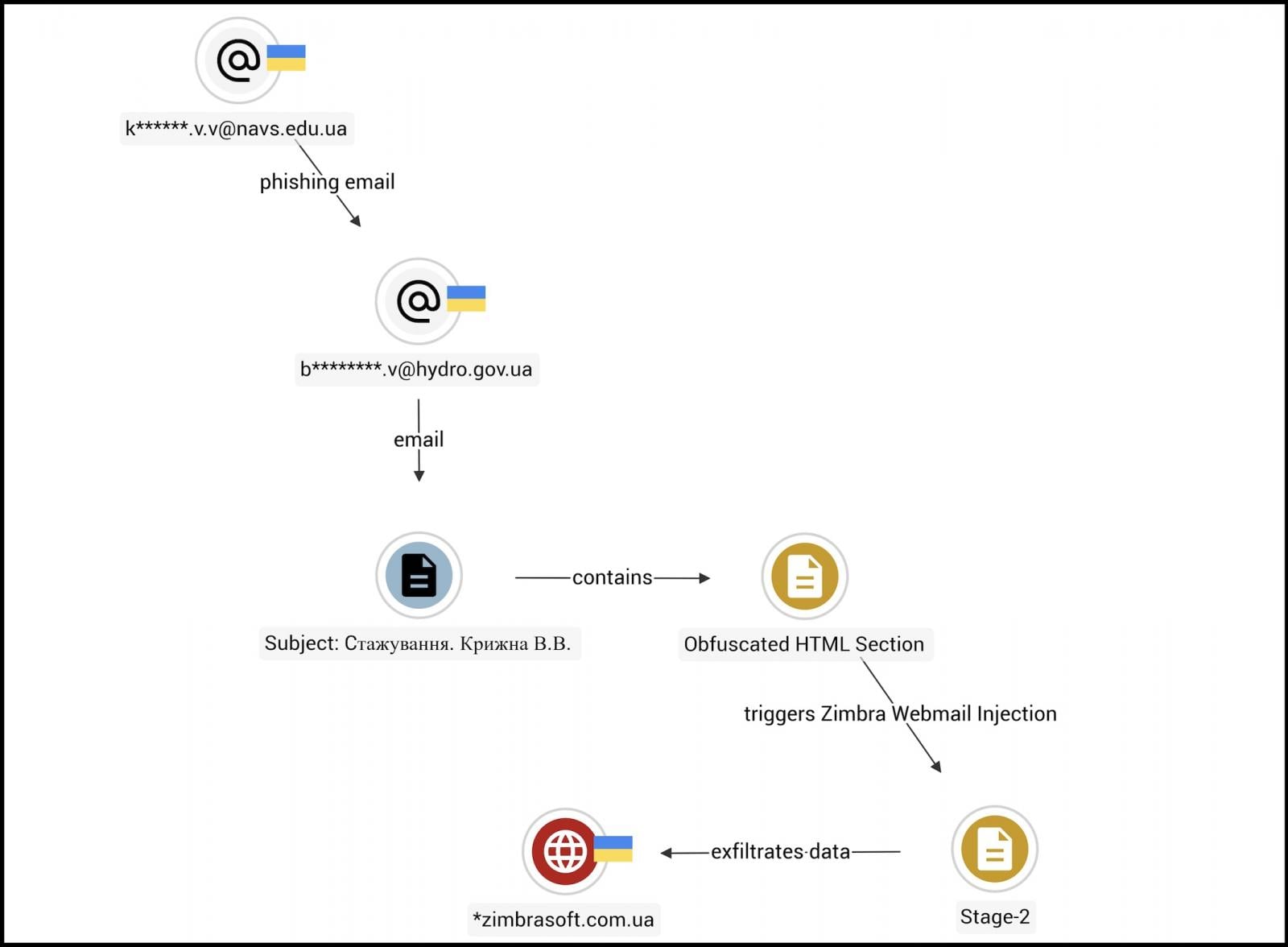
While CISA provided limited public commentary regarding the specifics of the ongoing exploitation against U.S. assets, independent security analysis had already detailed the campaign’s execution in the Ukrainian theatre. Researchers at Seqrite Labs, in a report published just a day prior to the CISA advisory, explicitly linked APT28’s activities to the weaponization of this Zimbra XSS flaw against Ukrainian targets. The campaign, which Seqrite Labs has dubbed "Operation GhostMail," demonstrates a focused effort targeting sensitive governmental nodes.
One confirmed victim in this espionage operation is the Ukrainian State Hydrology Agency. This entity holds significant strategic importance, falling under the purview of the Ministry of Infrastructure and responsible for crucial navigational, maritime, and hydrographic support—data vital for both civilian logistics and military defense posture in the Black Sea region.
The methodology employed in Operation GhostMail is noteworthy for its deceptive simplicity and reliance on complex payload delivery within the email structure itself. According to the Seqrite analysis, these malicious communications deliberately eschew conventional indicators of compromise. "The phishing email has no malicious attachments, no suspicious links, no macros," the researchers observed. "The entire attack chain lives inside the HTML body of a single email, there are no malicious attachments." This "fileless" approach significantly hampers traditional gateway defenses that rely heavily on scanning attached files or blacklisting known URLs.
The core of the attack relies on an obfuscated JavaScript payload embedded within the email’s HTML structure. When a user with a vulnerable, active webmail session opens the email in the Zimbra interface, the script executes silently in the browser environment. This immediate, client-side execution bypasses server-side scanning and targets the active user session directly.

