The Federal Bureau of Investigation (FBI), spearheading a sophisticated, multinational law enforcement campaign designated "Operation Leak," has successfully neutralized LeakBase, a prominent clandestine digital marketplace dedicated to the trafficking of illicit data and cyber intrusion tooling. This coordinated takedown, involving agencies across fourteen jurisdictions, signals a significant escalation in global efforts to disrupt the infrastructure underpinning modern cybercrime ecosystems. The operation culminated in the seizure of the platform’s primary domains on March 3rd and 4th, replacing the illicit storefront with official seizure notifications, thereby formally alerting its expansive user base—estimated to comprise over 142,000 registered members—to the forfeiture of their digital assets.
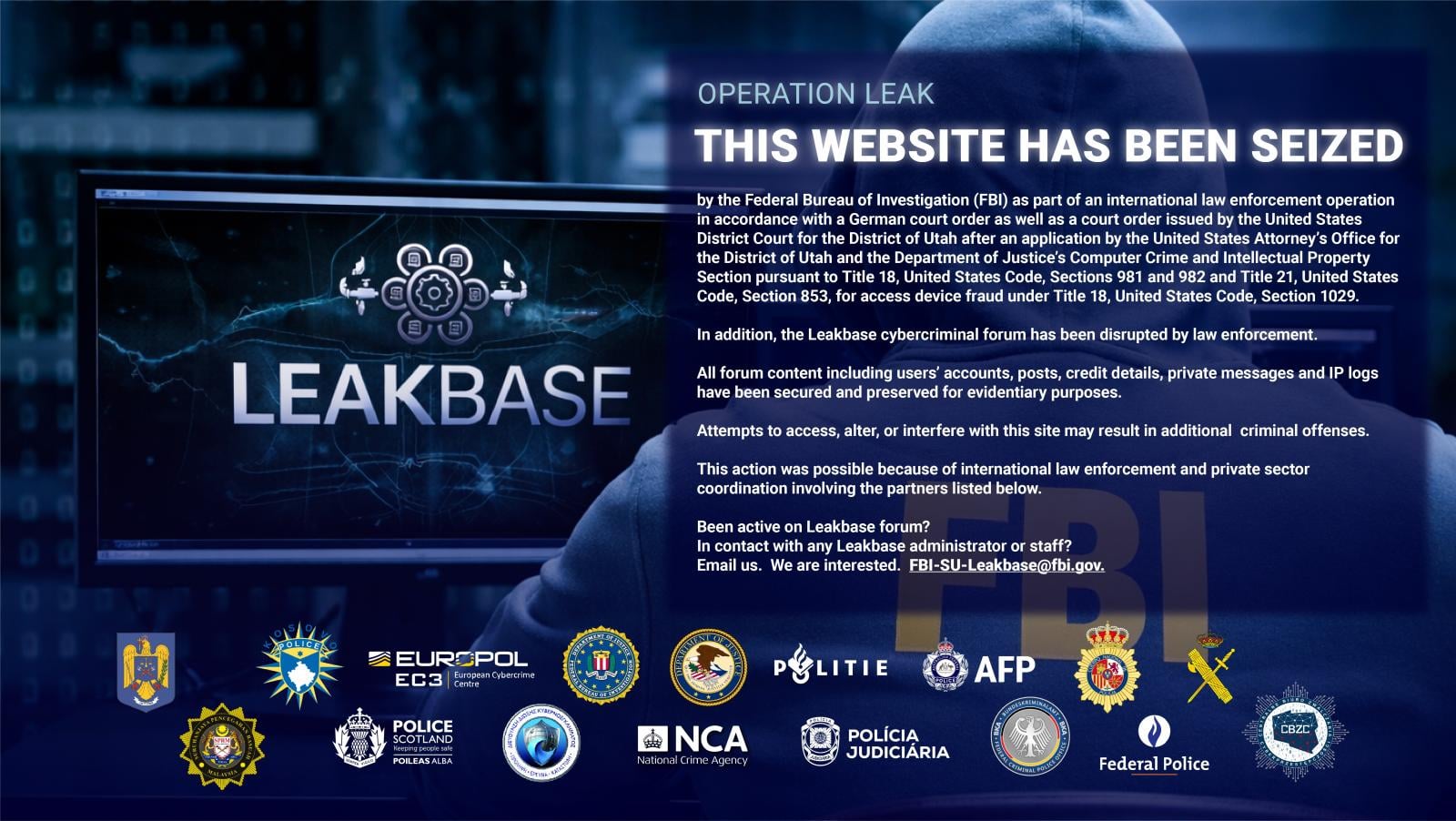
This action was not merely a domain seizure; it represented a comprehensive operational disruption. Law enforcement executed synchronized physical raids, conducted intensive interviews, and served numerous warrants across the United States, Australia, Belgium, Poland, Portugal, Romania, Spain, and the United Kingdom. These boots-on-the-ground activities complemented the digital neutralization efforts, aiming to apprehend key facilitators and gather ancillary evidence outside the immediate digital sphere of the forum itself. The immediate technical consequence of the shutdown is visible on the former primary address, leakbase[.]la, which now displays an FBI banner explicitly stating that the website has been seized as part of this international action.
