The landscape of mobile device security is undergoing a significant evolution, driven by the increasing realization that the modern smartphone is not merely a communication tool but a repository of critical financial data, identity credentials, and sensitive personal information. In a strategic move to counter rising threats associated with physical device theft, Google has unveiled a new suite of enhanced authentication safeguards and recovery mechanisms specifically targeting the Android ecosystem. These updates represent a crucial iteration of the platform’s commitment to user security, building upon foundational anti-theft protocols initially introduced in late 2024.
The urgency underpinning these developments is clearly articulated by Google’s Android Security Team, which noted that phone theft transcends simple device loss; it functions as a vector for sophisticated financial fraud, instantly exposing individuals to risks of data exfiltration and monetary compromise. This ongoing arms race against opportunistic criminals necessitates a proactive, layered defense strategy, moving beyond simple screen locks to embed security deeper within the operating system’s core interactions.
Deepening Authentication Resilience
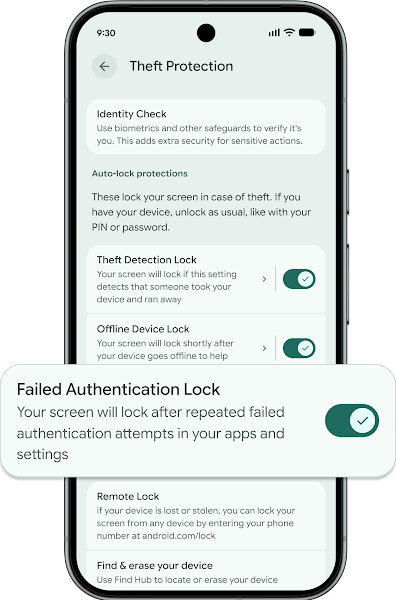
Central to this latest rollout are granular refinements to existing security features, designed to thwart brute-force attacks and unauthorized access attempts following a physical seizure of a device. A key enhancement involves the Failed Authentication Lock feature. Previously, this mechanism operated with a static response to repeated incorrect entries of PINs, patterns, or passwords. Now, users gain greater control, with a dedicated settings toggle allowing them to govern its activation. This offers flexibility for users in specific environments while ensuring the feature remains easily accessible for those prioritizing maximum resistance to physical tampering.
Simultaneously, Google is addressing the practical challenges of securing devices that may be handled by non-users, such as children, while tightening the net against determined thieves. The system now intelligently differentiates between accidental input errors and deliberate guessing sprees. Repeated incorrect guesses will no longer prematurely trigger hard lockouts caused by innocent mistakes, but conversely, the system is increasing the required lockout duration following sustained failed attempts. This dual approach optimizes the user experience while raising the temporal barrier for attackers attempting dictionary or brute-force attacks on credential entry screens.
Biometric Integrity Across the Operating System
Perhaps the most far-reaching update concerns the expansion of Identity Check. This feature mandates biometric authentication (fingerprint or facial recognition) for sensitive operations executed when the device is outside of established "trusted locations" (like the user’s home or workplace Wi-Fi). The critical expansion here is the integration across the entire Android Biometric Prompt framework.

Previously, this might have been limited to core system functions or proprietary Google applications. Now, any application—including critical third-party services such as major banking applications and the Google Password Manager—that leverages the standardized Android Biometric Prompt for high-stakes actions will automatically inherit this geo-fenced biometric verification requirement.
This change has profound industry implications. For financial institutions, it means that even if a thief manages to bypass the initial lock screen, accessing stored credentials or initiating high-value transfers within a banking application requires the physical presence and biometric validation of the legitimate user, even if the device has been transported miles away from its usual operational environment. It effectively renders stolen credentials useless unless the thief also possesses the user’s physical biometric markers. This shifts the security paradigm from solely securing the device boundary to securing the action itself, irrespective of the device’s immediate location.
Strengthening Remote Control and Recovery
The ability to remotely secure a device after theft has long been a staple of mobile security, but the integrity of that remote command is paramount. Google has updated its Remote Lock utility, accessible via android.com/lock, by introducing an optional, secondary security challenge.
Before executing a remote lock command, users can now opt for an additional verification step designed to confirm ownership beyond the initial Google account credentials used to access the remote portal. While the specifics of this challenge are kept confidential for security reasons, this move is likely intended to mitigate scenarios where an attacker gains access to a user’s Google account credentials through a separate phishing attack, preventing them from remotely locking the device as a malicious act of harassment or to accelerate the resale of the device by eliminating the owner’s final recourse. This adds a vital layer of defense against account takeover attacks that precede physical theft.