The objectives of the exfiltration phase are comprehensive. Once executed, the script begins a systematic harvest of sensitive user data. This includes standard credentials, active session tokens (allowing the attacker to hijack ongoing sessions), backup Two-Factor Authentication (2FA) codes, and even passwords previously saved by the browser profile. Furthermore, the payload gains the capability to access and exfiltrate the contents of the victim’s mailbox dating back 90 days. Data extraction is managed covertly, utilizing both standard HTTPS channels and, more stealthily, DNS tunneling to minimize detection by network monitoring tools.
The Enduring Appeal of Zimbra for Cyber Espionage
The targeting of Zimbra Collaboration Suite by Russian state-backed groups is not an isolated incident; rather, it represents a deeply entrenched operational preference. Zimbra, as a widely deployed open-source and commercial email and collaboration platform, services a vast ecosystem spanning hundreds of millions of users, including a significant footprint within governmental bodies and critical infrastructure organizations globally. This ubiquity makes it a high-value target for actors seeking broad access or specific intelligence.
This pattern of exploitation illustrates a recurring tactical theme: Russian intelligence services demonstrate a consistent pattern of prioritizing the compromise of widely used, perimeter-facing communication platforms. The exploitation of zero-day flaws in these platforms offers the highest return on investment for espionage efforts.
Consider the precedent set by other Russian groups. Beginning in February 2023, the Winter Vivern group (also known as Vivern) utilized a different reflected XSS vulnerability within Zimbra. That campaign was explicitly directed at breaching webmail portals belonging to organizations aligned with NATO, focusing on the electronic communications of government officials, military personnel, and diplomatic staff. The goal was clearly intelligence collection concerning Western alliance coordination.
More recently, in October 2024, a joint alert from U.S. and U.K. cybersecurity agencies highlighted the activities of APT29 (Cozy Bear/Midnight Blizzard), a cluster associated with Russia’s Foreign Intelligence Service (SVR). APT29 was observed engaging in "mass scale" attacks against vulnerable Zimbra servers, exploiting a pre-existing vulnerability previously used to steal email account credentials. This indicates a sustained, multi-agency commitment to leveraging Zimbra weaknesses.
Industry Implications and Defense Posture Analysis
The continuous weaponization of Zimbra flaws—now involving APT28 exploiting CVE-2025-66376 via a novel, HTML-embedded XSS attack—presents several critical implications for the cybersecurity industry and enterprise defense strategies.
Firstly, the trend confirms that supply chain risk extends beyond software development into the security profile of widely adopted, on-premise collaboration tools. Unlike cloud-native environments where patching cycles are rapid and centrally managed, self-hosted solutions like Zimbra often suffer from delayed remediation, particularly in under-resourced public sector environments. The two-week deadline imposed by CISA on FCEB agencies is aggressive, acknowledging that many organizations may struggle to audit, test, and deploy patches across complex, legacy deployments in such a short timeframe.
Secondly, the sophistication of the attack vector—relying solely on HTML body manipulation to trigger client-side code execution without needing traditional files—demands a fundamental shift in email security monitoring. Traditional signature-based scanning or simple attachment filtering is rendered moot. Defenders must invest heavily in advanced sandboxing technologies and sophisticated behavior analysis that can scrutinize the dynamic rendering of email content, looking for anomalous JavaScript execution within the context of an authenticated webmail session. The exfiltration over DNS, in particular, highlights the need for robust DNS traffic monitoring, as this protocol is frequently abused for covert command-and-control (C2) communication when standard ports are scrutinized.
From an expert perspective, the targeting of Ukrainian critical infrastructure, such as the Hydrology Agency, suggests that APT28’s objective is not merely broad credential theft but highly specific operational reconnaissance directly supporting kinetic or geopolitical objectives. Compromising hydrological data, for instance, can inform targeting, logistics planning, or even environmental manipulation strategies.
Future Impact and Trends in State-Sponsored Exploitation
The exploitation of CVE-2025-66376 serves as a potent warning about future trends in Russian cyber operations:
-
Focus on Session Hijacking over Initial Access: The payload’s emphasis on stealing session tokens and 2FA backup codes, alongside static passwords, signifies a mature attacker methodology. Stealing an active session token provides immediate, high-privilege access without needing to repeatedly execute the initial exploit or bypass ongoing MFA mechanisms, making the compromise far more persistent and difficult to detect post-breach.
-
The Persistence of XSS in Web Applications: Despite decades of security focus, XSS vulnerabilities remain a persistent weakness in legacy and complex web application codebases. Attackers will continue to favor these flaws in environments like Zimbra where the application runs complex client-side code to render email interfaces. Future exploits will likely focus on novel ways to execute payloads within modern browser security contexts, perhaps leveraging WebAssembly or intricate DOM manipulation techniques.
-
Weaponization of Patching Timelines: The consistent, rapid weaponization of Zimbra flaws immediately following or even prior to public disclosure demonstrates an acute awareness within Russian intelligence circles regarding vendor security advisories. This suggests a high degree of integration between vulnerability intelligence gathering and active operational deployment, often outpacing the patching capabilities of target organizations, particularly in government sectors facing resource constraints due to ongoing conflict.
For organizations utilizing Zimbra, or any similar self-hosted collaboration suite, the lesson is clear: a proactive, layered defense is mandatory. This includes rigorous application of vendor patches within hours, not weeks; segmenting the network so that compromised email servers cannot easily pivot to critical internal assets; and employing advanced security monitoring tools capable of detecting malicious script execution within the browser context of web applications. The battle for digital sovereignty often begins with securing the inboxes that hold the keys to national operations. The continued targeting of Zimbra by groups like APT28 ensures that this platform remains a critical battleground in the ongoing cyber conflict landscape.