Crucially, the seizure notice confirms the preservation of the entire platform architecture for forensic analysis. This includes the comprehensive database containing user accounts, financial transaction details, private correspondence, and, most alarmingly for its members, detailed IP logs. The notice serves a dual purpose: asserting governmental control and issuing a direct legal warning that any attempt to access, modify, or interfere with the seized infrastructure will constitute an additional federal offense. Furthermore, the redirection of the domain’s nameservers to ns1.fbi.seized.gov and ns2.fbi.seized.gov is a standardized procedural marker indicating definitive control by U.S. federal authorities in domain confiscation matters.
Europol confirmed the scope of the enforcement phase, noting that approximately 100 coordinated enforcement actions took place globally on March 3rd. These actions specifically targeted the community’s most dedicated participants, with measures being executed against 37 of the platform’s most active contributors. The subsequent day, March 4th, marked the technical phase where domain control was asserted, transitioning the operation into a sustained prevention phase focused on long-term deterrence and offender education regarding the tangible legal repercussions of engaging in these activities.
Background and Operational Context
LeakBase emerged in 2021, capitalizing on the vacuum created by the dissolution of predecessor platforms. Its origins are linked to the ARES threat group, suggesting a degree of sophistication and existing network infrastructure from its inception. Its growth trajectory was rapid, particularly following the cessation of operations for the Breached hacker forum. The platform’s success lay in its accessibility and comprehensive service offering. Unlike some high-tier, invite-only cybercrime markets, LeakBase maintained a low barrier to entry—it was free to join—which facilitated its rapid accumulation of a massive membership base.
The services offered spanned the breadth of the cybercrime economy. This included access to databases of compromised credentials and proprietary information, a dedicated marketplace for selling data leaks, proprietary exploits, and various other cyber services. A critical feature was its integrated escrow payment system, designed to mediate disputes and foster trust among otherwise adversarial criminal elements. Beyond transactional activities, LeakBase served as a knowledge repository, hosting specialized sub-forums dedicated to programming techniques, advanced hacking methodologies, social engineering tactics, cryptographic obfuscation, and operational security (OpSec) best practices. This fusion of marketplace and educational hub made it a potent incubator for emerging cyber threats.

The dismantling of LeakBase follows a decisive pattern established by international law enforcement over the past several years. The takedown of RaidForums in 2022 and BreachForums in 2023—the latter resulting in the eventual conviction and sentencing of its founder to three years imprisonment in 2025—demonstrates a sustained, strategic focus on degrading the communication and commerce channels utilized by threat actors. These forums are not merely repositories; they are the organizational scaffolding that allows disparate actors to collaborate, validate exploits, and monetize their illicit gains efficiently.
Industry Implications: The Erosion of Cybercrime Infrastructure
The seizure of LeakBase carries significant implications for the cybersecurity industry and corporate risk management. The immediate impact is the disruption of the data supply chain. Companies whose data was listed or sold on LeakBase now have potential intelligence regarding the scope and nature of their breaches, and law enforcement now possesses a treasure trove of evidence detailing how that data was traded.