Regional Rollouts and Foundational Requirements
Google is employing a targeted strategy for deployment, linking feature availability to OS versions and geographic necessity. For new Android devices activated in Brazil—a region frequently cited for high rates of device snatching—two key features are being enabled by default: Theft Detection Lock and Remote Lock. Theft Detection Lock is particularly noteworthy as it employs on-device intelligence to recognize the tell-tale signs of a "snatch-and-run" incident—rapid acceleration followed by immediate power-down or disconnection—and locks the device instantaneously, often before the thief can even attempt to access it.
However, the feature requirements highlight a segmentation in the Android user base:

- Authentication Safeguards (e.g., enhanced Identity Check, granular Failed Authentication Lock controls): These require the latest iteration, Android 16 or later, signifying that these deep, OS-level changes are reserved for the most current devices.
- Enhanced Recovery Tools (e.g., updated Remote Lock functionality): These are accessible to a broader base, running on Android 10 or later.
This distinction underscores the complexity of maintaining uniform security across the vast, fragmented Android hardware ecosystem. While core recovery functions can be pushed back to older, widely adopted OS versions, the most advanced, context-aware security features necessitate the newer underlying architecture provided by Android 16.
Contextualizing the Security Evolution
This current security push does not exist in a vacuum. It follows closely on the heels of significant advancements in combating digital fraud, notably the expansion of In-Call Scam Protection. Introduced in Android 16 and recently broadened in the US to include major banking applications like Cash App and JPMorgan Chase, this feature actively monitors screen-sharing activity during calls with unknown numbers. If a user launches a financial application while sharing their screen with a contact outside their trusted list, the system issues warnings, effectively interrupting common social engineering tactics used to coerce victims into transferring funds or revealing passwords.
The synergy between these physical and digital protections is critical. Thieves often use stolen devices to immediately access financial apps, or alternatively, use social engineering over the phone to trick victims into granting remote access. By hardening the physical device against immediate access (via new lock features) and hardening the digital interaction against real-time manipulation (via in-call scam protection), Google is constructing a more robust digital perimeter.
Expert Analysis: The Move Toward Device-Level Zero Trust
From a security architecture perspective, these updates signal Google’s accelerated commitment to a "device-level Zero Trust" model. In traditional models, once a user authenticates to the device, a high degree of trust is implicitly granted to applications running on that device. The expansion of Identity Check, requiring re-authentication outside trusted zones, breaks this implicit trust chain.
Dr. Evelyn Reed, a mobile security architect formerly with a major telecommunications firm, notes: "What Google is doing with Identity Check is embedding location awareness directly into the authorization policy engine for critical services. This is far more resilient than relying solely on hardware-level encryption keys. If a thief manages to clone the device’s encrypted storage, they still cannot use stored application credentials or banking apps without the user’s current, real-world biometric confirmation near the device. It forces the attacker back to a physical presence requirement, which significantly increases their risk of apprehension."
The introduction of optional security challenges for Remote Lock also aligns with evolving standards for managing digital assets. As more of our lives migrate to mobile devices, the recovery process itself becomes a high-value target. Ensuring that the recovery action cannot be easily hijacked is as important as securing the device during active use.
Industry Implications and Future Trajectories
The impact of these security enhancements extends beyond the immediate user base. For the broader mobile application development community, the mandatory utilization of enhanced biometric prompts for sensitive operations sets a higher baseline expectation for security hygiene across the ecosystem. Developers must now ensure their apps correctly interface with Android 16’s security layers to benefit from these protections, standardizing behavior across diverse hardware manufacturers.
The move to bundle features like Theft Detection Lock by default in key markets like Brazil sets a powerful precedent. If successful in reducing crime statistics in those regions, it creates market pressure for these features to become standard, opt-out settings globally. This mirrors the industry shift seen with mandatory two-factor authentication—once optional, now often the default expectation for account security.
Looking ahead, the trajectory suggests further integration of on-device AI/ML models to detect anomalous user behavior beyond simple location data. Future iterations might incorporate gait analysis, typical usage patterns, or even changes in typing cadence to further refine the definition of a "trusted user" versus a thief attempting to mimic legitimate activity.
The challenge remains the maintenance burden. As the threat landscape evolves—with criminals employing more sophisticated social engineering and potentially exploiting vulnerabilities in the biometric APIs themselves—Google must commit to rapid patching cycles for these foundational security modules. The successful deployment across Android 10+ for recovery tools demonstrates Google’s capability to maintain legacy support while pushing cutting-edge defense mechanisms to the latest OS versions. These updates solidify Android’s position, emphasizing that mobile security is now a holistic concern encompassing physical control, digital credential protection, and real-time behavioral monitoring.

