The operational integrity of the United Kingdom’s official corporate registrar, Companies House, has been severely compromised, necessitating an emergency shutdown and subsequent remediation of its WebFiling platform. Following reports of a critical security vulnerability that persisted for approximately five months, the agency confirmed that sensitive data belonging to the five million entities registered in the UK was potentially exposed to unauthorized viewing. The incident highlights the inherent fragility in large-scale government digital infrastructure, particularly when managing vast repositories of proprietary corporate and personal information.
The issue came to light through the diligent efforts of external researchers. Dan Neidle, the founder of the non-profit organization Tax Policy Associates, formally reported the exploit to the UK corporate register after initial attempts by John Hewitt of Ghost Mail, the individual who first identified the specific flaw, to secure a timely response were apparently unsuccessful. This delay in initial acknowledgment underscores a potential procedural gap in how external security disclosures are triaged and escalated within the agency’s response framework, even when the reporting parties are acting in good faith to protect national business data.
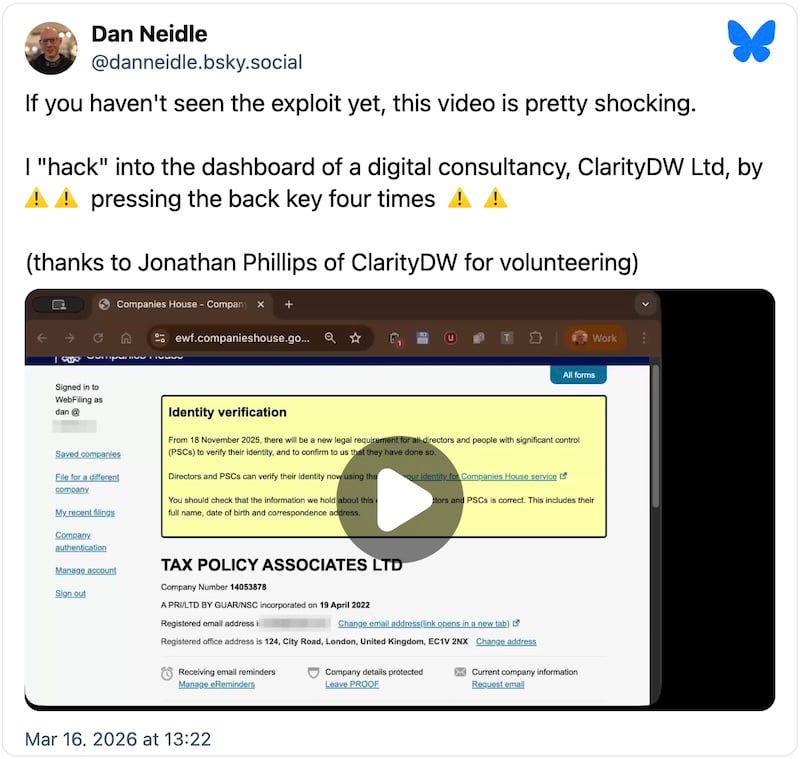
The mechanics of the breach, as detailed by Neidle, illustrate a classic case of inadequate state management within the WebFiling service following a major update. The vulnerability was reportedly triggered by a sequence of actions available to any authenticated user. Upon logging into their own company dashboard, an authorized user could navigate to the function intended for filing on behalf of a different entity. By inputting the unique company number of any of the five million registered businesses, the system should have strictly required an authentication code specific to that target entity. However, due to the flaw introduced during a system update in October 2025, navigating back from the authentication prompt—by utilizing the browser’s ‘back’ function—incorrectly redirected the user not to their original dashboard, but directly into the administrative portal of the second, unrelated company.
This simple yet devastating navigation error effectively bypassed crucial authorization checks, granting the logged-in user access to the target company’s sensitive internal data repository. The scope of the exposure is significant: the data accessible included information not typically visible on the public register, most critically the residential addresses and email contact details of company directors and management personnel. Furthermore, the agency acknowledged that the flaw created a window wherein unauthorized filings—such as changes to director appointments or the submission of annual accounts—might have been technically possible, though the extent of any successful malicious modifications remains under intensive investigation.
Companies House formally acknowledged the severity of the situation on Monday, concurrent with bringing the patched WebFiling service back into operational status. Their internal review traced the root cause back to the system overhaul performed in October 2025, suggesting that the vulnerability was not an introduced vulnerability but rather a regression or an oversight in the security hardening following the update.
The Spectrum of Compromised Data and Mitigation Efforts
While the initial reports focused on the exposure of private addresses, the agency’s subsequent official statement detailed a broader set of potential compromises. The data potentially viewed by unauthorized parties included dates of birth, residential addresses, and specific company email addresses. This level of PII (Personally Identifiable Information) leakage represents a substantial risk, moving beyond simple corporate espionage into the realm of targeted fraud, identity theft, and physical security threats for company officers.
Crucially, Companies House moved quickly to clarify what remained secure, attempting to reassure the business community. They asserted that core authentication credentials, specifically user passwords, were not compromised. Furthermore, data handled during the initial Know Your Customer (KYC) or identity verification process, such as passport details or other highly sensitive document scans used for initial registration, were reportedly isolated from the compromised WebFiling session pathways. Perhaps most reassuringly for legal and financial stability, the agency stated that no already-filed historical documents, such as finalized accounts or confirmation statements, could have been retroactively altered or deleted through this specific vector. The threat was primarily one of unauthorized viewing and, potentially, unauthorized submission of new, unverified data.