From a security perspective, the loss of LeakBase means that threat actors lose a centralized, reliable source for ready-made tools, zero-day exploits, and verified compromised data sets. While the cybercrime community is inherently resilient and decentralized, these major forum closures create temporary friction. Criminals must now dedicate time and resources to establishing new trusted marketplaces, vetting new suppliers, or reverting to less efficient, peer-to-peer communication methods. This friction translates into momentary delays in the deployment of new attack vectors derived from forum knowledge.
Moreover, the preservation of IP logs and private messages is an invaluable intelligence coup for global security agencies. These records can link anonymous forum handles to real-world identities, map out criminal networks, and provide insights into the specific motivations, financing, and technical proficiency levels within the threat landscape. This intelligence will undoubtedly fuel future targeted operations against ransomware groups, state-sponsored actors, and financially motivated hacking syndicates who frequented the platform.
Expert Analysis: The Shifting Landscape of Underground Forums
Security analysts have long characterized the evolution of these cybercrime forums as a cyclical process of emergence, growth, consolidation, and disruption. LeakBase represented the current iteration of the "hacker forum" model. Its predecessor, BreachForums, was structurally similar but perhaps more focused on ransomware-related data dumps. LeakBase broadened the scope, becoming a more generalized hub for criminal knowledge exchange.
The sustained success of these forums often hinges on the perceived longevity and security promised by the administrators. LeakBase, by offering free access and integrating robust escrow services, managed to attract a wider demographic, including lower-skilled actors who benefit from the ready access to vetted tools. The core expertise of the administrators—often skilled programmers or network engineers—is what lends credibility to the platform. When the FBI and Europol dismantle these structures, they are targeting not just the marketplace, but the specific technical acumen that keeps the marketplace functional and trusted.
A key analytical point here is the role of international cooperation. The involvement of fourteen countries underscores that cybercrime infrastructure is inherently borderless, and its effective dismantling requires a synchronized global response. Europol’s role as the central coordinator highlights the maturation of cross-border digital investigations, moving beyond simple data sharing to executing complex, simultaneous physical and digital enforcement actions. This level of integration is difficult for decentralized criminal enterprises to counter.
The fact that the seizure occurred just a year after the BreachForums administrator was sentenced indicates that law enforcement is rapidly moving to intercept successor platforms before they achieve critical mass. This proactive stance suggests a strategy of "whack-a-mole" that is becoming increasingly effective, forcing adversaries to constantly rebuild and re-establish trust among new cohorts.
Future Impact and Emerging Trends
The disruption of LeakBase will inevitably lead to fragmentation and adaptation within the cybercriminal underground. Several trends are likely to emerge in the wake of this operation:
1. Increased Decentralization and Encryption: Threat actors, wary of centralized, seizure-prone domains, may migrate toward more decentralized communication methods. This could involve greater reliance on end-to-end encrypted chat applications, blockchain-based forum structures, or sophisticated peer-to-peer networks that are inherently more difficult for single-entity law enforcement actions to neutralize. The reliance on clearnet domains for primary commerce will likely decrease.
2. Specialized Niche Markets: Instead of large, all-encompassing forums like LeakBase, the market may bifurcate into highly specialized, smaller, invite-only communities focusing on specific threats, such as dedicated ransomware affiliates, specific exploit development groups, or state-backed intelligence sharing circles. These smaller groups are harder to infiltrate and monitor comprehensively.
3. Heightened OpSec Paranoia: The seizure of IP logs and private messages will instill a deeper sense of paranoia among remaining threat actors. This might lead to stricter internal vetting processes, forcing members to rely on complex chains of proxies, Virtual Private Networks (VPNs), and anonymization layers, potentially increasing the operational cost and complexity for minor criminal ventures.
4. Focus on Private Sector Intelligence Sharing: The success of "Operation Leak" was partially attributed to "private sector coordination." Moving forward, the industry can expect increased pressure and incentive for security vendors and corporations to proactively share Indicators of Compromise (IOCs) and threat intelligence with law enforcement agencies, effectively creating an early warning system that helps identify the digital footprints of emerging forums before they become major threats.
The takedown of LeakBase is a significant victory in the ongoing digital conflict, demonstrating the capability of international collaboration to dismantle sophisticated criminal enterprises. However, it is a temporary victory. The enduring challenge for global security lies not just in seizing the current iteration of the marketplace, but in anticipating and neutralizing the next evolution of underground criminal infrastructure that is already likely under development.