The regulatory implications of this event are immediate and severe. Companies House has formally engaged the United Kingdom’s primary data protection authority, the Information Commissioner’s Office (ICO), and the National Cyber Security Centre (NCSC), the technical advisory body for the UK government’s cybersecurity strategy. This dual reporting mechanism signals the dual nature of the breach: a failure in data privacy compliance and a failure in critical national digital security infrastructure.
Industry Implications and the Erosion of Trust
The implications of a security lapse at the central corporate registry ripple far beyond the immediate technical fix. Companies House serves as the bedrock of trust for corporate transparency in the UK economy. Banks, lenders, investors, legal firms, and international trade partners rely on the authenticity and security of the data held within this register to conduct due diligence and execute transactions.
For the five million affected companies, the immediate concern shifts to forensic investigation and notification compliance. They must now assess whether their specific data was accessed and, if so, formulate appropriate risk mitigation strategies for their directors. This could involve enhanced personal security measures, changing contact information, or managing reputational fallout.
From an industry perspective, this incident acts as a stark reminder of the risks associated with centralized data storage, even within governmental silos. The reliance on a single point of failure for verification and identity management creates an attractive, high-value target for malicious actors. If a vulnerability exists in the workflow of filing information—even one requiring an existing login—it undermines the entire premise of digital corporate governance.
Furthermore, the nature of the exploit—a session management or state-handling error—is often indicative of insufficient unit testing or regression testing protocols following major system updates. In an environment where continuous integration/continuous deployment (CI/CD) pipelines are standard, the fact that a vulnerability introduced in October 2025 went undetected through regular monitoring and testing until March 2026 suggests potential weaknesses in the quality assurance gates protecting public-facing government applications.
Expert Analysis: Session Management and Privilege Escalation
Security architects often categorize this type of breach as unauthorized privilege escalation, albeit achieved through a flawed state transition rather than a traditional elevation of user rights. The system incorrectly associated the authenticated session token of User A with the context and permissions of Company B after the user navigated back from an authorization checkpoint.
Dr. Alistair Finch, a specialist in secure software architecture and public sector compliance, noted that such vulnerabilities frequently arise in applications that manage multiple distinct organizational contexts within a single authenticated session. "The WebFiling service handles millions of distinct tenants," Dr. Finch commented. "The architecture must rigorously maintain session context boundaries. If the application failed to correctly invalidate or refresh the session context when the user aborted the ‘file for another company’ workflow, the previous request state—which was successfully authenticated for Company A—might have incorrectly inherited the context of the subsequent request intended for Company B, leading to a dangerous cross-tenant data bleed."
The fact that the exploit required the attacker to already be logged in (i.e., a legitimate user) defines this as an insider threat vector or, more accurately, a vulnerability exploited by a legitimate user against other legitimate users. This type of flaw is particularly insidious because standard perimeter defenses (firewalls, intrusion detection systems) are designed to stop external attackers; they offer little defense against authenticated users who possess the necessary credentials to initiate the flawed workflow.
Future Impact and Regulatory Scrutiny
The fallout from this security incident will undoubtedly drive significant changes in how UK government bodies manage digital registries. We can anticipate increased scrutiny from the ICO regarding the data handling practices of all public sector entities, particularly concerning the storage and transmission of director PII.
Firstly, expect an immediate, mandatory audit of all similar government services that manage context switching between organizational entities. This will likely involve stress-testing session management protocols under unusual navigation paths, mirroring the exact technique used to expose the flaw.
Secondly, there will be intensified pressure on Companies House to expedite the transition to more modern, identity-centric access controls, potentially moving away from legacy WebFiling interfaces toward more robust, API-driven systems where context validation is enforced at a granular, request-level, rather than relying on sequential page navigation.
Thirdly, the incident raises serious questions about accountability and the security culture surrounding government technology modernization projects. Tax Policy Associates’ role in escalating the issue highlights the critical function of external watchdogs when internal reporting mechanisms may not be sufficiently rapid or responsive. Future policy may need to mandate clearer, faster disclosure channels for high-severity vulnerabilities reported by external researchers, perhaps overseen by the NCSC.
The five-month window during which this vulnerability existed—from October 2025 until the fix was deployed—is a crucial metric for regulators. Companies House must now conduct a thorough forensic accounting to definitively state whether data was merely visible or if unauthorized changes were successfully perpetrated. Even if no malicious filings were made, the mere potential for directors’ sensitive personal information to be systematically harvested over five months constitutes a significant data breach requiring specific remedial action under UK GDPR guidelines.
In conclusion, the temporary shuttering of WebFiling following the confirmation of this systemic flaw represents a major governance challenge for the UK. It serves as a high-profile case study demonstrating that even core infrastructure responsible for national business transparency is susceptible to critical errors introduced during routine maintenance and updates. The long-term consequence will be a mandate for deeper, more rigorous security validation across the entire public digital estate, prioritizing state management integrity above all else when handling sensitive, multi-tenant data. The ongoing investigation into exploitation remains paramount to fully quantifying the damage to corporate and personal security across the five million affected UK businesses.

